Cloud-computing enables mobile devices to provide users with access to a wide variety of applications and services. Which of the following is a disadvantage of mobile devices?
Proprietary information for your company’s online business was released to a competitor. Which of the following preventative measures should your company take to ensure that its proprietary information is protected in the future?
Prior to HTML5, structuring a Web site using style sheets with the < dlv > tag and its, attribute has been an acceptable practice to govern the document’s structure. With the emergence of
HTML5, what five new elements were introduced for more effectiveness?
You are configuring an e-mail client to connect to your e-mail account. Which of following is required to set up the e-mail account?
A family member has just sent you an e-mail message that contains highly personal details about a family matter. The message was sent to your company e-mail address. The family member has requested that you respond with your ideas about how to resolve the situation. Which of the following is a reason for you to call your family member and discuss the matter over the phone instead?
Consider the following address:
http://www.ClWcertified .com/certifications/web_foundations/iba.php
Which part of the URL represents the server name on which this page resides?
When the user clicks the Submit Query button on a form, the browser sends the information entered in the form to the Web server as a raw text string. The basic element of a raw text string is a name=value pair. A CGI script parses and formats the raw text string into a human-readable format. Which attribute of the form field elements organizes information input by the user into name=value pairs?
Emelia and Lola have created a new software application that allows messaging site subscribers to analyze the message statistics in order to more easily assess and interact with followers. They have decided to license this software according to the GNU GPL Version 3. What does this license allow them to do with their software?
Marion has been hired by a popular national salon business to refresh its existing Web site and update it to valid HTML5 code. Money is not an issue, but time is. Marion is asked to complete the project within eight weeks. The site currently includes 10 pages and connects to a back-end database so that customers can sign in for a personalized experience. Marion suspects that most of the existing code will need to be replaced. Marion must ensure that she has plenty of time for the testing phase, so she needs to complete the planning phase, in which she selects the multimedia for the site, within the next couple days. Which strategy should Marion use in the planning phase?
The process of wire framing typically includes determining Web site goals plus:
Marcella is looking for a very unique product online. She has found one on the XYZ Company’s Web site, which is designed well and appears to be legitimate. As she navigates through the checkout process, she reaches the checkout page with this URL, which asks her to enter her credit card information:
http://XYZ.com/gp/checkout.html/ref=chk_out_TLS12B_lb?ie=IJTFB & docld=10007931
Why should Marcella cancel her online transaction instead of proceeding?
You are a small-business owner and would like to encourage employees to bring their own devices (BYOD) to work. Which of the following can help reduce the security risks associated with a BYOD implementation?
Jenny recently switched from broadband cable Internet to ADSL service with her local phone company. To economize, she chose the self-installation option. It appears that her ADSL modem is not allowing her to connect to the Internet. Which setting should she check first?
Which organization is responsible for managing domain names so that each one is unique, and (once registered) cannot be used by an unauthorized individual or organization?
Which choice lists the HTML5 elements that define the document structure for a Web page?
You are a computer technician supporting a small 15-computer Internet lab. The computers are regularly used to browse the Internet and download files. Users have recently complained that they receive error messages saying the hard disk is full or out of space. You suspect this is a result of a large amount of temporary Internet files. Which of the following is a way to easily delete all the temporary Internet files?
You have recently purchased a new wireless router. You would like to configure a name for your wireless network so that you can easily identify it when scanning available wireless networks. Which term describes this wireless network device name?
Consider the network configuration shown in the command prompt:
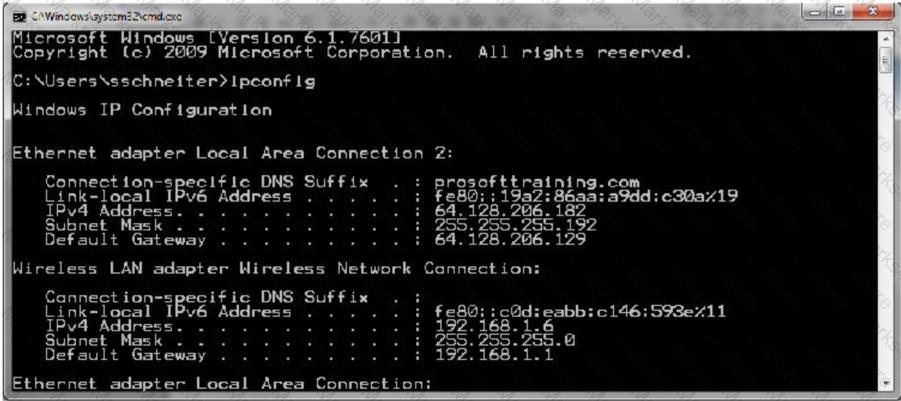
What does the Default Gateway identify?
Paul has just finished a very important sales meeting with a potential customer and he needs to update his supervisor at the corporate office, which is located in another country. Paul is debating whether to text or e-mail his supervisor about the meeting details. Which of the following would be the best practice for communicating with his supervisor?
Sampson has used HTML5 to create a Web page that contains image-based navigation buttons.
He would like to add text-based navigation to help ensure accessibility. Which of the following
HTML5 elements should he use?
A friend just sent you a link to a Facebook page with information that you find very useful. You want to be able to recall the site in the future from your desktop computer, or from your mobile device while away from your desk. Which is the best approach?