Which process allows continuous IP address retention in a wireless network during roaming?
Which result is produced using a power ratio of 10:1 in standard decibel calculations?
Exhibit:
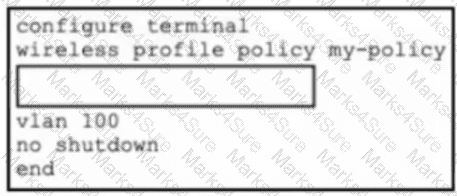
Refer to the exhibit. An enterprise is deploying Cisco Catalyst 9800 WLCs and is using Catalyst Center as the management platform to oversee wireless access policies. To meet the organization's compliance requirements, all wireless endpoints must be evaluated with security posture validation before gaining access. Which set of CLI commands must be added to the box in the code to complete the configuration?
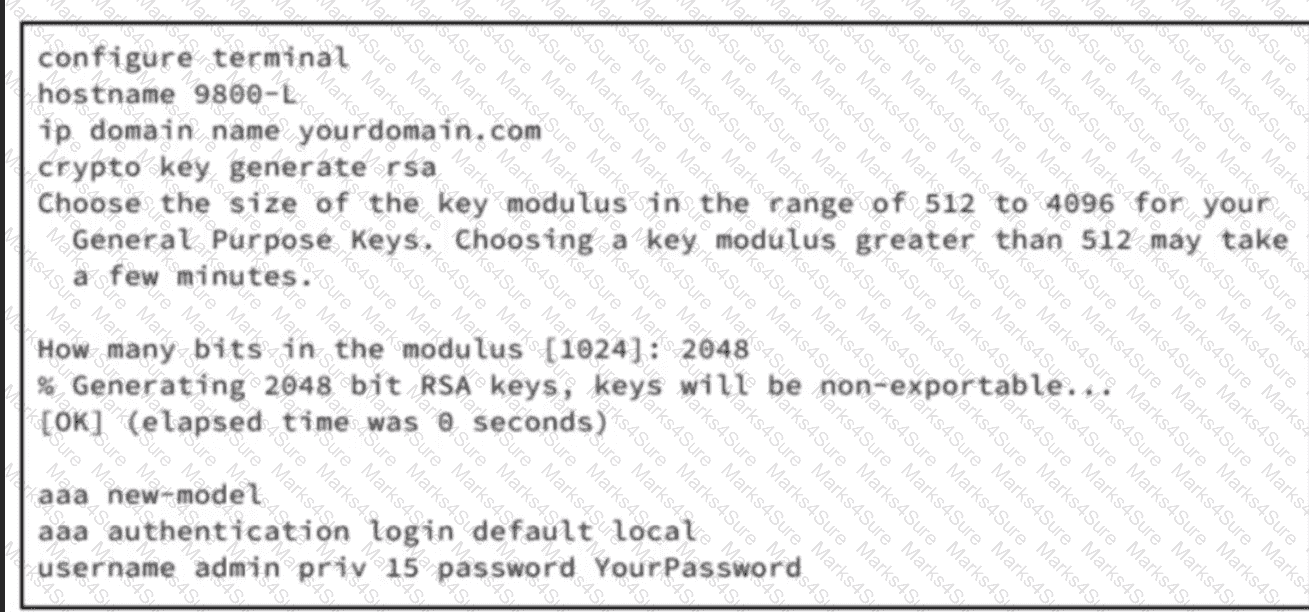
Refer to the exhibit. An engineer is preparing a Cisco 9800-L WLC for deployment in a sensitive area. Only encrypted remote management via SSH is allowed, and all other VTY access methods must be disabled. The 9800-L WLC will be part of a larger deployment, and an external audit will check for any unencrypted management protocols. According to the requirements, only SSH is allowed for remote CLI sessions. Which set of commands must be executed to complete the Cisco IOS XE CLI configuration on the WLC?
Refer to the exhibit.
import requests
import json
API_ENDPOINT = "https://your-api-server.com/api/v1/devices/wireless"
AUTH_TOKEN = "YOUR_SECRET_API_TOKEN"
headers = {
"Accept": "application/json",
"Authorization": f"Bearer {AUTH_TOKEN}"
}
print("Fetching wireless inventory from the API...")
try:
response = requests.get(API_ENDPOINT, headers=headers, timeout=10)
response.raise_for_status()
wireless_inventory_list = response.json()
print("Successfully retrieved and parsed device data.\n")
print("--- Wireless Device Summary ---")
if isinstance(wireless_inventory_list, list) and wireless_inventory_list:
for device in wireless_inventory_list:
mac = device.get("macAddress", "N/A")
ip = device.get("ipAddress", "N/A")
print(f"Device Found - > MAC: {mac}, IP: {ip}")
else:
print("No wireless devices were found in the inventory.")
except requests.exceptions.RequestException as e:
print(f"Error during API request: {e}")
except json.JSONDecodeError:
print("Error: Failed to parse the response from the API. It is not valid JSON.")
A Cisco engineer is analyzing how a dictionary interacts with key-value pairs in a Python script that processes device records collected from a wireless controller. The engineer reviews the construction of the script to interpret the sequence used for data extraction. Which element performs the interaction within the script?
A wireless controller is deployed at a branch location to facilitate secure client connectivity. A network engineer configures one WLAN using WPA2 Personal authentication and activates the preshared key method to align with company security policies. Which action must be taken to enable the client to connect to the WLAN?
An engineer has been tasked with configuring a Cisco Catalyst 9100 AP to join a WLC using a static configuration as DHCP and DNS discovery methods are not available. The engineer has set the AP hostname to ‘AP053540555’, and has configured the AP with a static IP address, subnet mask, and default gateway. The engineer must now configure the AP to discover the primary WLC with hostname ‘WLC-PRIMARY’ and IP address ‘192.168.100.10’. Which CLI command must the engineer use on the AP?
An onsite engineer is working to connect devices to the wireless network using central switching in a corporate environment. Security protocols and network-specific settings must be configured as per enterprise policy. After the initial wireless settings are applied on an iOS tablet, the engineer must ensure that VLAN ID 10 is assigned on the client device to complete a successful enterprise Wi-Fi connection. Which action meets this requirement?
A hotel wants to provide guests with wireless connectivity via a captive portal using a Cisco 9800 WLC. The solution must meet these requirements:
• Ensure that guests are redirected to a custom web page for login and after authentication must have only internet access.
• The guest SSID must not require a password and must be visible to all clients.
• Network segmentation between staff and guests is required at the VLAN level.
What must the IT team configure on the WLAN?
A deployment requires that several APs be connected to edge switches, and each AP must support management and guest Wi-Fi traffic. The APs tag guest traffic separately from management, and the organization expects to add more VLANs for IoT and voice soon, so the configuration must support scalability. The security team requires that guest traffic never mix with internal resources. Which port configuration must be used for the switch interfaces that connect to the APs?
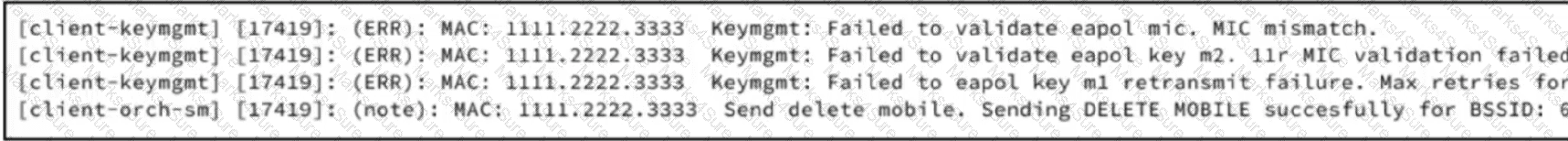
Refer to the exhibit. A network engineer must create a PSK WLAN that will be anchored to the DMZ. After this WLAN is created, users cannot connect to it. Based on the output from the RA trace, which action must the engineer take to resolve the issue?
An IT team is deploying Meraki APs at a remote branch and must ensure that they are automatically assigned to the correct network in the Meraki dashboard. The branch is scheduled to receive 20 new APs, and site connectivity to headquarters was set up. Before shipping the APs, the team must make sure that each one is claimed by the intended network for management and monitoring. Which deployment action must they take before physically connecting the APs?
Which Cisco Ultra-Reliable Wireless Backhaul process enables devices to establish a reliable connection with the next AP along their path before losing connectivity to the current one in a wireless network during roaming?
A wireless administrator must configure detailed and comprehensive monitoring for client devices across branch locations. The team wants to streamline operations for faster response during performance degradation. To support the organization's growth, the administrator needs a centralized reporting platform that displays aggregated data. Which solution must the administrator use to monitor the clients in the network?
A university is deploying Cisco Catalyst 9176 APs at several satellite campuses, each with its own subnet and DNS services. The APs will be shipped with only their MAC addresses preregistered on the WLC. The satellite campuses do not use DHCP option 43, but they have access to a central DNS server. IT staff want APs to discover and join the Catalyst 9800 WLC automatically without site visits. Which solution must the IT staff implement?
A network administrator at a marketing company manages a Cisco Catalyst 9800 Series Wireless Controller running Cisco IOS XE 17.x. The WLAN named XYZ-Guest is set up for visitors, and the administrator wants to implement a web authentication (WebAuth) portal using an external server to manage guest access. To ensure seamless and secure guest authentication, the controller must be configured to use an external WebAuth server for the WLAN. The administrator must configure the XYZ-Guest WLAN to use an external WebAuth server with a parameter map named webauth-ext. Which set of Cisco IOS XE commands must be used?
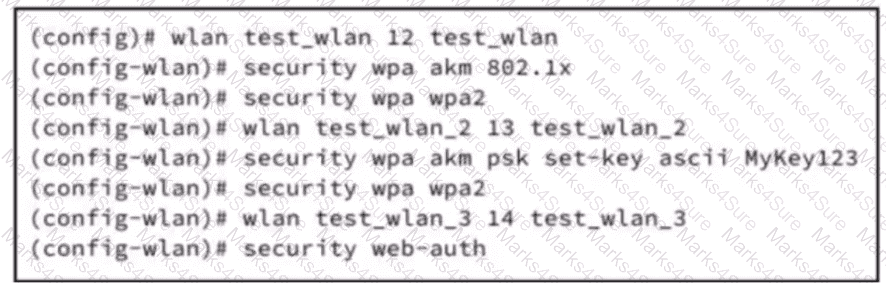
Refer to the exhibit.
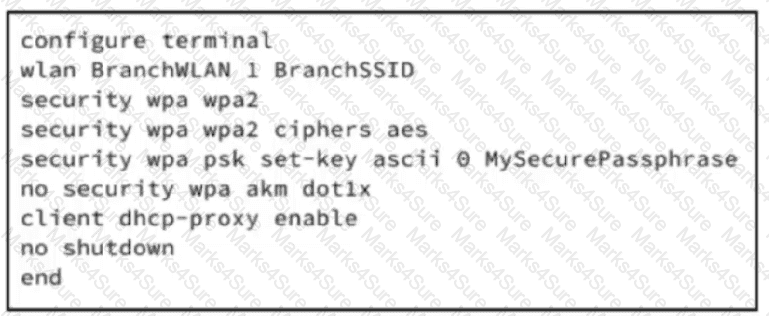
A WLC is deployed at a branch location to facilitate secure client connectivity. A network engineer configures one WLAN using WPA2 Personal passphrase and activates ASCII format key to align with company security policies. Which configuration enables client authentication for this WLAN?
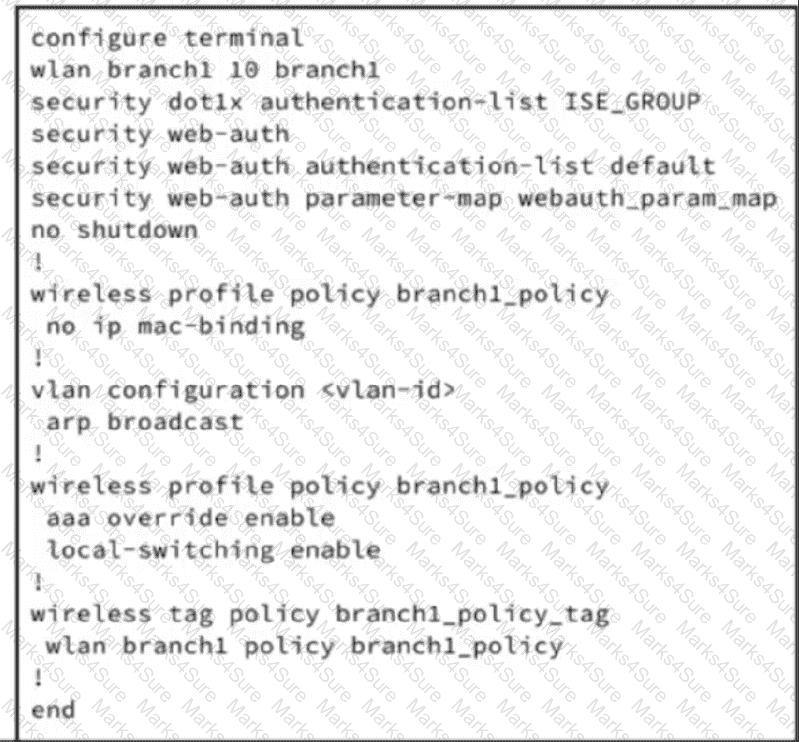
Refer to the exhibit. A wireless controller is deployed at a branch location to facilitate secure client connectivity. A network engineer configures a WLAN using 802.1X to align with company security policies. Which configuration enables client authentication for this WLAN?
Which process enables seamless Layer 2 handoff in a wireless network during roaming?
A business is deploying Cisco Catalyst 9100 APs managed by Catalyst 9800 WLCs. The IT team needs policies that adapt based on user identity and device posture and also provide visibility into device activity and location. Which configuration meets these requirements?
A managed service is rolling out advanced wireless infrastructure to support an expanding organization with diverse device types. The implementation requires integration of dynamic endpoint profiling for secure access and device classification. According to the baseline deployment with ISE policy sets, the engineering group must enforce access parameters based on device category rules. Which configuration action must be taken to fulfill the initiative?
Refer to the exhibit.
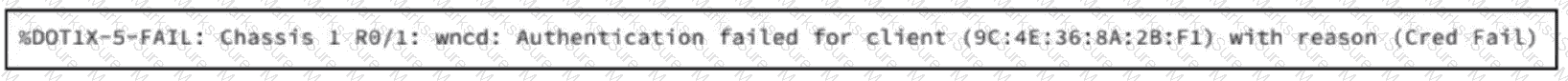 The Catalyst 9800 WLC logs show when a client with MAC address 9C:4E:36:8A:2B:F1 fails to connect to a WLAN configured for Wi-Fi Protected Access 3-Enterprise with 802.1X. Which action must the engineer take to resolve the issue?
The Catalyst 9800 WLC logs show when a client with MAC address 9C:4E:36:8A:2B:F1 fails to connect to a WLAN configured for Wi-Fi Protected Access 3-Enterprise with 802.1X. Which action must the engineer take to resolve the issue?