Where in the Enforce management console can a DLP administrator change the “UI.NO_SCAN.int” setting to disable the “Inspecting data” pop-up?
Which two (2) actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
How should a DLP administrator exclude a custom endpoint application named “custom_app.exe” from being monitored by Application File Access Control?
Which option correctly describes the two-tier installation type for Symantec DLP?
Which tool must a DLP administrator run to certify the database prior to upgrading DLP?
Which two DLP products support the new Optical Character Recognition (OCR) engine in Symantec DLP 15.0? (Choose two.)
Which two automated response rules will be active in policies that include Exact Data Matching (EDM) detection rule? (Choose two.)
Which of the following would have to be a custom attribute (and not an out-of -the-box system attribute) in incident snapshots?
Which two factors are common sources of data leakage where the main actor is well-meaning insider? (Choose two.)
An administrator is unable to log in to the Enforce management console as “sysadmin”. Symantec DLP is configured to use Active Directory authentication. The administrator is a member of two roles: “sysadmin” and “remediator.”
How should the administrator log in to the Enforce console with the “sysadmin” role?
What detection server is used for Network Discover, Network Protect, and Cloud Storage?
A DLP administrator has performed a test deployment of the DLP 15.0 Endpoint agent and now wants to uninstall the agent. However, the administrator no longer remembers the uninstall password.
What should the administrator do to work around the password problem?
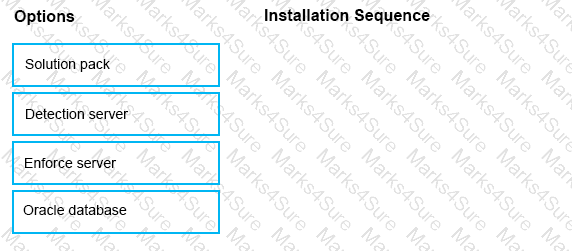
What is the correct installation sequence for the components shown here, according to the Symantec Installation Guide?
Place the options in the correct installation sequence.
Which two locations can Symantec DLP scan and perform Information Centric Encryption (ICE) actions on? (Choose two.)
Which product is able to replace a confidential document residing on a file share with a marker file explaining why the document was removed?
Which statement accurately describes where Optical Character Recognition (OCR) On-Premises DLP Core components must be installed?
An organization wants to restrict employees to copy files only a specific set of USB thumb drives owned by the organization.
Which detection method should the organization use to meet this requirement?
A DLP administrator needs to remove an agent its associated events from an Endpoint server.
Which Agent Task should the administrator perform to disable the agent’s visibility in the Enforce management console?
What is the correct order for data in motion when a customer has integrated their CloudSOC and DLP solutions?
Which two Infrastructure-as-a-Service providers are supported for hosting Cloud Prevent for Office 365? (Choose two.)