300-910 Implementing DevOps Solutions and Practices using Cisco Platforms (DEVOPS) Questions and Answers
Which approach must be used to integrate DevOps practices into the team structure in an existing organization?
An IT department needs to deploy a new application named ‘Entfin434772390’ across the entire enterprise. The deployment must gradually transfer user traffic from an on older and nearly identical version of the application named ‘Entfin02754932l’. Both versions of the application are running in the production environment.
Which release strategy should be used by the IT department?
A precheck validation is being designed for the network state in a Cl/CD pipeline This design requires:
• the CI/CD pipeline to spin up test instances.
• instances must be used to validate changes.
• changes must be validated prior to a continuous deployment workflow, and
• then push the changes to production
How should the pipeline target the required environment?
Which two characteristics of a build tool that is used in an automated build pipeline? (Choose two.)
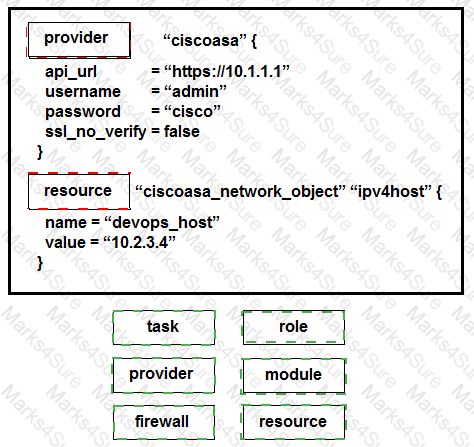
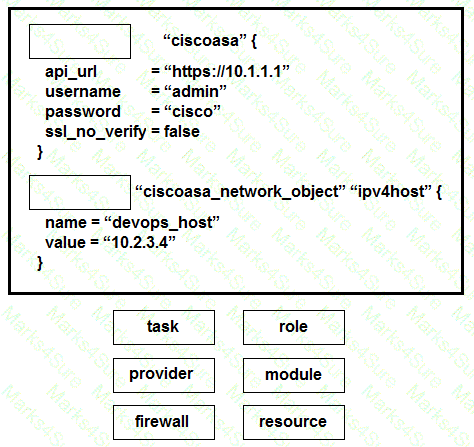
Drag and drop the commands from the bottom onto the correct Terraform code in the exhibit to push a network object to a Cisco ASA Firewall device.
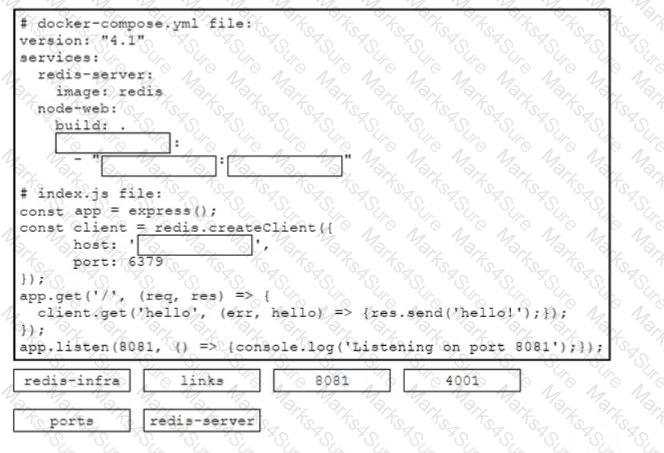
Drag and drop the code snippets from the bottom onto the boxes in the code to complete the docker-compose y ml and the mdex.js files to enable network communication between the containers of a Redis instance and a Node js web application The application must be reachable on the host via port 4001 Not all options are used
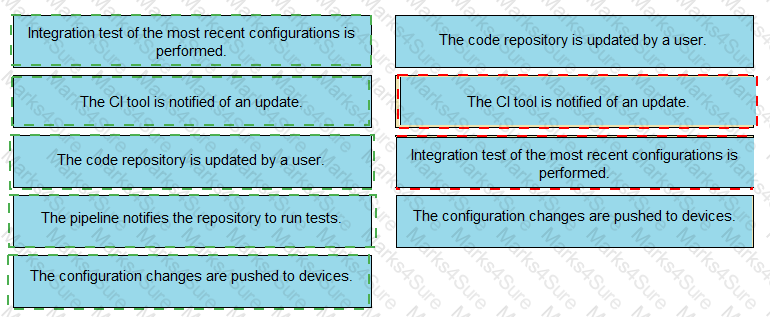
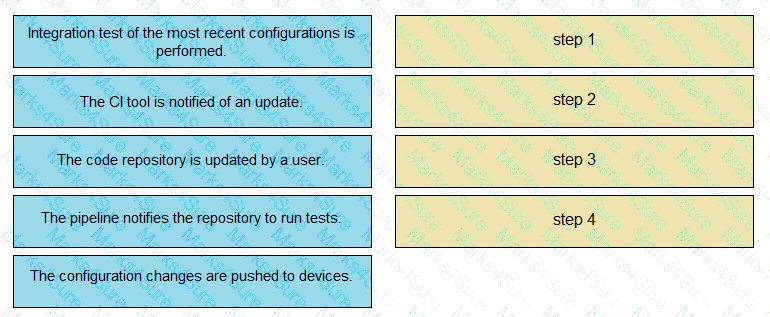
The IaC configuration for an application is being deployed using a CI/CD pipeline. Drag and drop the steps for this pipeline from the left into the correct order that they would be executed on the right. Not all options are used.
What is an advantage of using configuration management tools to automate infrastructure services?
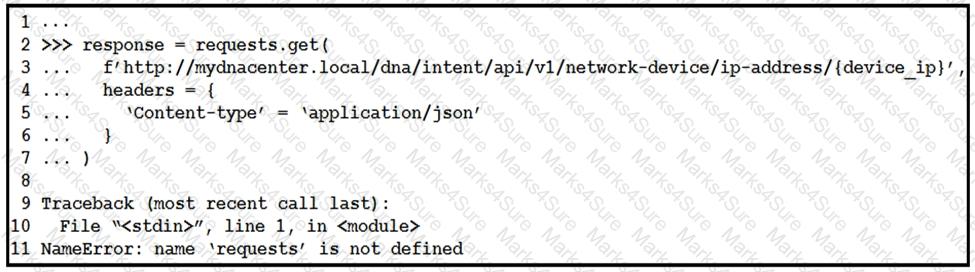
Refer to the exhibit.
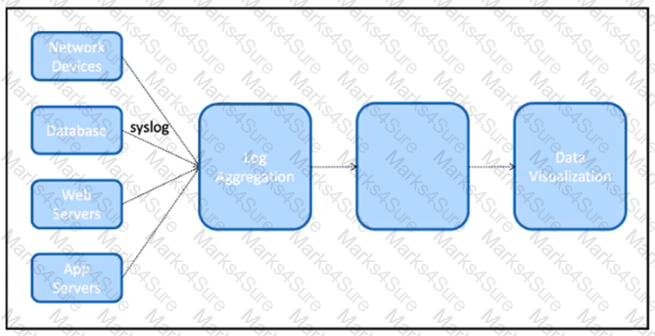
The IT team is creating a new design for a logging system. The system must be able to collect logs from different components of the infrastructure using the SNMP protocol. When the data is collected it will need to be presented in a graphical UI to the NOC team.
What is the architectural component that needs to be placed in the unlabeled box to complete this design?
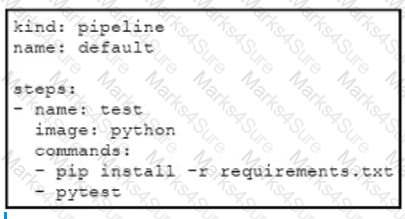
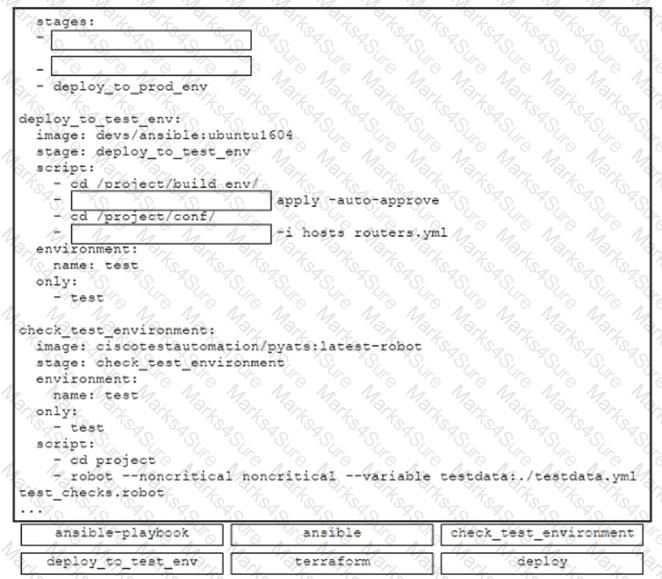
A developer must create a GitLab CI/CD pipeline with these requirements:
• builds an on-demand test environment
• deploys configurations
• verifies the results
Drag and drop the code from the bottom onto the box where the code is missing to complete the GitLab CI/CD pipeline. Not all options are used.
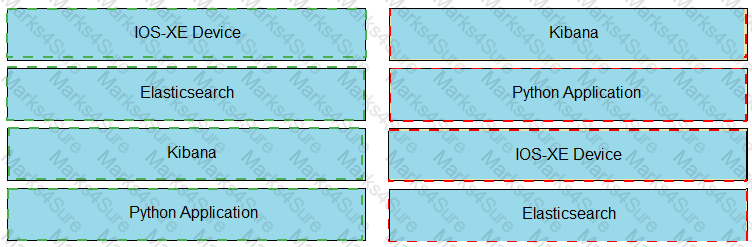
Drag and drop the tools from the left onto the tools function on the right Not all options are used.

When static routes are added to a router in a network using a CI/CD pipeline, an Ansible playbook is used to make these changes. Which steps must be added to the pipeline to validate that the changes have the intended effect on the traffic flow?
To make logging searches more efficient and useful in Kibana, an Administrator wants to implement index patterns around the hostname of some software systems. Where should this be configured?
An application for storing and categorizing has been developed. The application uses dual-factor authentication for user access. After authentication, users can upload sensitive data. The application has been hacked through system exploits and most of the saved data has been lost.
Which action prevents new security threats in the environment?
Which Kubernetes object ensures that each node is limited to running no more than one pod?
A company has a CI/CD pipeline implemented to automate application deployment. An urgent change is required in the production environment. A developer produces and tests the required change in the company ' s environment, but the pipeline fails when pushed.
Which action conforms to the rules of a CI/CD pipeline and enables the pipeline to pass?
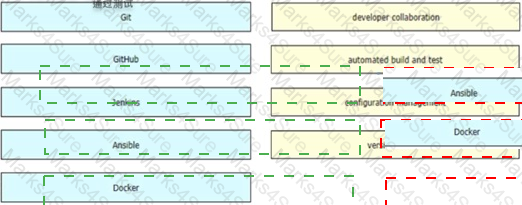
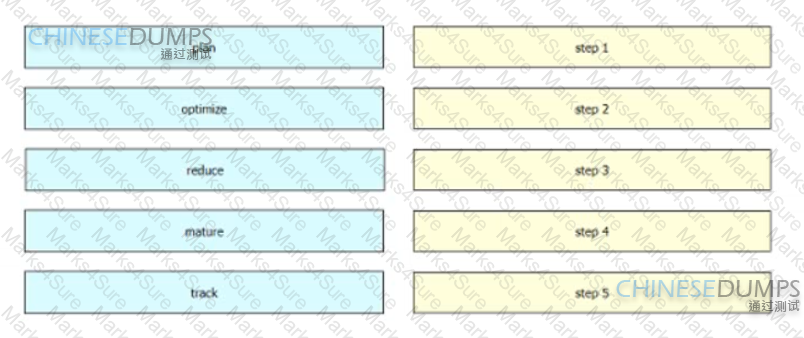
Drag and drop the steps in Garter’s public cloud management framework from the left into the order on the right.
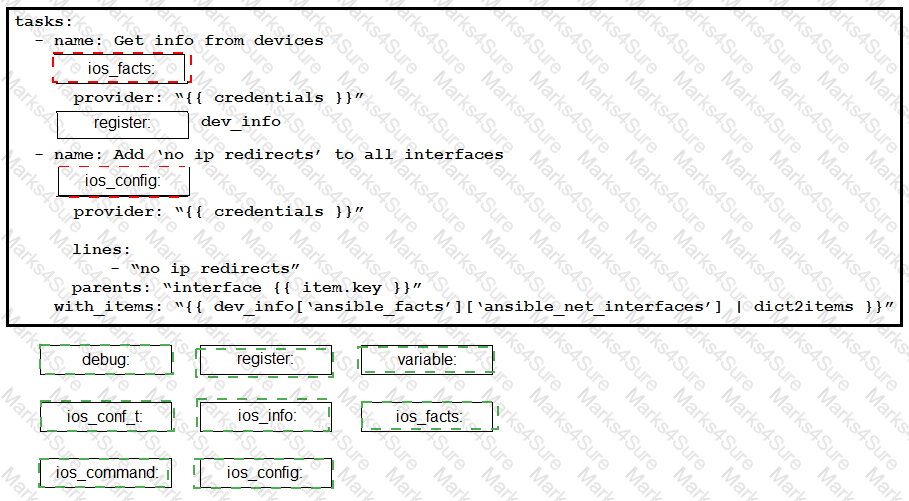
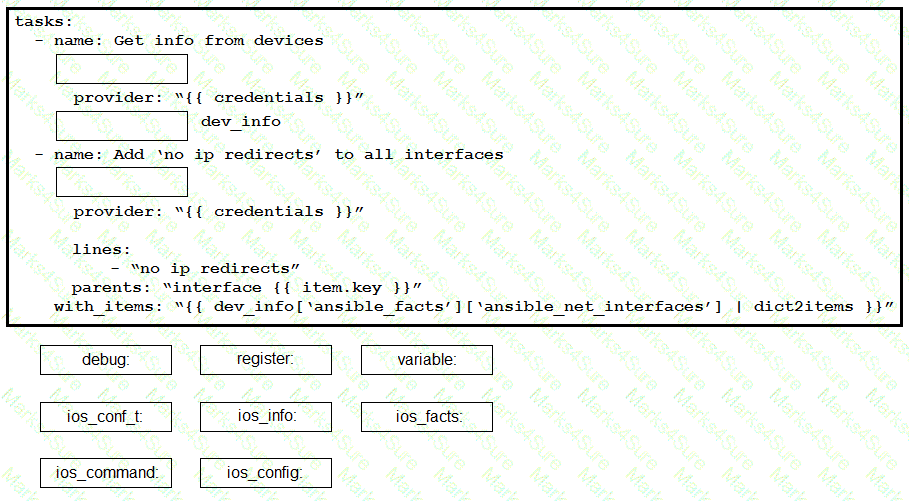
Construct an Ansible script to gather information about target routers and then use it to apply no ip redirects to every interface on each device. Drag and drop the code from the bottom onto the correct location in the exhibit to complete the tasks section of the Ansible playbook so that it accomplishes your goal.
An IT team at a SaaS company has this Cl/CD pipeline
Developers push code to the central repository by using Git.
The code is packaged and sent by an automated process to the staging environment where the tests are executed again automatically
If the automated tests pass in staging the code is pushed to production
Which change improves the Cl/CD pipeline?
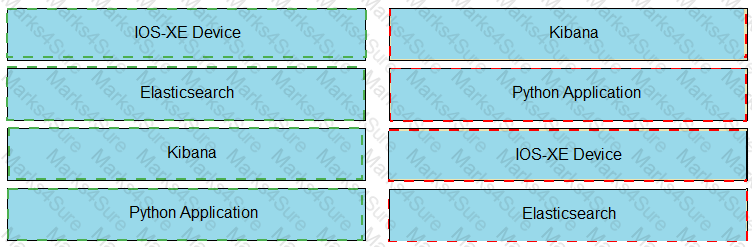
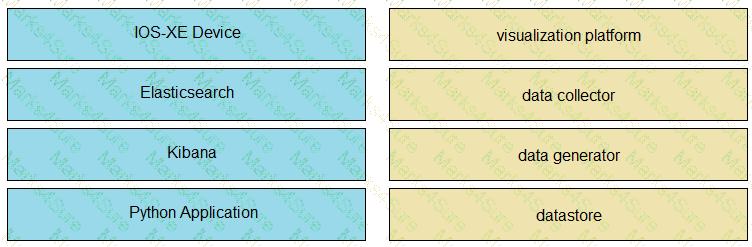
An application is being built to collect and display telemetry streaming data. Drag and drop the elements of this stack from the left onto the correct functions on the right.
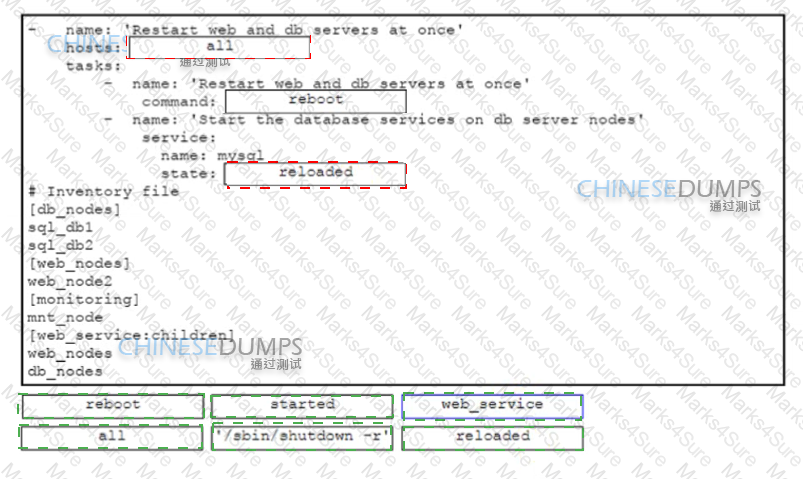
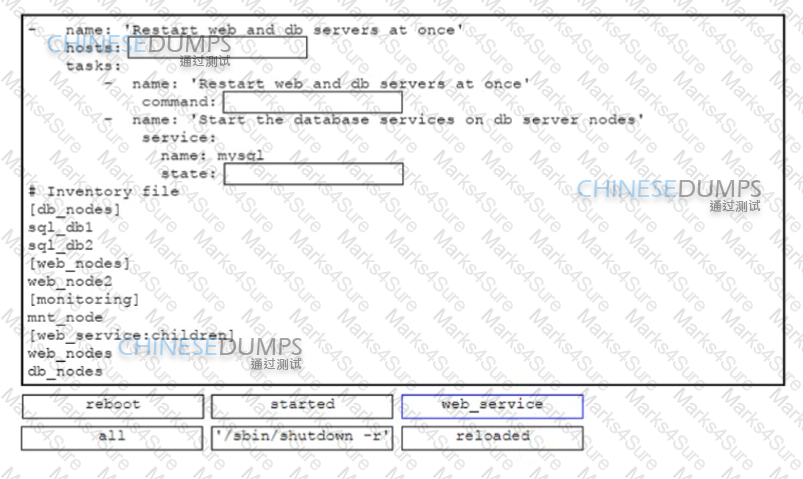
Drag and drop the code snippets from the bottom onto the boxes in the code in the Ansible playbook to restart multiple services in the correct sequence Not all options are used
Refer to the exhibit.
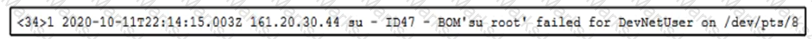
The text represents a syslog message sent from a Linux server to a centralized log system.
Based on the format of the log message, how must the functionality of the log parser be extended to improve search capabilities?
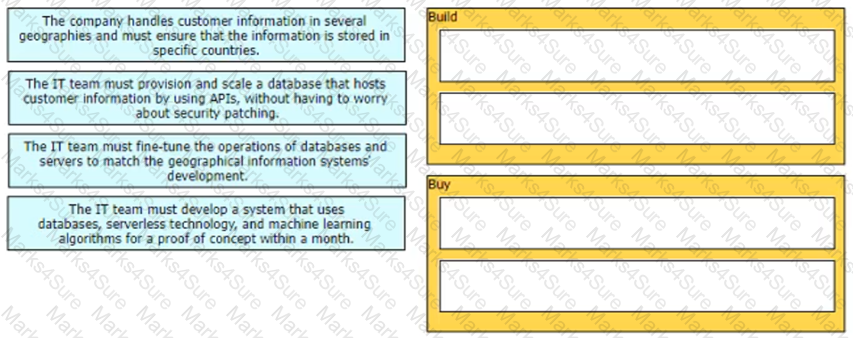
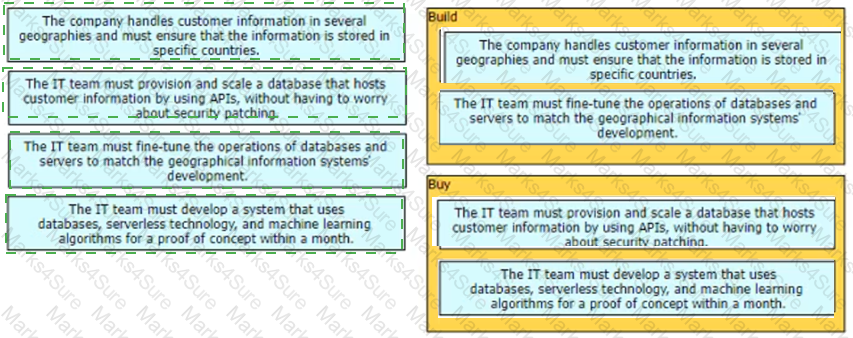
Drag and drop the scenarios from the left onto the cloud strategy categories on the right.
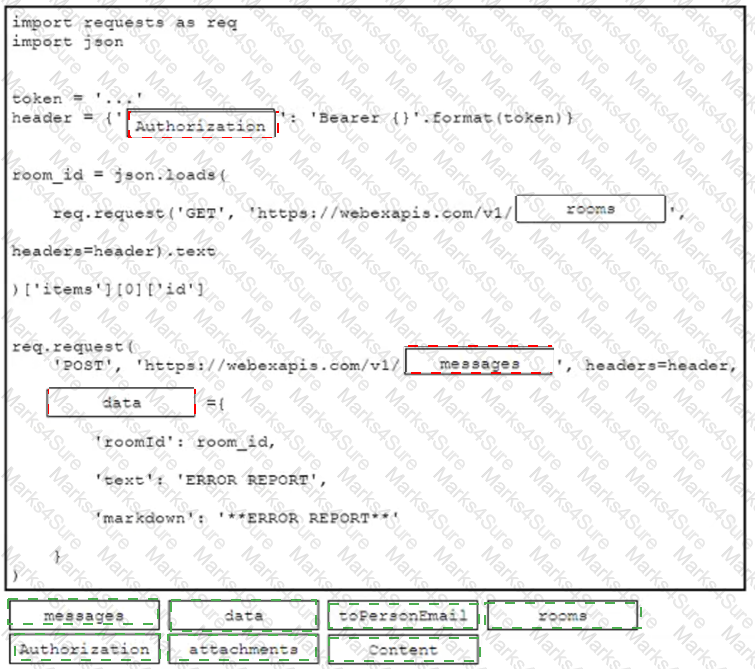
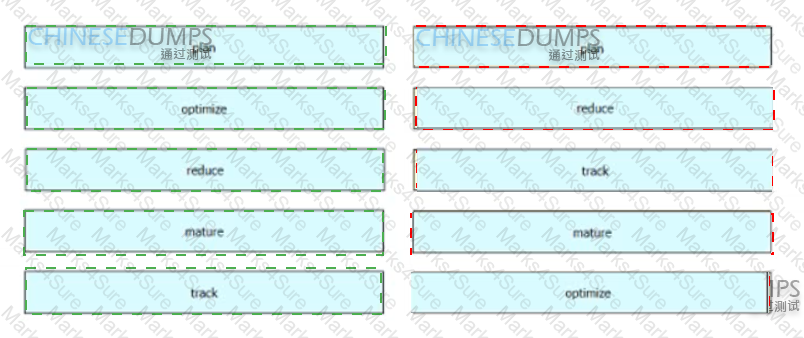
Refer to the exhibit.
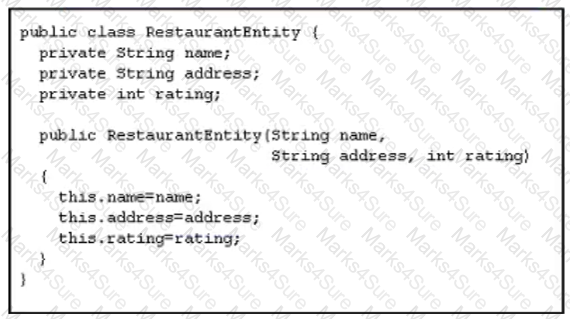
An application has been developed as a fileserver. To create this application as a fileserver. the class is used to store data in an SQL database.
Which two steps help minimize the risk of attack and compromise of the application? (Choose two.)
A three-tier web application must be moved to containers. A webserver is already in place, and the middleware container can talk to a central database server. The hostname of the database server is known, but the name of the middleware server must be provided to the webserver.
In which file should the name of the middleware server be configured?
Which two practices help make the security of an application a more integral part of the software development lifecycle? (Choose two.)
Which type of security testing should be performed as a part of a CI/CD pipeline by analyzing the source code itself without compiling the code into a running executable?
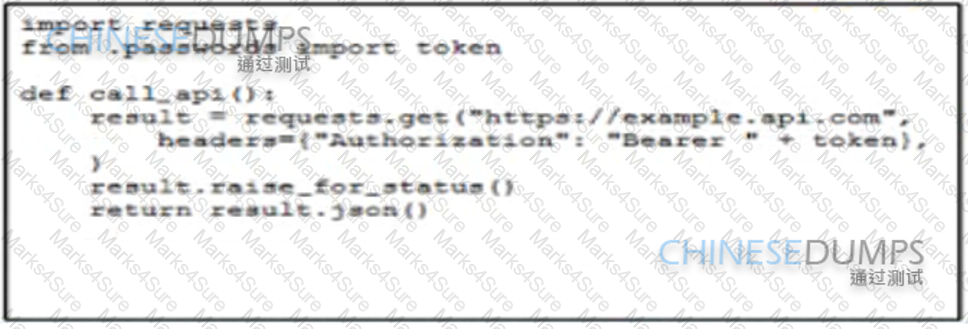
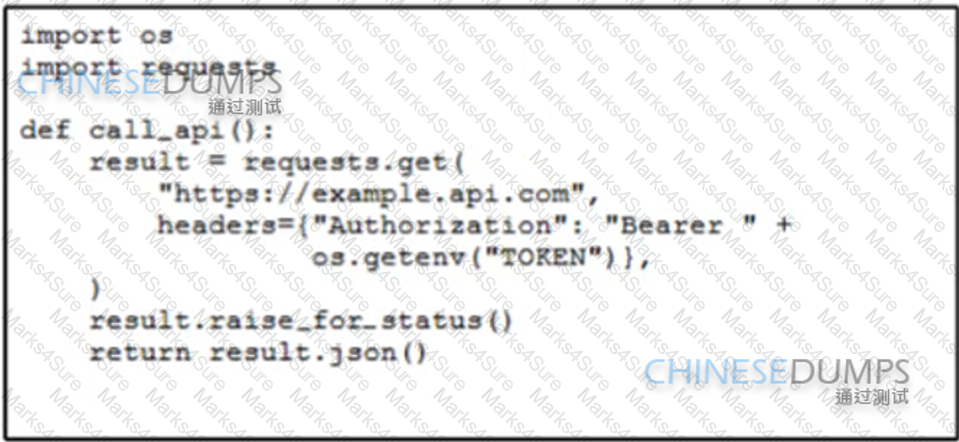
An engineer is developing a script that must call an API using a static Bearer token Which solution securely protects the credentials from being retrievable from the source code?
A)
A)
B)
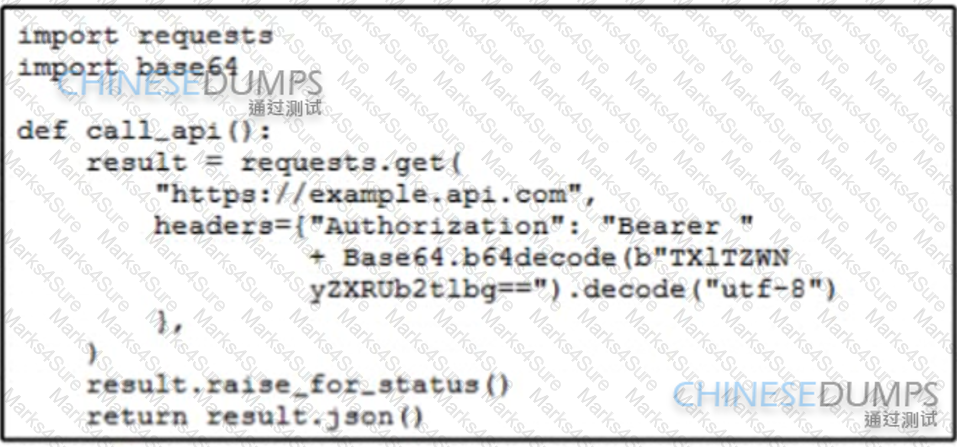
C)
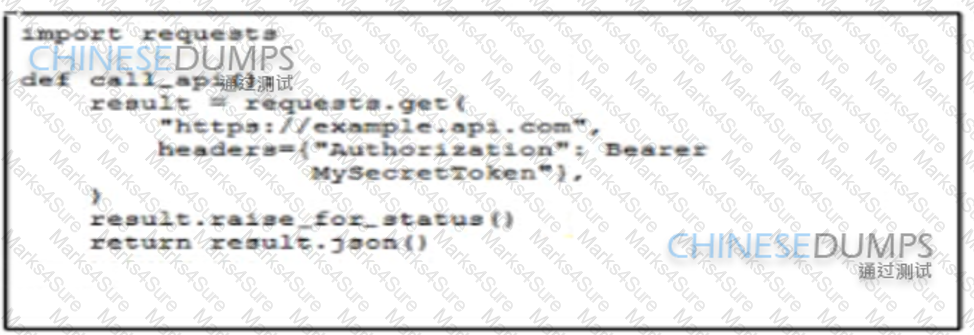
D)