Which feature works with SSO to continue forwarding packets after a route processor failure until the control plane recovers?
Which two actions are recommended as security best practices to protect REST API? (Choose two.)
When deploying Cisco SD-Access Fabric APs, where does the data plane VXLAN tunnel terminate?
A customer has several small branches and wants to deploy a Wi-Fi solution with local management using CAPWAP. Which deployment model meets this requirement?
An engineer is configuring RADIUS-Based Authentication with EAP. MS-CHAPv2 is configured on a client device. Which outer method protocol must be configured on the ISE to support this authentication type?
Refer to the exhibit.
What does the error message relay to the administrator who is trying to configure a Cisco IOS device?
Which two operational modes enable an AP to scan one or more wireless channels for rogue access points and at the same time provide wireless services to clients? (Choose two.)
Which A record type should be configured for access points to resolve the IP address of a wireless LAN controller using DNS?
Ascriptcontainsthe statement white loop != 999 ’ Which value terminates the loop?
A customer requests a design that includes GLBP as the FHRP. The network architect discovers that the members of the GLBP group have different throughput capabilities. Which GLBP load balancing method supports this environment?
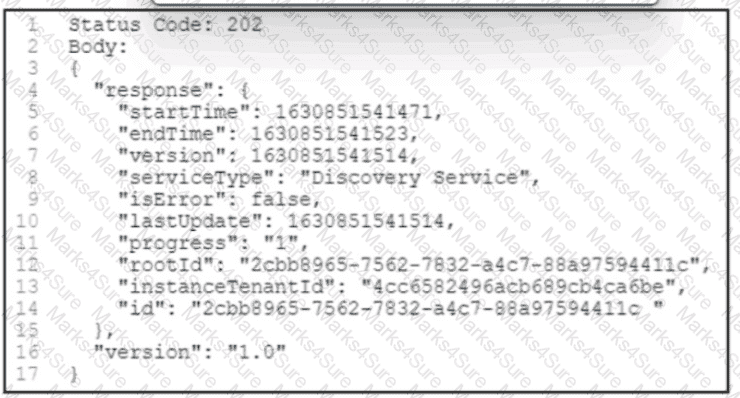
Refer to the exhibit. A POST /discovery request spawns an asynchronous task. After querying for more information about the task, the Cisco DNA Center platform returns the REST API response. What is the status of the discovery task?
Which characteristic applies to the endpoint security aspect of the Cisco Threat Defense architecture?
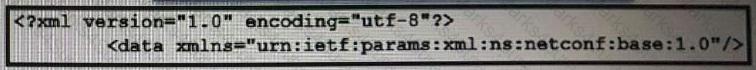
A company recently decided to use RESTCONF instead of NETCONF. and many of their NETCONF scripts contain the operation
An engineer is implementing a new SSID on a Cisco Catalyst 9800 Series WLC that must be broadcast on 6 GHz radios. Users will be required to use EAP-TLS to authenticate. Which wireless Layer 2 security method is required?
Exhibit.
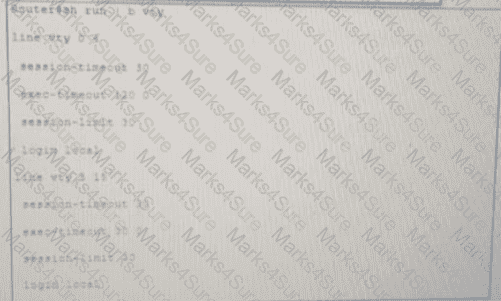
Security policy requires all idle-exec sessions to be terminated in 600 seconds. Which configuration achieves this goal?
Which features does Cisco EDR use to provide threat detection and response protection?
Which type of roaming event occurs when a client roams across multiple mobility groups?