The Security Operations Center team at a company detects a successful VPN connection from a country outside the known countries of operation. After the connection occurs, the team receives multiple triggers from the same source IP address about file access and modifications to the file server. The team concludes that this is a case of data exfiltration from an unknown adversary through a compromised user account. To find other potential actions taken by the adversary, which type of threat hunting should be used?
A threat hunter is performing a structured hunt using Cisco Secure Endpoint (AMP) telemetry to identify credential harvesting activity. Which data source is MOST critical during the data collection and processing phase of the hunt?
A security architect is designing a threat model for a multi-tier cloud application that includes public APIs, backend microservices, and an identity provider. The goal is to identify how an attacker could chain multiple weaknesses together to achieve account takeover and data exfiltration. Which threat modeling technique is MOST appropriate?
A SOC analyst using Cisco security tools wants to differentiate threat hunting from traditional detection engineering . Which activity BEST represents threat hunting rather than detection engineering?
A threat hunting team wants to ensure hunts are repeatable, scalable, and less dependent on individual analyst intuition. What is the MOST important process improvement?
A security team wants to create a plan to protect companies from lateral movement attacks. The team already implemented detection alerts for pass-the-hash and pass-the-ticket techniques. Which two components must be monitored to hunt for lateral movement attacks on endpoints? (Choose two.)
A mature SOC notices that several incidents over the past year involved attackers abusing legitimate administrative tools rather than deploying custom malware. Leadership asks the threat hunting team to improve detection coverage in a way that increases attacker cost rather than relying on easily replaceable indicators. Which detection strategy best aligns with this objective?
The CISO must improve the threat-hunting strategy to strengthen the organization's security posture and better prepare against sophisticated threats. Which aspect of the Threat Hunting Maturity Model can significantly enhance an organization's ability to address challenges outlined in the Pyramid of Pain?
A threat hunting team is attempting to attribute a series of intrusions across multiple organizations to a known threat actor. The malware binaries differ across incidents, infrastructure changes frequently, and IP addresses rotate daily. Which evidence provides the STRONGEST basis for confident attribution?
During a structured hunt, analysts using Cisco SIEM tools complete hypothesis testing and confirm malicious activity. What is the NEXT step in the Cisco threat hunting lifecycle?
A SOC analyst is using Cisco Secure Network Analytics (Stealthwatch) to hunt for command-and-control (C2) activity across the enterprise. The analyst wants to identify stealthy C2 channels that intentionally avoid known malicious IP addresses and domains. Which Stealthwatch hunting approach BEST supports this objective?
A SOC using Cisco security technologies wants to measure the success of its threat hunting program over time. Which metric BEST reflects increased threat hunting maturity?
Refer to the exhibit.
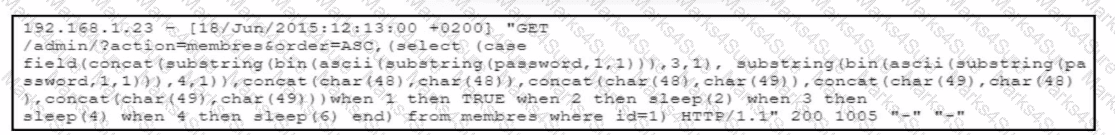
The cybersecurity team at a company detects an ongoing attack directed at the web server that hosts the company website. The team analyzes the logs of the web application firewall and discovers several HTTP requests encoded in Base64. The team decodes the payloads and retrieves the HTTP requests. What did the attackers use to exploit the server?
A SOC team wants to detect lateral movement performed using legitimate administrative tools rather than malware. Which telemetry source provides the MOST reliable visibility for this hunting objective?
A SOC team using Cisco security technologies wants to distinguish Indicators of Attack (IOAs) from Indicators of Compromise (IOCs) during threat hunting. Which scenario BEST represents an IOA rather than an IOC?