200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) Questions and Answers
Which metric is used to capture the level of access needed to launch a successful attack?
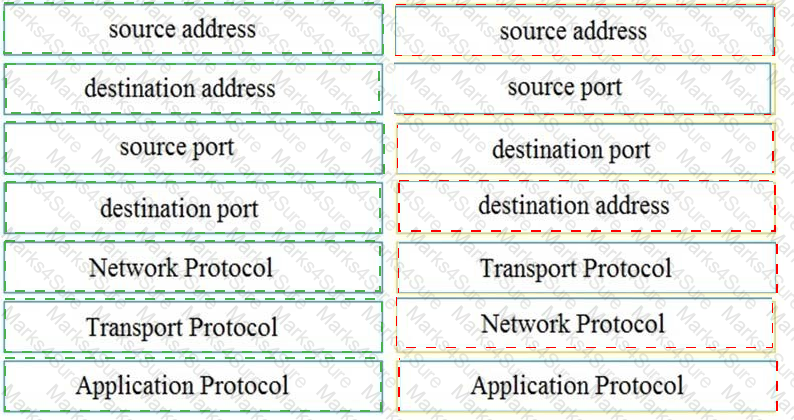
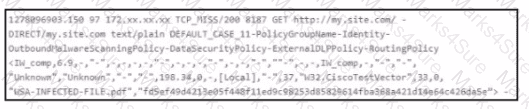
Refer to the exhibit.

Which two elements in the table are parts of the 5-tuple? (Choose two.)
A company had a recent breach and lost confidential data to a competitor. An internal investigation found out that a new junior accounting specialist logged in to the accounting server with their user ID and stole confidential data. The junior accounting specialist denies the action and claims that the attempt was done by someone else. During court proceedings, the company presents logs and CCTV camera recordings that show the malicious insider in action. Which type of evidence has the company presented?
Which security principle is violated by running all processes as root or administrator?
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.

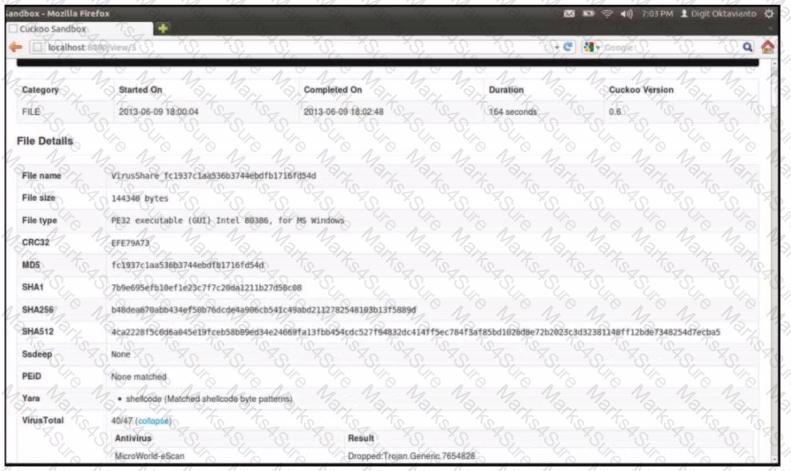
Exhibit.
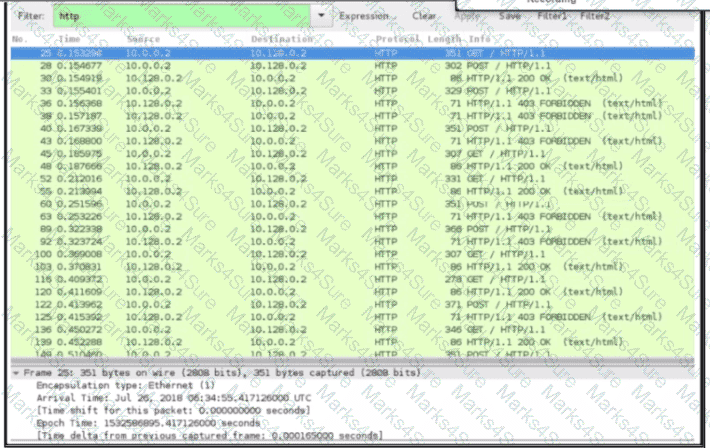
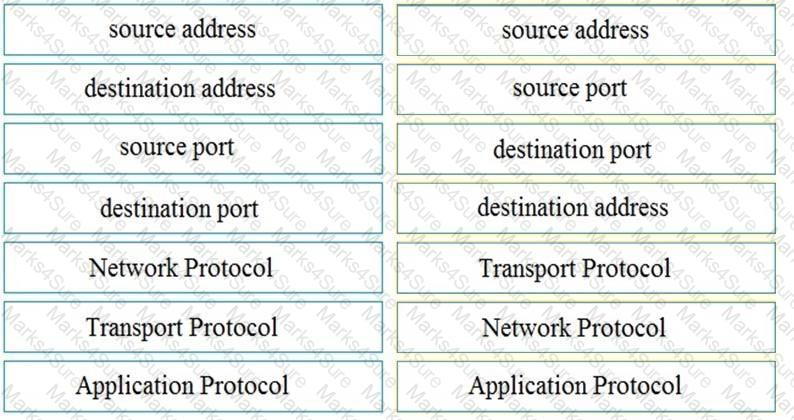
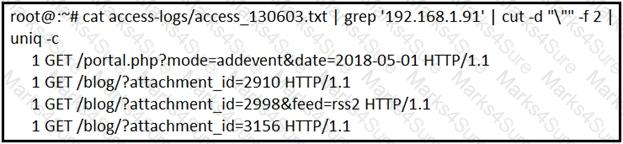
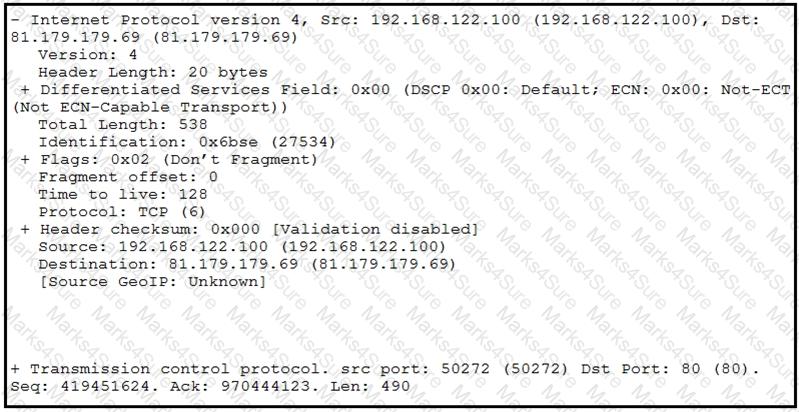
An engineer received a ticket about a slowdown of a web application, Drug analysis of traffic, the engineer suspects a possible attack on a web server. How should the engineer interpret the Wiresharat traffic capture?
A company encountered a breach on its web servers using IIS 7 5 Dunng the investigation, an engineer discovered that an attacker read and altered the data on a secure communication using TLS 1 2 and intercepted sensitive information by downgrading a connection to export-grade cryptography. The engineer must mitigate similar incidents in the future and ensure that clients and servers always negotiate with the most secure protocol versions and cryptographic parameters. Which action does the engineer recommend?
An engineer is working on the implementation of digital certificates for new cntical web applications One of the requirements is that the https connection must be validated and protected against malicious network impersonators The server will be exposed externally from the DMZ network Which certificate must be used?
An automotive company provides new types of engines and special brakes for rally sports cars. The company has a database of inventions and patents for their engines and technical information Customers can access the database through the company ' s website after they register and identify themselves. Which type of protected data is accessed by customers?
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
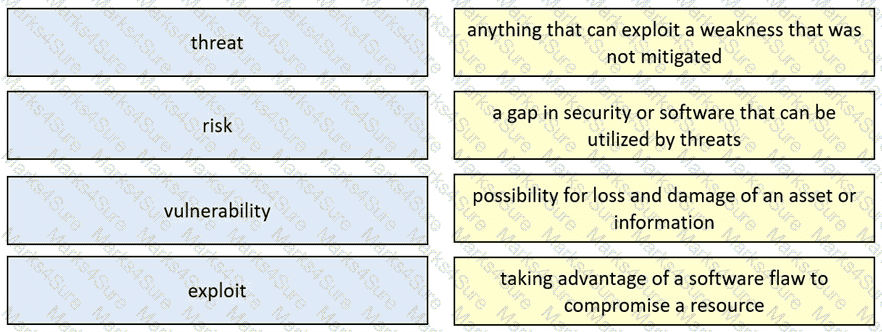
What describes the difference when comparing attack surface and vulnerability in practice?
Drag and drop the security concept from the left onto the example of that concept on the right.
An intruder attempted malicious activity and exchanged emails with a user and received corporate information, including email distribution lists. The intruder asked the user to engage with a link in an email. When the fink launched, it infected machines and the intruder was able to access the corporate network.
Which testing method did the intruder use?
A CMS plugin creates two files that are accessible from the Internet myplugin html and exploitable php A newly discovered exploit takes advantage of an injection vulnerability m exploitable php To exploit the vulnerability an HTTP POST must be sent with specific variables to exploitable php A security engineer notices traffic to the webserver that consists of only HTTP GET requests to myplugin html Which category does this activity fall under?
STION NO: 102
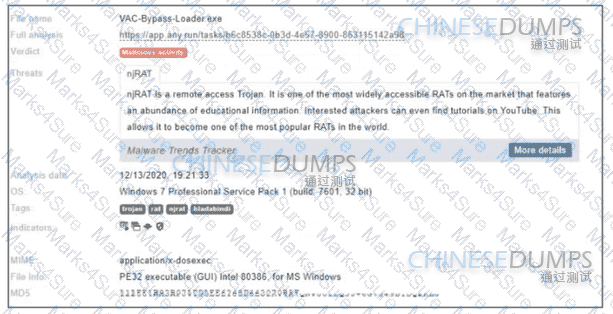
Refer to the exhibit.
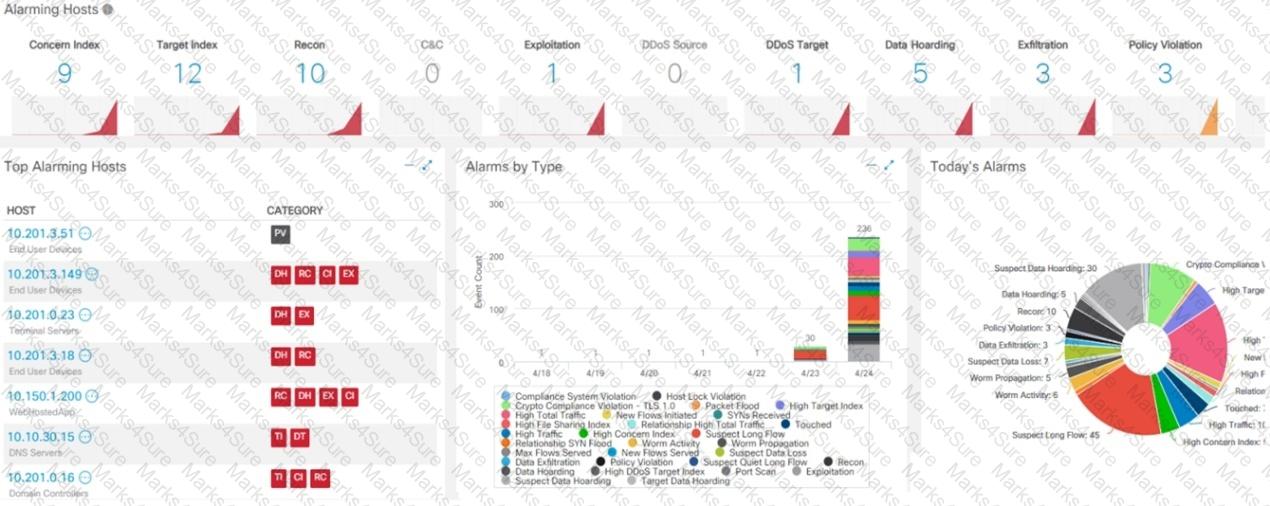
What is the potential threat identified in this Stealthwatch dashboard?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
An engineer runs a suspicious file in a sandbox analysis tool to see the outcome. The analysis report shows that outbound callouts were made post infection.
Which two pieces of information from the analysis report are needed to investigate the callouts? (Choose two.)
A network engineer discovers that a foreign government hacked one of the defense contractors in their home country and stole intellectual property. What is the threat agent in this situation?
Which principle reduces the risk of attackers gaining access to sensitive data by compromising a low-level user account?
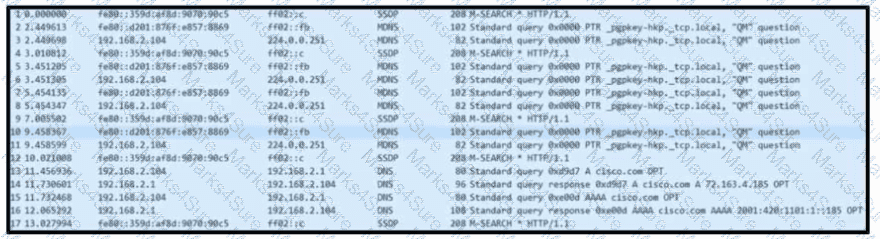
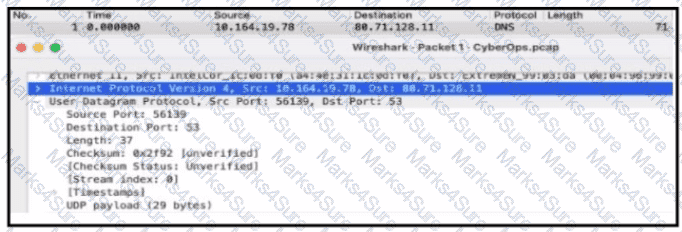
Refer to the exhibit. Based on the .pcap file, which DNS server is used to resolve cisco.com?
One of the objectives of information security is to protect the CIA of information and systems. What does CIA mean in this context?
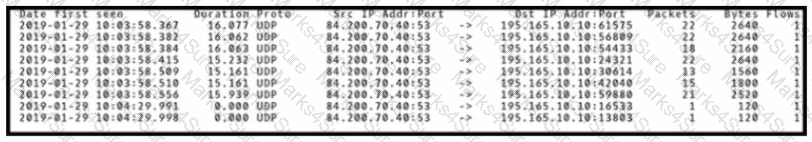
Refer to the exhibit
An engineer is analyzing DNS response packets that are larger than expected The engineer looks closer and notices a lack of appropriate DNS queries What is occurring?
An organization recently experienced a major incident in which servers were attacked and data integrity was compromised. The attacker exploited a vulnerability in TLS 1.2 and performed a man-in-the-middle attack by downgrading the connection. Which action should a security specialist take to prevent similar attacks in the future?
Which access control should a chief information security officer select to protect extremely sensitive data categorized at various levels of confidentiality?
Which type of attack occurs when an attacker is successful in eavesdropping on a conversation between two IP phones?
A security team receives a ticket to investigate suspicious emails sent to company employees from known malicious domains. Further analysis shows that a targeted phishing attempt was successfully blocked by the company’s email antivirus. At which step of the Cyber Kill Chain did the security team mitigate this attack?
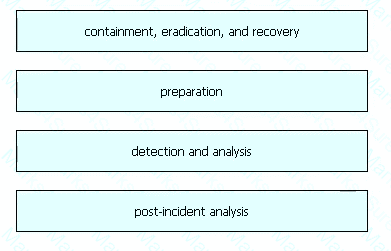
Which two elements of the incident response process are stated in NIST Special Publication 800-61 r2? (Choose two.)
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture, the analyst cannot determine the technique and payload used for the communication.
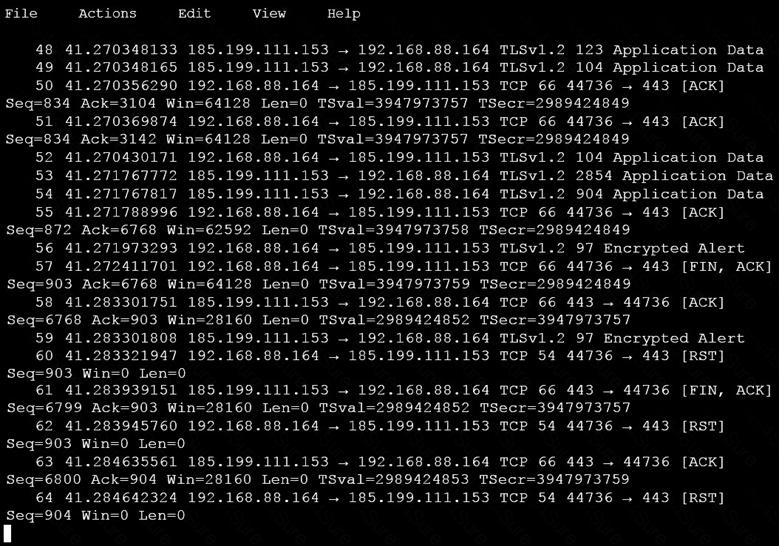
Which obfuscation technique is the attacker using?
Refer to the exhibit.
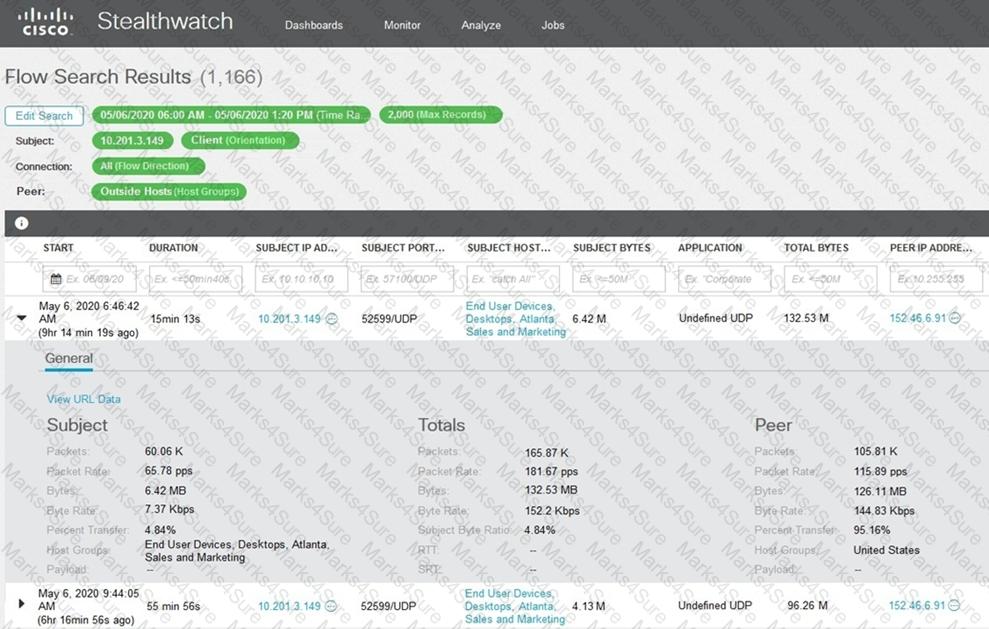
What is the potential threat identified in this Stealthwatch dashboard?
What is the impact of false positive alerts on business compared to true positive?
Which incidence response step includes identifying all hosts affected by an attack?
A threat actor penetrated an organization ' s network. Using the 5-tuple approach, which data points should the analyst use to isolate the compromised host in a grouped set of logs?
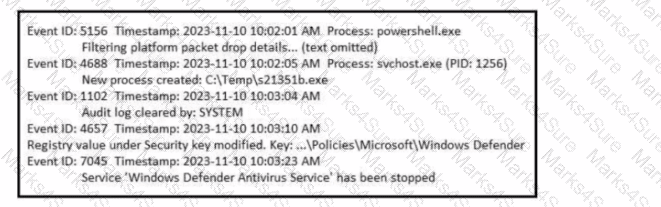
Refer to the exhibit.
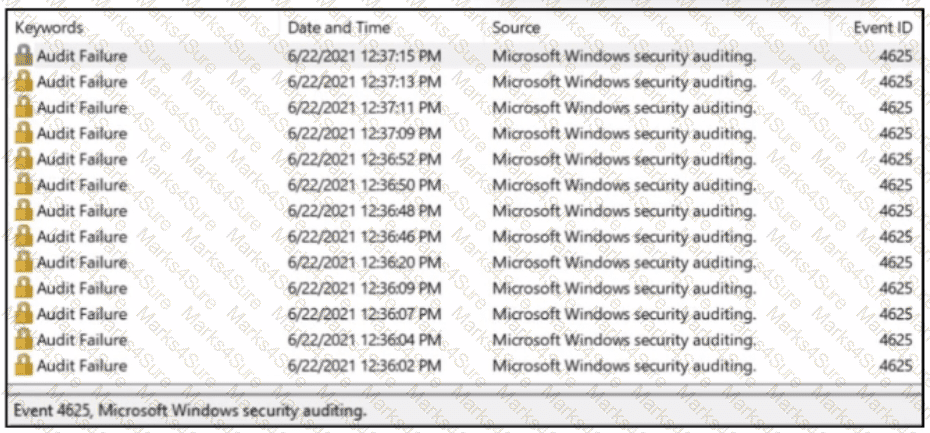
A SOC analyst received a message from SIEM about abnormal activity on the Windows server The analyst checked the Windows event log and saw numerous Audit Failures logs. What is occurring?
Refer to the exhibit.
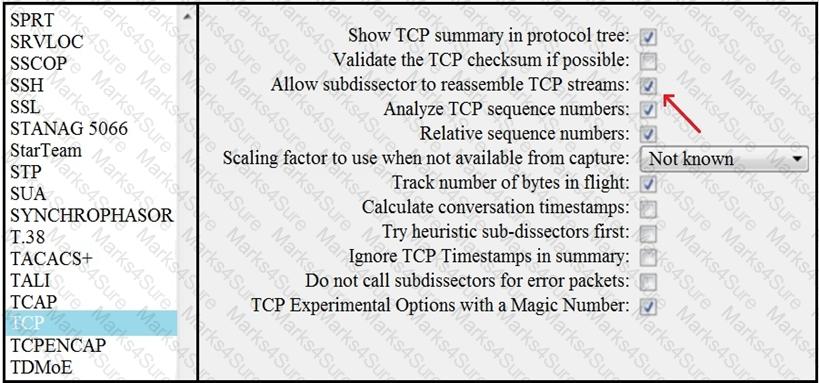
What is the expected result when the " Allow subdissector to reassemble TCP streams " feature is enabled?
What is the impact of false positive alerts on business compared to true positive?
Drag and drop the elements from the left into the correct order for incident handling on the right.

A security engineer notices confidential data being exfiltrated to a domain " Ranso4134-mware31-895 " address that is attributed to a known advanced persistent threat group The engineer discovers that the activity is part of a real attack and not a network misconfiguration. Which category does this event fall under as defined in the Cyber Kill Chain?
Refer to the exhibit.
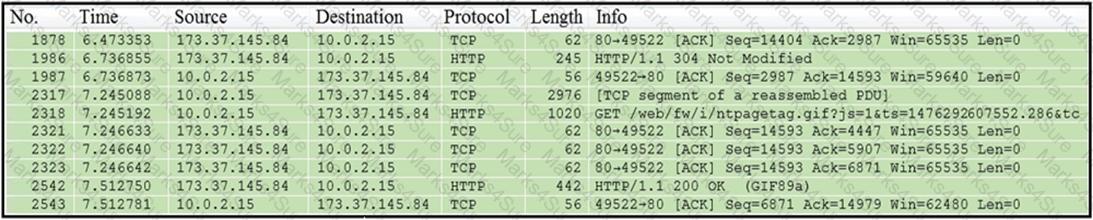
Which packet contains a file that is extractable within Wireshark?
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
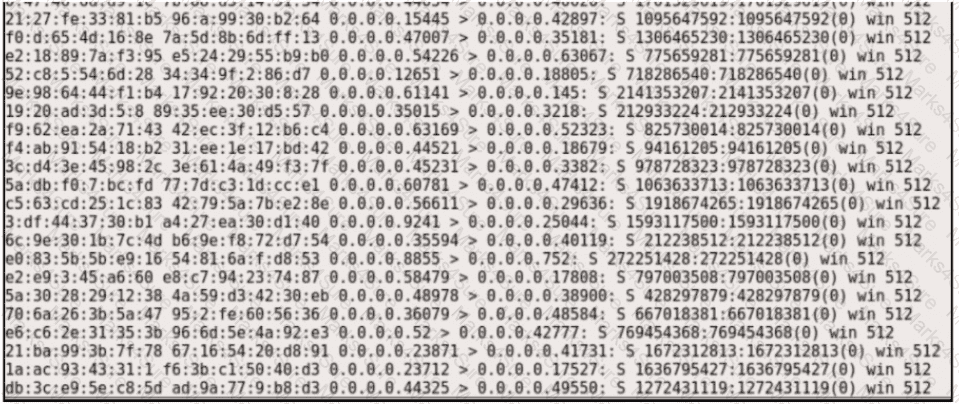
A user reports difficulties accessing certain external web pages. When an engineer examines traffic to and from the external domain in full packet captures, they notice that many SYNs have the same sequence number, source, and destination IP address, but they have different payloads. What is causing this situation?
Refer to the exhibit.
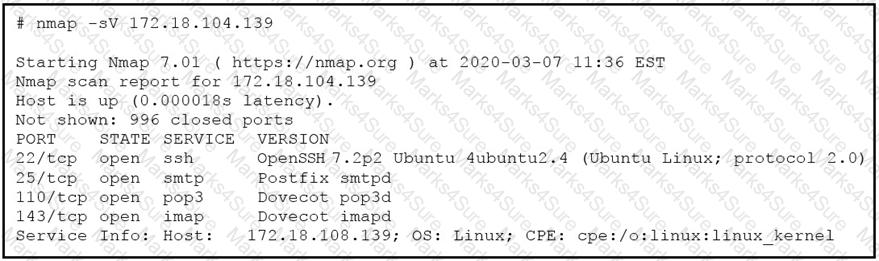
What does the output indicate about the server with the IP address 172.18.104.139?
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
An engineer must investigate suspicious connections. Data has been gathered using a tcpdump command on a Linux device and saved as sandboxmatware2022-12-22.pcaps file.The engineer is trying to open the tcpdump in the Wireshark tool. What is the expected result?
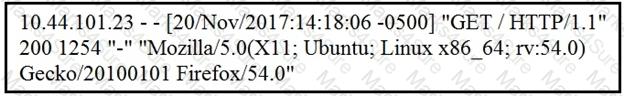
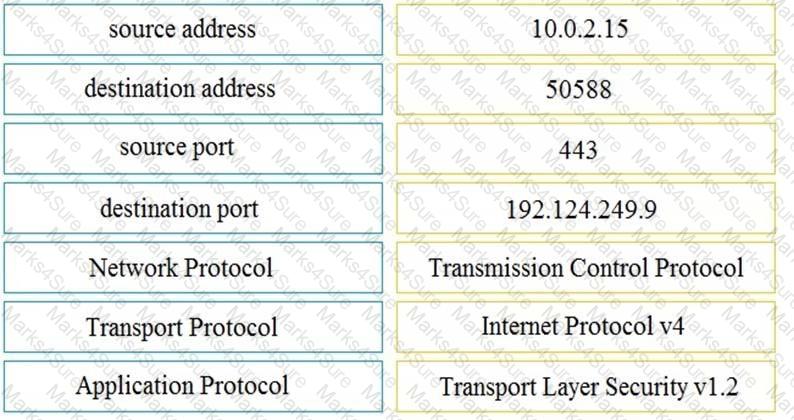
Refer to the exhibit.
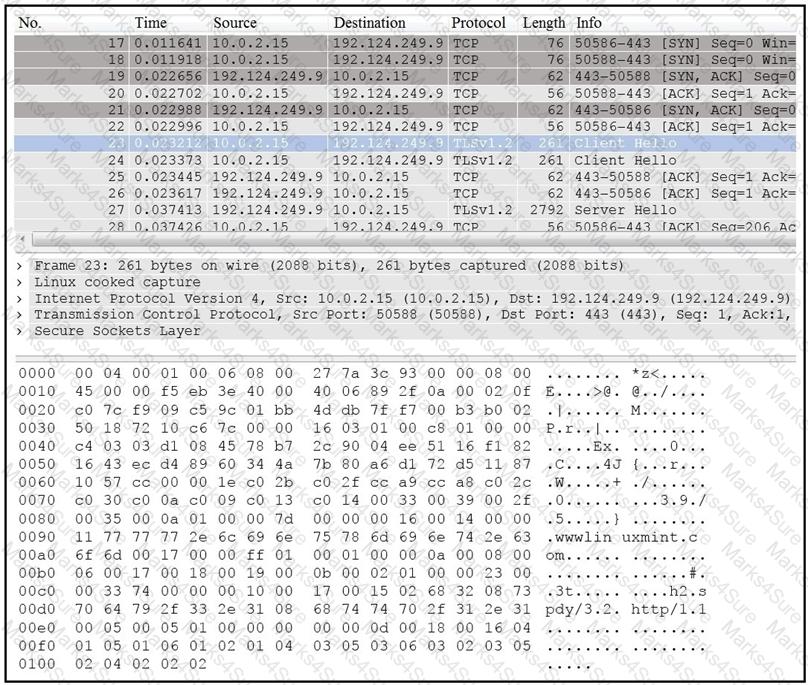
Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.
What specific type of analysis is assigning values to the scenario to see expected outcomes?
What causes events on a Windows system to show Event Code 4625 in the log messages?
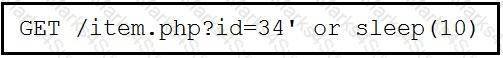
Refer to the exhibit.
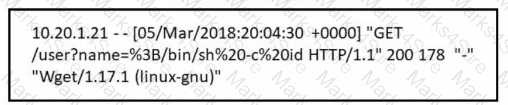
Which attack is being attempted against a web application?
Refer to the exhibit.
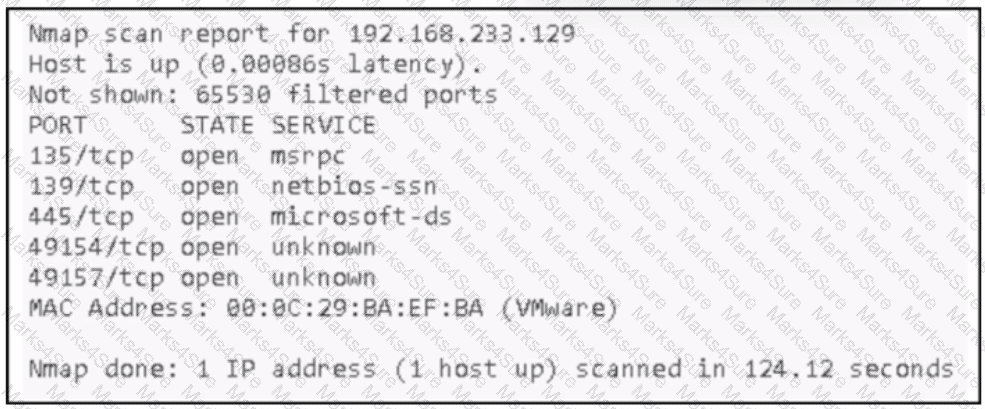
An attacker Infiltrated an organization ' s network and ran a scan to advance with the lateral movement technique. Which two elements from the scan assist the attacker? (Choose two.)
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
Which two pieces of information are collected from the IPv4 protocol header? (Choose two.)
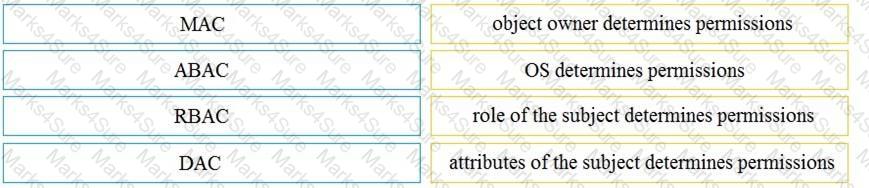
Drag and drop the access control models from the left onto the correct descriptions on the right.
A company receptionist received a threatening call referencing stealing assets and did not take any action assuming it was a social engineering attempt. Within 48 hours, multiple assets were breached, affecting the confidentiality of sensitive information. What is the threat actor in this incident?
A security analyst notices a sudden surge of incoming traffic and detects unknown packets from unknown senders After further investigation, the analyst learns that customers claim that they cannot access company servers According to NIST SP800-61, in which phase of the incident response process is the analyst?
A multinational organization uses a complex network infrastructure incorporating multiple cloud services, diverse endpoints, and distributed networks with several security devices. Which challenge will the security team face when ensuring robust data visibility for effective threat detection and response?
After a large influx of network traffic to externally facing devices, a security engineer begins investigating what appears to be a denial of service attack When the packet capture data is reviewed, the engineer notices that the traffic is a single SYN packet to each port Which type of attack is occurring?
Developers must implement tasks on remote Windows environments. They decided to use scripts for enterprise applications through PowerShell. Why does the functionality not work?
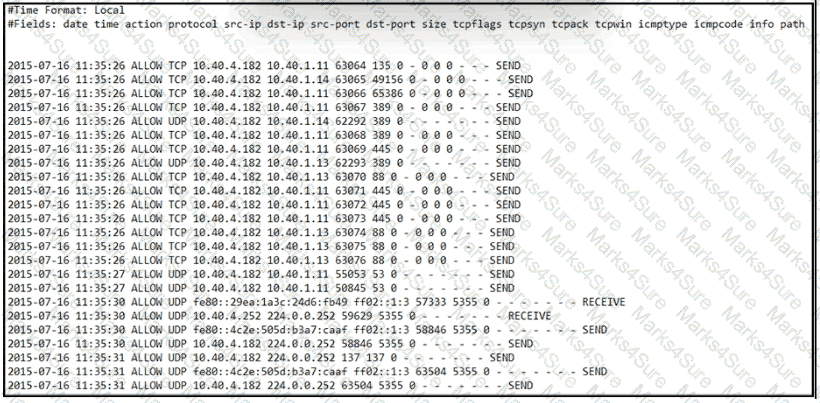
Refer to the exhibit.
During the analysis of a suspicious scanning activity incident, an analyst discovered multiple local TCP connection events Which technology provided these logs?
Refer to the exhibit.
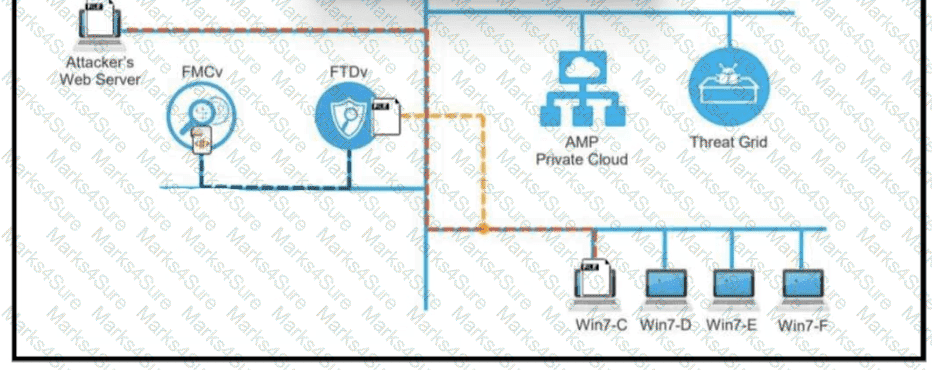
A workstation downloads a malicious docx file from the Internet and a copy is sent to FTDv. The FTDv sends the file hash to FMC and the tile event is recorded what would have occurred with stronger data visibility.
What is a difference between inline traffic interrogation and traffic mirroring?
Which information must an organization use to understand the threats currently targeting the organization?
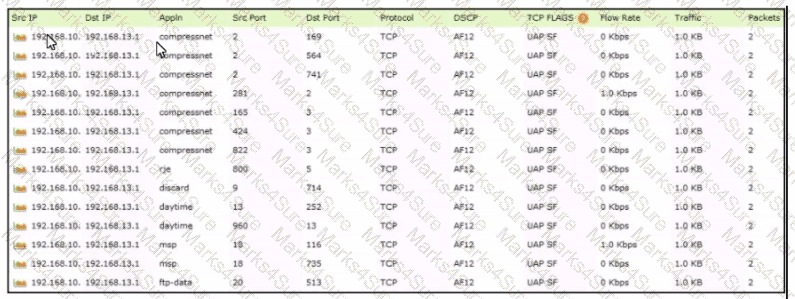
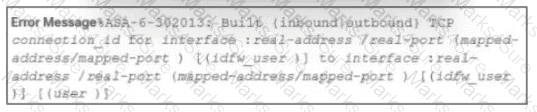
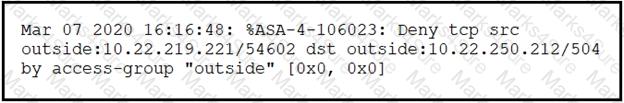
Refer to the exhibit.
An engineer received an event log file to review. Which technology generated the log?
An engineer is working on a ticket for an incident from the incident management team A week ago. an external web application was targeted by a DDoS attack Server resources were exhausted and after two hours it crashed. An engineer was able to identify the attacker and technique used Three hours after the attack, the server was restored and the engineer recommended implementing mitigation by Blackhole filtering and transferred the incident ticket back to the IR team According to NIST SP800-61, at which phase of the incident response did the engineer finish work?
A software development company develops high-end technology for the customer that will go through the HIPAA audit program. The technology will be hosted in the cloud, and the healthcare, employee names, and contact information will be stored on two separate logically isolated private cloud services. The patents and inventions will be hosted on a separate encrypted database. A compliance team is asked to analyze the cloud infrastructure and architecture to identify the protected data. Which two types of protected data should be identified? (Choose two.)
Syslog collecting software is installed on the server For the log containment, a disk with FAT type partition is used An engineer determined that log files are being corrupted when the 4 GB tile size is exceeded. Which action resolves the issue?
Which NIST IR category stakeholder is responsible for coordinating incident response among various business units, minimizing damage, and reporting to regulatory agencies?
An engineer needs to discover alive hosts within the 192.168.1.0/24 range without triggering intrusive portscan alerts on the IDS device using Nmap. Which command will accomplish this goal?
Refer to the exhibit. A SOC analyst is examining the Windows security logs of one of the endpoints. What is the possible reason for this event log?
According to the NIST SP 800-86. which two types of data are considered volatile? (Choose two.)
Refer to the exhibit.
This request was sent to a web application server driven by a database. Which type of web server attack is represented?
What are two differences in how tampered and untampered disk images affect a security incident? (Choose two.)
A security analyst received a ticket about suspicious traffic from one of the workstations. During the investigation, the analyst discovered that the workstation was communicating with an external IP. The analyst could not investigate further and escalated the case to a T2 security analyst. What are the two data visibility challenges that the security analyst should identify? (Choose two.)
What describes the impact of false-positive alerts compared to false-negative alerts?
Which type of attack involves sending input commands to a web server to access data?
A vulnerability analyst is performing the monthly scan data review Output data is very big and getting bigger each month The analyst decides to create a more efficient process to complete the task on time All false positives and true positives are excluded from the results The remaining findings will be assigned to a technical team for further remediation What is the result of such activity?
Refer to the exhibit.
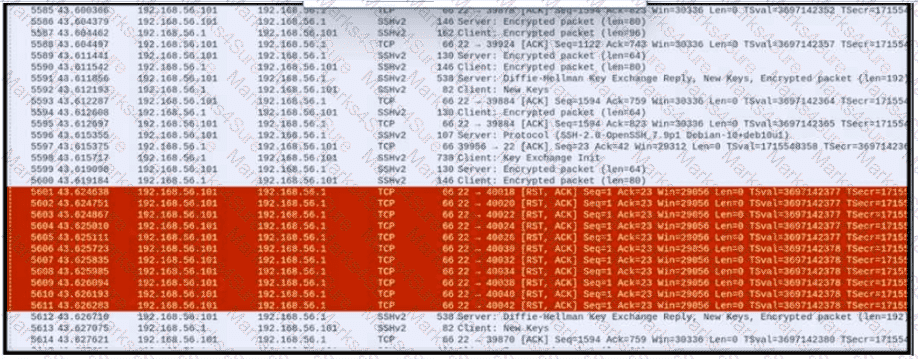
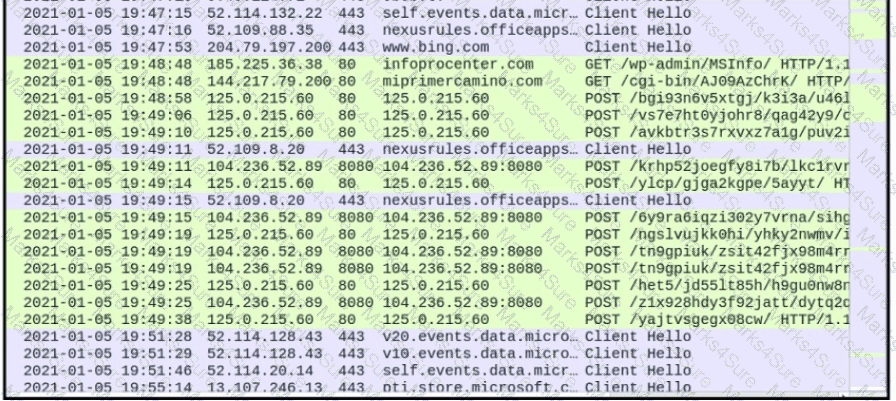
An engineer is analyzing a PCAP file after a recent breach An engineer identified that the attacker used an aggressive ARP scan to scan the hosts and found web and SSH servers. Further analysis showed several SSH Server Banner and Key Exchange Initiations. The engineer cannot see the exact data being transmitted over an encrypted channel and cannot identify how the attacker gained access How did the attacker gain access?
An employee received an email from a colleague’s address asking for the password for the domain controller. The employee noticed a missing letter within the sender’s address. What does this incident describe?
An analyst received a ticket regarding a degraded processing capability for one of the HR department ' s servers. On the same day, an engineer noticed a disabled antivirus software and was not able to determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
An engineer is working with the compliance teams to identify the data passing through the network. During analysis, the engineer informs the compliance team that external penmeter data flows contain records, writings, and artwork Internal segregated network flows contain the customer choices by gender, addresses, and product preferences by age. The engineer must identify protected data. Which two types of data must be identified ' ? (Choose two.)
A suspicious user opened a connection from a compromised host inside an organization. Traffic was going through a router and the network administrator was able to identify this flow. The admin was following 5-tuple to collect needed data. Which information was gathered based on this approach?
What is a difference between rule-based and role-based access control mechanisms?
What is the difference between statistical detection and rule-based detection models?

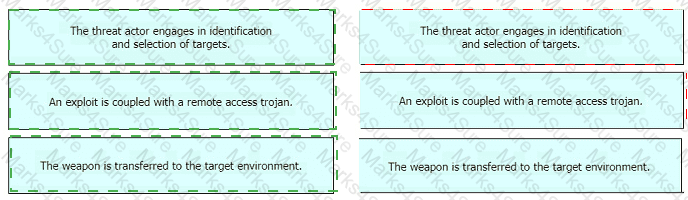
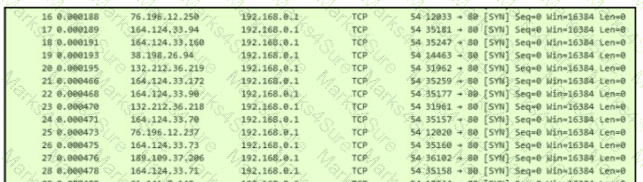
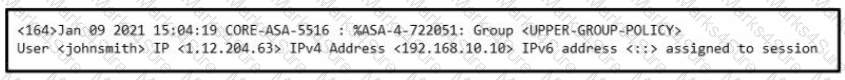
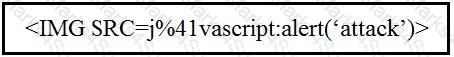

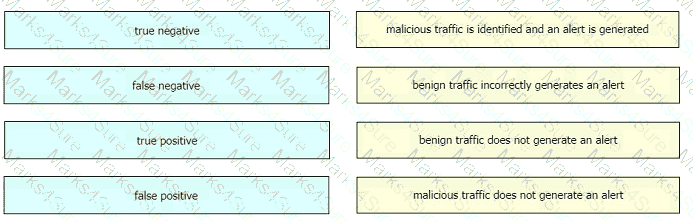
 Table Description automatically generated
Table Description automatically generated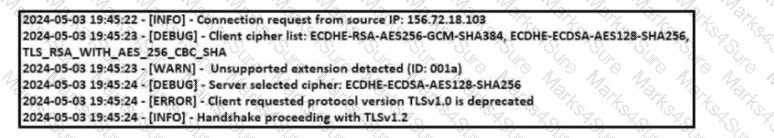
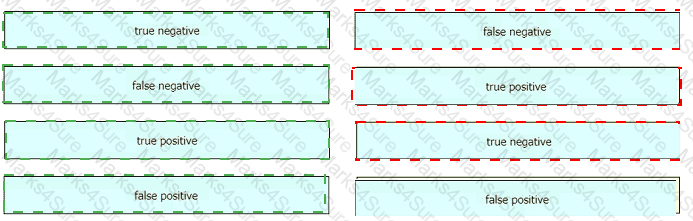
 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated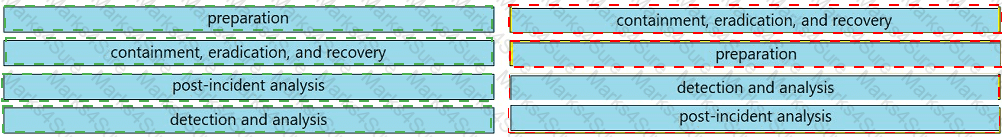
 A close-up of several blue rectangular boxes Description automatically generated
A close-up of several blue rectangular boxes Description automatically generated