Which product is able to replace a confidential document residing on a file share with a marker file explaining why the document was removed?
Which server target uses the “Automated Incident Remediation Tracking” feature in Symantec DLP?
Which two automated response rules will be active in policies that include Exact Data Matching (EDM) detection rule? (Choose two.)
Which two actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
Where in the Enforce management console can a DLP administrator change the “UI.NO_SCAN.int” setting to disable the “Inspecting data” pop-up?
Under the “System Overview” in the Enforce management console, the status of a Network Monitor detection server is shown as “Running Selected.” The Network Monitor server’s event logs indicate that the packet capture and filereader processes are crashing.
What is a possible cause for the Network Monitor server being in this state?
Which option correctly describes the two-tier installation type for Symantec DLP?
What is the default fallback option for the Endpoint Prevent Encrypt response rule?
An administrator is unable to log in to the Enforce management console as “sysadmin”. Symantec DLP is configured to use Active Directory authentication. The administrator is a member of two roles: “sysadmin” and “remediator.”
How should the administrator log in to the Enforce console with the “sysadmin” role?
Refer to the exhibit.
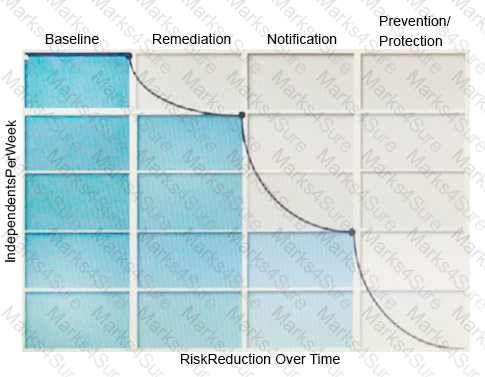
What activity should occur during the baseline phase, according to the risk reduction model?
Which service encrypts the message when using a Modify SMTP Message response rule?
A company needs to secure the content of all mergers and Acquisitions Agreements/ However, the standard text included in all company literature needs to be excluded.
How should the company ensure that this standard text is excluded from detection?
Which two components can perform a file system scan of a workstation? (Choose two.)