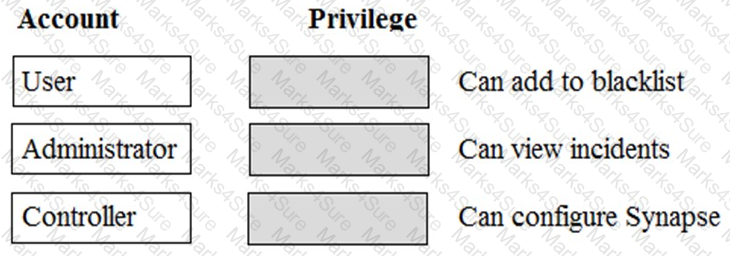
Which level of privilege corresponds to each ATP account type?
Match the correct account type to the corresponding privileges.
Which two widgets can an Incident Responder use to isolate breached endpoints from the Incident details
page? (Choose two.)
Why is it important for an Incident Responder to copy malicious files to the ATP file store or create an image of the infected system during the Recovery phase?
Which attribute is required when configuring the Symantec Endpoint Protection Manager (SEPM) Log
Collector?
An Incident Responder has noticed that for the last month, the same endpoints have been involved with malicious traffic every few days. The network team also identified a large amount of bandwidth being used over P2P protocol.
Which two steps should the Incident Responder take to restrict the endpoints while maintaining normal use of the systems? (Choose two.)
An Incident Responder has reviewed a STIX report and now wants to ensure that their systems have NOT been compromised by any of the reported threats.
Which two objects in the STIX report will ATP search against? (Choose two.)
Which Advanced Threat Protection (ATP) component best isolates an infected computer from the network?
An ATP Administrator set up ATP: Network in TAP mode and has placed URLs on the blacklist.
What will happen when a user attempts to access one of the blacklisted URLs?
During a recent virus outlook, an Incident found that the incident Response team was successful in identifying malicious that were communicating with the infected endpoint.
Which two (2) options should be incident Responder select to prevent endpoints from communicating with malicious domains?
An organization recently deployed ATP and integrated it with the existing SEP environment. During an outbreak, the Incident Response team used ATP to isolate several infected endpoints. However, one of the endpoints could NOT be isolated.
Which SEP protection technology is required in order to use the Isolate and Rejoin features in ATP?
Malware is currently spreading through an organization’s network. An Incident Responder sees some
detections in SEP, but there is NOT an apparent relationship between them.
How should the responder look for the source of the infection using ATP?
An Incident Responder observers and incident with multiple malware downloads from a malicious domain. The domain in question belongs to one of the organization suppliers. The organization to the site to continue placing orders. Network is configured in Inline Block mode?
How should the Incident responder proceed?
An Incident Responder wants to investigate whether msscrt.pdf resides on any systems.
Which search query and type should the responder run?
Which two tasks should an Incident Responder complete when recovering from an incident? (Choose two.)
An Incident Responder wants to run a database search that will list all client named starting with SYM.
Which syntax should the responder use?
Which two actions an Incident Responder take when downloading files from the ATP file store? (Choose two.)
What is the main constraint an ATP Administrator should consider when choosing a network scanner model?
An Incident Responder needs to remediate a group of endpoints but also wants to copy a potentially suspicious file to the ATP file store.
In which scenario should the Incident Responder copy a suspicious file to the ATP file store?
What impact does changing from Inline Block to SPAN/TAP mode have on blacklisting in ATP?
Which final steps should an Incident Responder take before using ATP to rejoin a remediated endpoint to the network, according to Symantec best practices?
Which two user roles allow an Incident Responder to blacklist or whitelist files using the ATP manager?
(Choose two.)
A large company has 150,000 endpoints with 12 SEP sites across the globe. The company now wants to
implement ATP: Endpoint to improve their security. However, a consultant recently explained that the company needs to implement more than one ATP manager.
Why does the company need more than one ATP manager?