Refer to the exhibit.
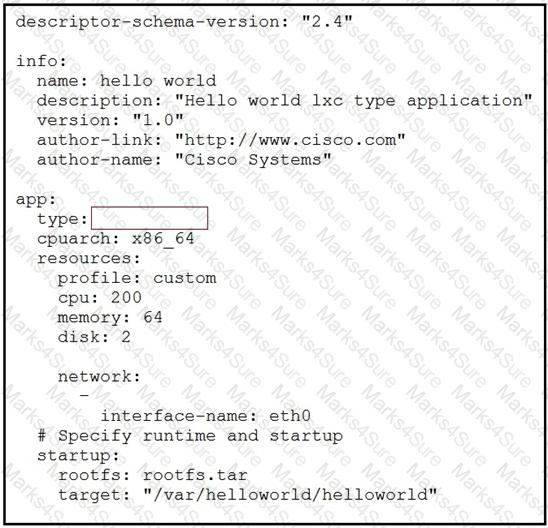
While troubleshooting an error on an application descriptor for a Docker app in Cisco IOx (package.yaml), the app type appears to be missing. Which app type must be added to the snippet to resolve the issue?
Refer to the exhibit.

The red line represents the energy consumption of an industrial machine. Which two statements about the graphs are true? (Choose two.)
A company is collecting data from several thousand machines globally. Which software component in the overall architecture is the next destination of the dataflow after the data has been gathered and normalized on the edge data software?
As part of an IoT project, an organization is developing an application that will share multiple clients using a REST API.
Based on the software development process, what are two valid technical activities that can be suggested to secure the REST API that is developed during the development of the software? (Choose two.)
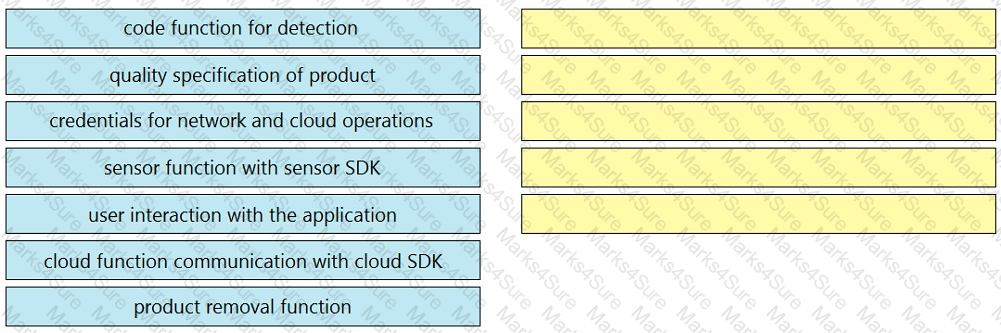
An application needs to calculate if the product meets a determined quality specification, activate an automation to remove poor quality products, and report detailed results back to the cloud. All data are captured from an application that is connected to a sensor. Using the SDK of the cloud provider, drag and drop the tasks that must be completed from the left to the right. Not all options are used.
Refer to the exhibit.
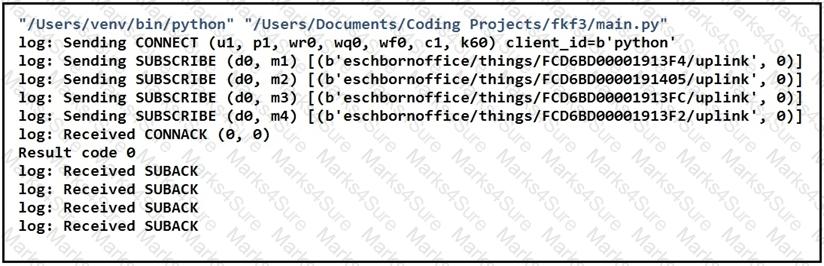
Which two statements about MQTT messaging are true? (Choose two.)
Which data visualization technique should be used to represent an important single metric on a dashboard?
Which method defines the integration of Cisco Industrial Network Director with the Cisco identity Service Engine?
Refer to the exhibit.
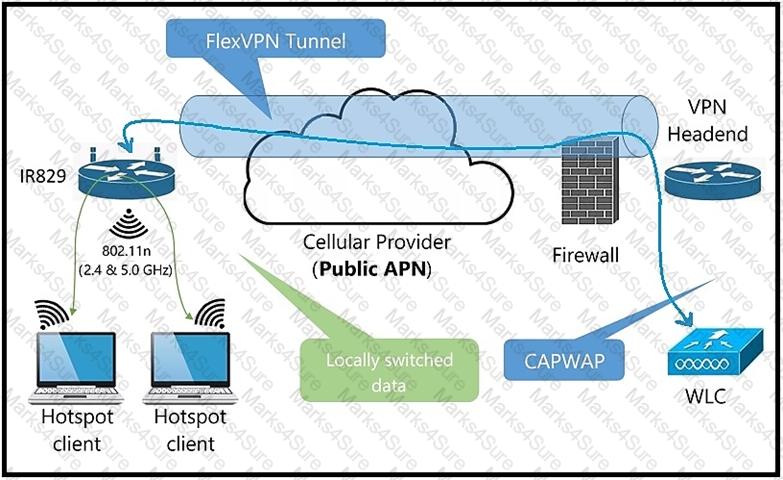
Which protocol is used to make a FlexVPN connection from a Cisco IR829 router to a headend router?
Mosquitto was installed correctly on the Cisco IR829 router as a Cisco IOx application. When the sensor is connected to the broker on the Cisco IR829 router with the default port, the connection is refused (Error Code 5).
Which action should be done to resolve the issue?
Which two data sources are used with a visualization tool such as Grafana? (Choose two.)
An IoT engineer is responsible for security at an organization. Humans and machines need to be allowed to access services like database or compute on AWS. The engineer decides to implement dynamic secrets.
Which method helps to get this implementation accurate from a security point of view?
Which two statements about how to provision and manage data originators in a cloud environment are true? (Choose two.)
When an RS232 device is connected to a Cisco IR829 router, the data collected is not being parsed correctly by the edge application.
Which two steps should be taken to troubleshoot the issue? (Choose two.)