An email administrator must configure DLP policies on the Cisco Secure Email Gateway. The DLP policies must be added to the default outgoing mail policy. How is this task accomplished?
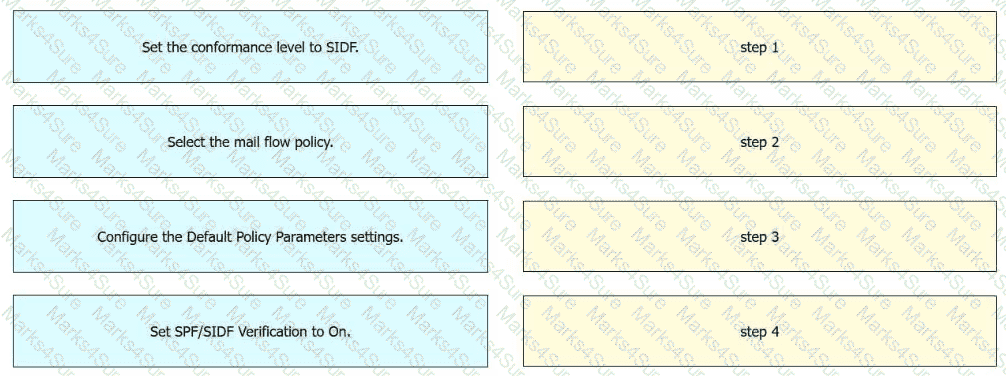
An engineer must enable SIDF for a mail flow policy on an incoming listener in Cisco Secure Email Gateway. Drag and drop the actions from the left into the sequence on the right to meet the requirement.
Which Cisco Secure Email Threat Defense visibility and remediation mode is only available when using Cisco Secure Email Gateway as the message source?
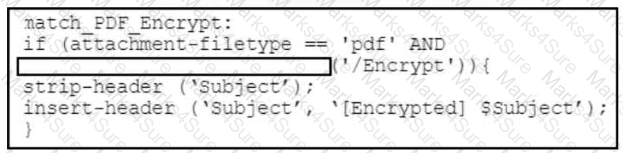
Refer to the exhibit. A security engineer must create a message filter on a Cisco Secure Email Gateway to scan all incoming emails for encrypted PDF files. Which code snippet completes the message filter?
An organization wants to designate help desk personnel to assist with tickets that request the release of messages from the spam quarantine because company policy does not permit direct end-user access to the quarantine. Which two roles must be used to allow help desk personnel to release messages while restricting their access to make configuration changes in the Cisco Secure Email Gateway? (Choose two.)
The CEO added a sender to a safelist but does not receive an important message expected from the trusted sender. An engineer evaluates message tracking on the Cisco Secure Email Gateway appliance and determines that the message was dropped by the antivirus engine. What is the reason for this behavior?
What are the two different phases in the process of Cisco Secure Email Gateway performing S/MIME encryption? (Choose two.)
Which action must be taken before a custom quarantine that is being used can be deleted?
An engineer is configuring a Cisco Secure Email Gateway and needs to reject email messages to a recipient with email address user0516585210@acme.com . Which list contains the allowed recipient addresses?
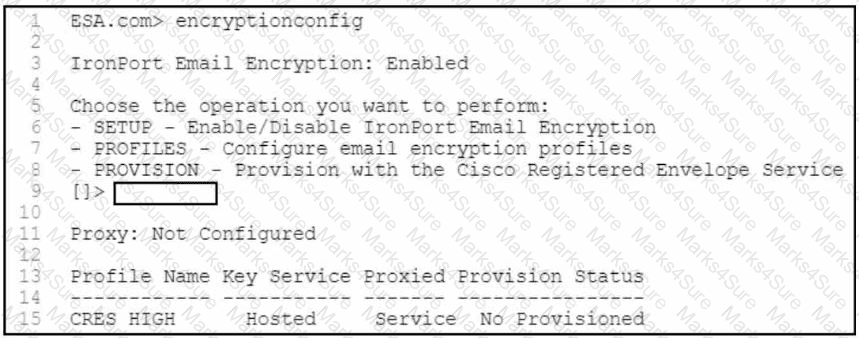
Refer to the exhibit. A security engineer must configure a Cisco Secure Email Gateway to ensure that encryption is enabled and the configured profile is provisioned. Which command must be used?
An organization wants to use its existing Cisco ESA to host a new domain and enforce a separate corporate policy for that domain.
What should be done on the Cisco ESA to achieve this?
An engineer must provide differentiated email filtering to executives within the organization Which two actions must be taken to accomplish this task? (Choose two)
A security engineer wants to ensure that legitimate emails from info@partners.com are not quarantined as spam in Cisco Secure Email. Which action must be taken to meet this requirement?
Which two features of Cisco Email Security are added to a Sender Group to protect an organization against email threats? (Choose two.)
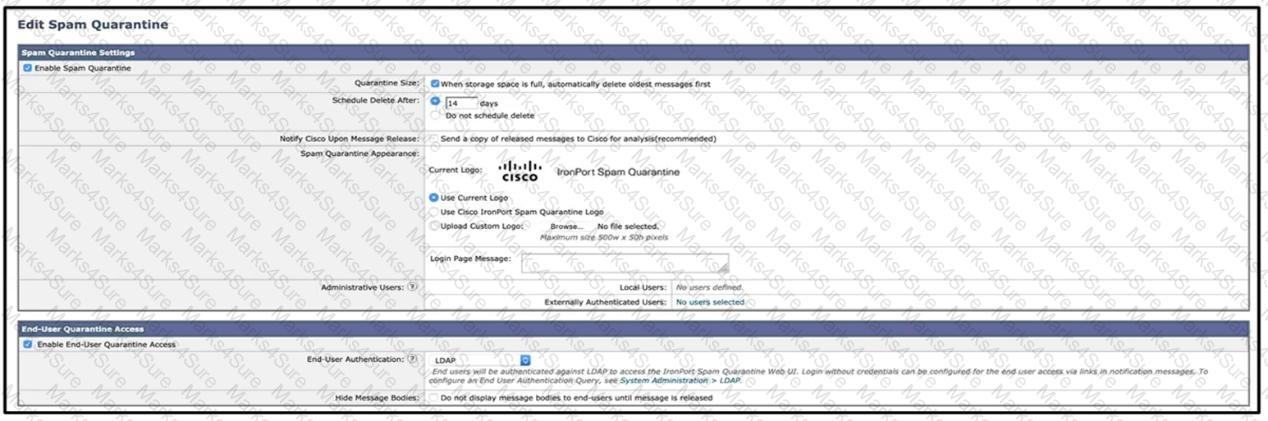
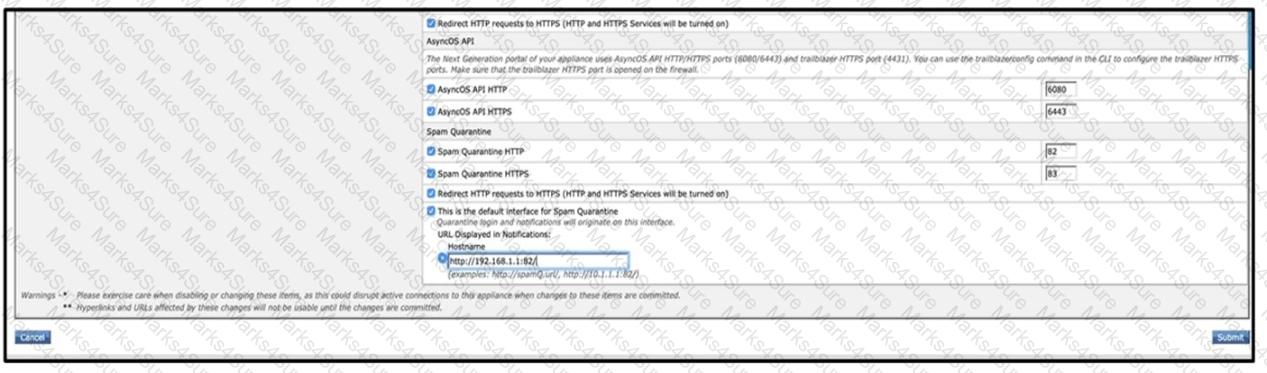
Refer to the exhibits. What must be done to enforce end user authentication before accessing quarantine?
Which of the following two statements are correct about the large file attachments (greater than 25MB) feature in Cisco Secure Email Encryption Service? (Choose two.)
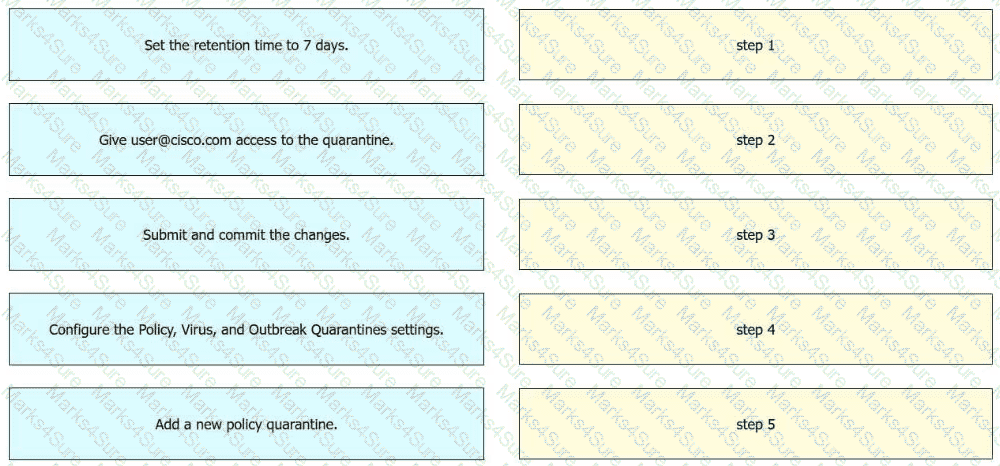
An engineer must configure a policy quarantine in Cisco Secure Email Gateway. The retention time must be 7 days and user@cisco.com must have access to the quarantine. Drag and drop the actions from the left into the sequence on the right to meet the requirements.
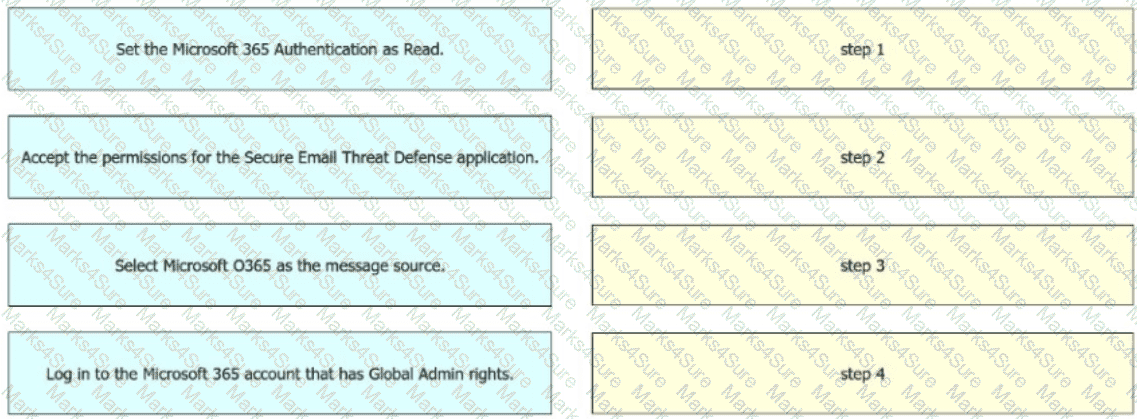
An engineer must configure the message source when integrating Cisco Secure Email Threat Defense with Microsoft 365. The integration must allow visibility but not remediation. Drag and drop the actions from the left into sequence on the right to meet the requirement.
An administrator is trying to enable centralized PVO but receives the error, " Unable to proceed with Centralized Policy, Virus and Outbreak Quarantines configuration as esa1 in Cluster has content filters / DLP actions available at a level different from the cluster level. "
What is the cause of this error?
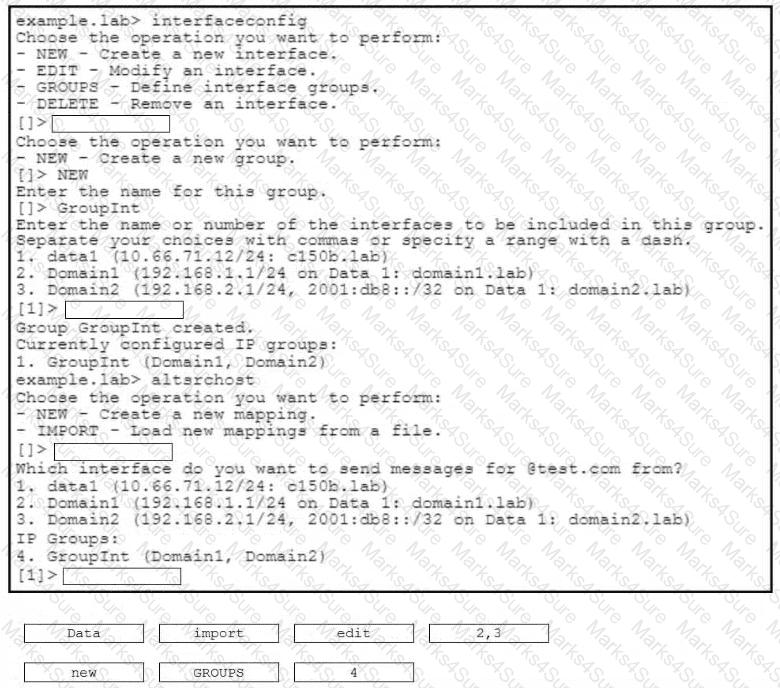
An engineer must configure a virtual gateway on a Cisco Secure Email Gateway to send email for a group named Grouplnt. Grouplnt is part of these domains:
•domain 1 -lab
•domain2.lab
Drag and drop the code snippets from the right onto the boxes to configure the virtual gateway. Not all options are used.
Which method enables an engineer to deliver a flagged message to a specific virtual gateway address in the most flexible way?
An engineer must modify the altsrchost table on a Cisco Secure Email Gateway Messages destined for a domain named @cisco.com must be mapped to Newlnterface with an IP address of 10.10.10.1. What must be added to the table?
Which component must be added to the content filter to trigger on failed SPF Verification or DKIM Authentication verdicts?
Which of the following two steps are required to enable Cisco SecureX integration on a Cisco Secure Email Gateway appliance? (Choose two.)
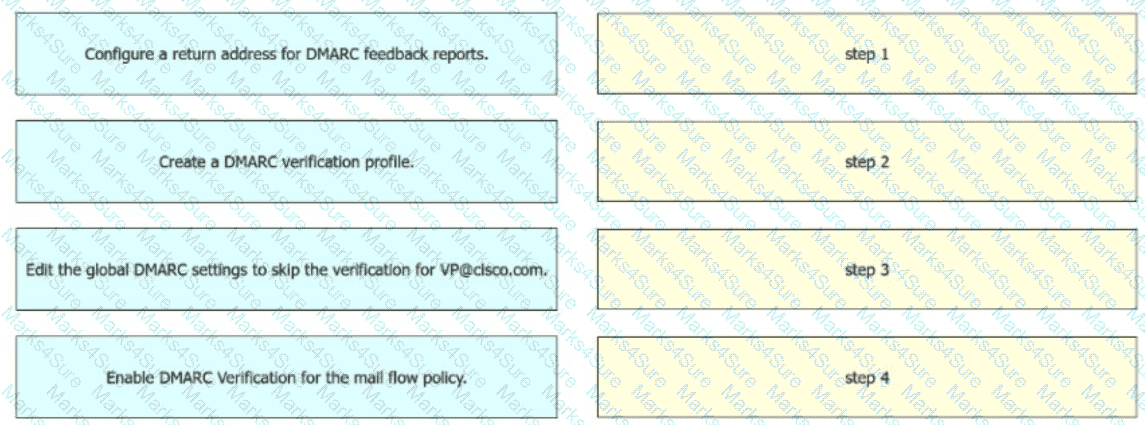
An engineer must configure incoming message verification using DM ARC in Cisco Secure Email Gateway. Emails from VP@cisco.com must skip the verification Drag and drop the actions from the left into the sequence on the right to meet the requirement.
An engineer must configure a local spam quarantine in Cisco Secure Email Gateway These configurations were already performed: •Enable the Anti-Spam feature and configure the quarantine settings •Specify the disk space to allocate to the spam quarantine.
Which two actions must be taken to complete the configuration? (Choose two.)
Which feature must be configured before an administrator can use the outbreak filter for nonviral threats?
A network administrator notices that there are a high number of queries to the LDAP server. The mail logs show an entry “550 Too many invalid recipients | Connection closed by foreign host.”
Which feature must be used to address this?
When virtual gateways are configured, which two distinct attributes are allocated to each virtual gateway address? (Choose two.)
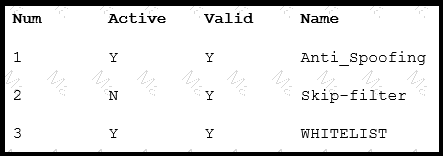
Refer to the exhibit. What is the correct order of c ommands to set filter 2 to active?
An email containing a URL passes through the Cisco ESA that has content filtering disabled for all mail policies. The sender is sampleuser@test1.com, the recipients are testuser1@test2.com, testuser2@test2.com, testuser3@test2.com, and mailer1@te st2.com. The subject of the email is Test Document395898847. An administrator wants to add a policy to ensure that the Cisco ESA evaluates the web reputation score before permitting this email.
Which two criteria must be used by the administrator to achie ve this? (Choose two.)
An engineer is tasked with reviewing mail logs to confirm that messages sent from domain abc.com are passing SPF verification and being accepted by the Cisco ESA. The engineer notices that SPF veri fication is not being performed and that SPF is not being referenced in the logs for messages sent from domain abc.com.
Why is the verification not working properly?
A Cisco Secure Email Gateway administrator must provide outbound email authenticity and configures a DKIM signing profile to handle this task. What is the next step to allow this organization to use DKIM for their outbound email?
A network administrator is modifying an outgoing mail policy to enable domain protection for the organization. A DNS entry is created that has the public key.
Which two headers will be used as matching criteria in the outgoing mail policy? (Choose two.)
Email encryption is configured on a Cisco ESA that uses CRES.
Which action is taken on a message when CRES is unavailable?
A company ' s CFO is requesting the email administrator create an exception for graymail from a certain yoga studio ' s weekly newsletter. Which category of graymail does this fall under?
Which restriction is in place for end users accessing the spam quarantine on Cisco Secure Email Gateway appliances?
Which feature utilizes sensor information obtained from Talos intelligence to filter email servers connecting into the Cisco ESA?
An analyst creates a new content dictionary to use with Forged Email Detection.
Which entry will be added into the dictionary?
When email authentication is configured on Cisco ESA, which two key types should be selected on the signing profile? (Choose two.)
An engineer is testing mail flow on a new Cisco ESA and notices that messages for domain abc.com are stuck in the delivery queue. Upon further investigation, the engineer notices that the messages pending delivery are destined for 192.168.1.11, when they should instead be routed to 192.168.1.10.
What configuration change needed to address this issue?
What is the default port to deliver emails from the Cisco ESA to the Cisco SMA using the centralized Spam Quarantine?
An Encryption Profile has been set up on the Cisco ESA.
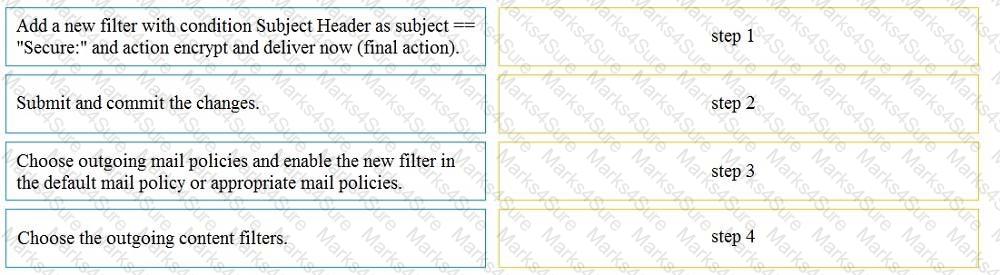
Drag and drop the steps from the left for creating an outgoing content filter to encrypt emails that contains the subject " Secure: " into the correct order on the right.
An engineer must add the user1@cisco.co m with an IP address of 10.1.1.13 to a safelist in Cisco Secure Email Gateway. Which two safelist syntaxes must be configured to meet the requirement? (Choose two.)
When the spam quarantine is configured on the Cisco Secure Email Gateway, which type of query is used to validate non administrative user access to the end-user quarantine via LDAP?