300-415 Implementing Cisco SD-WAN Solutions (300-415 ENSDWI) Questions and Answers
How must the application-aware enterprise firewall policies be applied within the same WAN Edge router?
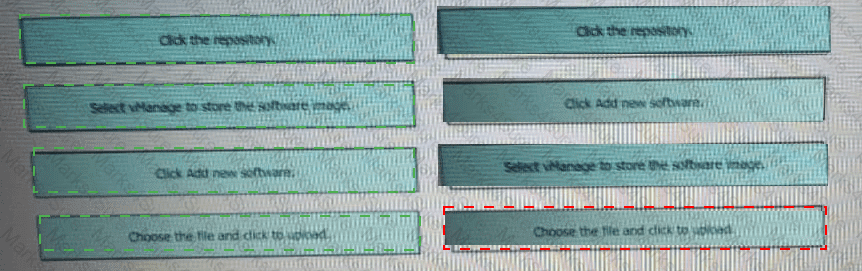
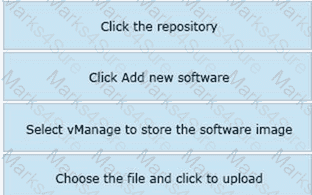
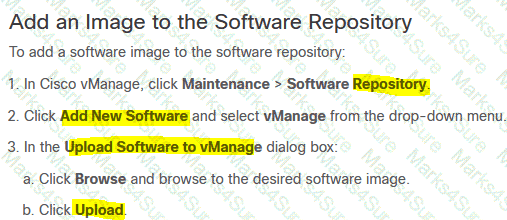
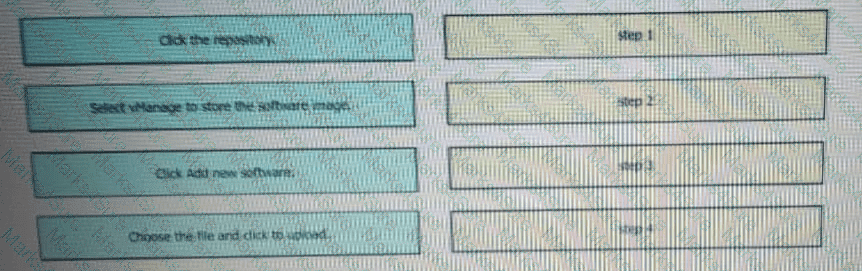
Drag and drop the steps from the left into the order on the right to upload software on vManage repository that is accessible from maintenance > Software Repository.
How should the IP addresses be assigned for all members of a Cisco vManage cluster located in the same data center?
An engineer is applying QoS policy for the transport-side tunnel interfaces to enable scheduling and shaping for a WAN Edge cloud router Which command accomplishes the task?
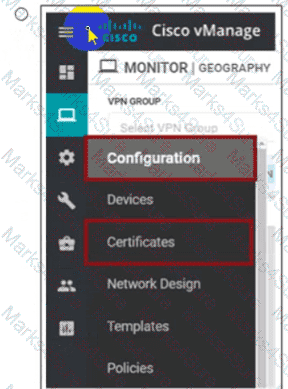
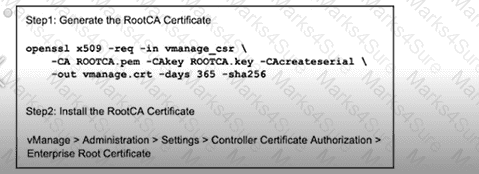
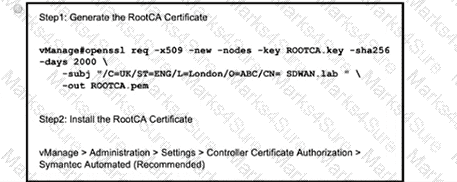
Which two actions are necessary to set the Controller Certificate Authorization mode to indicate a root certificate? (Choose two)
An administrator needs to configure SD-WAN to divert traffic from the company ' s private network to an ISP network. What action should be taken to accomplish this goal?
When software is upgraded on a vManage NMS, which two image-adding options store images in a local vManage software repository? (Choose two.)
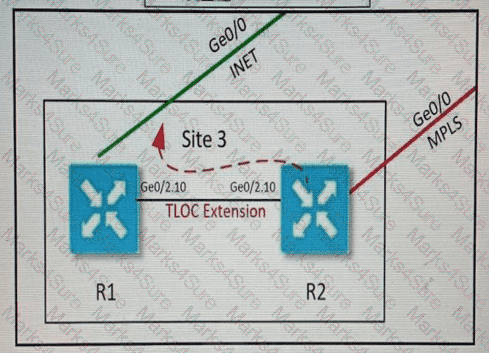
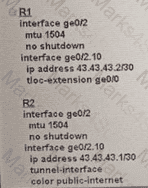
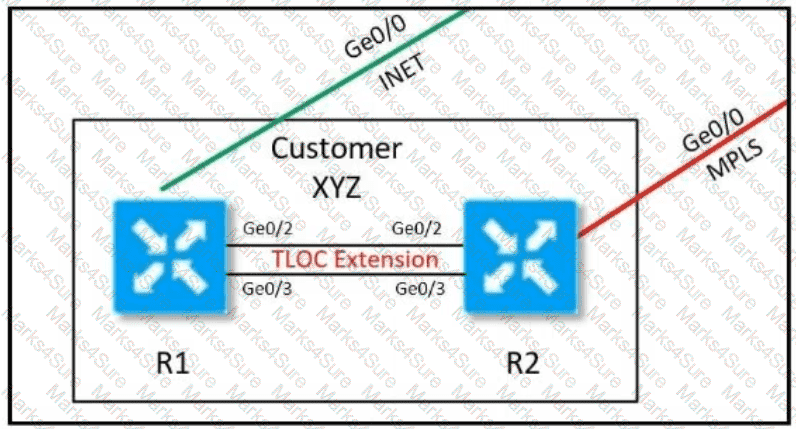
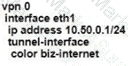
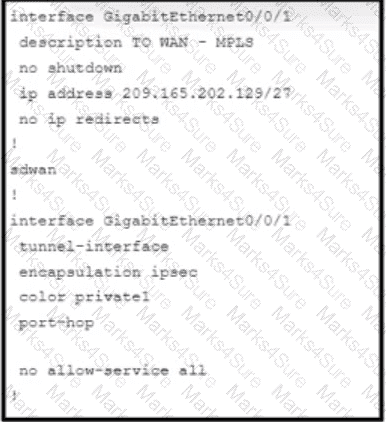
Refer to the exhibit. Which configuration extends the INET interface on R1 to be used by R2 for control and data connections?
A)
B)
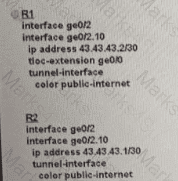
C)
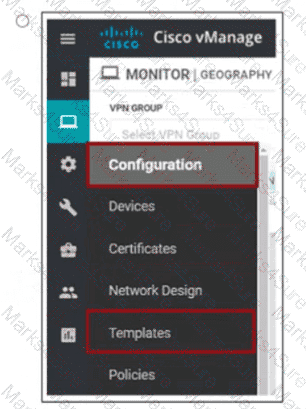
An engineer must automate certificate signing through Cisco. Which vManage configuration achieves this task?
A)
B)
C)
D)
Which command displays BFD session summary information per TLOC on vEdge routers?
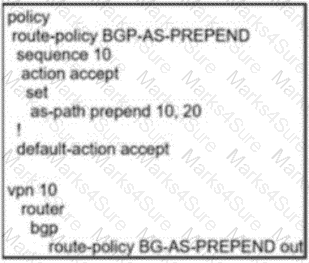
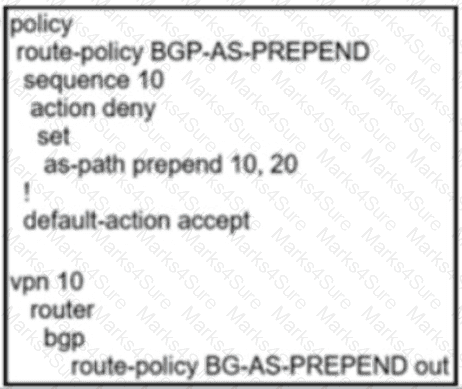
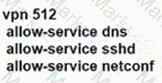
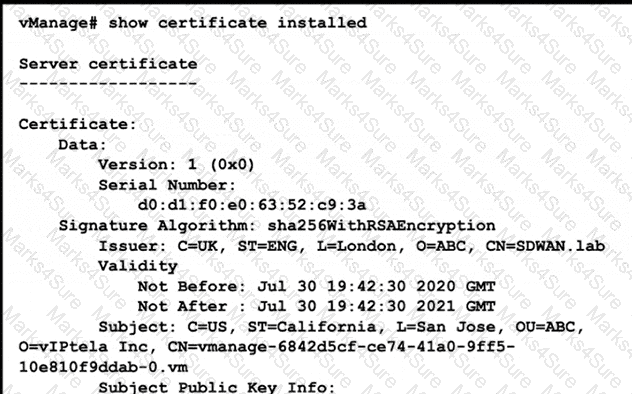
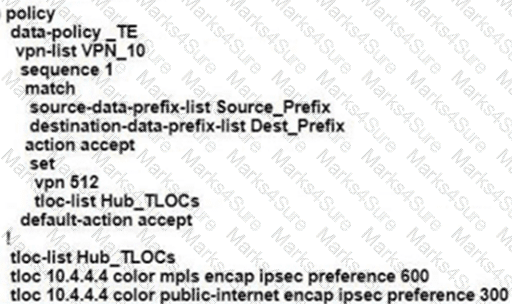
Refer to the exhibit.
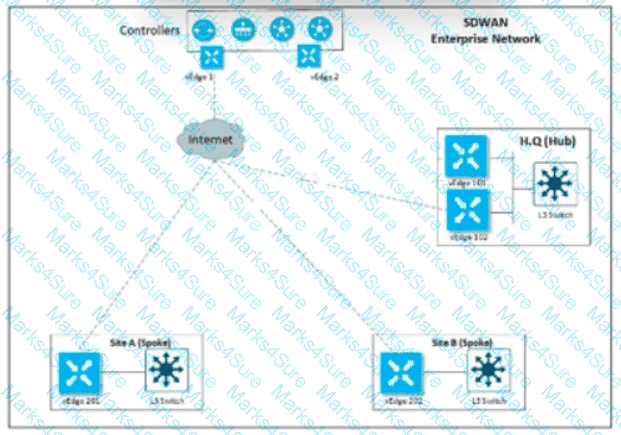
Customer XYZ cannot provison dual connectivity on both Its routers due to budget constratnts but wants to use tnth RI and R2 interface for users behind them for load toward the hub site Which configurauon achieves this objectives?
A)

B)
C)
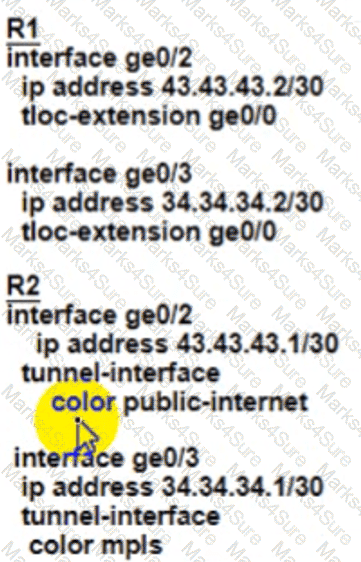
D)
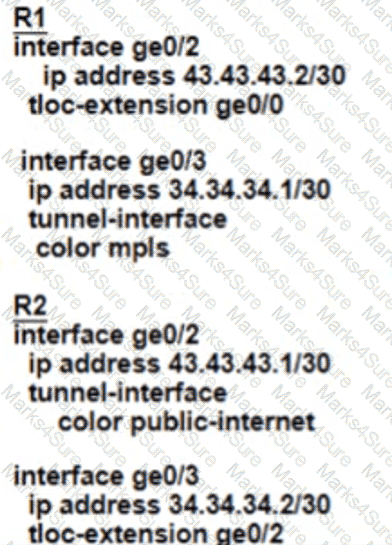
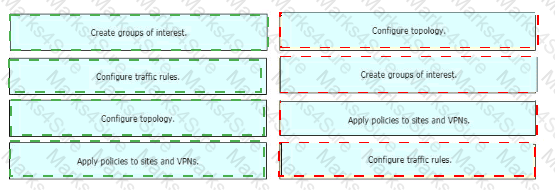
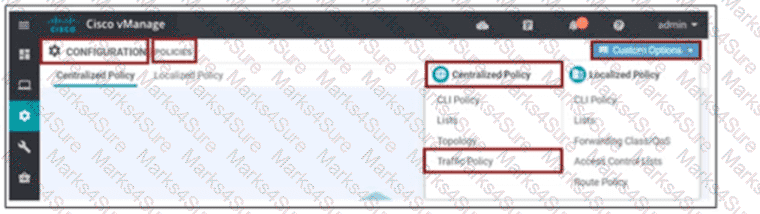
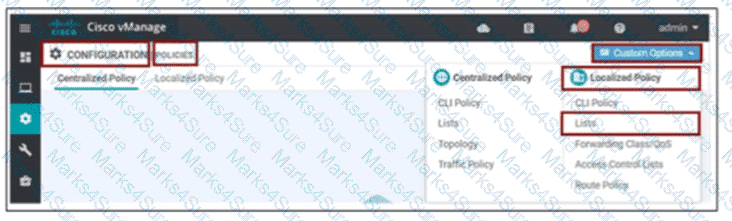
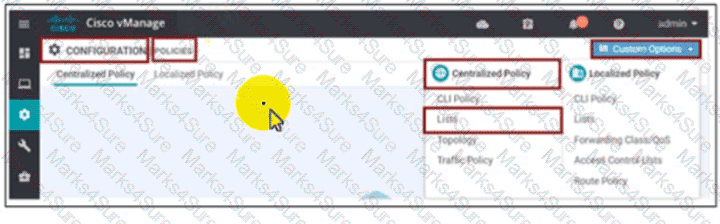
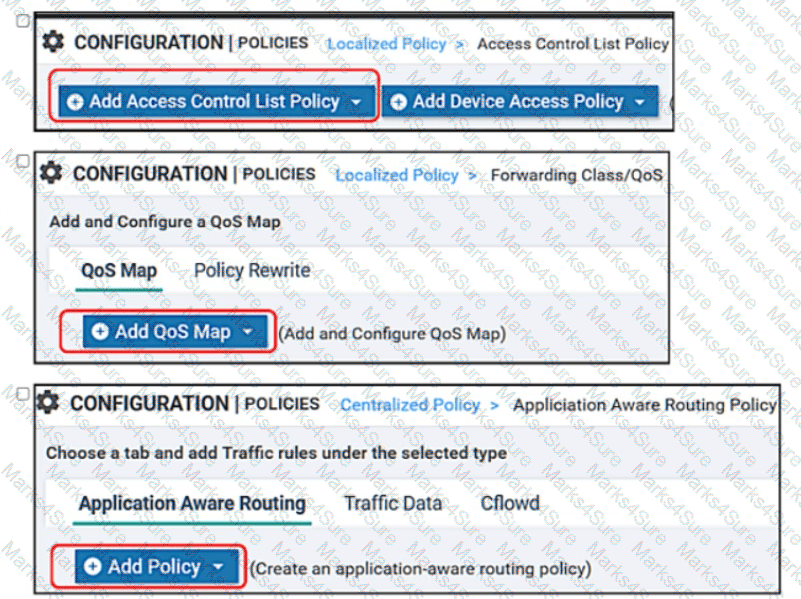
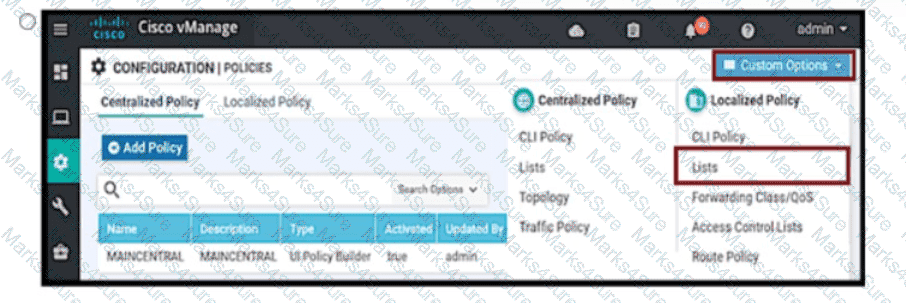
Drag and drop the vManage policy configuration procedures from the left onto the correct definitions on the right.
In a Cisco SD-WAN network, which component is responsible for distributing route and policy information via the OMP?
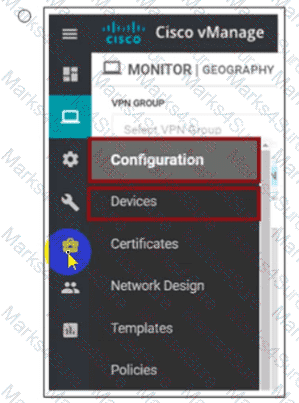
Company ABC has decided to deploy the controllers using the On-Prem method. How does the administrator upload the WAN Edge list to the vManage?
A)

B)
C)

D)
A customer has MPLS and Internet as the TLOC colors An engineer must configure conlroJIers with the Internet and not with MPLS Which configuration achieves this requirement on vManage?
A)

B)

C)
D)
Which two resource data types are used to collect information for monitoring using REST API in Cisco SD-WAN? (Choose two.)
Which secure tunnel type should be used to connect one WAN Edge router to other WAN Edge routers?
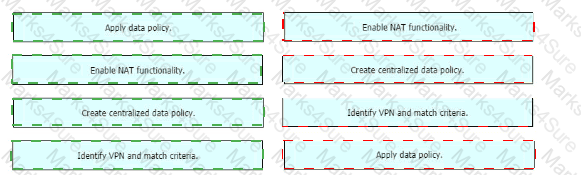
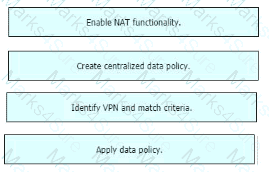
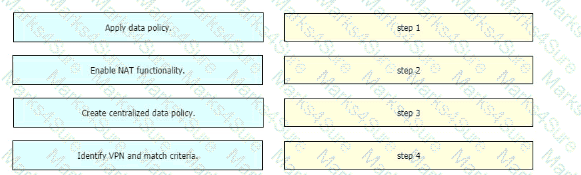
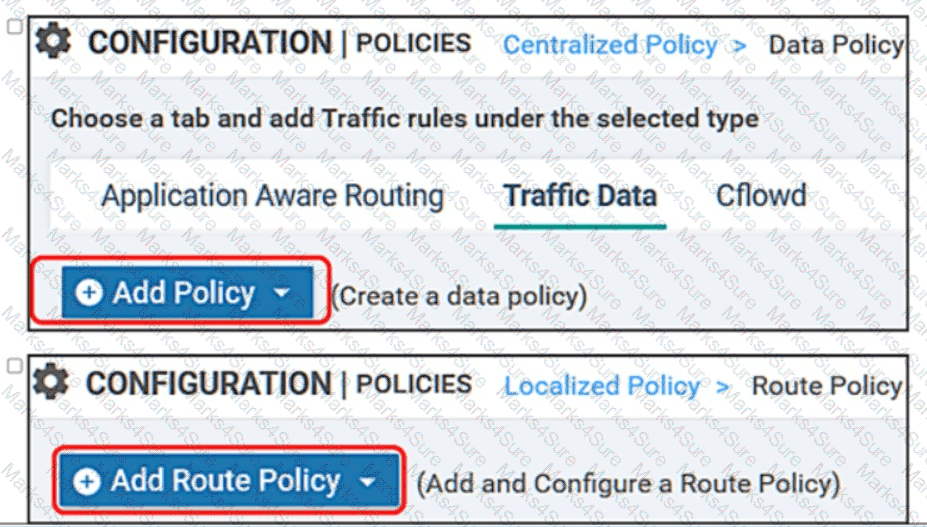
Drag and drop the actions from the left into the correct sequence on the right to create a data policy to direct traffic to the Internet exit.
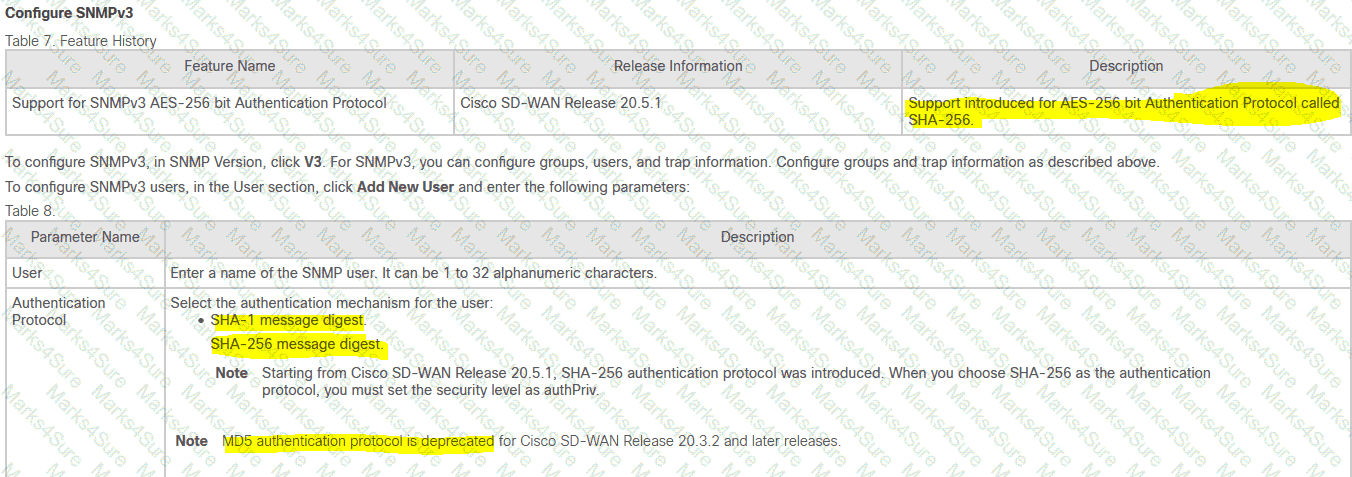
Which two algorithms authenticate a user when configuring SNMPv3 monitoring on a WAN Edge router? (Choose two.)
A customer wants to use AWS for Cisco SD-WAN laaS services by deploying virtual SD-WAN routers in a transit AWS VPC The transit VPC then connects via site-to-site IPsec tunnels to an AWS transit gateway Which transit VPC connects via site-to-site IPsec tunnels to an AWS transit gateway?
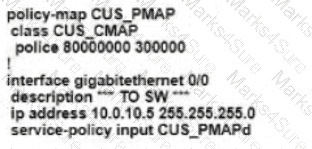
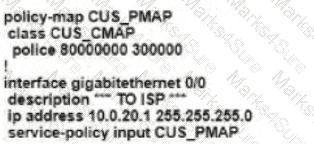
An engineer must create a QoS policy by creating a class map and assigning it to the LLQ queue on a WAN Edge router Which configuration accomplishes the task?
A)
 B)
B)
C)
D)

Which secure connection should be used to access the REST APIs through the Cisco vManage web server?
A large retail organization decided to move some of the branch applications to the AWS cloud. How does the network architect extend the in-house Cisco SD-WAN branch to cloud network into AWS?
In an AWS cloud, which feature provision WAN Edge routers automatically in Cisco SD-WAN?
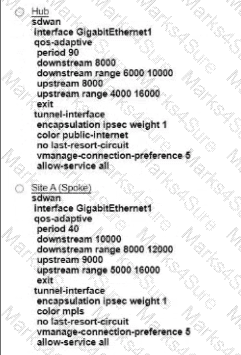
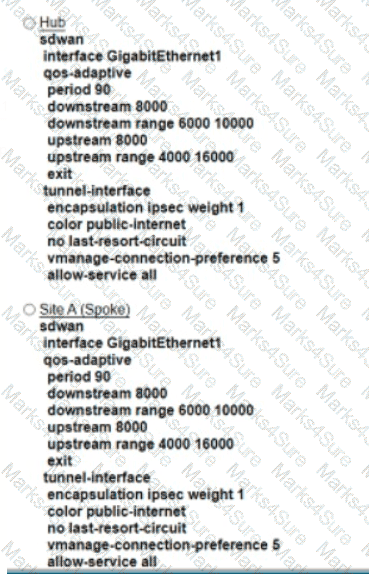
Refer to the exhibit An engineer must configure a QoS policy between me hub and site A (spoke) over a standard internet circuit where traffic shaping is adjusted automatically based on evaiiabk» bandwidth Which configuration meets the requirement?
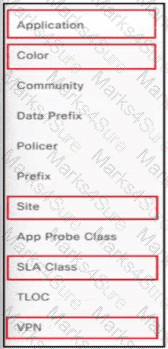
Which type of lists are used to group related items via an application-aware routing policy under the policy lists command hierarchy on vSmart controllers?
An engineer builds a three-node vManage cluster and then realizes that multiple nodes are unnecessary for the size of the company. How should the engineer revert the setup to a single vManage?
What are the default username and password for vSmart Controller when it is installed on a VMware ESXi hypervisor ' ?
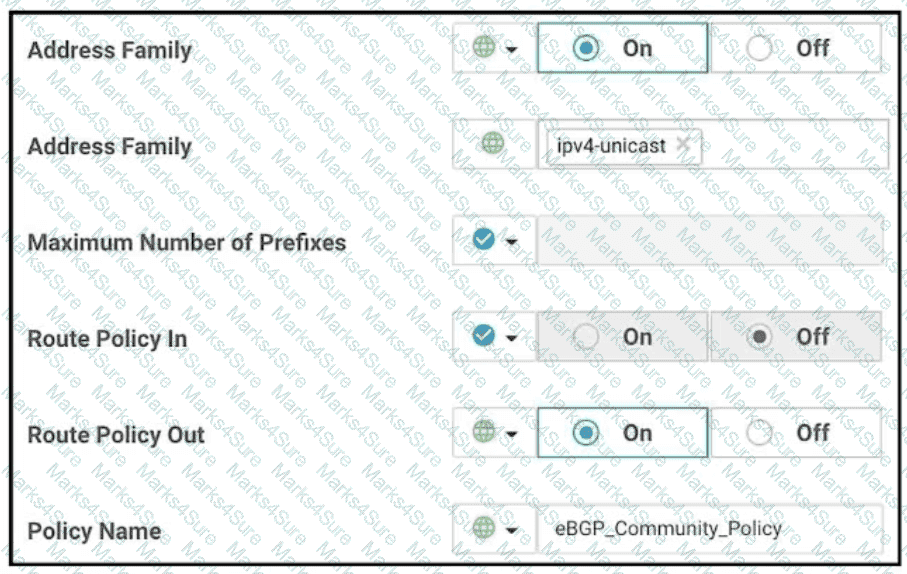
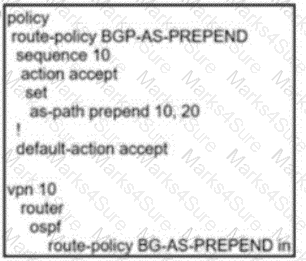
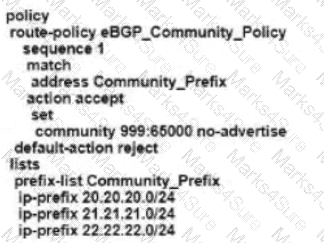
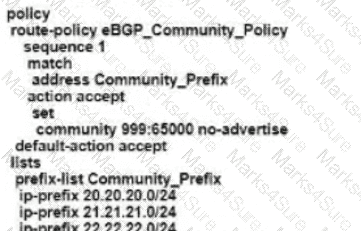
Refer to the exhibit The engineering must assign tags to 3 Of its 74 server networks as soon as they are advertised to peers These server network must not be advertised AS which configuration fulfil the requirement?
A)
B)
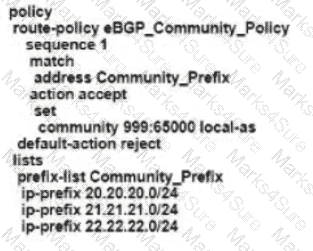
C)
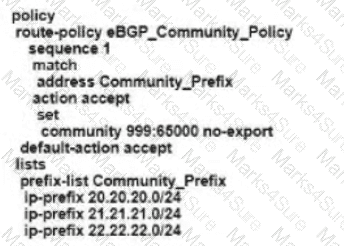
D)
Which service VPN must be reachable from all WAN Edge devices and the controllers?
Refer to the exhibit, which configuration configures IPsec tunnels in active and standby?

Which controller is used for provisioning and configuration in a Cisco SD-WAN solution?
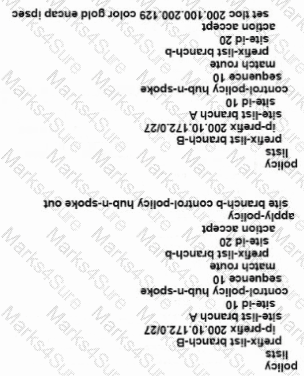
Which policy blocks TLOCs from remotes and allows TLOCs from the data center to form hub-and-spoke peering?
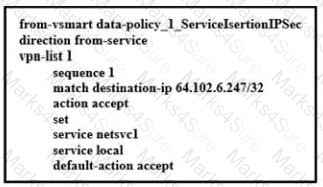
The Cisco SD-WAN engineer is configuring service chaining for a next-generation firewall located at the headquarters. Which configuration creates the service?
A)
B)
C)
D)
Which protocol runs between the vSmart controllers and WAN Edge routers when the vSmart controller acts like a route reflector?
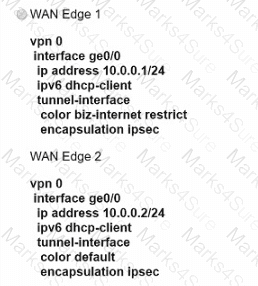
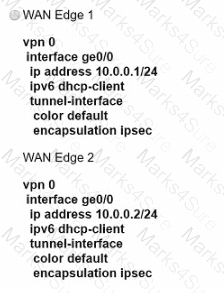
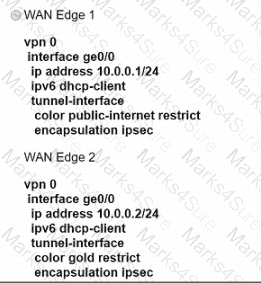
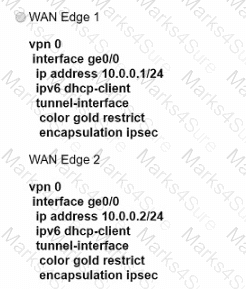
An engineer must configure two branch WAN Edge devices where an Internet connection is available and the controllers are in the headquarters. The requirement is to have IPsec VPN tunnels established between the same colors. Which configuration meets the requirement on both WAN Edge devices?
Which Cisco SD-WAN component the initial communication between WAN Edge devices to join the fabric?
Which policy tracks path characteristics such as loss, latency, and jitter in vManage?
Which two mechanisms are used by vManage to ensure that the certificate serial number of the WAN Edge router that is needed to authenticate is listed in the WAN Edge Authorized Señal Number Hst’ (Choose two)
An engineer must configure the SD-WAN Edge router to identify DSCP 26 traffic coming from the router ' s local site and then change the DSCP value to DSCP 18 before sending it over to the SD-WAN fabric. What are the two ways to create the required configuration? (Choose two).
A network administrator is configuring a tunnel interface on a branch Cisco IOS XE router to run TLOC extensions. Which configuration will extend a TLOC over a GRE tunnel to another router in the branch?

Which feature builds transport redundancy by using the cross link between two redundant WAN Edge routers?
Which protocol is used between redundant vSmart controllers to establish a permanent communication channel?
Which set of elements are verified by the controller to confirm the identity of edge devices?

Refer to the exhibit Cisco SD-WAN is deployed with controllers hosted in a data center All branches have WAN Edge devices with dual connections to the data center one via Internet and the other using MPLS Three branches out of 20 have issues with their control connections on MPLS circuit The local error refers to Control Connection Failure Which action resolves the issue*?
Which two mechanisms are used to guarantee the integrity of data packets in the Cisco SD-WAN architecture data plane? {Choose two)
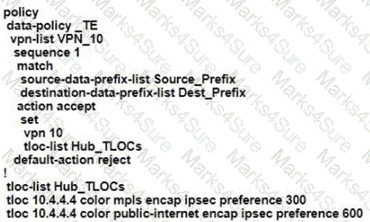
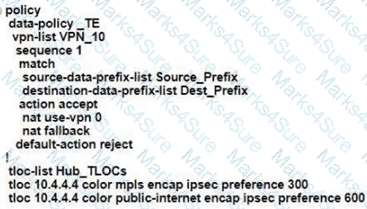
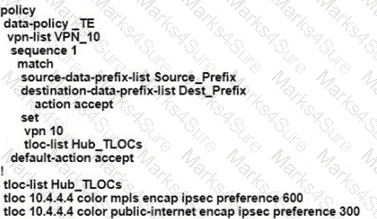
An engineer modifies a data policy for DIA in VPN 200 to meet the requirements for traffic destined to these locations:
* external networks; must be translated
* external networks; must use a public TLOC color
* syslog servers, must use a private TLOC color
Here is the existing data policy configuration:
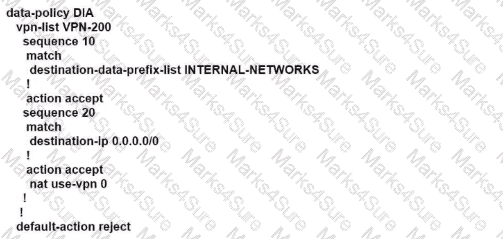
Which policy configuration sequence set meets the requirements?
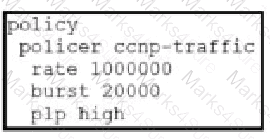
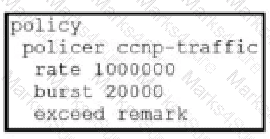
Which configuration changes the packet loss priority from low to highly?
A)
B)
C)
D)
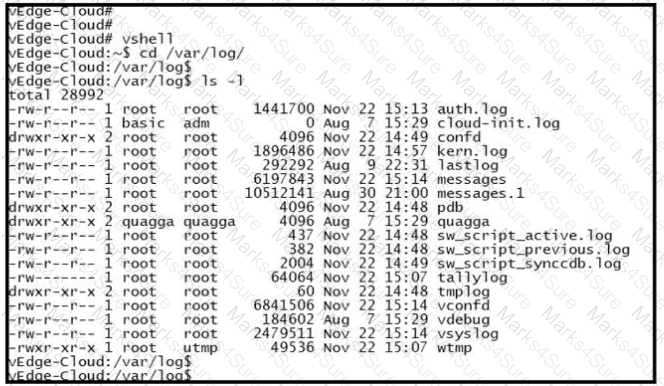
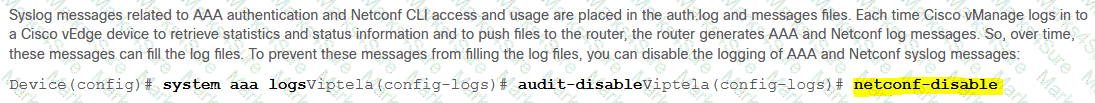
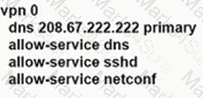
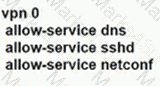
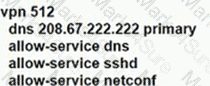
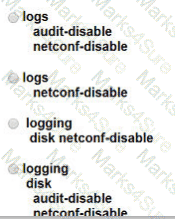
Refer to the exhibit. Which configuration stops Netconf CLI logging on WAN Edge devices during migration?
How many cloud gateway instance(s) can be created per region when provisioning Cloud OnRamp for Multicloud from AWS in a multiregion environment?
Which protocol is used to measure jitter, loss, and latency on SD-WAN overlay tunnels?
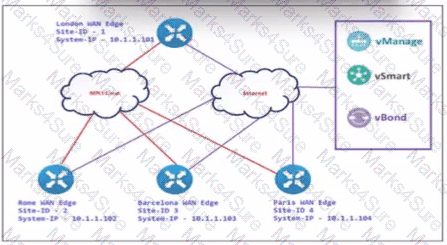
An engineer configures Rome WAN Edge 10 use MPLS cloud as the preferred link to reach Paris WAN Edge and use biz-internet as a backup. Which policy configuration must be led in the outbound direction toward Rome to accomplish the task?
A)

B)
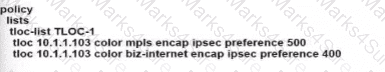
C)
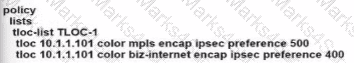
D)

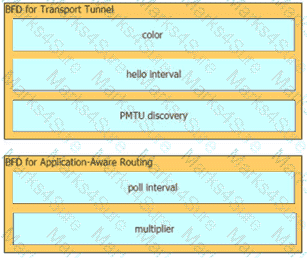
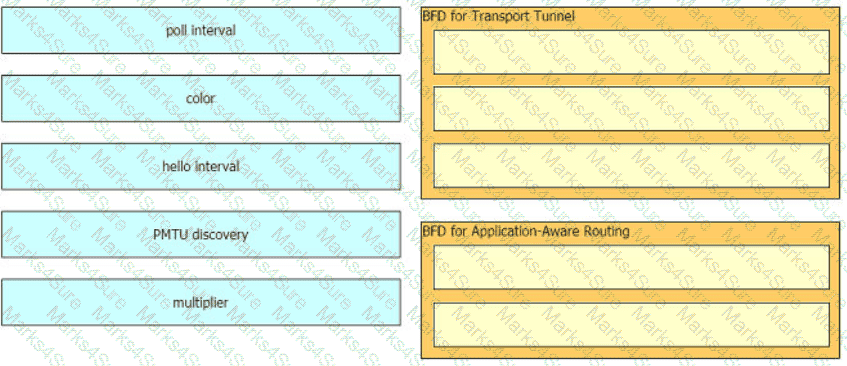
Drag and drop the BFD parameters from the left onto the BFD configurations on the right.
An SD-WAN customer must ensure that its network operations team can monitor and update the NTP server if needed on a WAN Edge in HQ. Which configuration meets this requirement?
An organization wants to use the cisco SD-WAN regionalized service-chaining feature to optimize cost and user experience with application in the network, which allows branch routers to analyze and steer traffic toward the required network function. Which feature meets this requirement?
When the VPN membership policy is being controlled at the vSmart controller, which policy disallows VPN 1 at sites 20 and 30?
A)
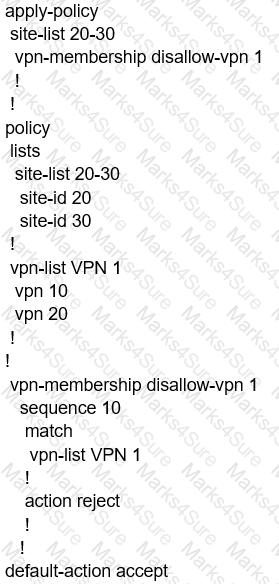
B)
C)
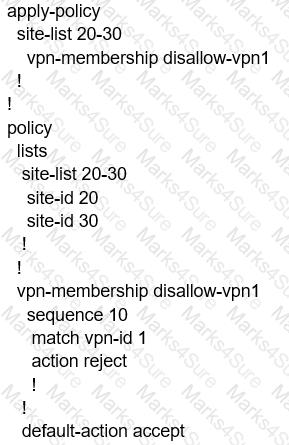
D)

An engineer is configuring a WAN Edge router for DIA based on matching QoS parameters. Which two actions accomplish this task? (Choose two.)
An engineer must configure local redundancy on a site. Which configuration accomplish this task?
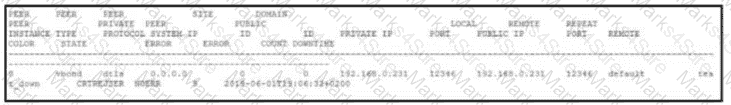
Refer to exhibit. An engineer is troubleshooting tear of control connection even though a valid CertificateSerialNumber is entered. Which two actions resolve Issue? (Choose two)
When a WAN Edge device joins the SD-WAN overlay, which Cisco SD-WAN components orchestrates the connection between the WAN Edge device and a vSmart controller?
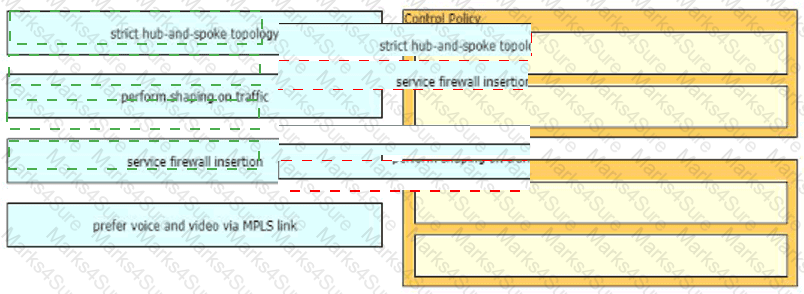
Drag and drop the policies from the left onto the correct policy types on the right.
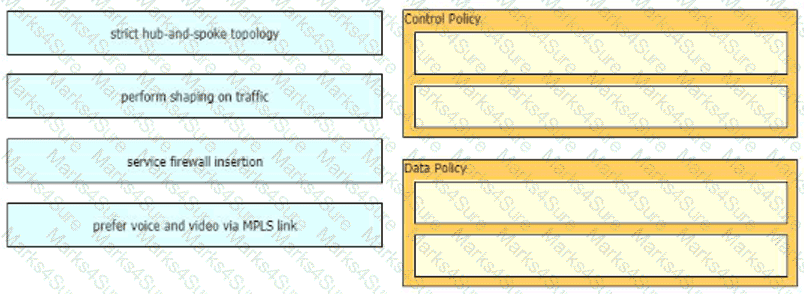
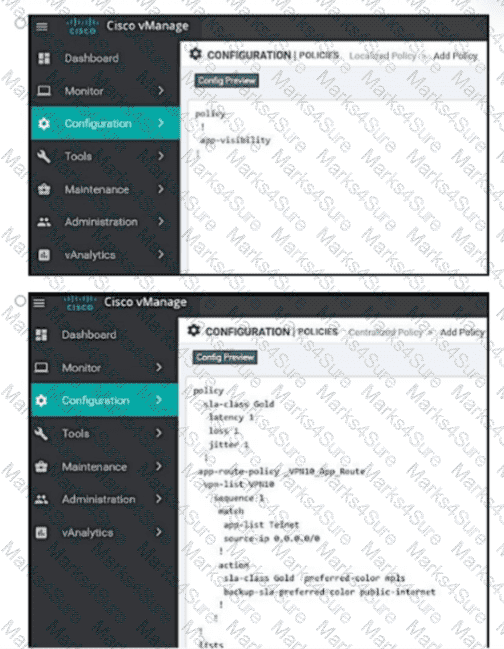
Exhibit.
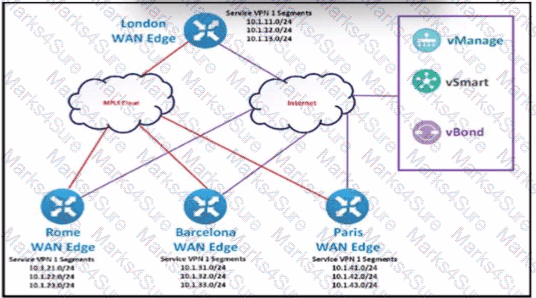
The SD-WAN network Is configured with a default full-mesh topology. The network engineer wants the Rome WAN Edge to use the MPLS TLOC as the preferred TLOC when ….. Telnet traffic as long as me MPLS Ink has these, characteristics:
Loss: 5%
Latency: 100ms
Jitter: 100 ms
Which configuration must the network engineer use to create a list that that classifies the MPLS link characteristics?
A)

B)

C)

D)
In the Cisco SD_WAN solution, vSmart controller is responsible for which two actions? (Choose two.)
What is a benefit of the application aware firewall feature in the Cisco SD-WAN solution?
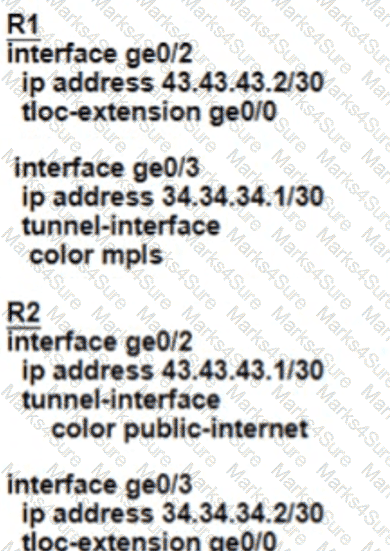
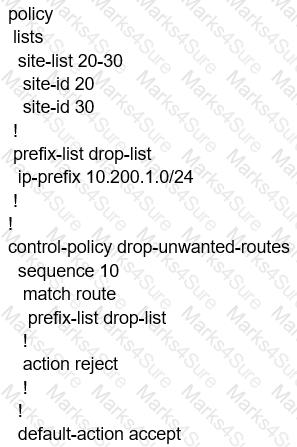
Refer to the exhibit.
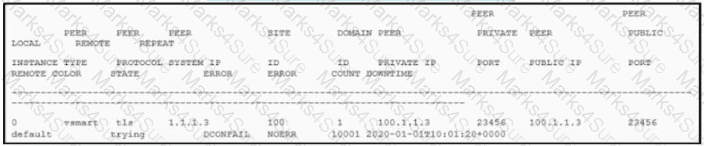
The control connection is failing. Which action resolves the issue?

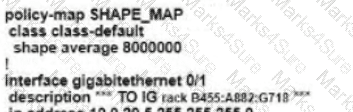
Refer to the exhibit. An enterprise network is connected with an ISP network on an 80 Mbps bandwidth link. The network operation team observes 100 Mbps traffic on the 1Gig-ISP link during peak hours Which configuration provides bandwidth control to avoid traffic congestion during peak hours?
A)
B)
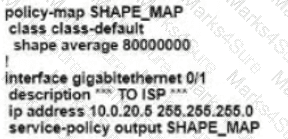
C)
D)
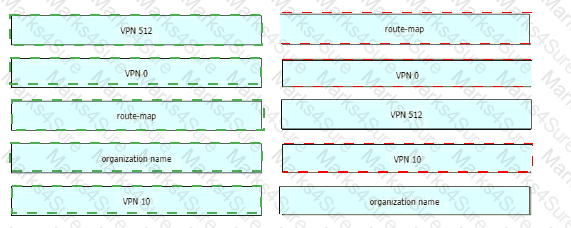
Which configuration defines the groups of interest before creation of the access list or route map?
A)
B)

C)
D.

How does the Cisco SD-WAN Cloud OnRamp solution rate the performance of a SaaS application from a branch office to the cloud via a given path?
Which two products are used to deploy Cisco WAN Edge Router virtual platforms? (Choose two.)
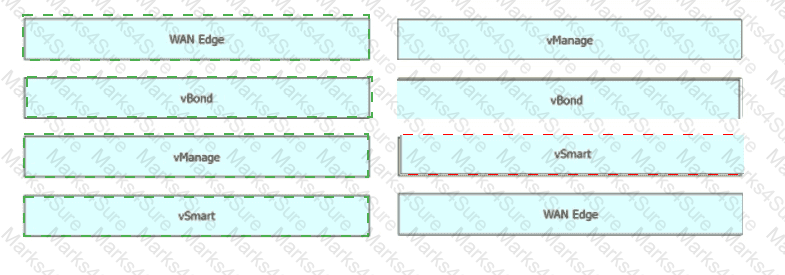
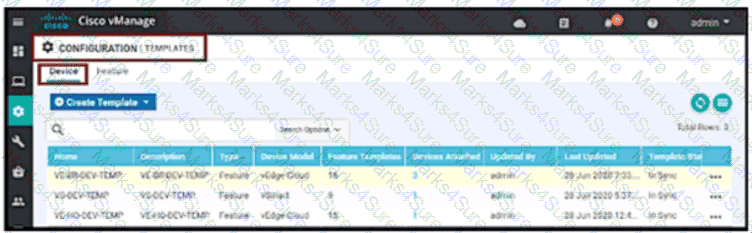
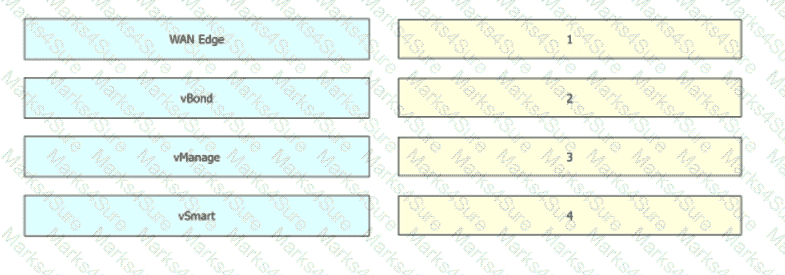
Drag and drop the devices from the left into order on the right to upgrade the software from version 19 to version 20.
A network administrator is configuring VRRP to avoid a traffic black hole when the transport side of the network is down on the master device. What must be configured to get the fastest failover to standby?
Which policy allows communication between TLOCs of data centers and spokes and blocks communication between spokes?
Which two protocols are supported for software image delivery when images are hosted on a remote server? (Choose two.)
Which two requirements must be met for DNS inspection when integrating with cisco umbrella? (Choose two)
Which device information is requited on PNP/ZTP to support the zero-touch onboarding process?
Refer to the exhibit.
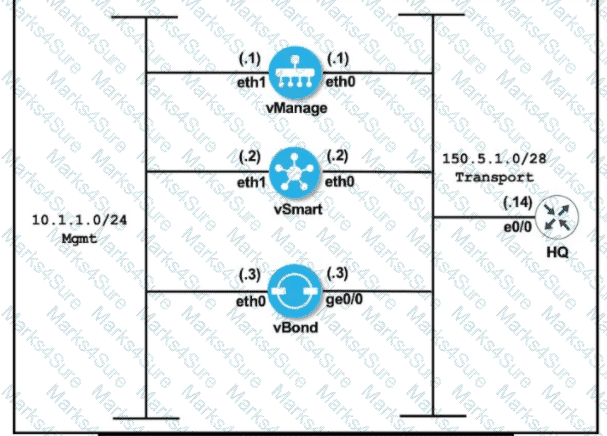

An engineer is troubleshooting an issue where vManage and vSmart have a problem establishing a connection to vBond. Which action fixes the issue?
Which two advanced security features are available on the Cisco SD-WAN WAN Edge (vEdge) device? (Choose two.)
Which IP address must be reachable by a WAN Edge device for the ZIP process to work?
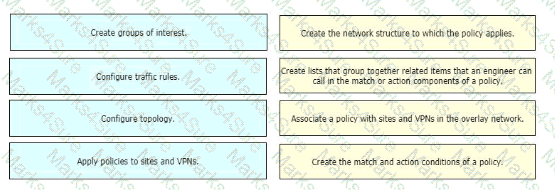
How is an event monitored and reported for an individual device in the overlay network at site ID:S4300T6E43F36?
Which routing protocol is used to exchange control plane information between vSmart controllers and WAN Edge routers in the Cisco SD-WAN secure extensible network?
Which issue triggers the Cisco Umbrella resolver to toward DNS requests to the intelligent proxy?
Which issue triggers the Cisco Umbrella resolver to toward DNS requests to the intelligent proxy?
Refer to the exhibit. An engineer is enabling command line access via MPLS for in-band management. Which command completes the partial SD-WAN interface configuration with the highest degree of security?

Which two criteria ate supported to filter traffic on a Cisco Umbrella Cloud-delivered firewall? (Choose two )
An engineer is adding a tenant with location ID 399533345 in vManage. What is the maximum number of alphanumeric characters that is accepted in the tenant name filed?
Which feature delivers traffic to the Cisco Umbrella SIG cloud from a Cisco SD-WAN domain?
What is the function of the AppNav Controller in the Cisco SD-WAN AppNav solution?
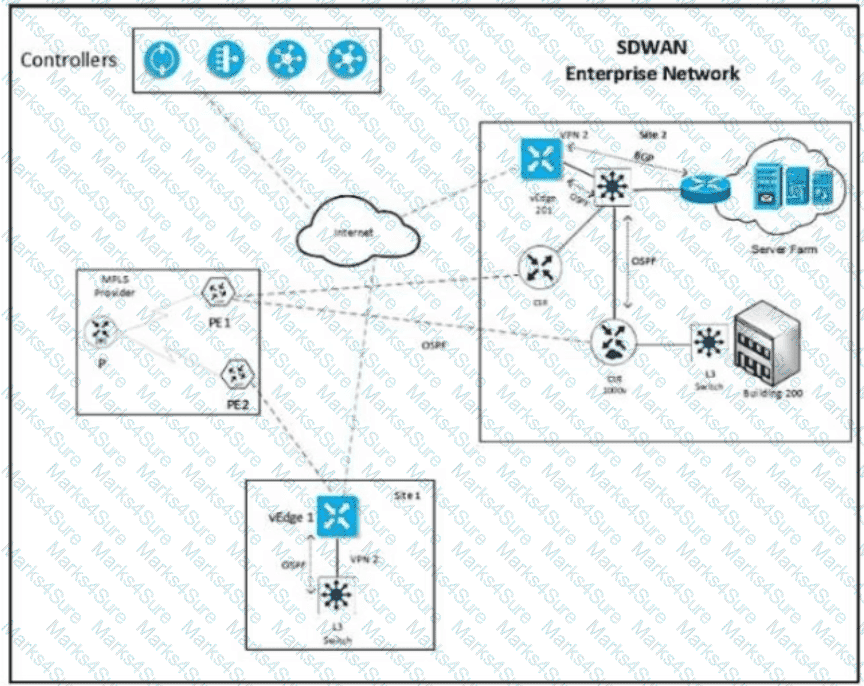
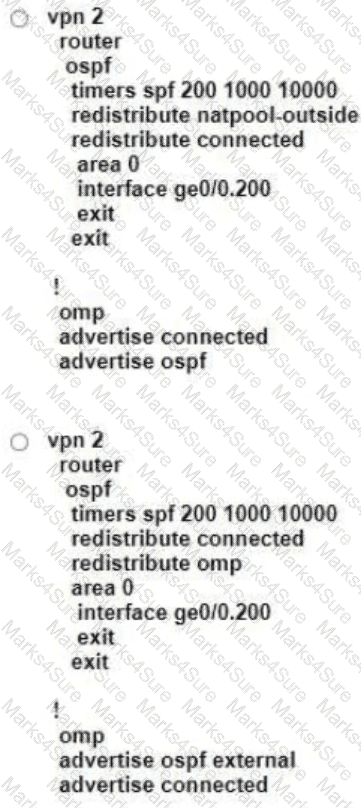
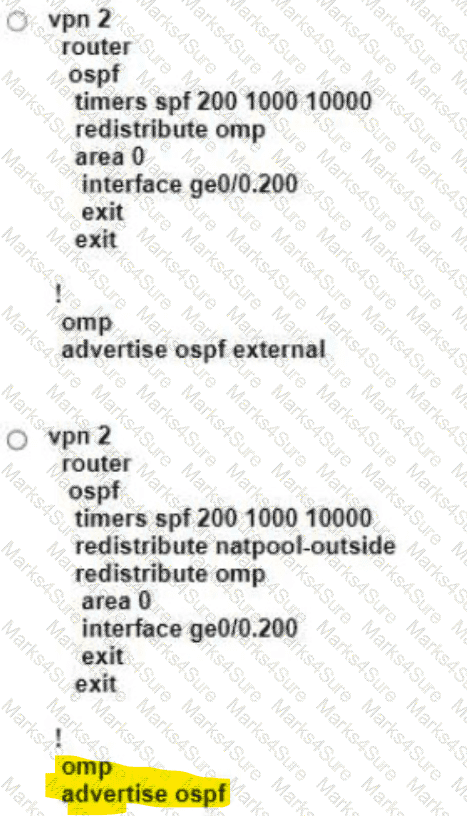
Refer to the exhibit Which configuration ensures that OSPF routes learned from Site2 are reachable at Sitel and vice-versa?
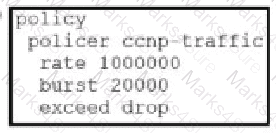
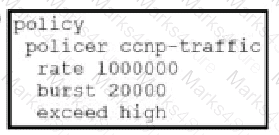
An engineer must deploy a QoS policy with these requirements:
• policy name: App-police
• police rate: 1000000
• burst: 1000000
• exceed: drop
Which configuration meets the requirements?

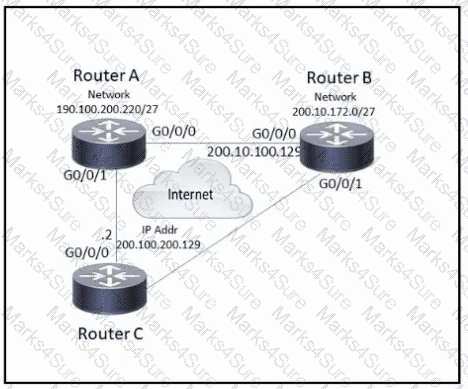
Refer to the exhibit. An engineer configures a hub-and-spoke SD-WAN topology with the requirement that traffic from router A branch to router B branch is guaranteed to flow through the network hub, router C. Which configuration meets the requirement for router A?


Refer to the exhibit. An engineer must block FTP traffic coming in from a particular Service VPN on a WAN Edge device Which set of steps achieves this goal?
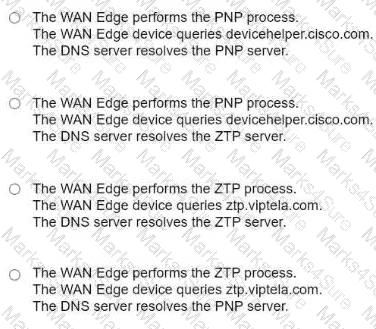
Which action is performed during the onboarding process when a WAN Edge router is connected to ZTP server ztp.viptela com?
Refer to the exhibit.

Which shaping-rate does the engineer use to shape traffic at 9 Mbps?
An organization wants to discover monitor and track the applications running on the WAN Edge device on the LAN Which configuration achieves this goal?

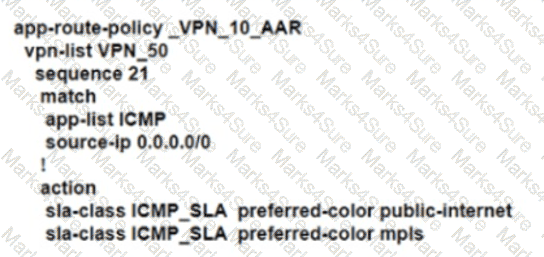
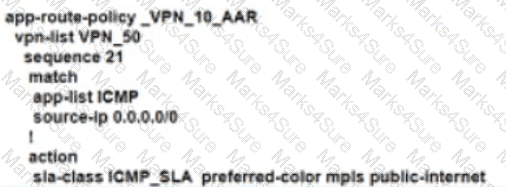
An enterprise deployed a Cisco SD-WAN solution with hub-and-spoke topology using MPLS as the preferred network over the Internet. A network engineer must implement an application-aware routing policy to allow ICMP traffic to be load-balanced over both the available links. Which configuration meets the requirement?
A)
B)
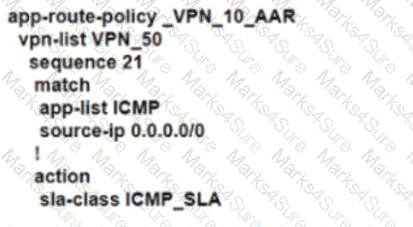
C)
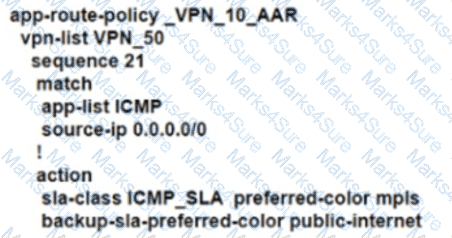
D)
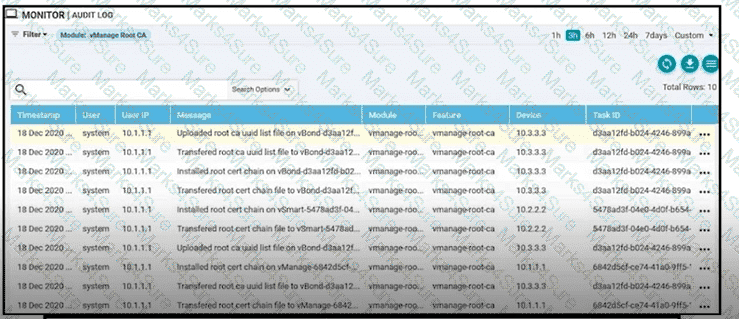
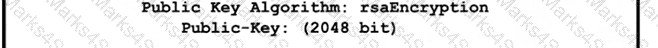
Refer to the exhibit A small company was acquired by a large organization As a result, the new organization decided to update information on their Enterprise RootCA and generated a new certificate using openssl Which configuration updates the new certificate and issues an alert in vManage Monitor | Events Dashboard?
Refer to the exhibit.
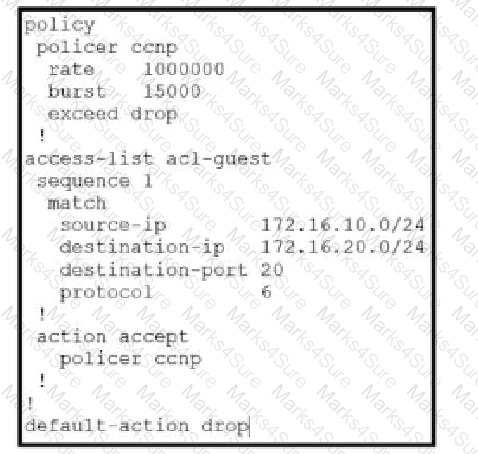
Which QoS treatment results from this configuration after the access list acl-guest is applied inbound on the vpn1 interface?
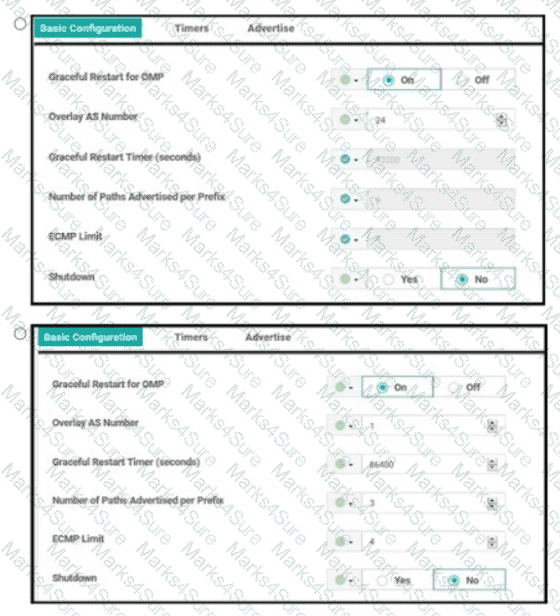
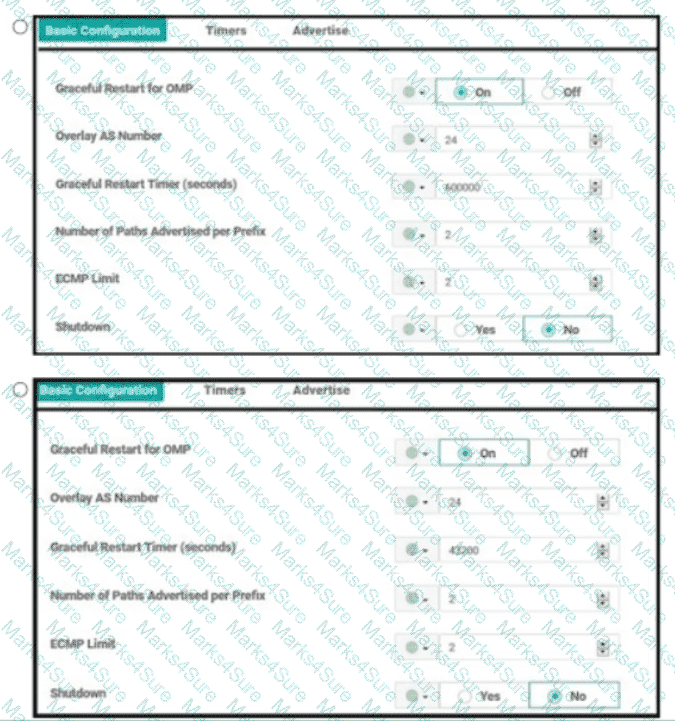
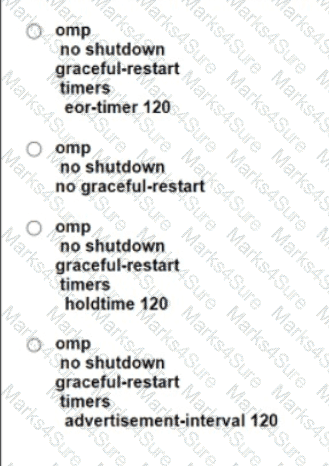
An enterprise is continuously adding new sites to its Cisco SD-WAN network. It must configure any cached routes flushed when OMP peers have lost adjacency Which configuration allows the cached OMP routes to be flushed after every 24 hours from its routing table?
Which component of the Cisco SD-WAN secure extensible network provides a single pane of glass approach to network monitoring and configuration?
A network administrator is configuring an application-aware firewall between inside zones to an outside zone on a WAN edge router using vManage GUI. What kind of Inspection is performed when the ‘’inspect’’ action is used?
Which website allows access to visualize the geography screen from vManager using the internet?
Which Cisco router provides a distributed multicore architecture optimized for SD-WAN branch support?
What is a requirement for a WAN Edge to reach vManage, vBond, and vSmart controllers in a data center?
Which timer specifies information in the cache after all OMP sessions are lost at location S0123T4E56F78?
A company deploys a Cisco SD-WAN solution but has an unstable Internet connection. When the link to vSmart comes back up, the WAN Edge router routing table is not refreshed, and some traffic to the destination network is dropped. The headquarters is the hub site, and it continuously adds new sites to the SD-WAN network. An engineer must configure route refresh between WAN Edge and vSmart within 2 minutes. Which configuration meets this requirement?
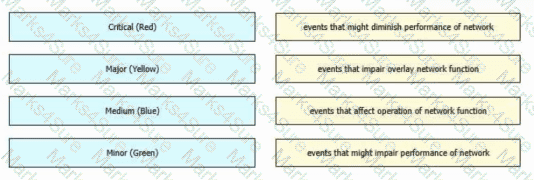
An administrator is configuring the severity level on the vManage NMS for events that indicate that an action must be taken immediately. Which severity level must be configured?
An engineer is configuring a data policy IPv4 prefixes for a site WAN edge device on a site with edge devices. How is this policy added using the policy configuration wizard?
An engineering team must prepare a traffic engineering policy where an MPLS circuit is preferred for traffic coming from the Admin VLAN Internet should be used as a backup only. Which configuration fulfill this requirement?
A)
B)
C)
D)
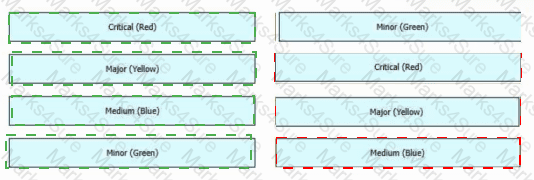
Drag and drop the alarm states from the left onto the corresponding alarm descriptions on the right.
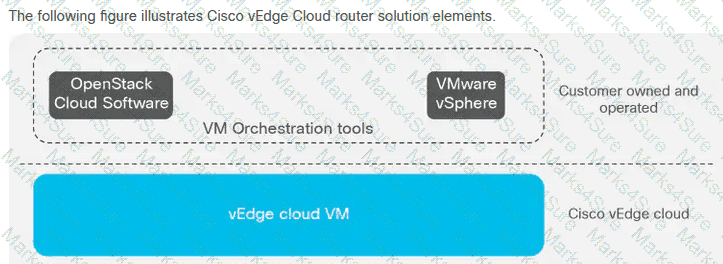
Which two products that perform lifecycle management for virtual instances are supported by WAN Edge cloud routers? (Choose two.)
An engineer wants to automate the onboarding process for a WAN Edge router with vManage. Which command will accomplish this?
Which two sets of identifiers does OMP carry when it advertises TLOC routes between WAN Edge routers? (Choose two.)
When redistribution is configured between OMP and BGP at two Data Center sites that have Direct Connection interlink, which step avoids learning the same routes on WAN Edge routers of the DCs from LAN?