How many items can be displayed in a single watched list in a Profiler Dashboard Content Block?
Which of the following capabilities are supported by the Cascade Sensor appliance but are not supported by the Cascade Sensor-VE RSP packagE. (Select 2)
A system administrator needs to update their Cascade Profiler host group settings to remove references to a decommissioned office on the 10.63.32.0/24 subnet.
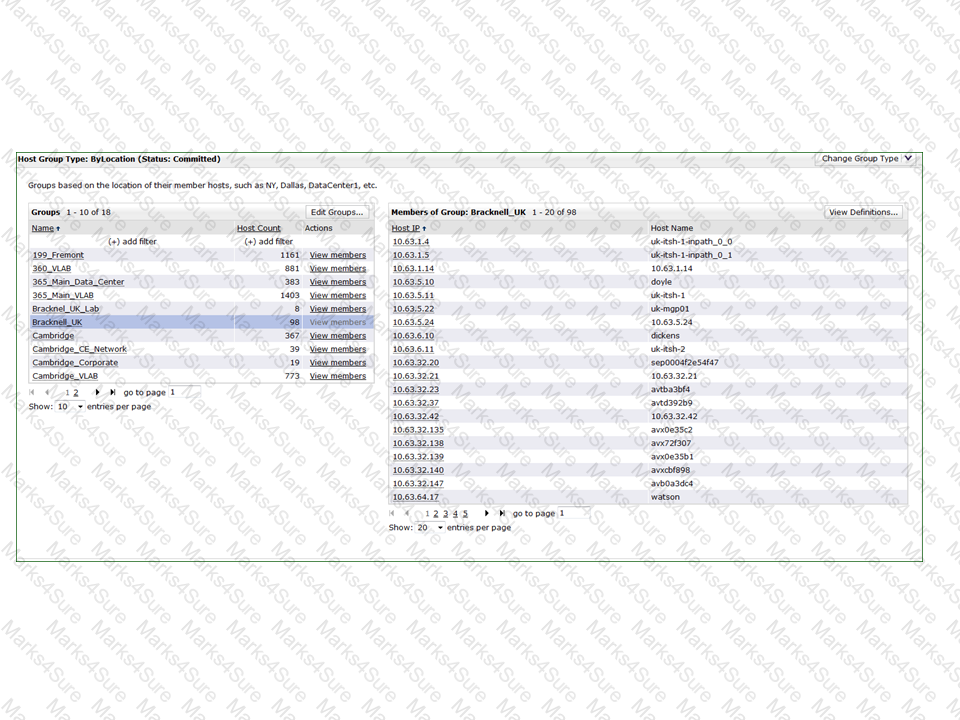
What is the best way to do this?
What integrations are available when an enterprise already owns an SNMP monitoring technology (such as Solarwinds or HPOV)? (Select 2)
If a prospective customer has 2000 users what would be a reasonable estimated number of flows per minute used in sizing Profiler?
When defining a service which of the following are supported ways of aggregating the results? (Select 2)
On Cascade Profiler, in terms of retention of completed reports and reporting sources (one minute flow and rollup files), which of the following is true? (Select 4)
When changing the priority for a Layer 4 mapping on Cascade Profiler best practices indicate that Application Mappings should be given higher priorities based on:
What are the two (at a minimum) devices you need to configure in Cascade Profiler for Switch Port Discovery integration to work for a portion of the network?
In this scenario, you have created a host group called My_Computers on Cascade Profiler. In that group you have included the subnet 192.168.1.0/25.
You have 10 devices in that group 192.168.1.1-10. The rest of the addresses are unused. While running reports on this segment of the network you notice that when a report is run using the entire subnet you see traffic destined for 192.168.1.120. When you run the same report specifying the host group the traffic does not appear. Why is this happening?
What is the maximum number of Cascade Profilers that can be configured in the Cascade Shark appliance as receivers of flows?
In the Cascade Profiler Dashboard GUI, which formats are available for Watched item content blocks? (Select 5)
What do you need to configure on the Profiler to detect utilization for an interface?
The Discovery Wizard has been used to map a complex application to be monitored by Cascade ' s service monitoring for a company with 25 remote locations and one data center, each defined as a group within the group type used. There are two front-end segments to signify incoming end user connections, and 15 back-end connections among all of the servers. The only metric/policy activated for each segment is the ' Response Time ' metric. How many policies on the Cascade Profiler will this service consume?
Which of the following is information that Netflow v5 provides to the Cascade solution? (Select 2)
Which of the following does the Cascade Sensor device provide that the Cascade Sensor-VE does not? (Select 2)
Technologies used for switching traffic between Virtual Machines under ESXi include:
Refer to the exhibit.
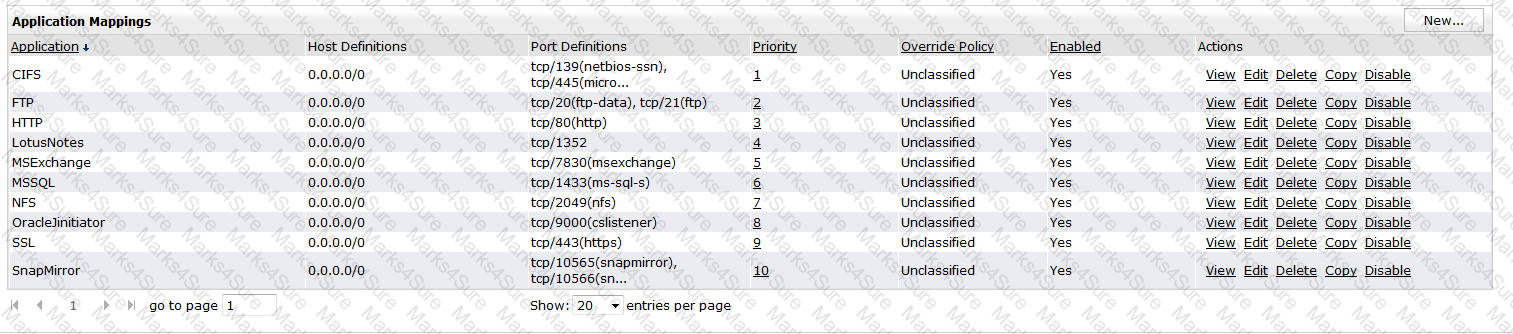
Traffic that is not analyzed by a Cascade Sensor such as Unclassified, under Override Policy, applies to which of the following conditions:
When saving a new application performance analytic on Cascade Profiler, which of the following is true?
If there is a Layer 7 fingerprint and a Layer 4 mapping for a particular application, which of the following is truE. (Select 5)
Which of the following metrics are monitored in an Application Performance Policy? (Select 4)
How does Cascade Profiler obtain switch port discovery and population information?
What is the minimum number of physical appliances required when building Cascade solution that will collect and process 3.6 million unique (de-duplicated) flows/minute from NetFlow sources?
What is the relationship between a Host Group and a Host Group Type in Cascade Profiler?
On Cascade Profiler, what does " tunneled " indicate when used as a keyword for an Application?
In Cascade Profiler, what is the minimum amount of historical flow data required for an Application Performance analytic to initialize?
The " Policies Usage " that is reported under System – Information pertains to which of the following:
Within Cascade Pilot, Sequence Diagrams represent TCP Errors in which of the following ways: (Select 2)
A router that has been recently configured to send NetFlow to a Cascade Gateway has yet to appear in the Devices/Interfaces page on the Cascade Profiler. What are the most likely thing to check?
On Cascade Profiler, what is the purpose of a Service Segment when creating a new service?
On an Enterprise Profiler, which Cascade software module usually runs on hardware with another software module, but can be placed on its own hardware to support extremely large clusters?
Which of the following is false in regards to Cascade Profiler reporting and alerting? (Select 2)
Which Cascade device actually polls for the SNMP information in the switch port Discovery process?
What is one way Cascade obtains information about retransmissions in the network?
When drilling down from a Cascade Profiler traffic report to analyze the underlying packets in Cascade Pilot, which of the following is NOT required?
A user wants to use the link congestion analytic policy on Cascade Profiler to monitor five key WAN links for an increase in traffic outside of the expected traffic that includes TCP/80, TCP/443, TCP25, and UDP/53. Can the link congestion policy be used for this scenario?
Which of the following are TRUE concerning packet capture jobs on the Cascade Shark appliancE. (Select 4)
When using Network Performance Monitoring solutions the following statements are truE. (select 2)
Within Cascade Profiler, what can be done to prevent a data resolution from being available for selection on the Report Criteria section of traffic reports?
In the Cascade Profiler GUI, what are two default dashboards that are automatically created for each user account? (Select 2)
For a worm security event to be triggered on Cascade Profiler, what event must have occurred first?
What must happen prior to running WAN Optimization reports on Cascade Profiler?
Which configuration option is it highly recommended that every Cascade Profiler Deployment implement?
What CIDR block would you use to define a group on Cascade Profiler that will include all hosts ending in .1 in the 10/8 subnet?
WAN optimization reports on Cascade Profiler require that the WAN interfaces for all Steelheads performing optimization are included in a WAN Interface group and are marked as Steelhead interfaces. Which of the following is true?
What is the purpose of the snmp-server ifindex-persist command in regards to Riverbed Steelhead appliances and Cascade Profiler? (Select 2)
On a newly created capture job on Cascade Shark appliance, by default, trending/indexing arE. (Select 2)
Which is a true statement regarding choosing between a 2U and a 3U Cascade Shark base appliancE. (Select 2)
One advantage of using a trace clip for analysis within Cascade Pilot instead of its parent capture job trace is:
Which parameters can be used to set up an Application Performance analytic on Cascade Profiler?
Which of the following best describes any limits that are enforced on the number of service, performance and availability policies that are supported on any Cascade Profiler?
When analyzing a large (100GB, for example) trace file within Cascade Pilot, you should:
On Cascade Profiler, Which of the following account role permissions is not unique to administrator accounts?
Which content block can be used to compare traffic between two time periods on the Cascade Profiler Dashboard?