A user cannot upload files to corporate servers from their mobile device when outside the office, but uploads work fine in-office. What should a technician do to determine the root cause?
Which of the following describes an attack in which an attacker sets up a rogue AP that tricks users into connecting to the rogue AP instead of the legitimate network?
Which of the following file types allows macOS users to uninstall software completely by placing the file in the trash?
Which of the following filesystems supports read and write operations for Windows, macOS, and Linux?
A town clerk wants to work from home and access documents on a town hall server. What should a technician set up?
What is the next step a technician should take after completing malware cleanup?
After completing malware removal steps, what is the next step the technician should take?
Which of the following methods would make data unrecoverable but allow the drive to be repurposed?
A user is experiencing issues with outdated images while browsing websites. Which of the following settings should a technician use to correct this issue?
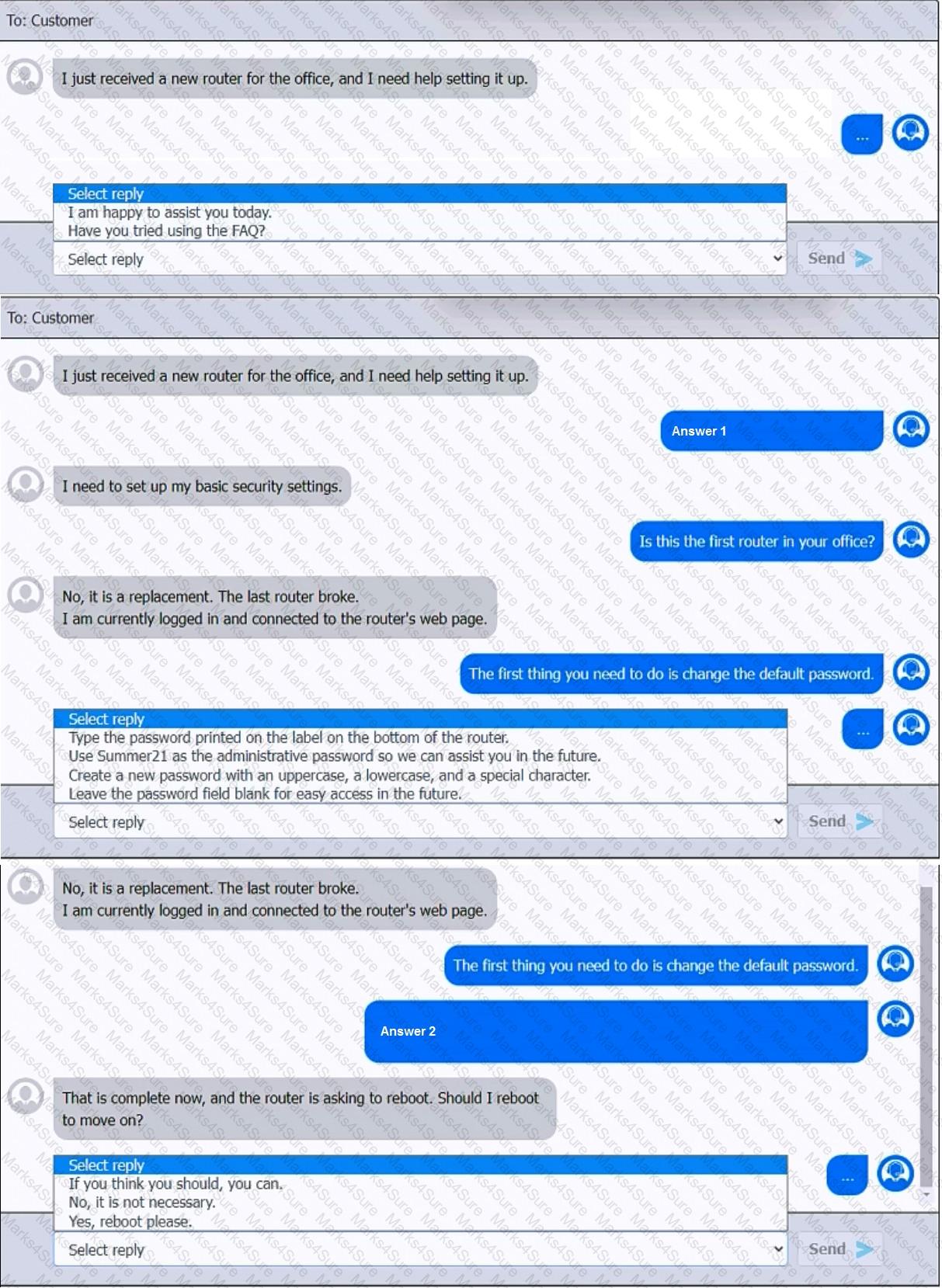
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
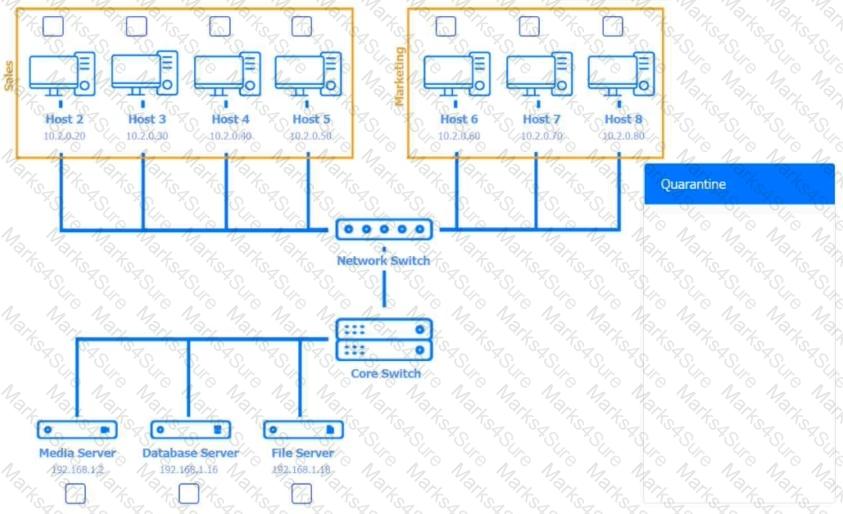
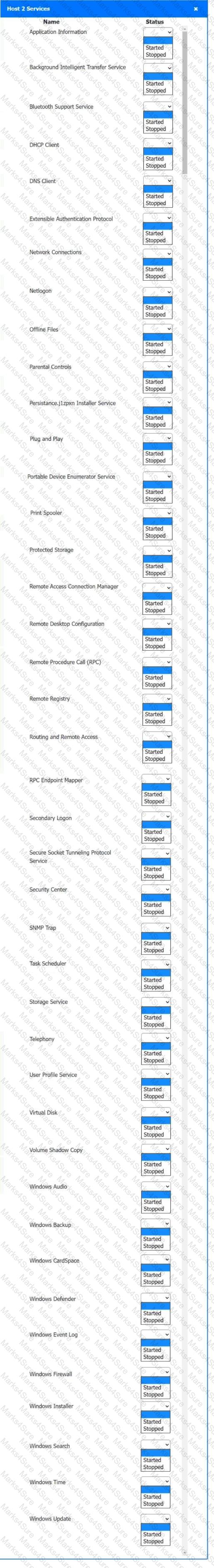
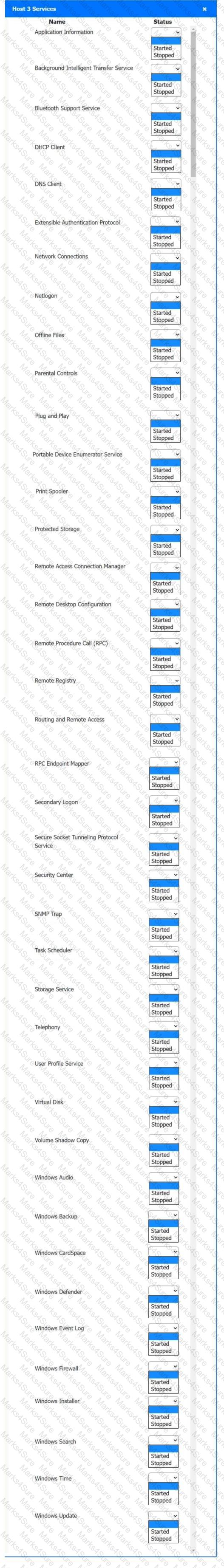
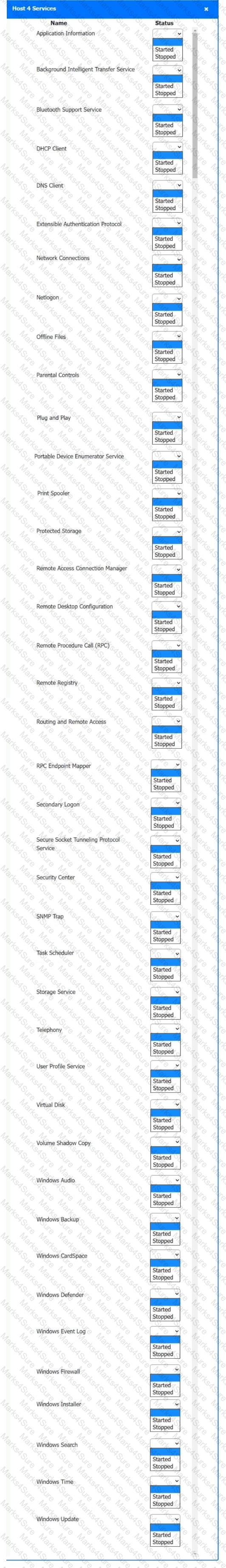
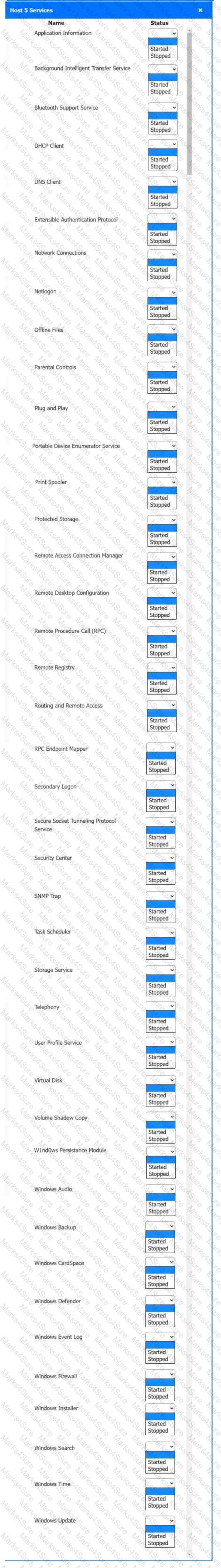
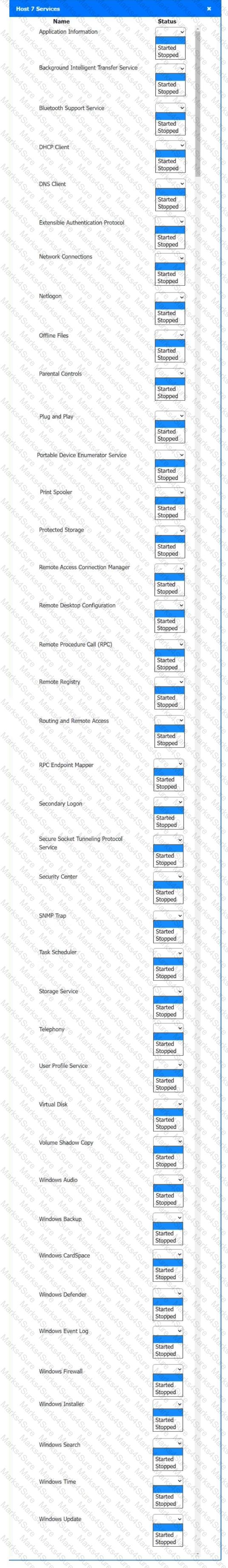
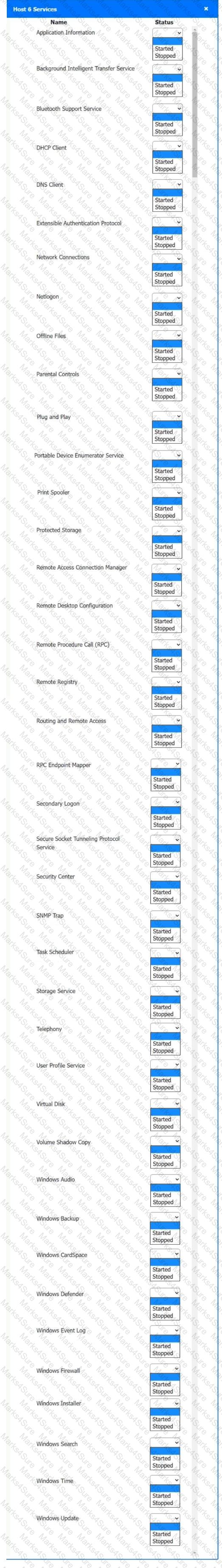
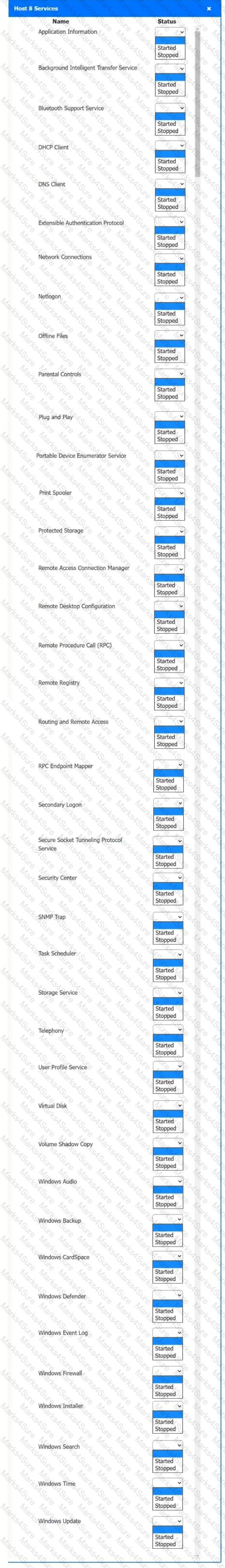
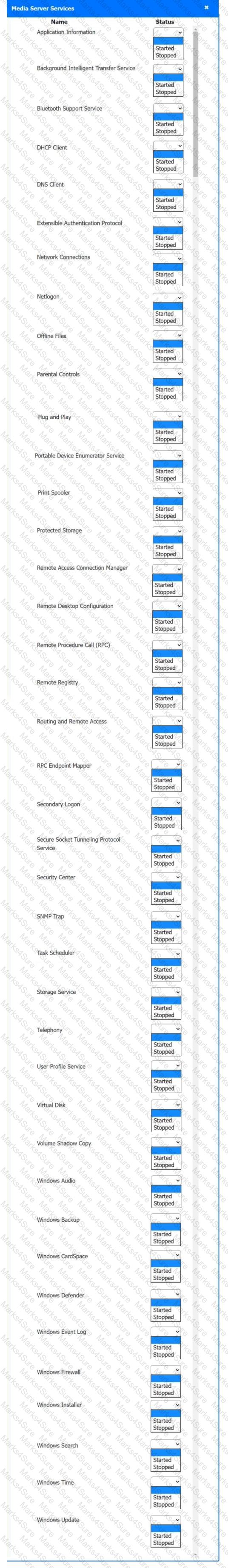
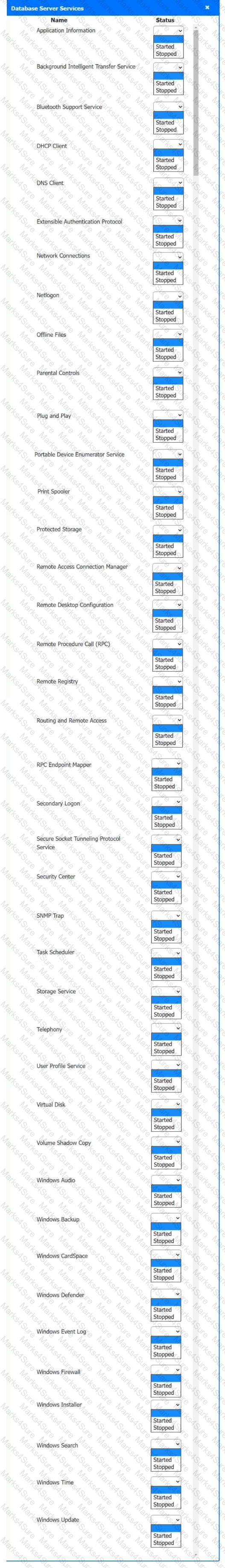
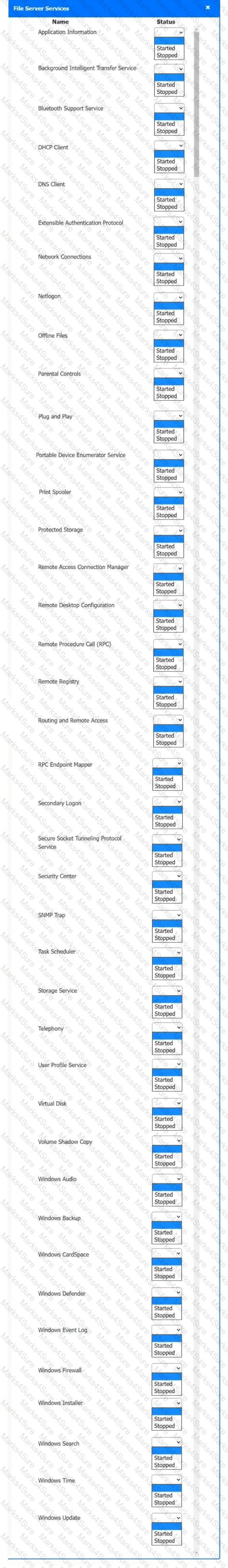
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
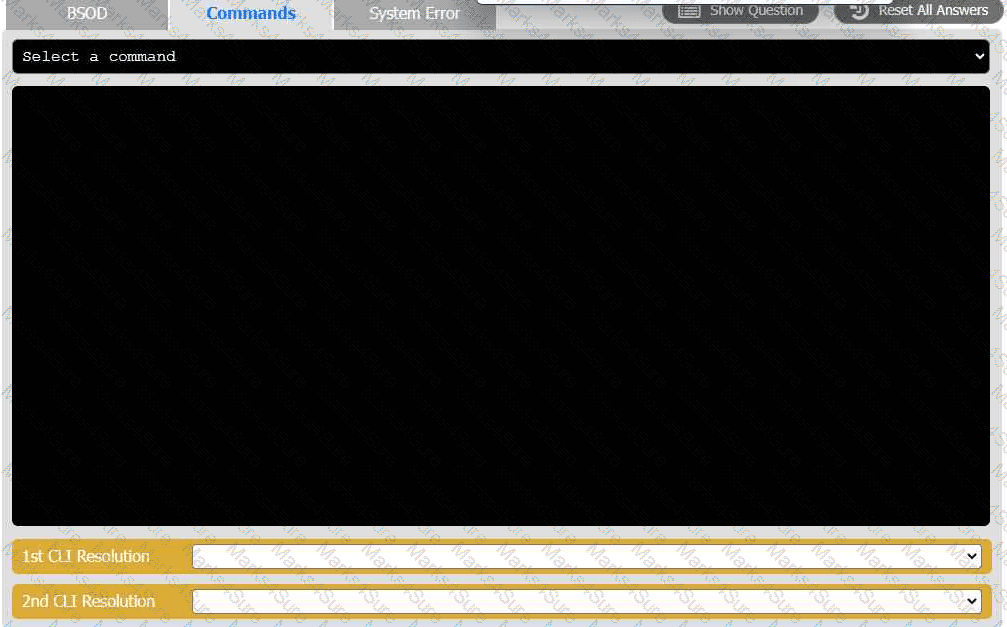
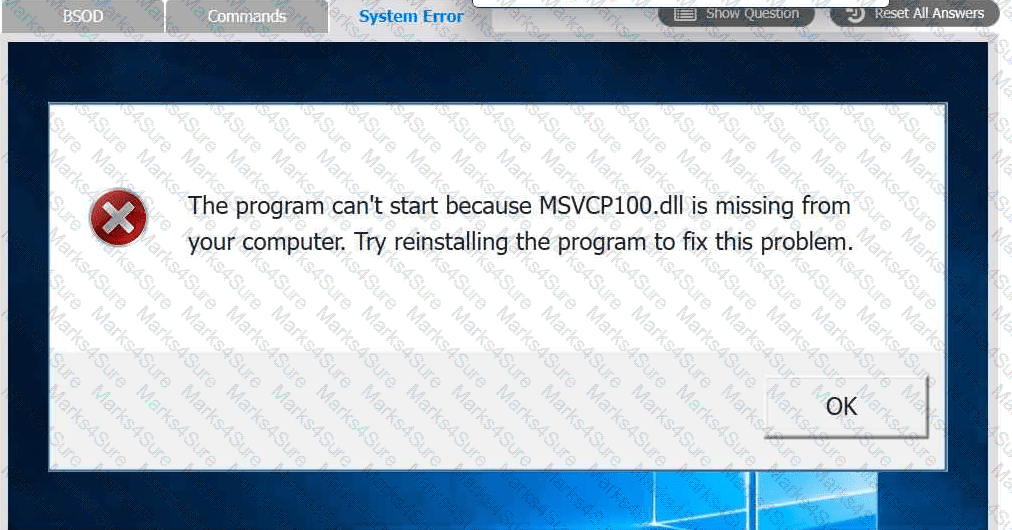
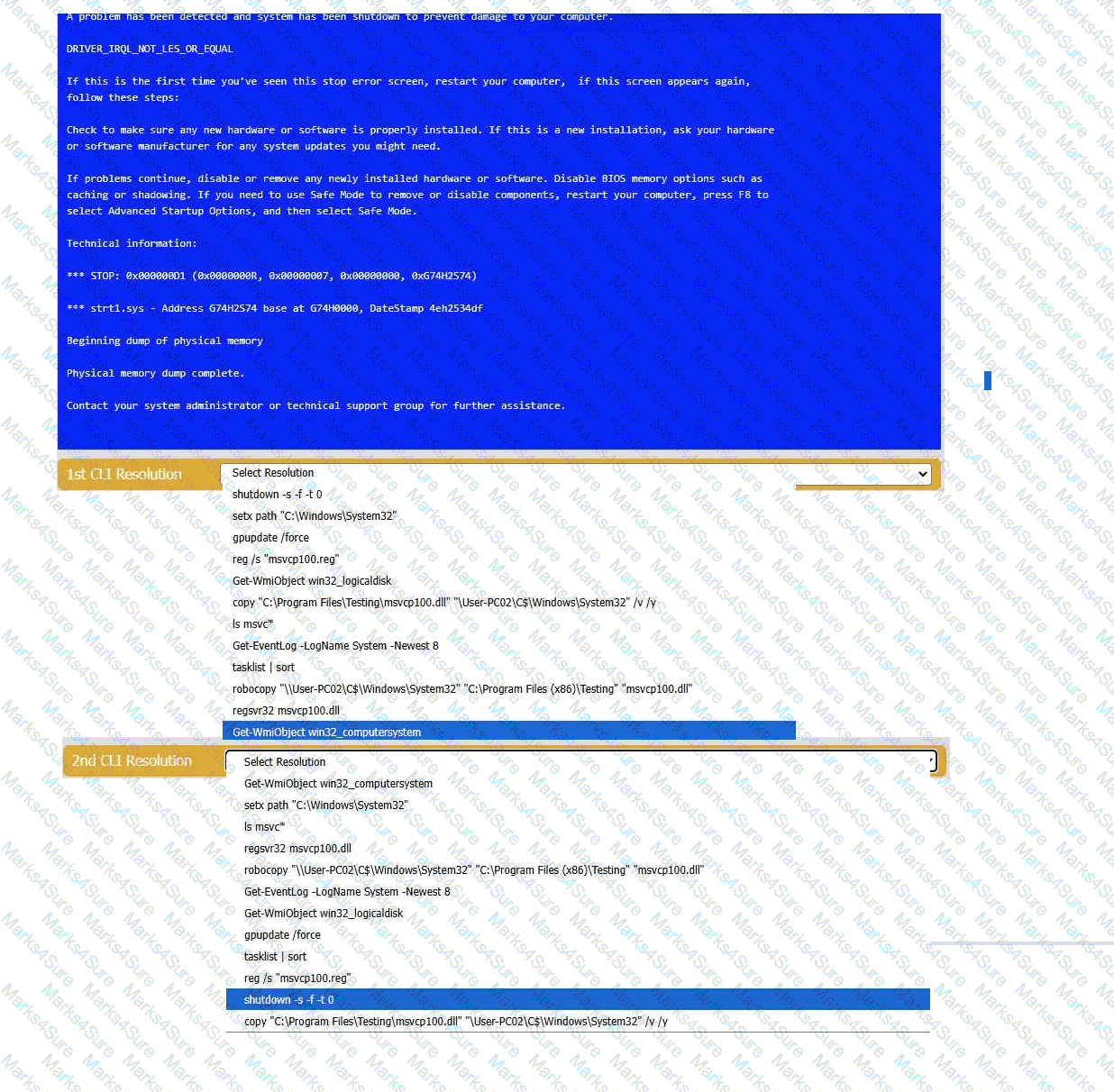
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
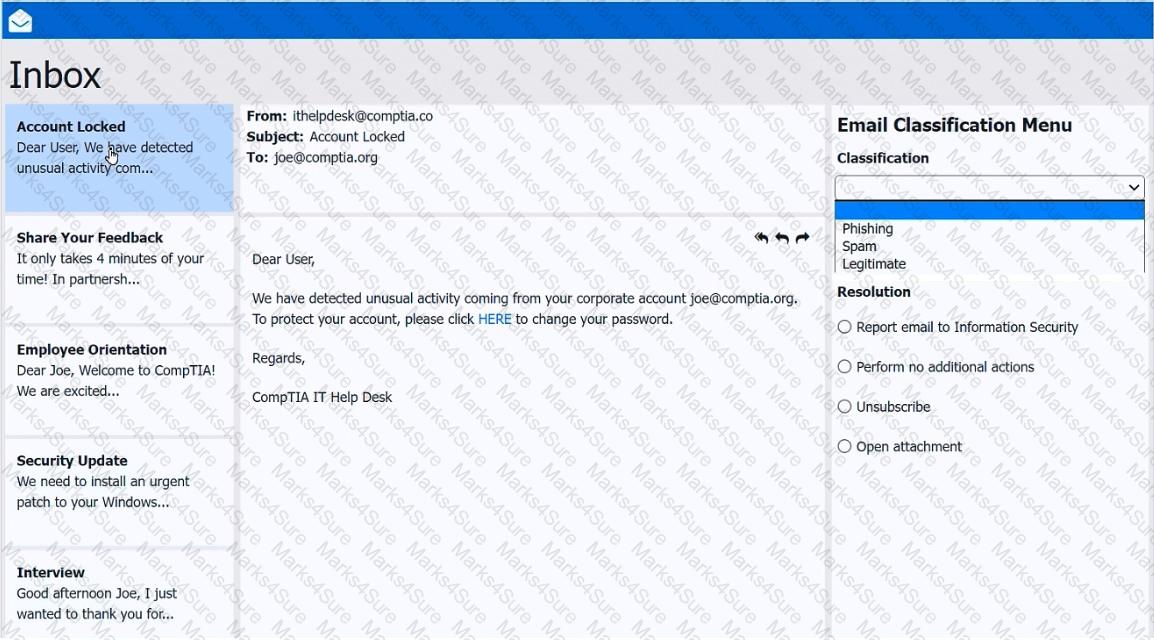
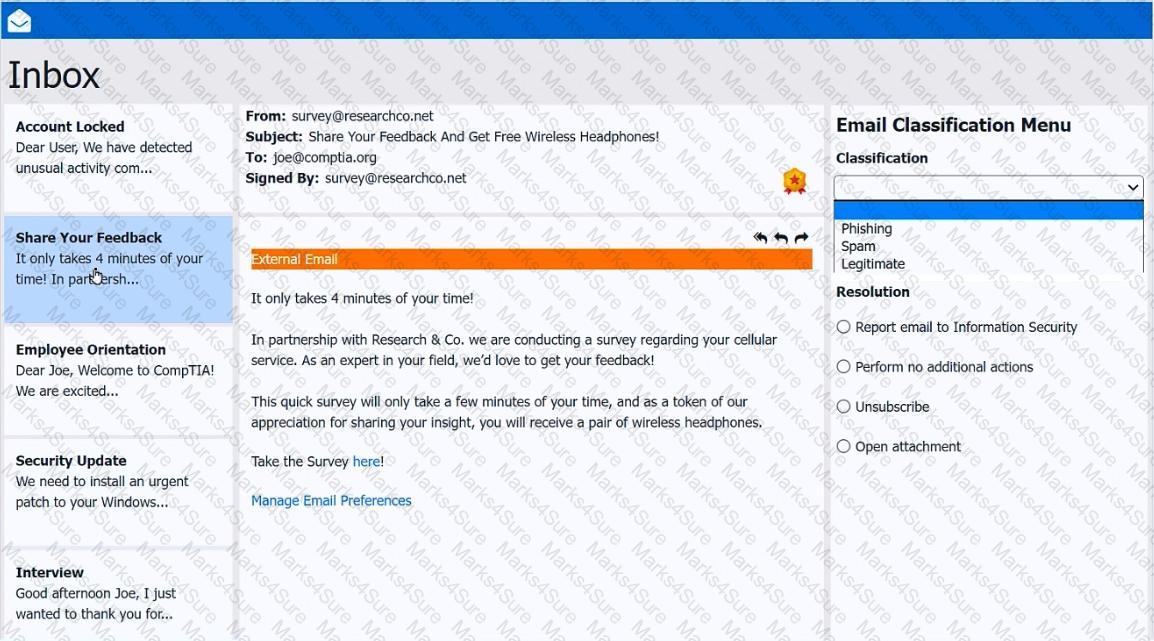
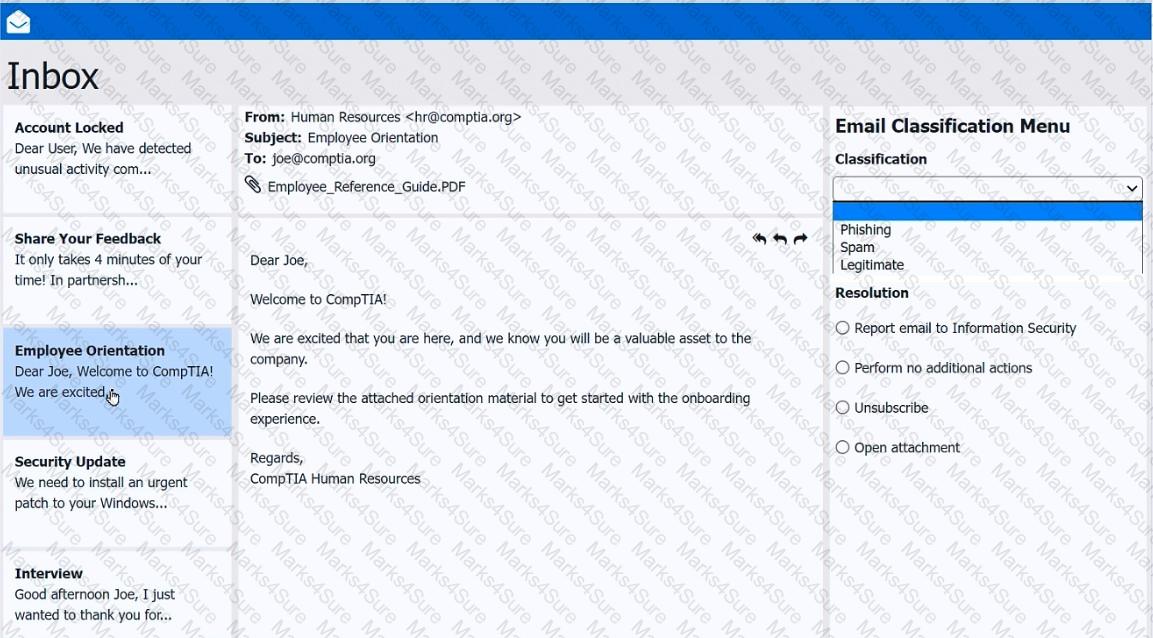
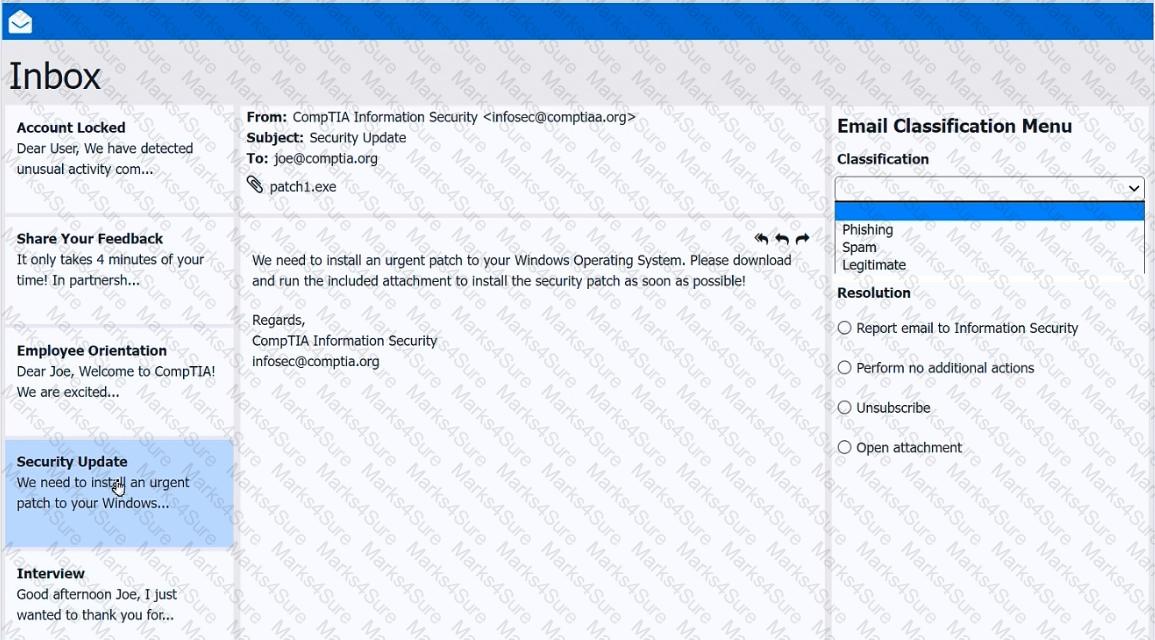
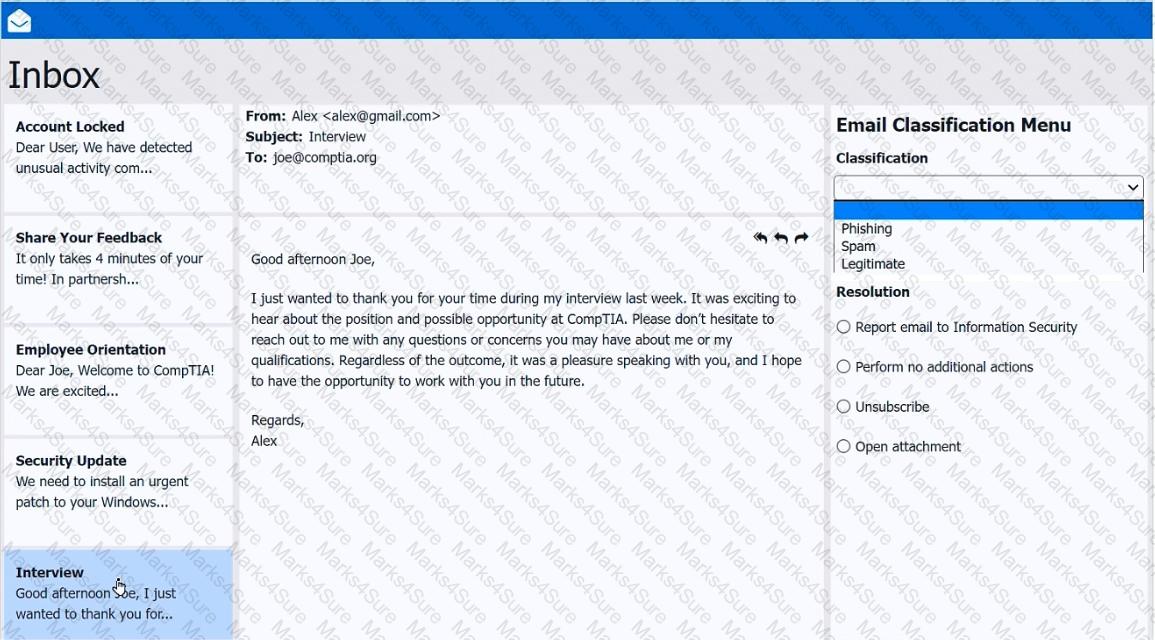
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
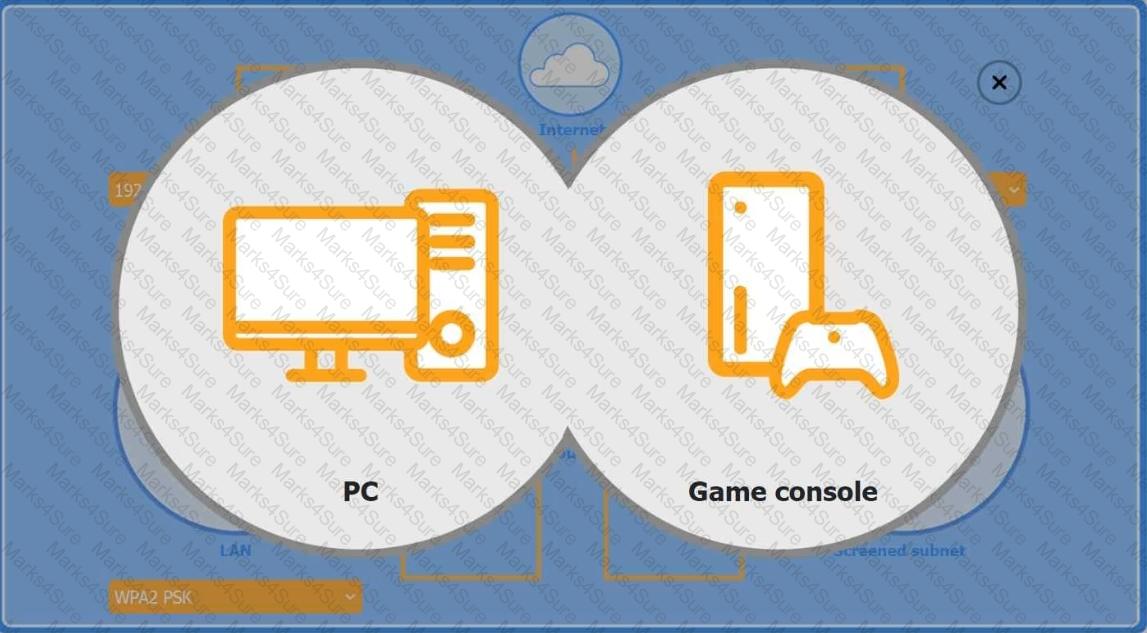
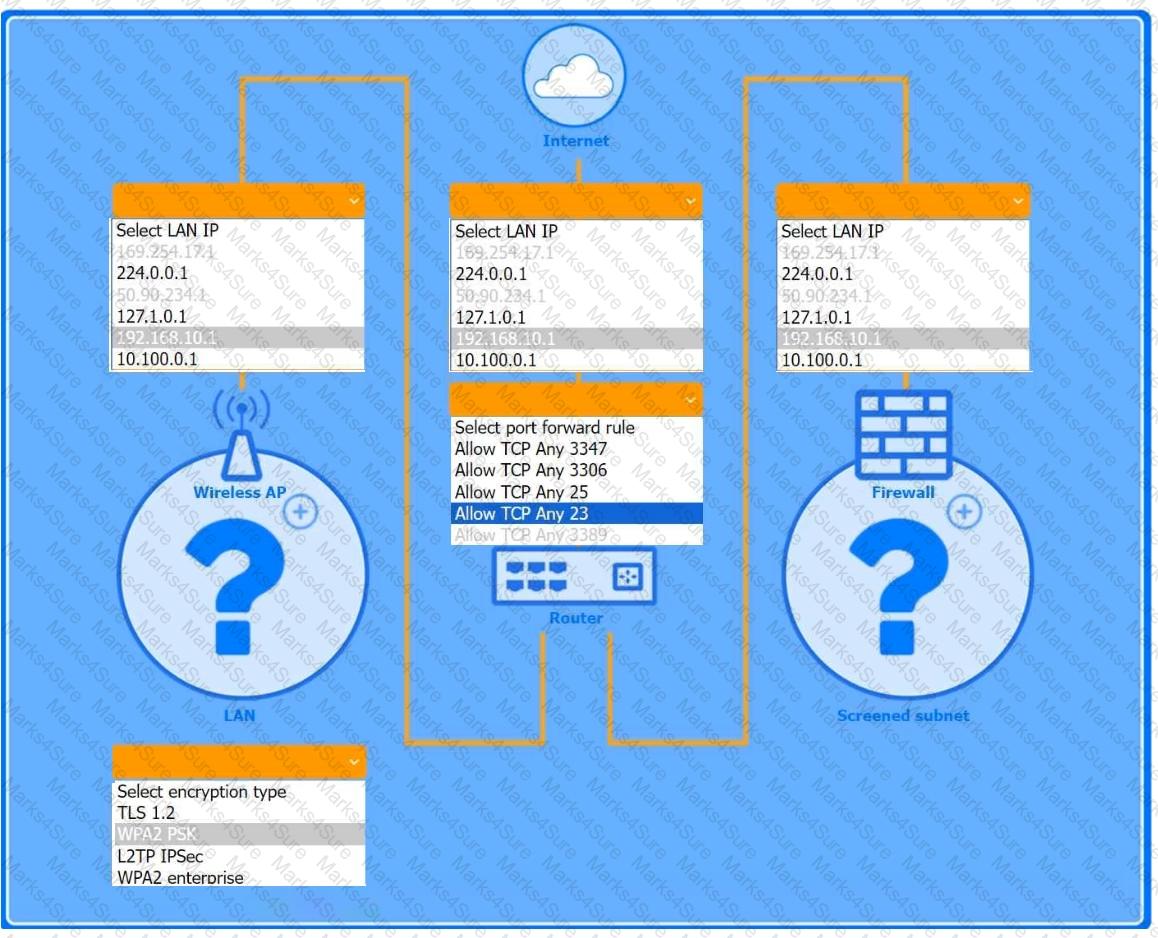
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
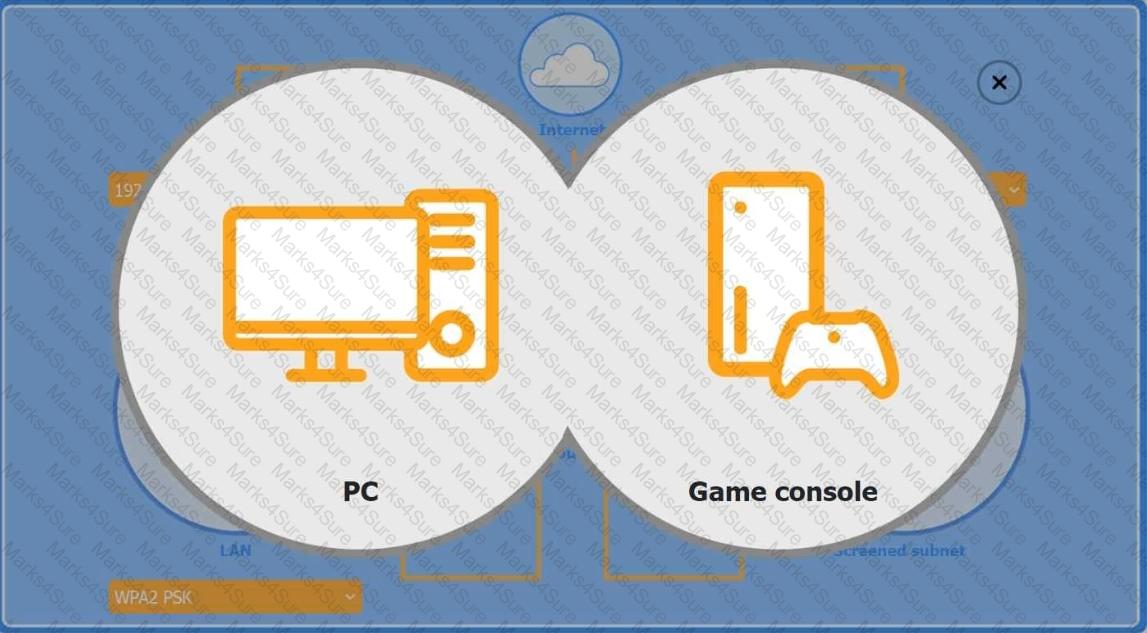
Firewall Screened Subnet
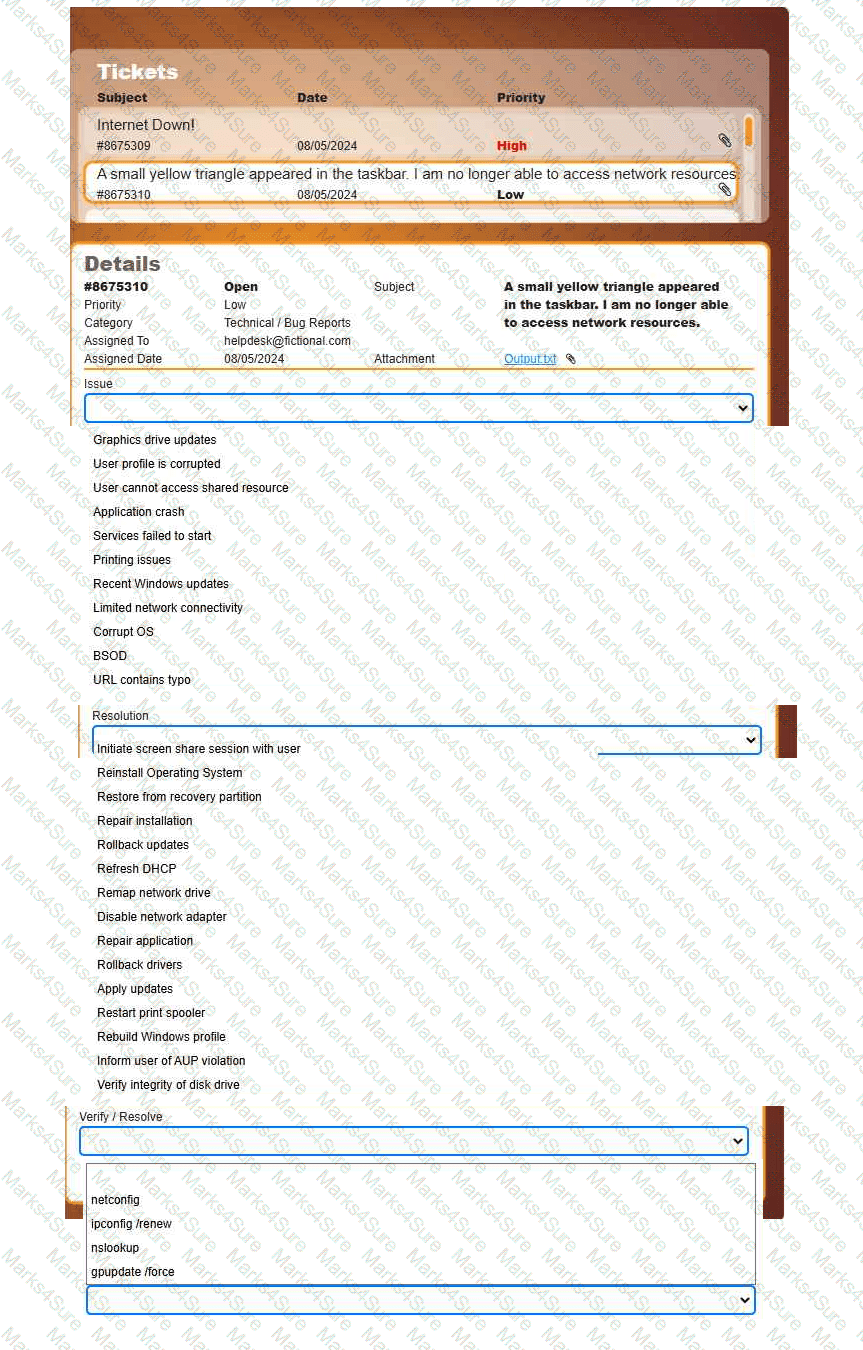
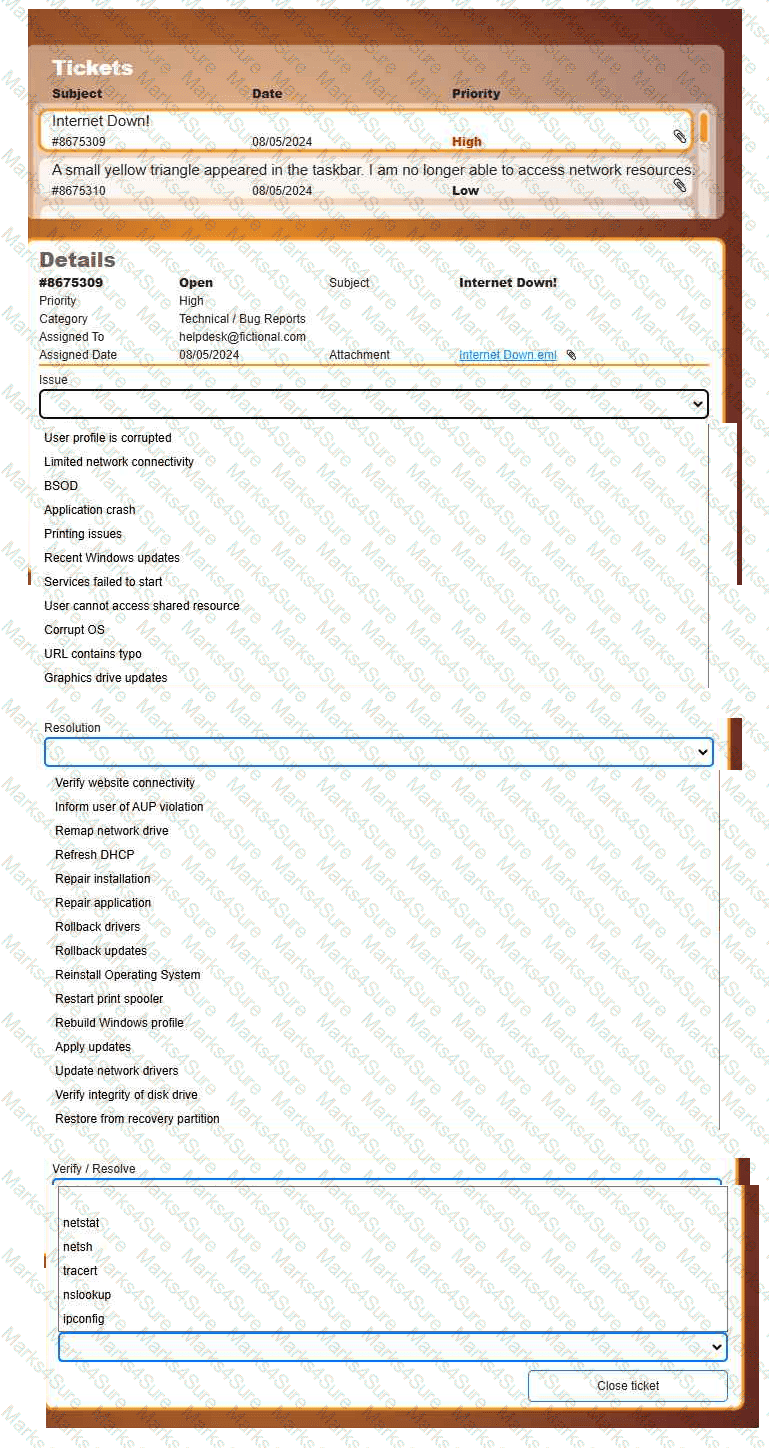
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
A user takes an iOS-based smartphone that is performing slowly to a repair shop. A shop technician finds the following information:
Battery charge: 25%
Battery health: 90%
Hot-spot: On
Mobile reception: |||
Roaming: Off
Used space: 63.76GB/64GB
Which of the following is the cause of the issue?
A technician notices that the weekly backup is taking too long to complete. The daily backups are incremental. Which of the following would most likely resolve the issue?
A technician follows proper malware removal procedures but cannot remove all malware. They decide to reload the OS. What should they select?
A user logs in to a computer each morning and tries to print a daily report, but it will not print. The help desk resolves the issue each day temporarily. To fix this permanently, which of the following should the technician do? (Select two)
A company would like to deploy baseline images to new computers as they are started up on the network. Which of the following boot processes should the company use for this task?
A user wants to connect a retro gaming console to the internet so that they can participate in online gaming. In order for the console to work, the Wi-Fi connection must adhere to a WPA-protected broadcast. Which of the following is the best option for the user to implement?
Which of the following types of social engineering attacks sends an unsolicited text message to a user ' s mobile device?
A client reports that their browser ' s home page changed. Every time they run an internet search, the results are returned from unfamiliar websites. Which of the following actions should a technician take first to resolve the issue? (Select two)
A company computer is being repurposed within an organization. The existing configuration has a static IP address, but it is no longer required. Which of the following should a technician do to satisfy the network requirements?
A user ' s application only works with a legacy version of the OS. The OS is reaching its end-of-life date. For security reasons, the company is migrating to the current version of the OS. Which of the following is the most efficient way to complete the migration while maintaining accessibility to the application?
A user receives a new personal computer but is unable to run an application. An error displays saying that .NET Framework 3.5 is required and not found. Which of the following actions is the best way to resolve this issue?
A company wants to perform an in-place upgrade of operating systems on all workstations. All types of removable storage are disabled for security reasons. Which of the following is the best way to upgrade while keeping security settings in place?
Which of the following must be followed during incident response to ensure the collected evidence is properly handled and accounted for?
A technician is troubleshooting a print spooler that fails to start on a Windows 11 desktop computer. The technician determines the root cause is that required dependencies are failing to run. Which of the following tools is the technician using?
Which of the following is the quickest way to move from Windows 10 to Windows 11 without losing data?