Refer to the exhibit.
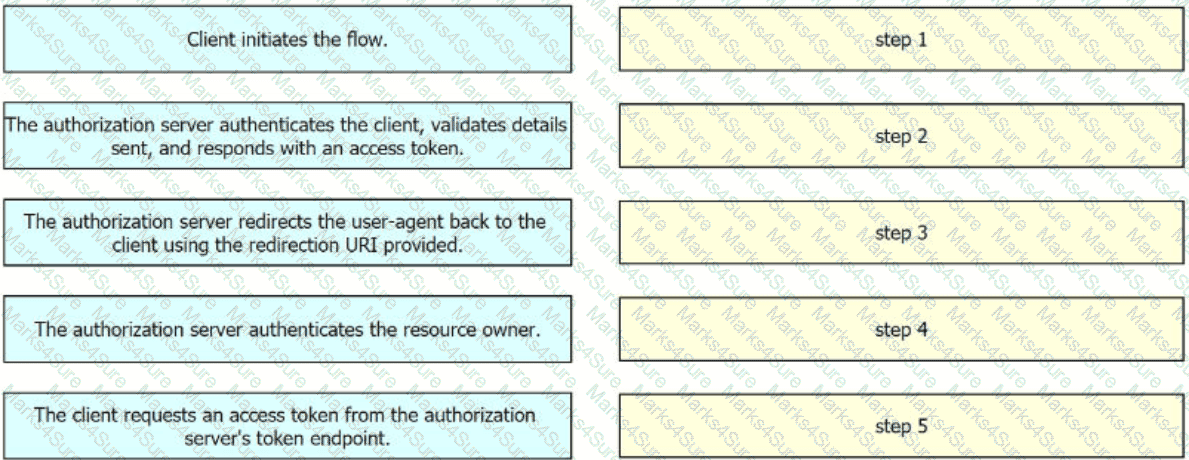
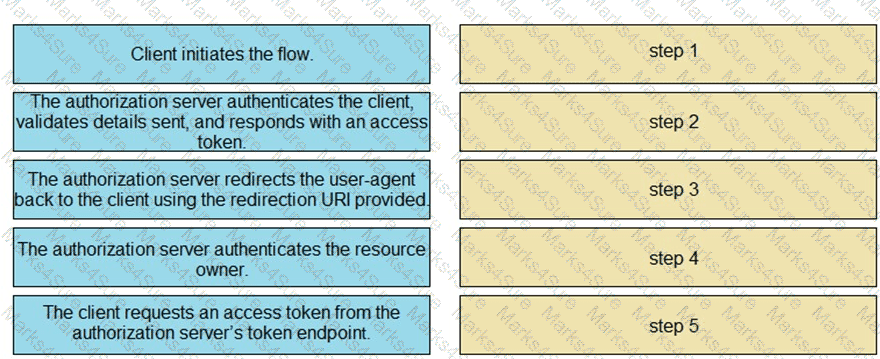
Drag and drop the steps from the left into the order of operation on the right for a successful OAuth2 three-legged authorization code grant flow,
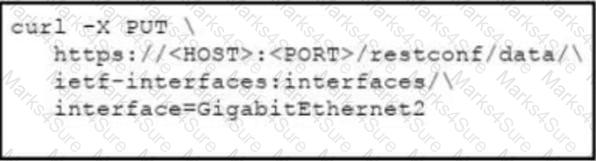
Refer to the exhibit.
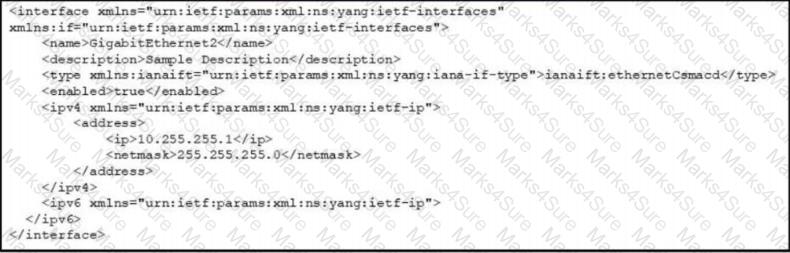
Which cURL request is included in the presented XML as the body of the response?
A)

B)
C)
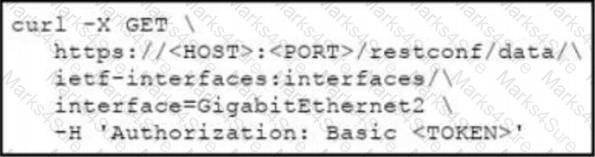
D)
A development team is working on a bug fix in a remote branch named " UXbug000222134 ' and the current working primary branch is named ,prod409024967’ A developer who just joined the learn needs to checkout the remote branch Which Git commands must be used?
A)
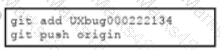
B)
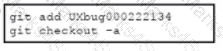
C)
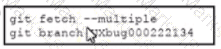
D)
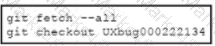
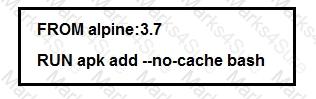
Refer to the exhibit.
The cisco_devnet Docker swarm service runs across five replicas The development team tags and imports a new image named devnet ' test 1 1 and requests that the image be upgraded on each container There must be no service outages during the upgrade process Which two design approaches must be used? (Choose two.)
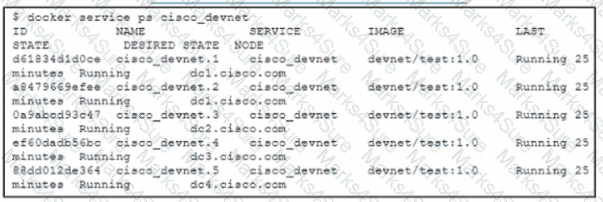
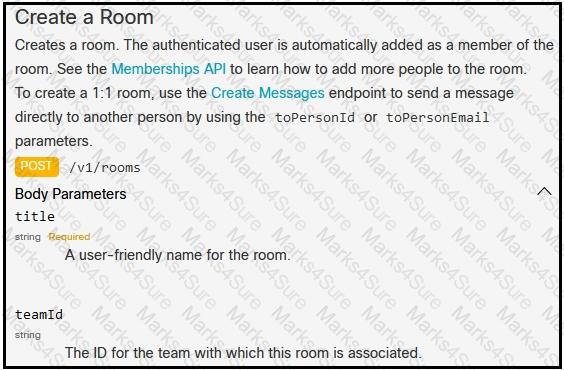
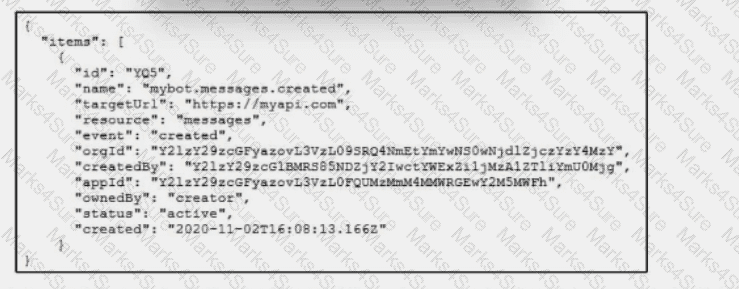
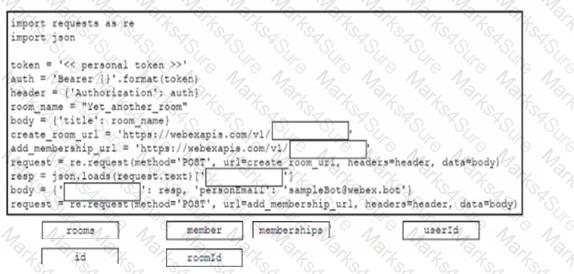
Refer to the exhibit. Which snippet creates a Webex Teams space and adds the users in the variable user list to that space?
A)
B)

C)
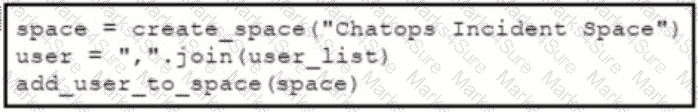
D)
When an application is designed that requires high availability, what is a reason to use a cross-region cloud?
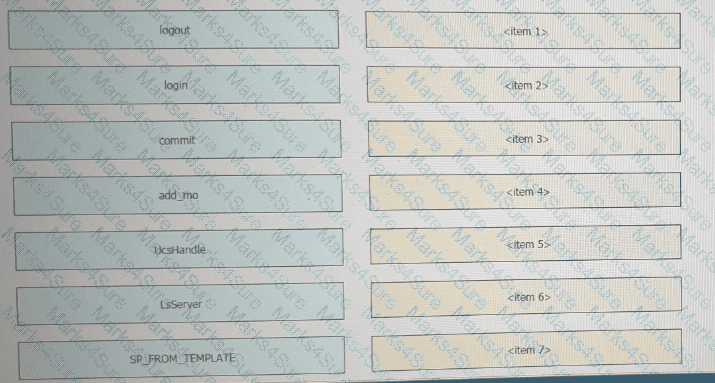
DRAG DROP
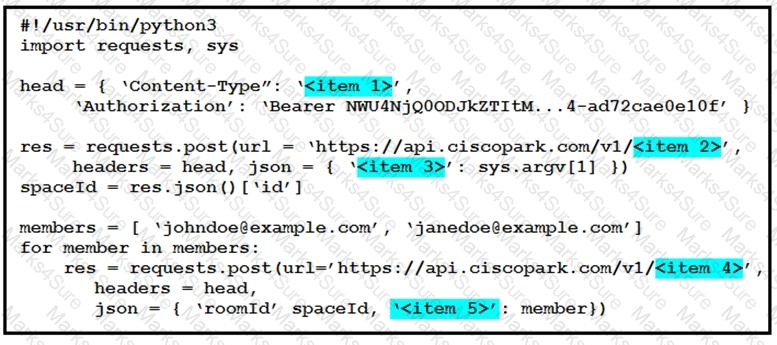
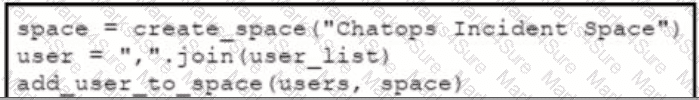
Refer to the exhibit above and click on the resource tabs in the top left corner to view resources to help with this question.
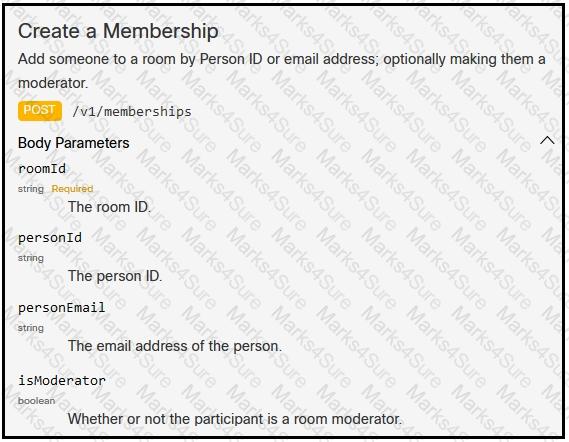
A developer is creating a Python Script that will use the Webex Teams REST API to automatical ly create a new collaboration space with him and his team leads on-demand via a Linux terminal command. Drag and drop the code snippets from the left onto the numbers on the right that match the missing sections in the exhibit to complete the script. Not a ll code snippets are used.
What is a benefit of running multiple instances of a back-end service and using load balancing to distribute the communication between the front-end and back-end services?
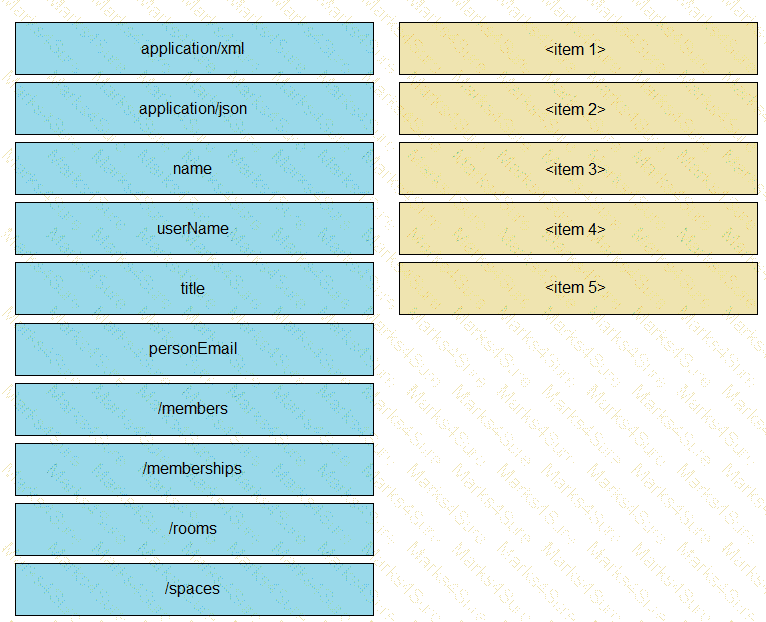
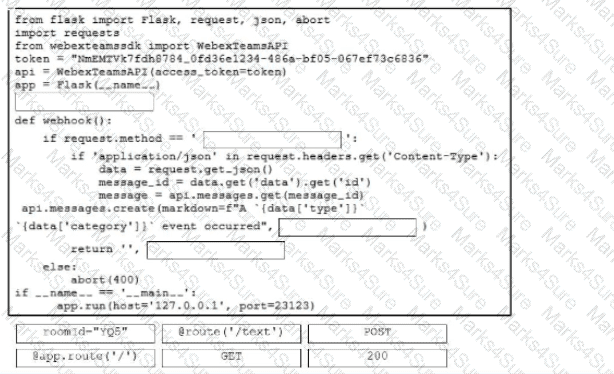
Refer to the exhibit. Drag and drop the code snippets from the bottom onto the blanks in the Python script to create messages in a Cisco Webex room using the Webex API. Not all options are used.
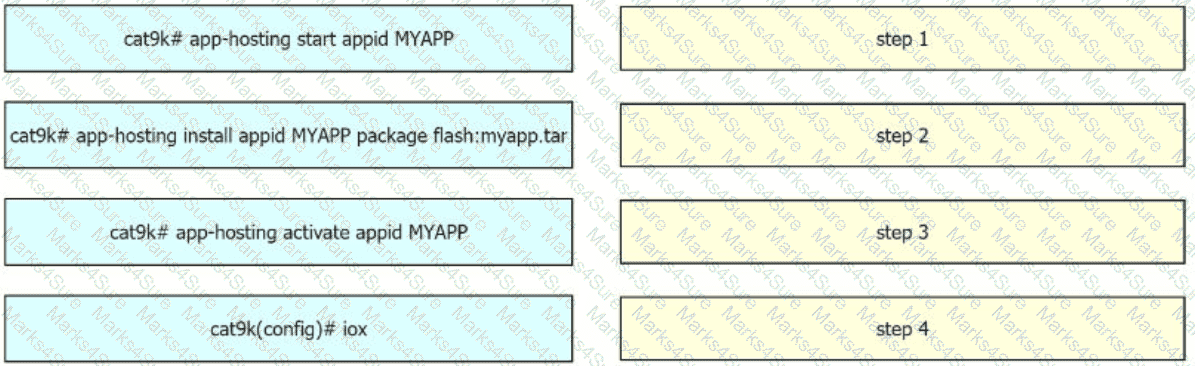
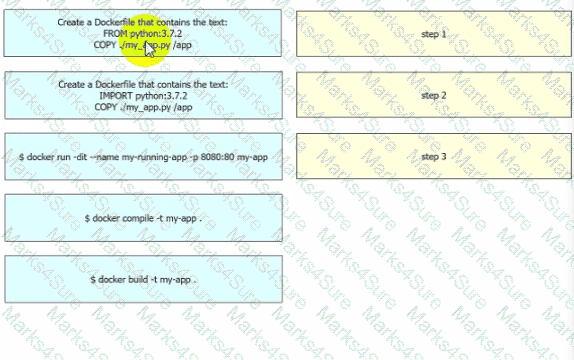
Drag and drop the steps from the left into the order on the right to configure and install a container on a Cisco Catalyst 9000 Series Switch.
A developer needs to configure an environment to orchestrate and configure. Which two tools should be used for each task? (Choose two.)
Which two gRPC modes of model-driven telemetry are supported on Cisco IOS XE Software? (Choose two.)
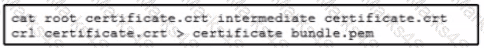
An application requires SSL certificates signed by an intermediate CA certificate. The crt files must be available to the application:
• The root CA certificate is root_certrficate.crt.
• The intermediate CA certificate is intermediate_certificate.crt
• The application-specific SSL certificate is crt_certificate.crt.
Which Bash command outputs the certificate bundle as a .pern file?
A)

B)
C)

D)

A container running a Python script is failing when it reaches the integration testing phase of the CI/CD process. The code has been reviewed thoroughly and the build process works on this container and all other containers pass unit and integration testing.
What should be verified to resolve the issue?
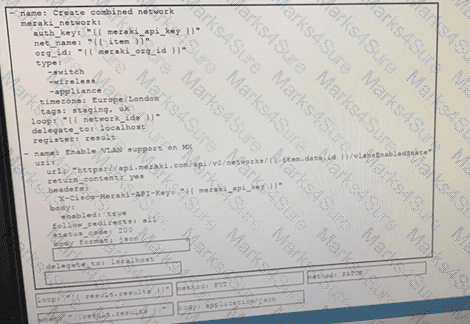
Drag and drop the code from the bottom onto the box where the code is missing on the Ansible task to enable a VLAN on a Meraki MX Device, Not all options are used.
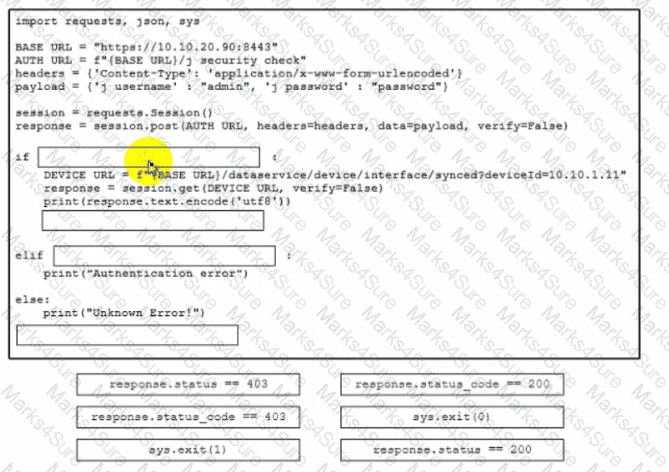
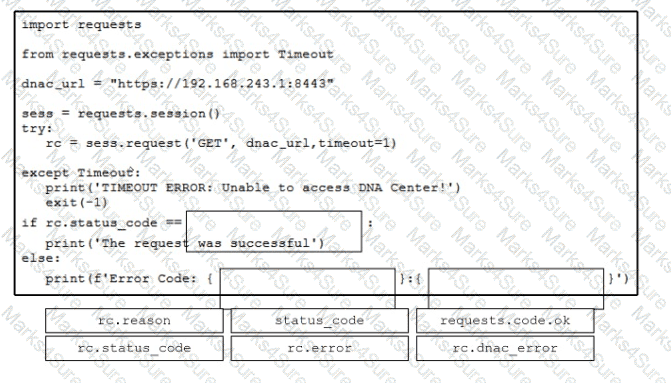
A developer is creating a Python script to analyze errors during REST API call operations. The script will be used with Cisco solution and devices. Drag and drop the code from the bottom to the box where the code is missing to implement control flow for handling unrecoverable REST API calls. Not all options are used.
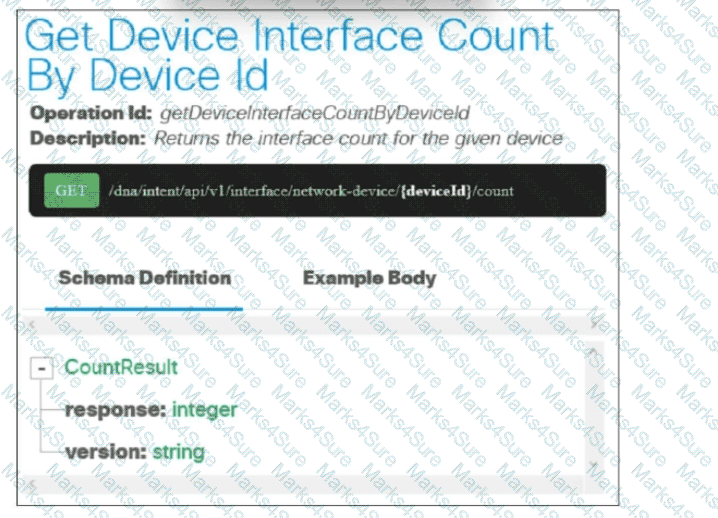
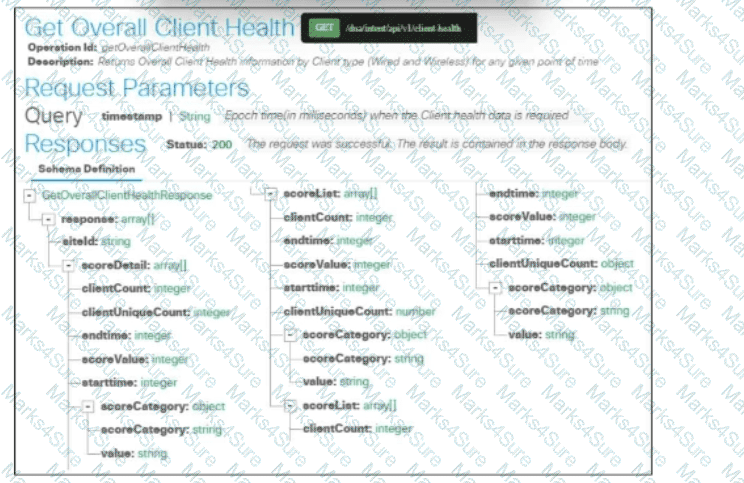
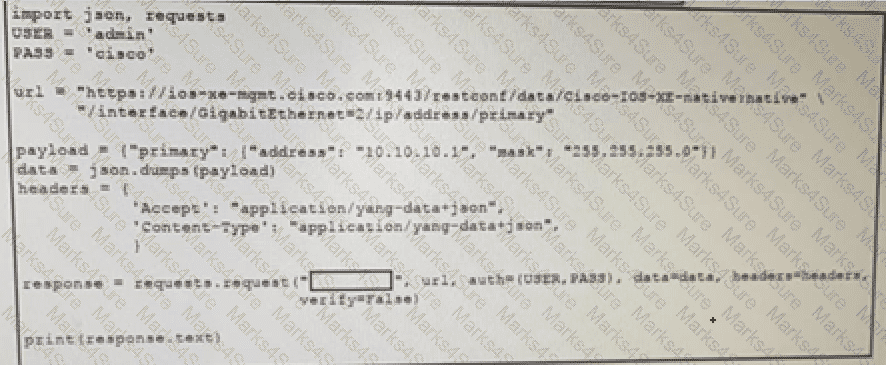
Refer to the exhibit.
Refer to the exhibit An application hosting server with the local data center is experiencing large amounts of traffic from enclusers. A developer must optimize this API server to reduce the toad on its host. What are two ways to optimize this code through HTTP cache controls? (Choose two.)
Include the " ETag " header in the API response.
How does the use of release packaging allow dependencies to be effectively managed during deployments?
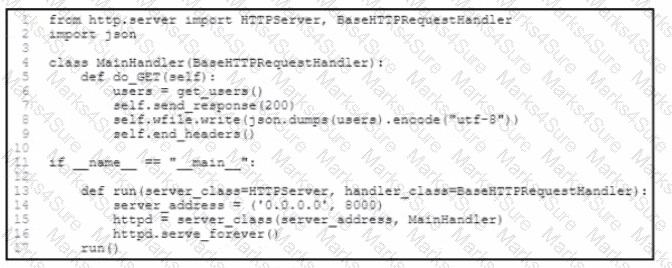
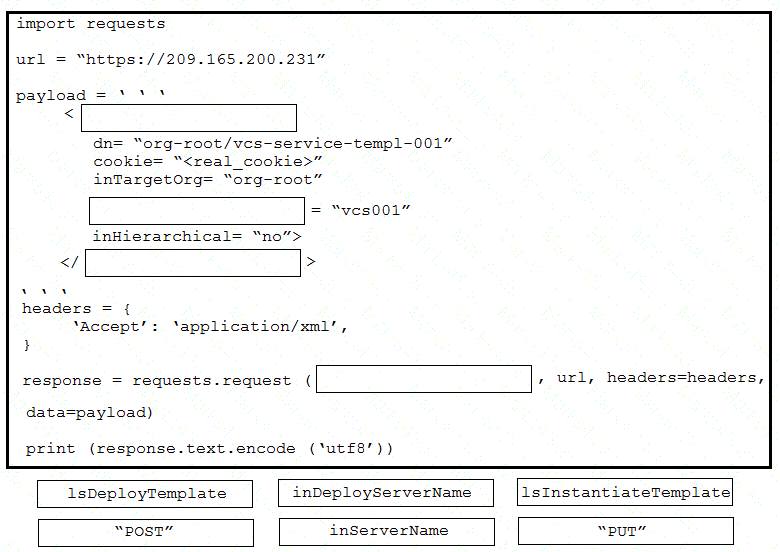
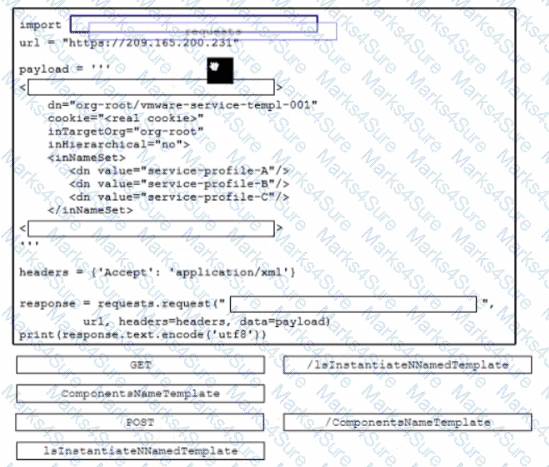
Drag and drop the code from the bottom onto the box where the code is missing to provision a new Cisco Unified Computing System server by using the UCS XML API. Options may be used more than once. Not all options are used.
The response from a server includes the header ETag: W/”7eb8b94419e371767916ef13e0d6e63d”. Which statement is true?
An automated solution is needed to configure VMs in numerous cloud provider environments to connect the environments to an SDWAN. The SDWAN edge VM is provided as an image in each of the relevant clouds and can be given an identity and all required configuration via cloud-init without needing to log into the VM once online.
Which configuration management and/or automation tooling is needed for this solution?
A developer is containerizing an application using Docker. A local Docker alpine image has been created, and it has the image ID ' b9c2d50f0b6y74998 ' with the tag ' dev ' . The developer must make a running container based on the tagged image, with the container port 80 bound to port 8080 on the host. Which command must be used?
An application is hosted on Google Kubernetes Engine. A new JavaScript module is created to work with the existing application. Which task is mandatory to make the code ready to deploy?
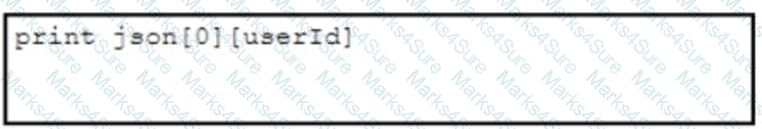
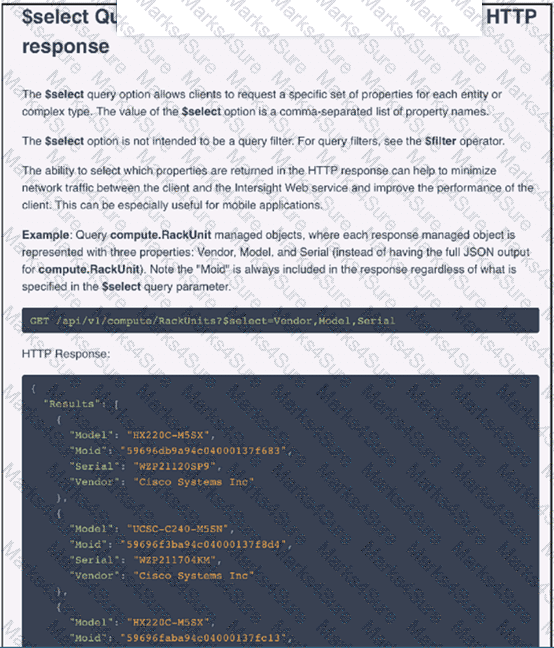
Refer to the exhibit.
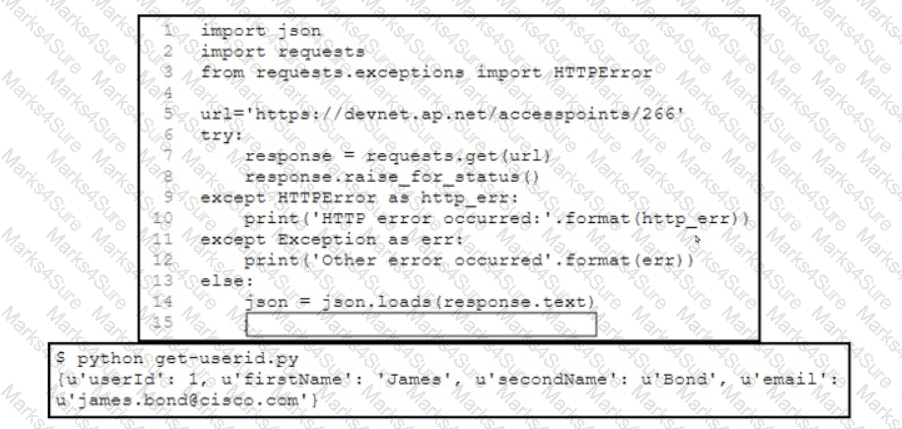
A developer has created a Python script that retrieves information about the deployment of Cisco wireless access points using REST API. Which two code snippets must be added to the blank in the code to print the value of the userid key instead of printing the full JSON response? (Choose two.)
A)
B)

C)
D)
E)
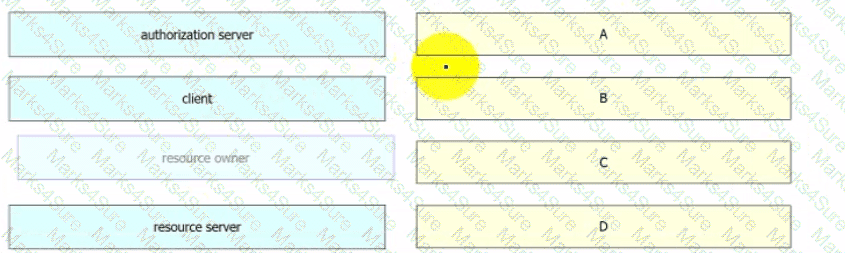
Refer to the exhibit.
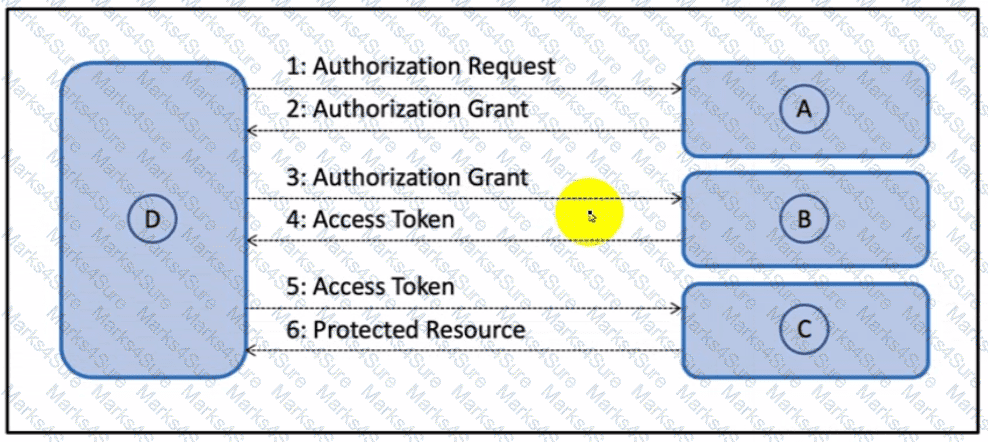
Drag and drop the components from the Oauth2 authorization protocol flow on the left onto the letter that matches the location in the exhibit.
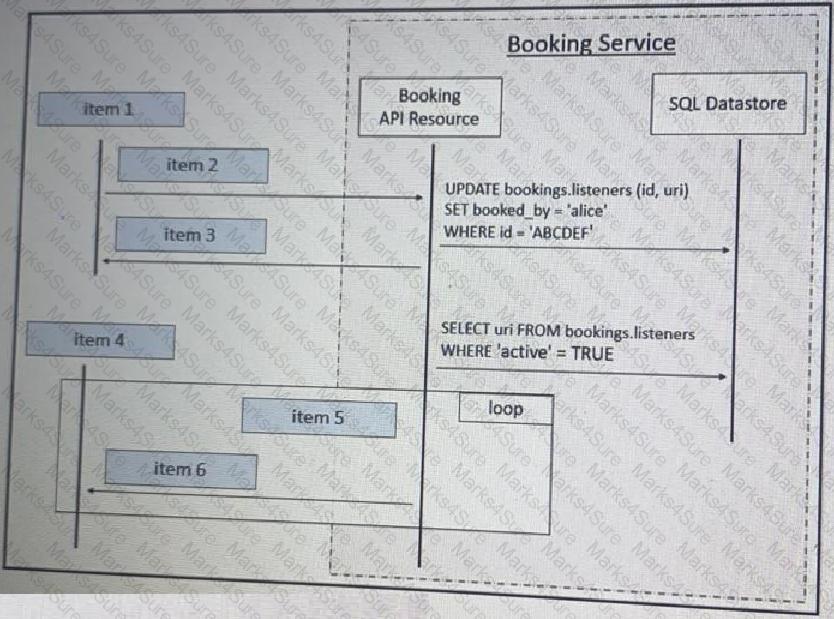
Refer to the exhibit above and click on the tab in the top left corner to view a diagram that describes the typical flow of requests involved when a webhook is created for a booking service. Drag and drop the requests from the left onto the item numbers on the right that match the missing sections in the sequence diagram to design the complete flow of requests involved as a booking is updated from a web application.
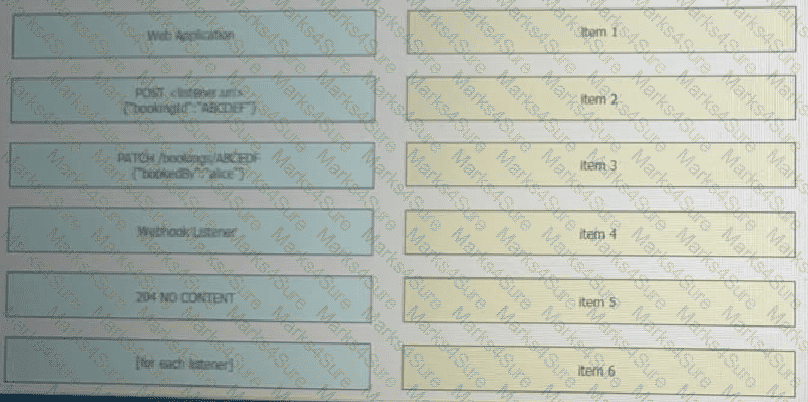
Refer to the exhibit.
Which key value pair from the ios_ntp Ansible module creates an NTP server peer?
Refer to the exhibit.
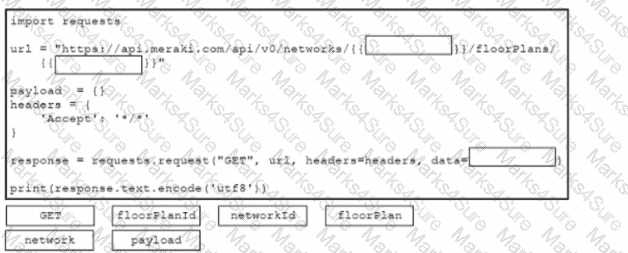
Drag and drop the code from the bottom onto the box where the code is missing to construct a Python script that will retrieve location data Not all options are used.
An application is made up of multiple microservices, each communicating via APIs. One service is beginning to be a bottleneck for the application because it can take a lot of time to complete requests. An engineer tried adding additional instances of this service behind the load balancer, but it did not have any effect. Which application design change must be implemented m this scenario?
Refer to the exhibit.
Which additional line results in the output of Test 1 upon execution of the docker run --rm devnet 1 command in a Dockerfile with this content?
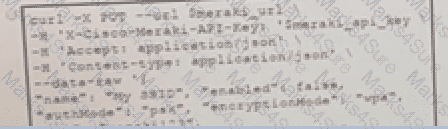
The Meraki API URL https://api.meraki.com/api/v0/networks/123456789/ssids/2 has been stored in the environment variable meraki_url and the API key has been stored in meraki_api_key. Which snippet present s the API call to configure, secure and enable an SSID using the Meraki API?
A)
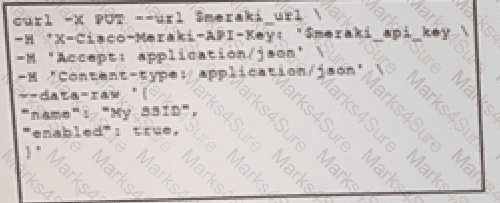
B)
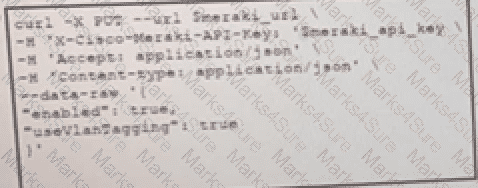
C)
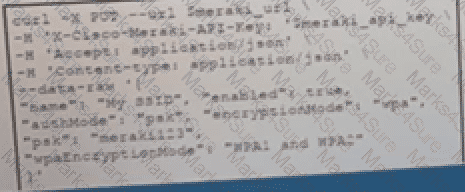
D)
A DevOps engineer needs to design an application to send emails based on incoming webhooks. No more than 10,000 outgoing emails should be sent per hour. How will the engineer ensure that all webhook transactions are processed within the email constraints?
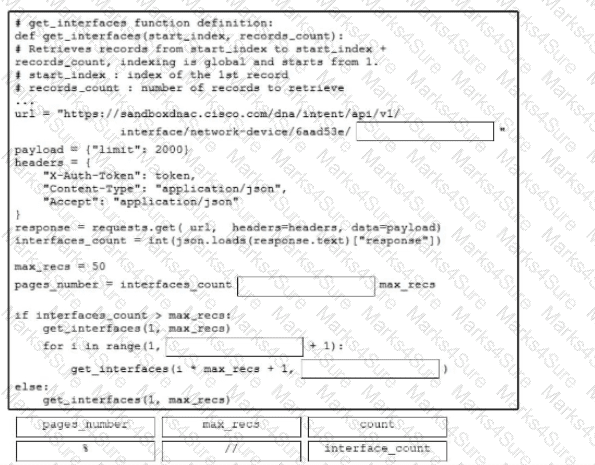
Refer to the exhibit. The got interfaces function is implemented already, and the interfaces must be retrieved in a controlled manner. Drag and drop the code snippets from the bottom onto the blanks in the Python function to split the job into batches of a maximum of 50 records. Not all options are used.
A developer releases a new application for network automation of Cisco devices deployed m a local data center. The application utilizes complex design patterns such as microservices that host multiple third-party libraries and programming languages. The development must be simplified by implementing an observability-driven development lifecycle. Which two considerations must be taken to meet the requirements? (Choose two.)
An application is developed in order to communicate with Cisco Webex. For reporting, the application must retrieve all the messages sent to a Cisco Webex room on a monthly basis.
Which action calls /v1/messages directly?
Refer to the exhibit.

An application ' s REST API GET call is tested to the inventory database. Which missing code must be included to limit
the number of values that are returned from the query to 20?
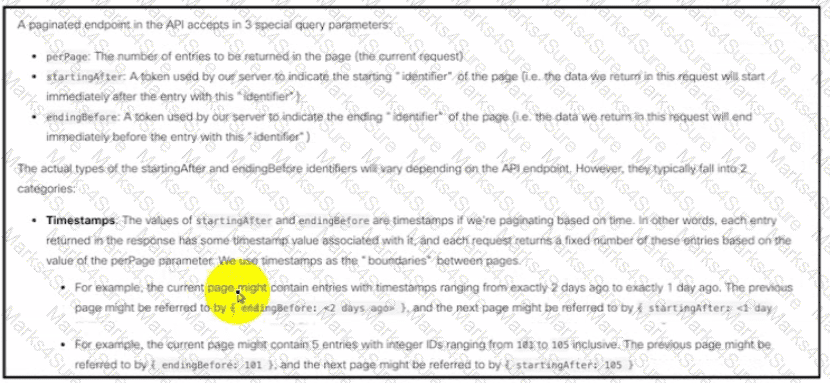
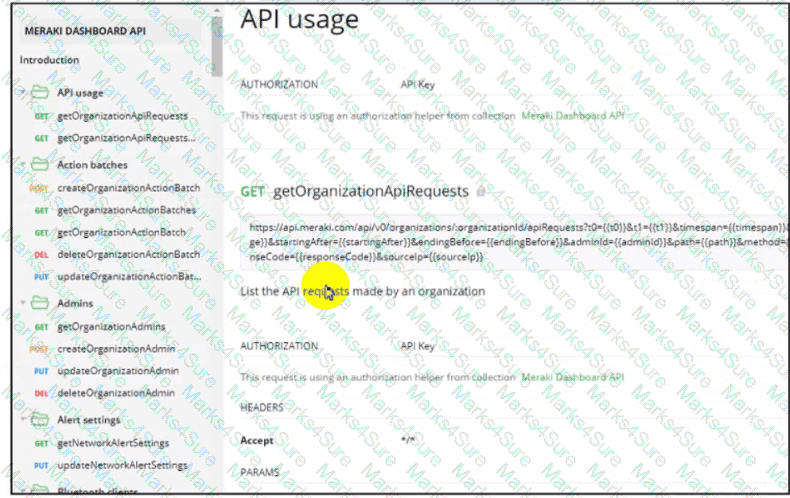
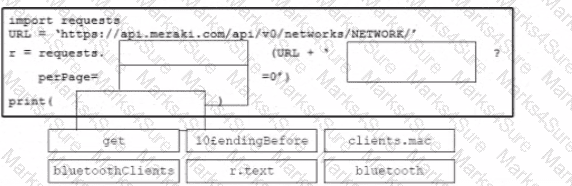
Refer to the exhibit Drag and drop the code from the bottom onto the box where the code is missing to query the last 10 Bluetooth clients seen by APs in their network using the Meraki Dashboard API Not all options are used.
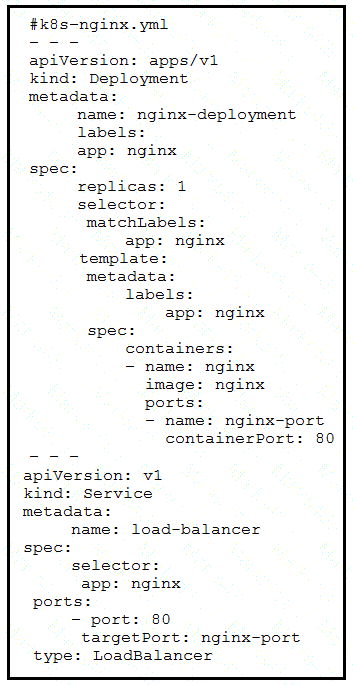
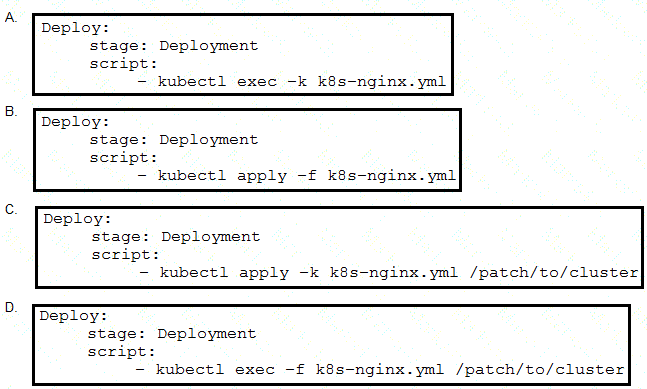
Refer to the exhibit. The presented application consists of a Nginx container and a load balancer service. Which GitLab CI/CD configuration implements the Kubernetes deployment?
Which transport layer protocol does gRPC use to retrieve telemetry information?
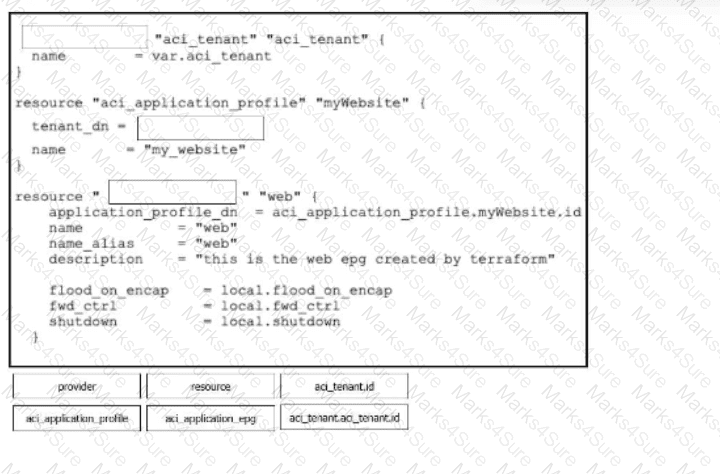
Drag and drop the code snippets from the bottom onto the boxes in the Terraform cod© to create a new application profile and EPG. Not all code snippets are used.
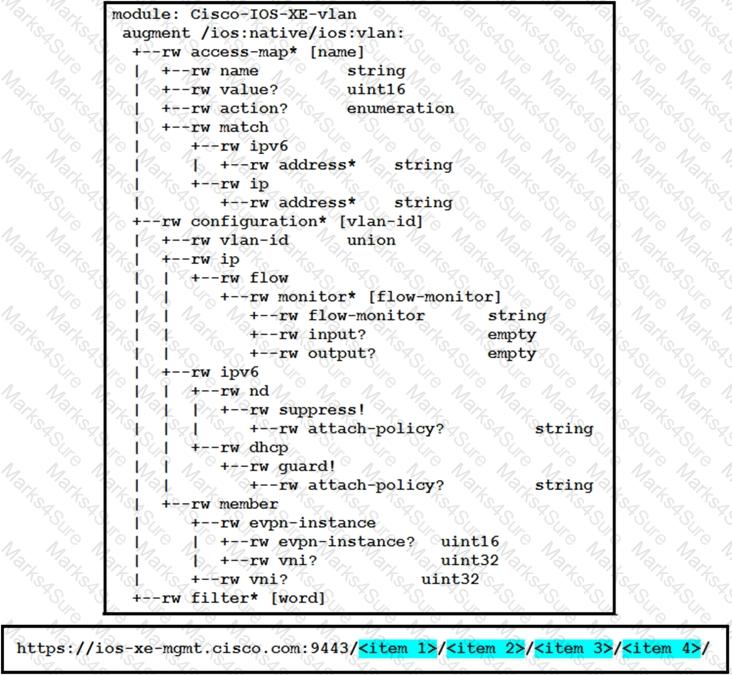
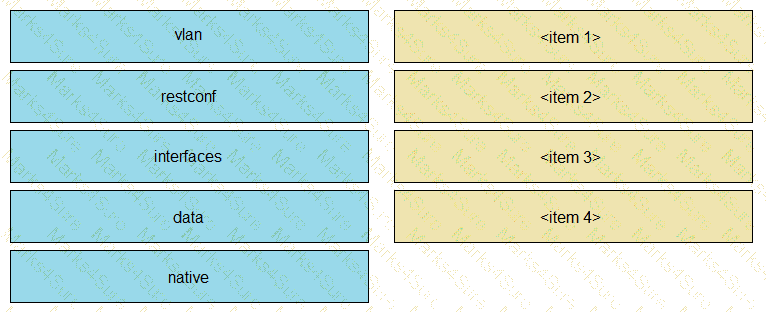
Refer to the exhibit. Drag and drop parts of the URL from the left onto the item numbers on the right that match the missing sections in the exhibit to create the appropriate RESTCONF URL to query the VLAN configuration given this YANG model. Not all URL parts are used.
Refer to the exhibit.

The cisco_devnet Docker swarm service runs across five replicas.The development team tags and imports a new image named devnet/ test:1.1 and requests that the image be upgraded on each container.There must be no service outages during the upgrade process. Which two design approaches must be used? (Choose two.)
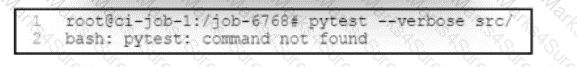
Refer to the exhibit. An engineer is setting up a CI/CD pipeline for a new application that depends on other services. The services must be prepared beforehand. Build dependencies must be installed by the pipeline. One of the pipeline stages fails. What is the cause of the issue?
Drag and drop the code from the bottom onto the box where the code is missing to create a new Cisco Webex space and attach a previously configured bot named ' sampleBot ' . Not all options are used.
Drag and drop the steps from the left into the order on the right to build and run a customized Python DocKer image. Not all options are used
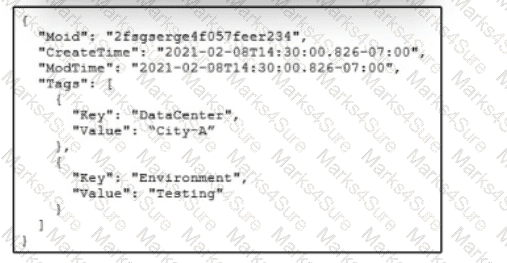
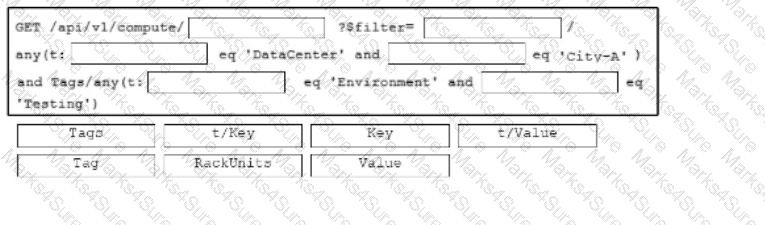
Refer to the exhibit. An engineer is attempting to retrieve information about free resources in the Cily-Adata center. The engineer wants to know only about resources in the testing environment. Drag and drop the code snippets from the bottom onto the blanks in the API call to meet this requirement. Some options may be used more than once. Not all options arc used.
An Etag header is included in the HTTP response for an API resource. What are two benefits of using the value of the Etag for future interactions involving the same API resource? (Choose two.)
A team is developing a cloud-native application. The project has these architecture requirements:
* Leverage the use of containers for effective usage of resources.
* Scale up the application automatically when more resources are needed.
* Ensure that the application is developed as a stateless application.
Which two guidelines must be met? (Choose two.)
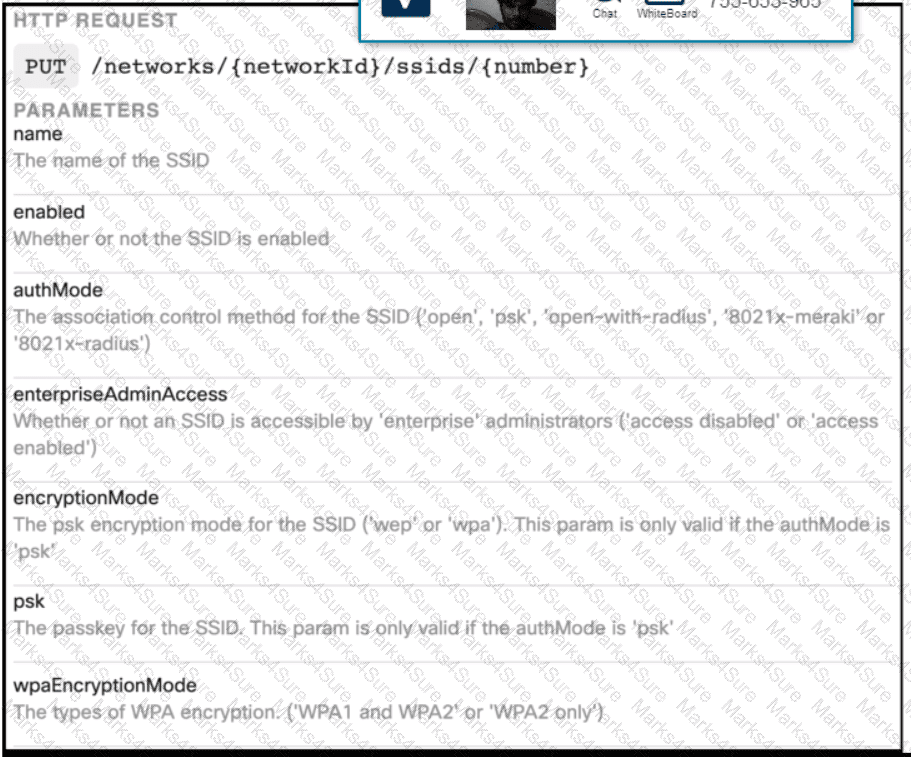
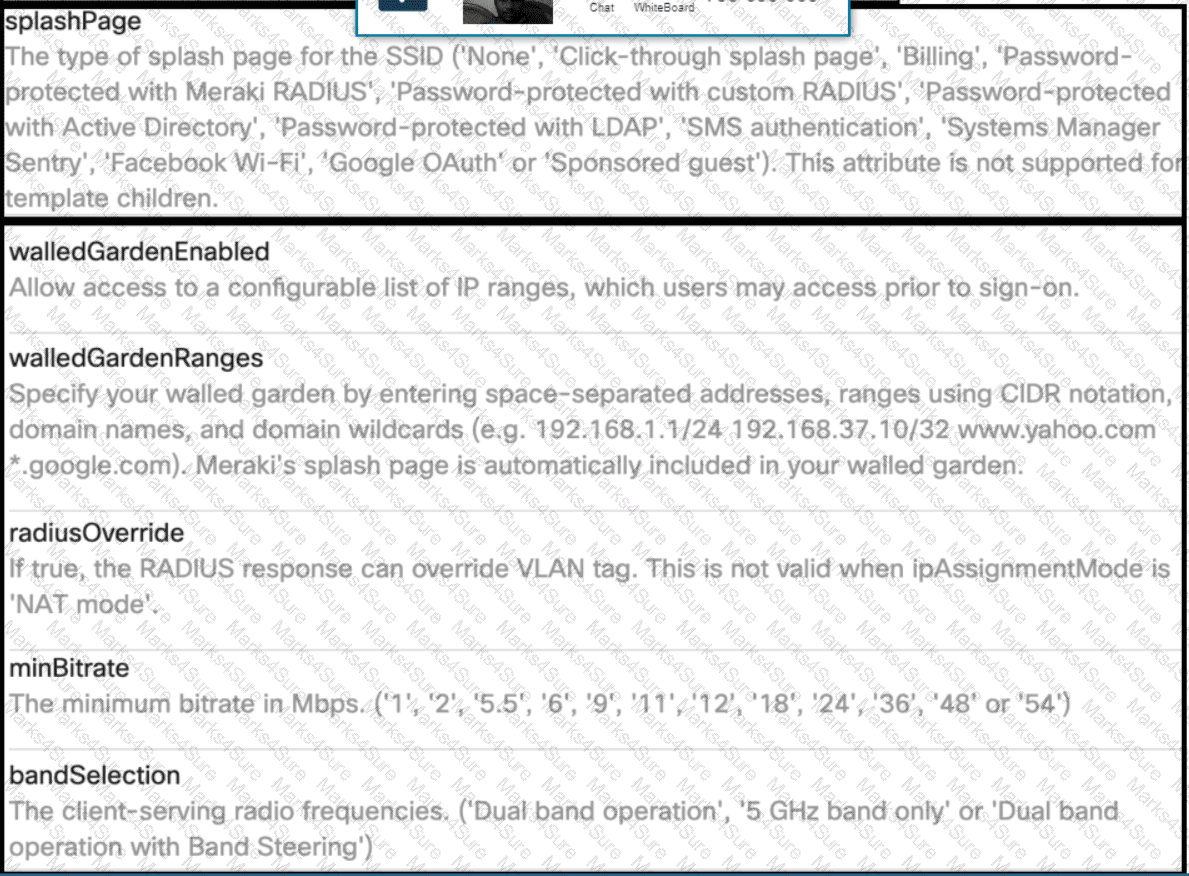
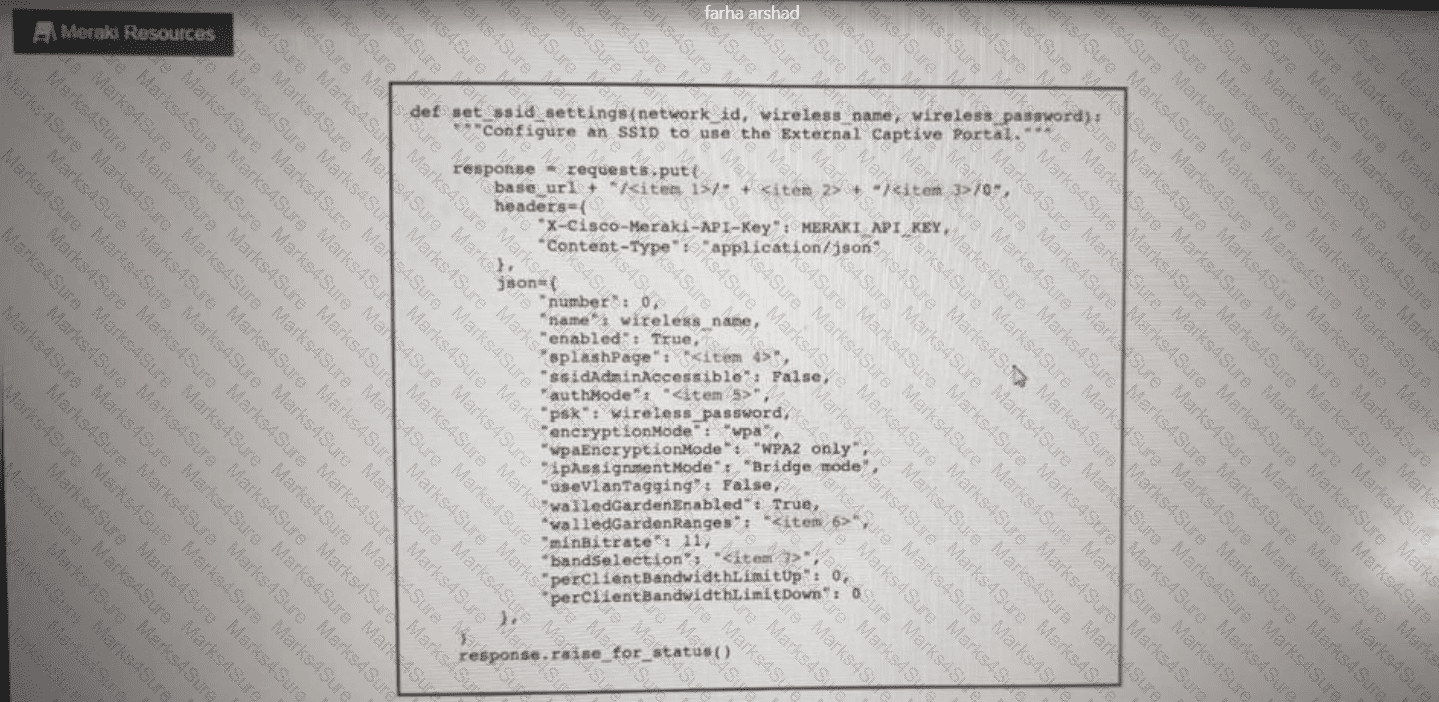
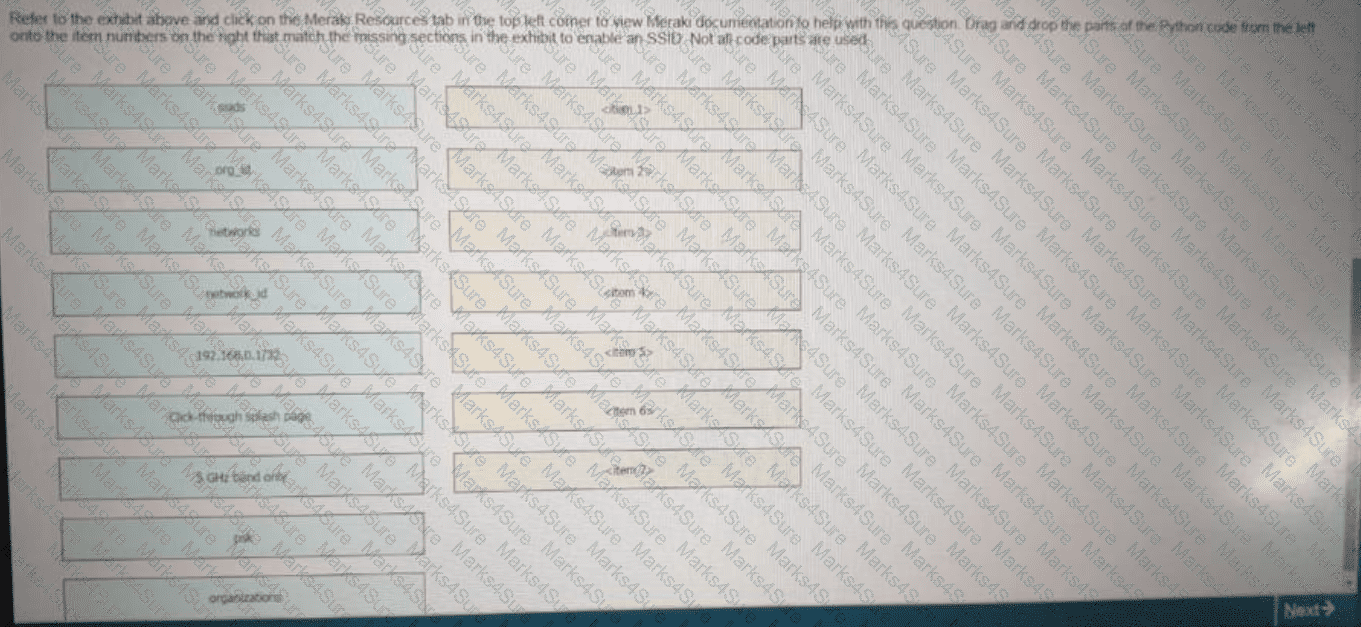
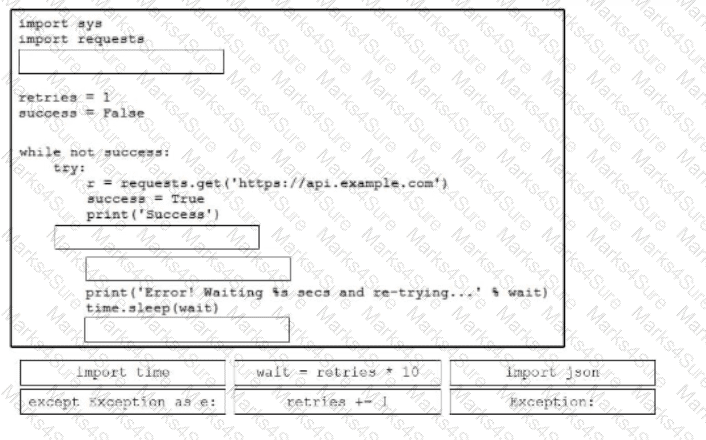
Click on the Meraki Resources tab in the left corner to view Meraki documentation to help with this question.Drag and drop the parts of the python code from the left onto the item numbers on the right that match the missing sections in the exhibit to enable an SSID. Not all code parts are used.
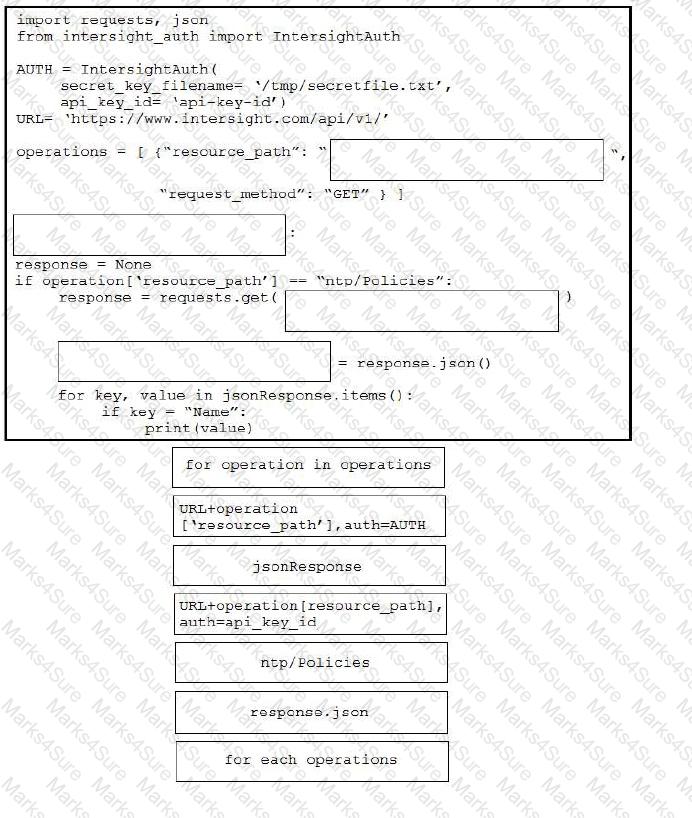
Drag and drop the code from the bottom onto the box where the code is missing in the Python script to execute a REST API call to query all the NTP policy names and print the name of each policy. Not all options are used.
Refer to the exhibit.
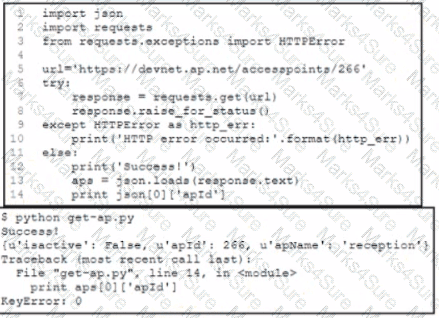
A Python developer is creating a wireless network device inventory application for local deployment of Cisco access points The developer is retrieving an access point ID by using a REST API The output indicates that there was a KeyError when parsing the JSON response. What returns the expected output of 266 at line 14?
A)
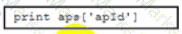
B)
C)
D)
A developer wants to automate virtual infrastructure to provision and manage it. The system will be implemented m large-scale deployment while offering redundancy and scalability with ease of management The solution must meet these requirements:
• Support the provisioning of up to 500 new virtual machines into private datacenters or the public cloud
• Support the modeling of a complex environment that consists of multiple virtual machines while supporting disaster recovery
• Maintain steady-state environments
Which configuration management solution must the developer use?
How is client code that consumes gRPC telemetry implemented, assuming that the preferred language is able to be chosen?
Cisco sensorBase gathers threat information from a variety of cisco products and services and performs analytics on threats. Which term describes this process?
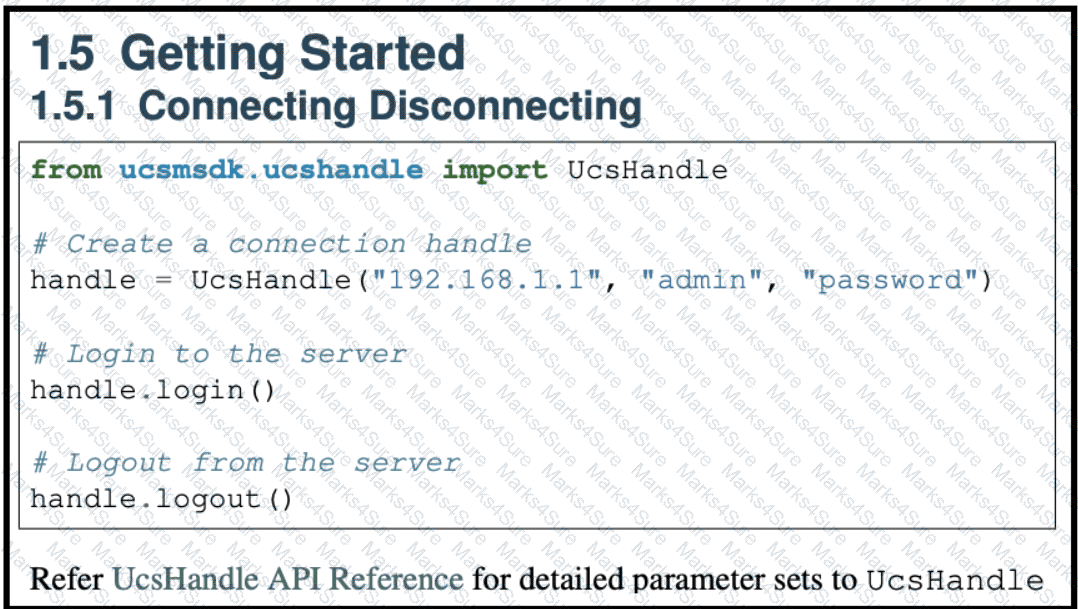
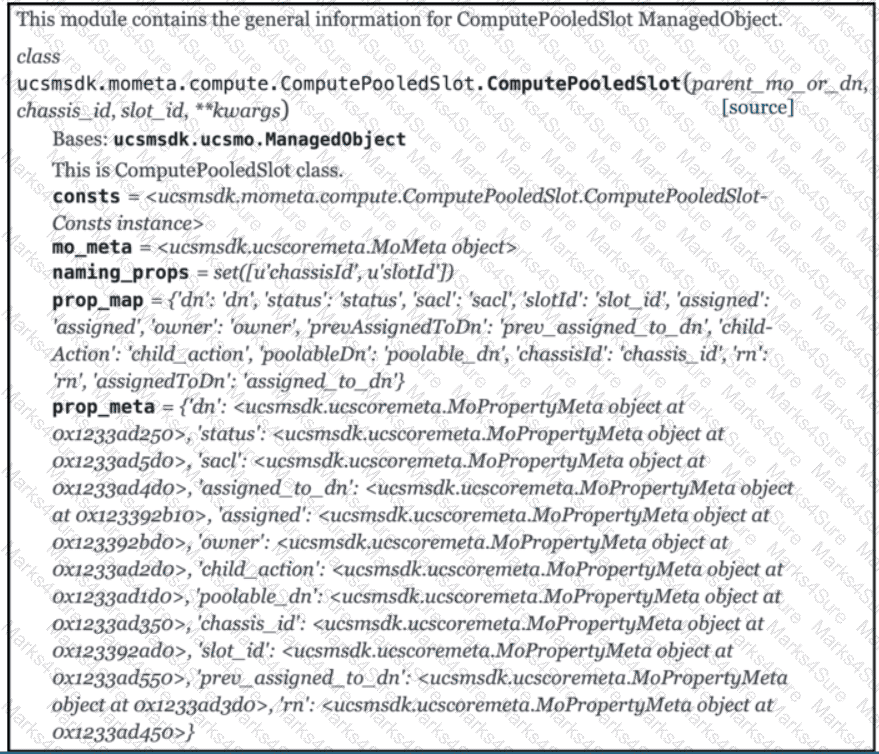
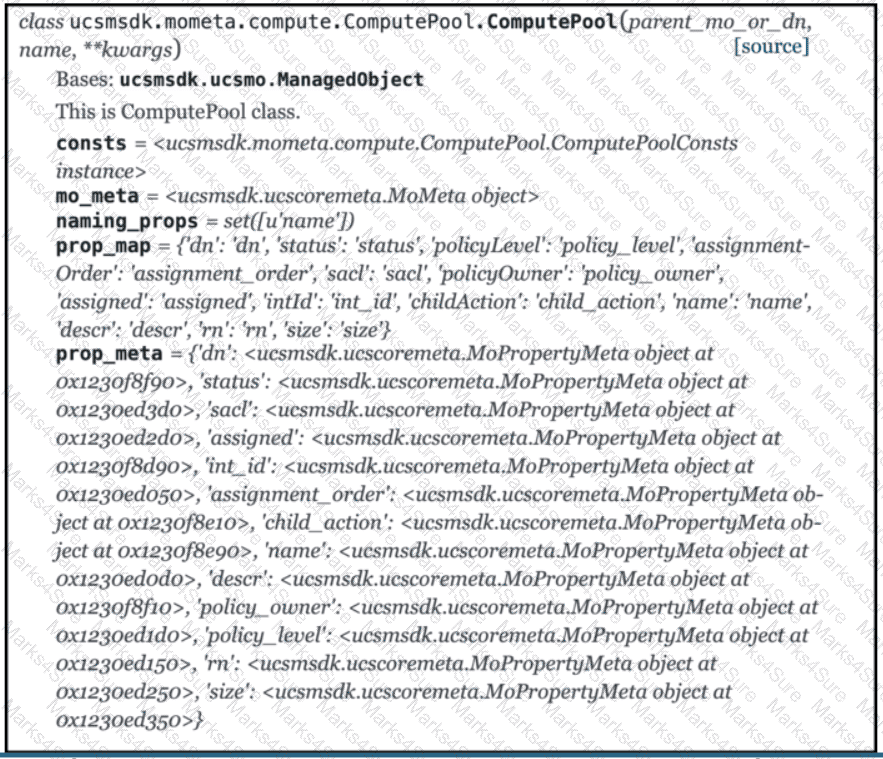
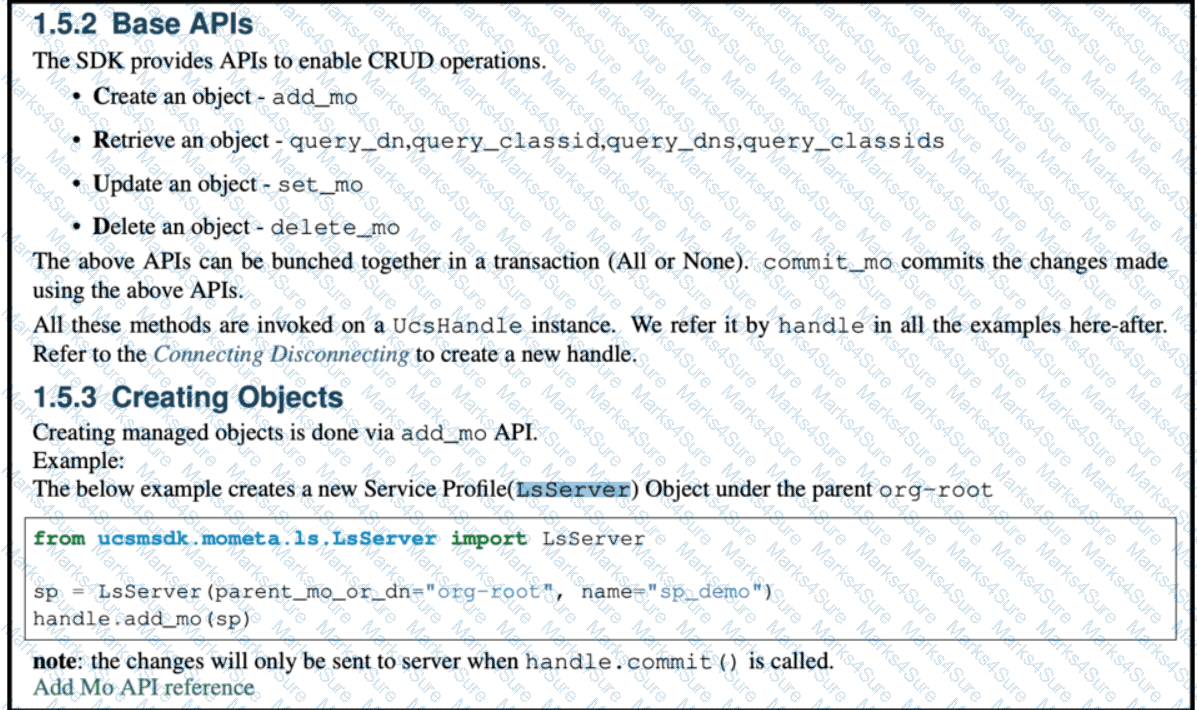
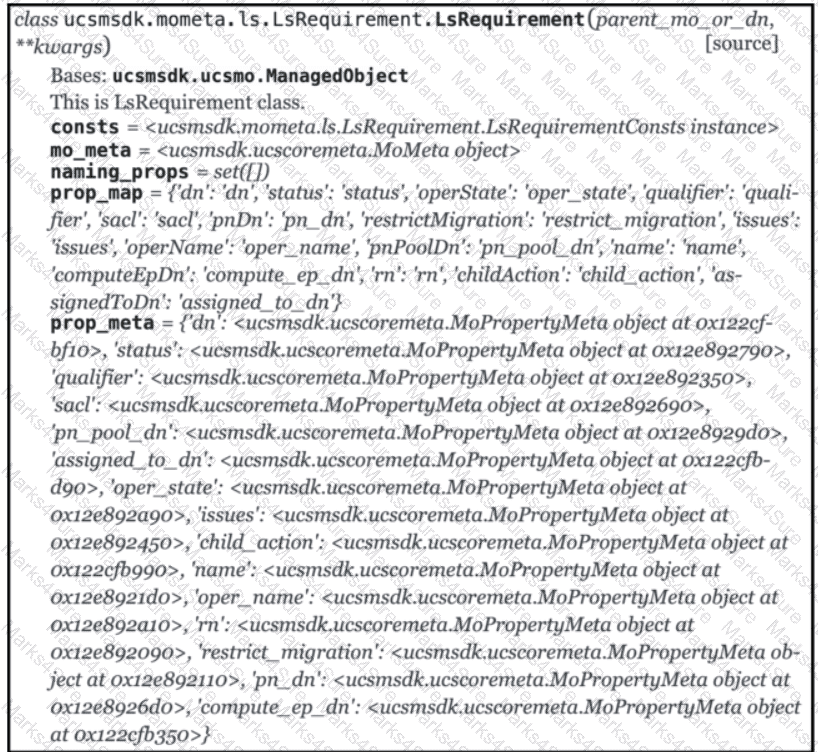
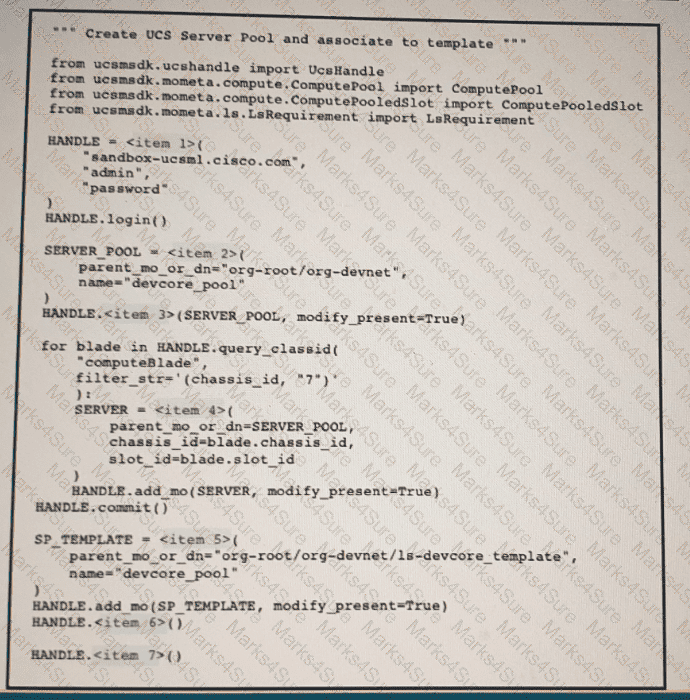
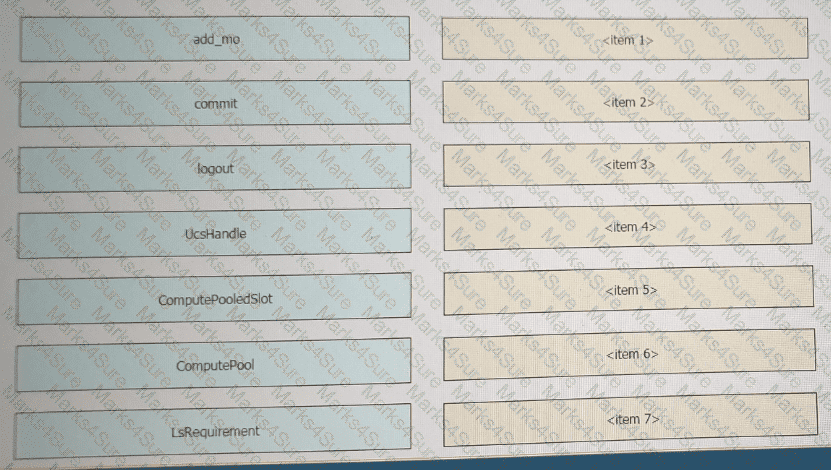
Refer to the exhibit above and click on the resource tabs in the top left corner to view resources to help with this question. Python code using the UCS Python SDK is creating a server pool named “devcore_pool” and populating the pool with all servers from chassis 7 and then the server pool is associated to existing service profile template “devcore_template”. Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the python exhibit.
Refer to the above and click on the resource labs in the top left corner to view resources to help with this question.
Python code using the UCS Python SDK is creating a server pool named " devcore_pool " and populating the pool with all servers from chassis 7, and then the server pool is associated to existing Service Profile template " devcore_template " Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the Python exhibit.
An application has these characteristics
• provide one service or function
• distributed database
• API gateway
• central repository for code
• configuration database
• uses session management
Which two design approaches contribute to the scalability of the application? (Choose two.)
Which snippet presents the correct API call to configure, secure, and enable an SSID using the Meraki API?
A)
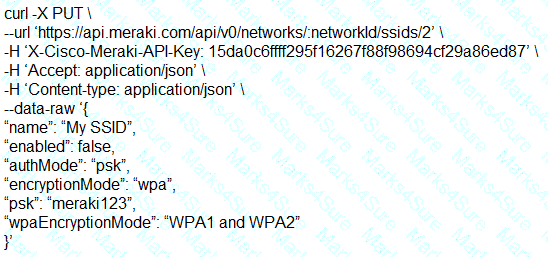
B)
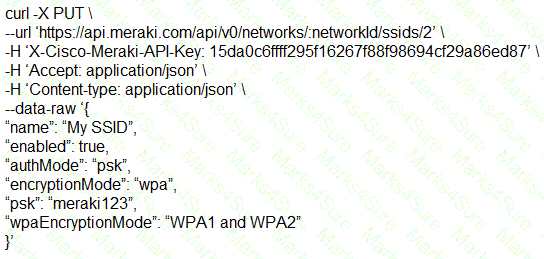
C)
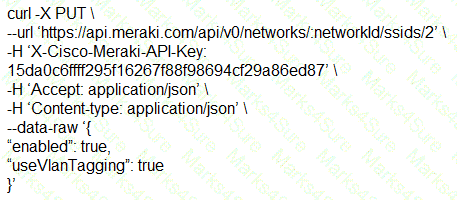
D)
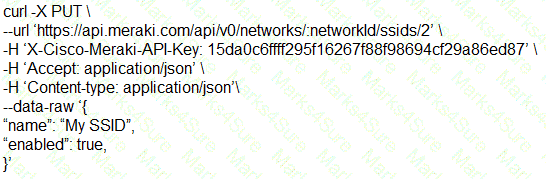
Refer to the exhibit.
A network engineer must integrate error handling tor time-outs on network devices using the REST interface. Which line of code needs to be placed on the snippet where the code is missing to accomplish this task?
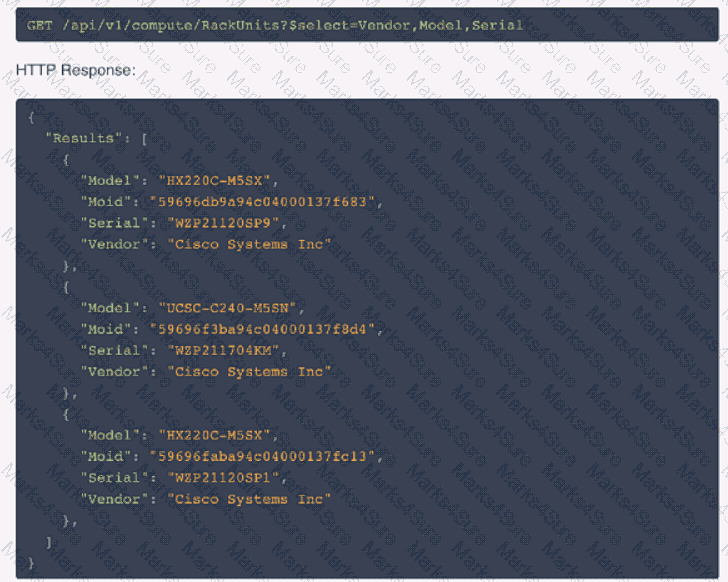

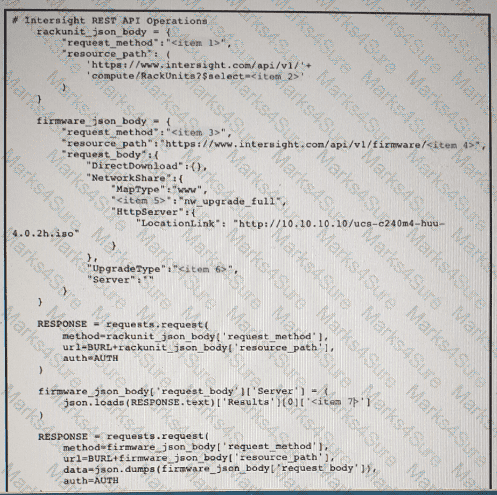
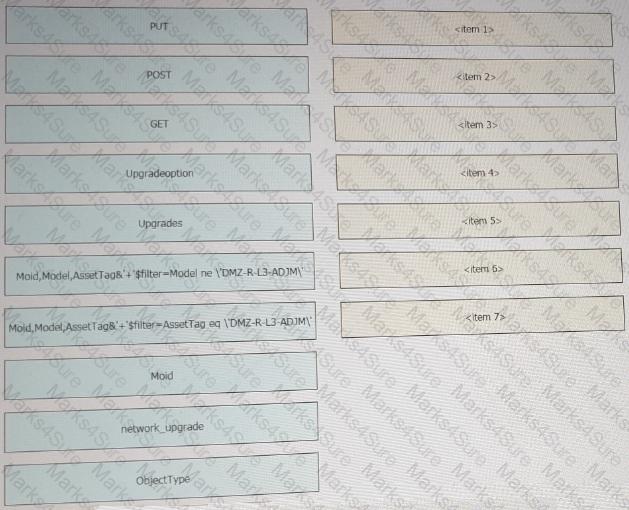
Refer to the exhibit above and click on the resource tabs in the top left corner to view resources to help with this question. The script uses the Cisco Intersight REST API. Drag and drop the code snippets from the left onto the item numbers on the right to match the missing sections in the Python script to update the firmware on specific Cisco Intersight USC rack server.DMZ_R-L3-ADJM. Not all code snippets are used.
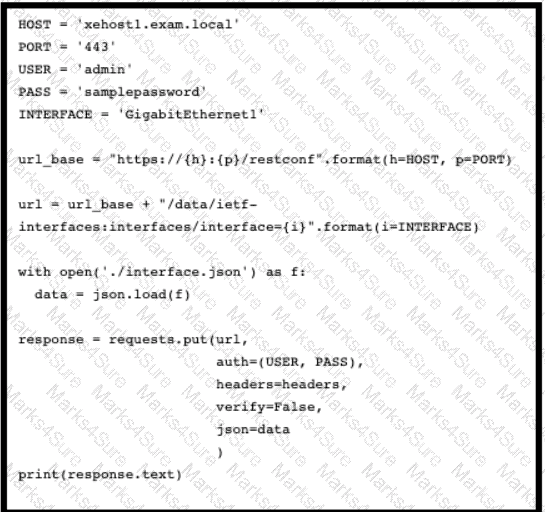
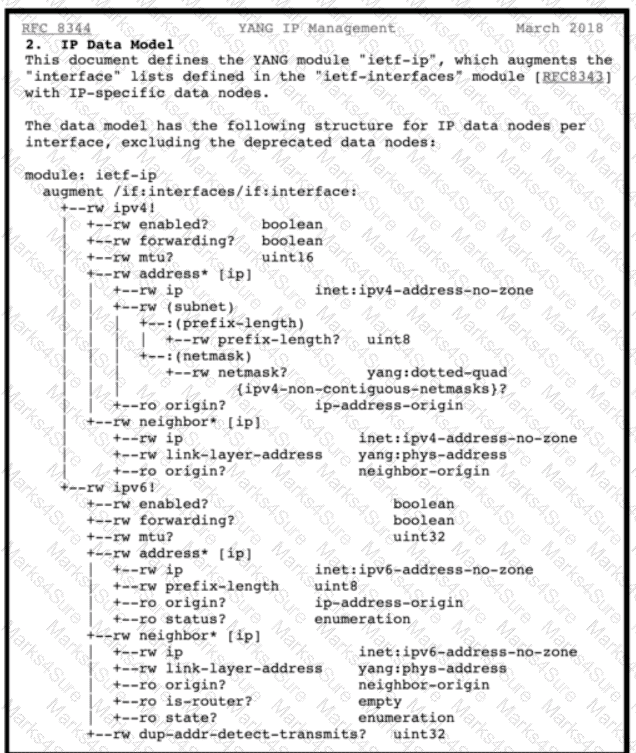
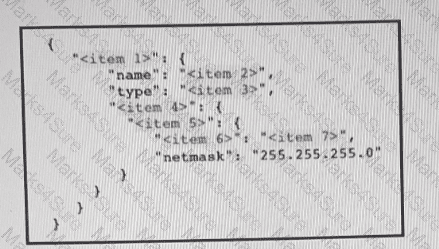
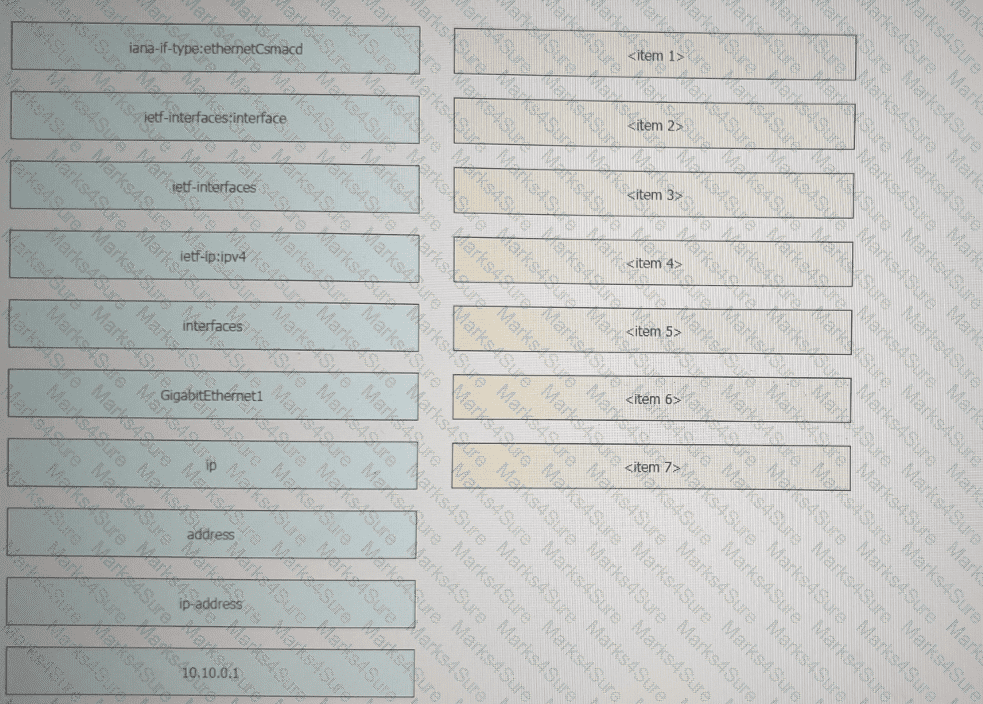
Refer to the exhibit above and click on the resource tabs in the top left corner to view an IETF TANG MODEL and a Python file that changes the configuration via RESTCONF. Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the exhibit to complete the JSON file that changes configuration of interface GigabitEthernet1 to have an IPv4 configuration of 10.10.0.1/24. Not all options are used.
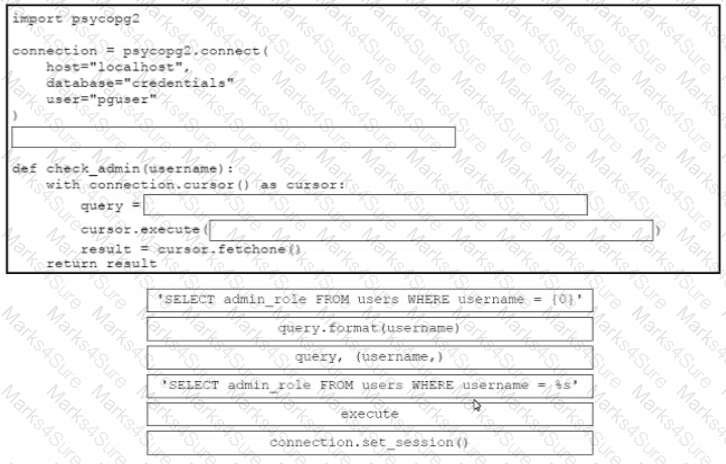
Drag and drop the code from the bottom onto the box where the code is missing in the Python code to query for user permissions while mitigating against SQL Injection Not all options are used.
Refer to the exhibit.
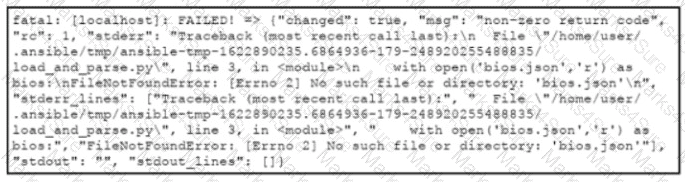
An engineer creates an application that leverages the Ansible framework to provision CPE endpoints that have configuration changes. The application contains an Ansible playbook named provision_cpes.yml that uses the ansible.builtin.script Ansible module to execute these two Python scripts:
• gather and_create.py. which creates a JSON file named bios.json that contains the CPE models and their respective IOS file information
• load and parse.py. which loads the file data and parses it for later consumption
After several successful runs, the application fails. During a review of the Ansible execution logs, the engineer discovers an error output that indicates that one of the stages failed. What is the cause of this issue?
An enterprise refactors its monolithic application into a modem cloud-native application that is based on microservices. A key requirement of the application design is to ensure that the IT team is aware of performance issues or bottlenecks in the new application Which two approaches must be part of the design considerations ' ' (Choose two.)
Refer to the exhibit , The command docker build -tag=friendlyhello . is run to build a docker image from the given Dockerfile,
requirements,txt, and app.py, Then the command docker run -p 4000:80 friendlyhello is executed to run the application. Which URL is entered in the web browser to see the content served by the application?
Drag and drop the code snippets from the bottom onto the boxes where the code is missing to deploy three Cisco UCS servers each from a different template Not all options ate used.
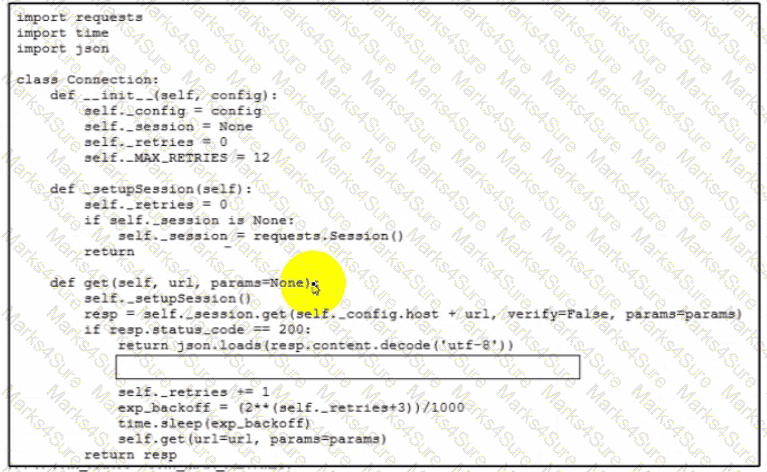
Refer to the exhibit.
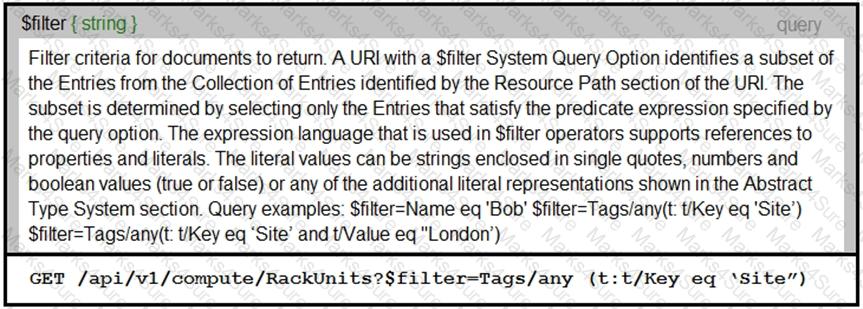
An Intersight API is being used to query RackUnit resources that have a tag keyword set to “Site”. What is the expected output of this command?
Refer to the exhibit.
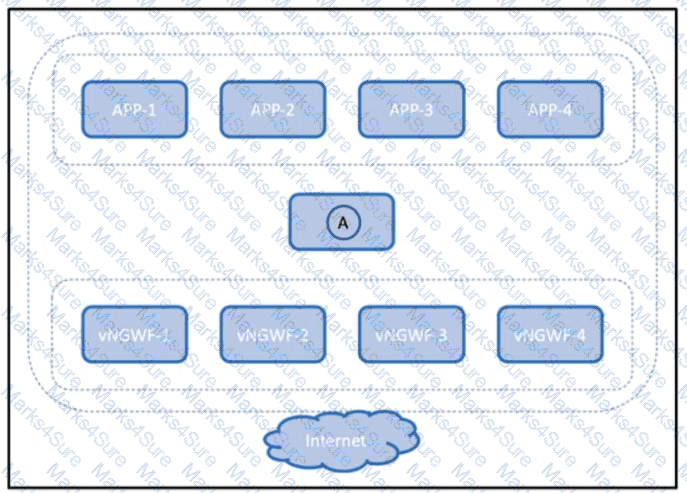
The virtual next-generation firewalls running in the public cloud must be scaled out to meet the throughput requirements of the application layer. Which component is deployed to location A in the diagram?
Why is end-to-end encryption deployed when exposing sensitive data through APIs?
How should a web application be designed to work on a platform where up to 1000 requests per second can be served?
A developer deploys a SQLite database in a Docker container. Single-use secret keys are generated each time
a user accesses the database. The keys expire after 24 hours. Where should the keys be stored?
What are two principles according to the build, release, run principle of the twelve-factor app methodology?
(Choose two.)
In the three-legged OAuth2 authorization workflow, which entity grants access to a protected resource?
Refer to the exhibit.
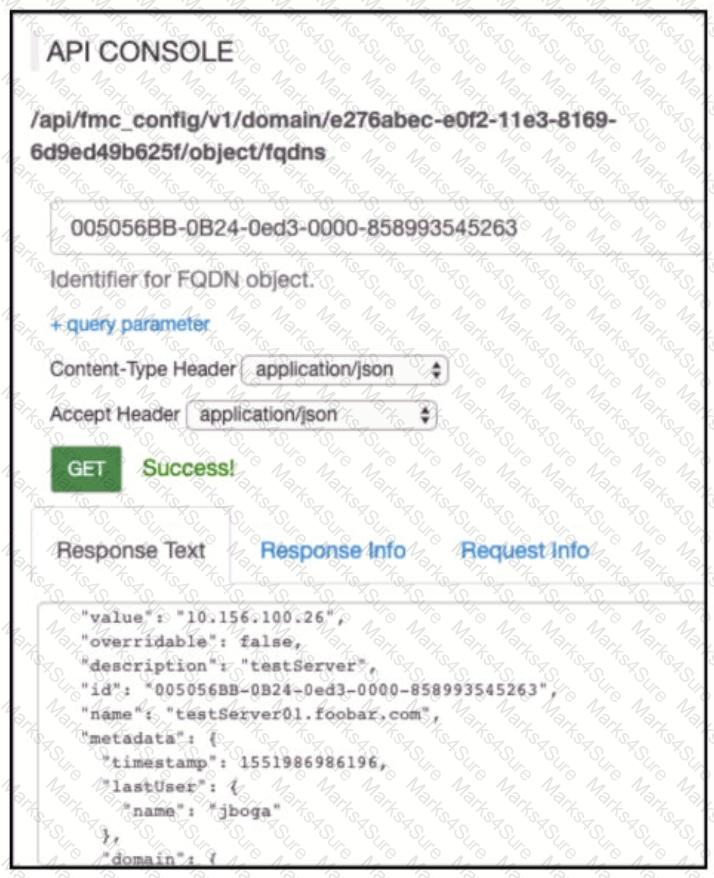
Which AP! call does an engineer use to delete the FQDN object?
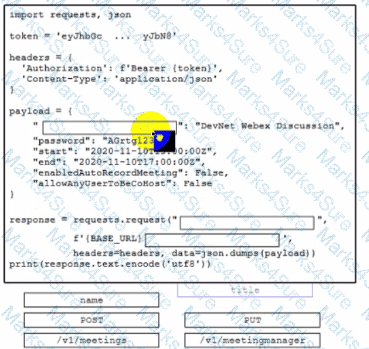
Drag and drop the code snippets from the bottom onto.the boxes where the code is missing to create a Cisco Webex meeting by using the Webex API. Not all options are used.
A developer is working on an enhancement for an application feature and has made changes to a branch called ‘devcor-432436127a-enhance4‘. When merging the branch to production, conflicts occurred. Which Git command must the developer use to recreate the pre-merge state?
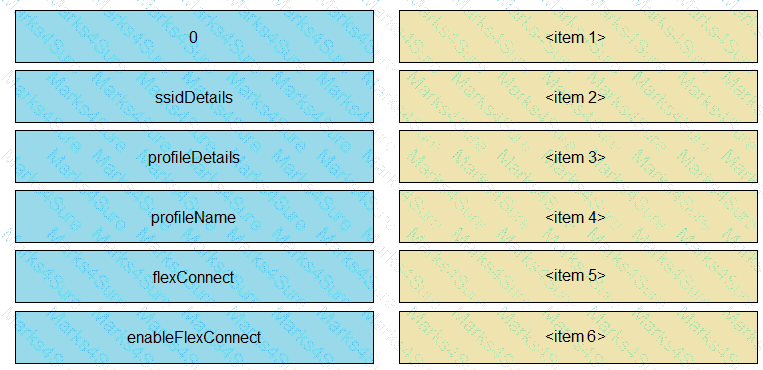
Refer to the exhibit.
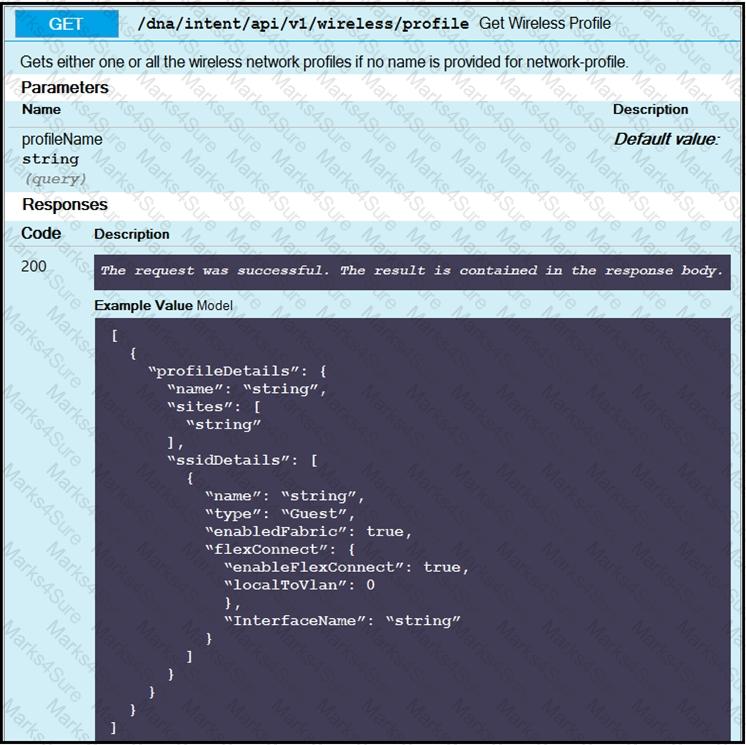
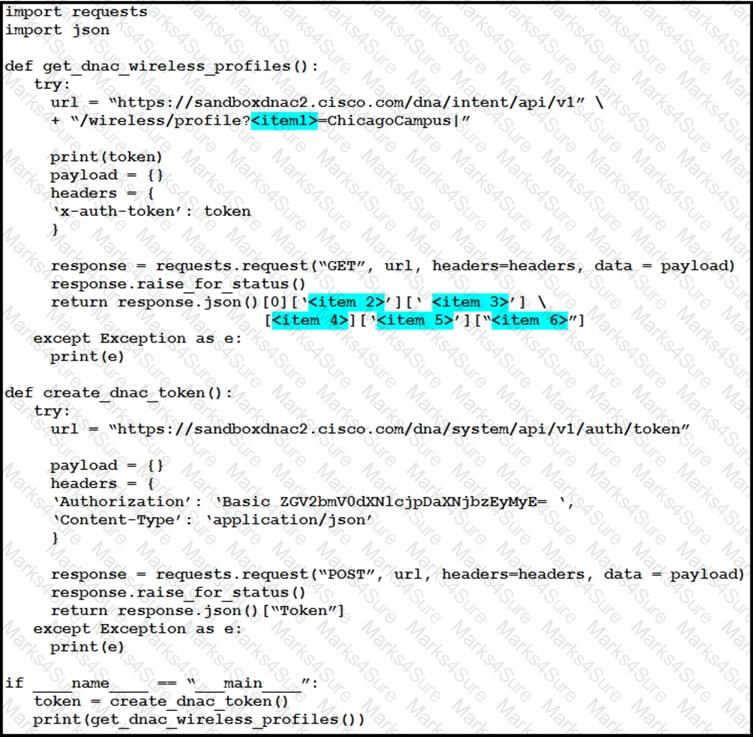
The Python script is supposed to make an API call to Cisco DNA Center querying a wireless profile for the “ChicagoCampus” and then parsing out its enable FlexConnect value. Drag and drop the parts of the Python code from the left onto the item numbers on the right that match the missing sections in the exhibit.
Refer to the exhibit.
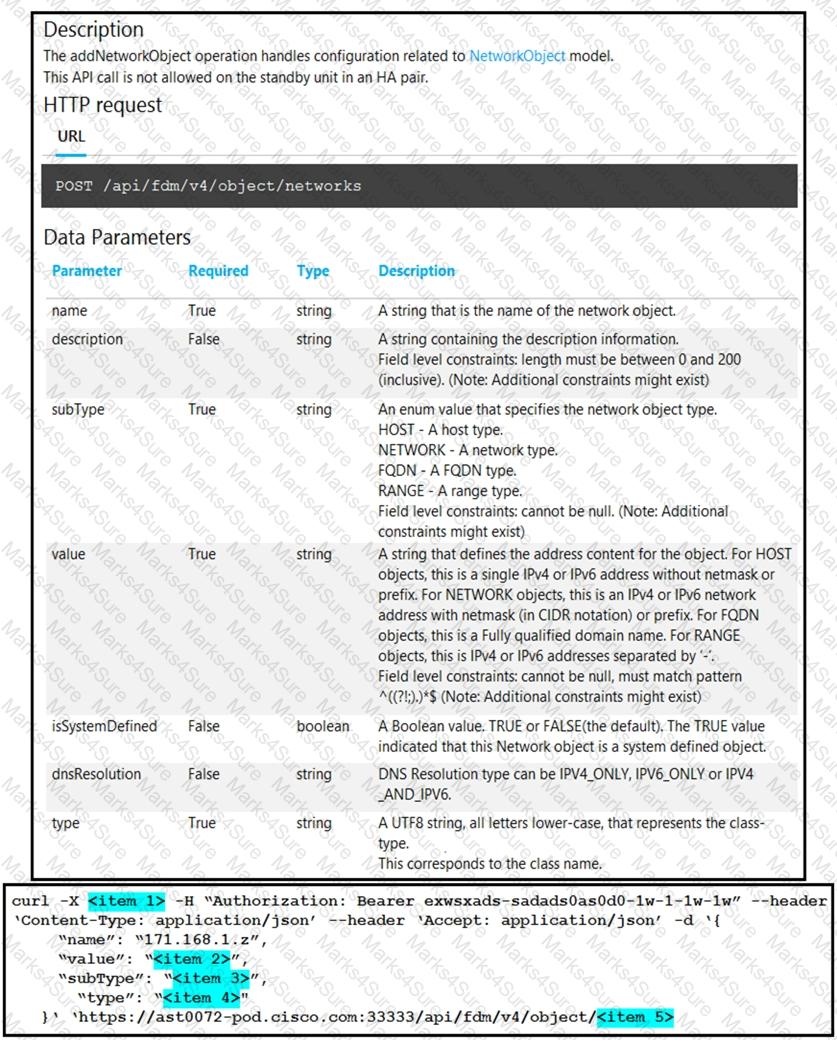
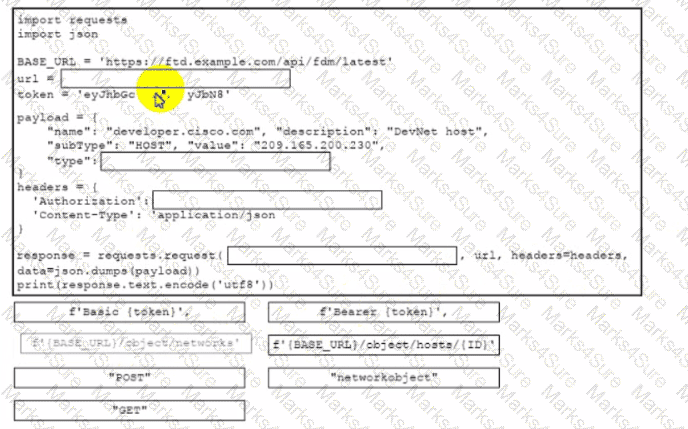
Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the cURL exhibit to complete the cURL request to FirePower Device Manager API to create objects. Not all code snippets are used.
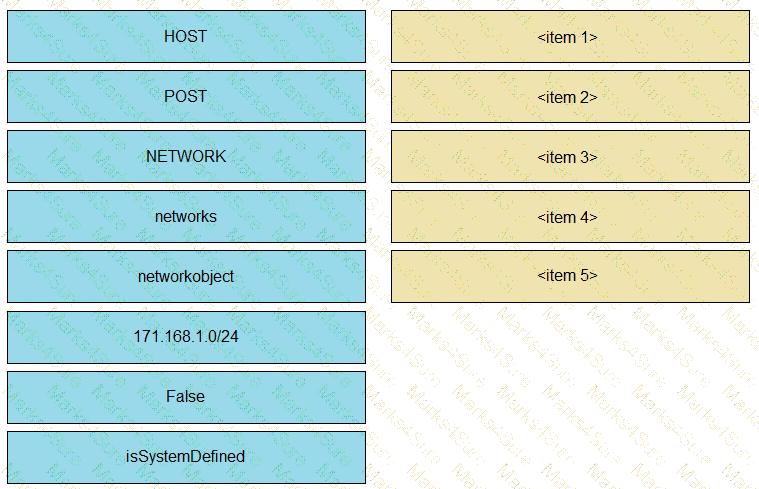
Drag and drop the coda snippets from the bottom onto the blanks in the code to implement error handling for an application that will attempt to call a REST API. In the event of an error, the script must back off for 10 seconds before trying again, adding an extra 10 seconds to the backoff period for every failure that occurs. Not all options are used.
Drag and drop the code from the bottom onto the box where the code is missing in the Python script to display the error message to the user. The script uses Python to connect to Cisco DNA Center and provides details if the connection fails. Not all options are used.
Drag and drop the code from the bottom onto the where the code is missing to create a host object by using the Cisco Firepower Device Manager API. Not all options are used.
Refer to the exhibit.
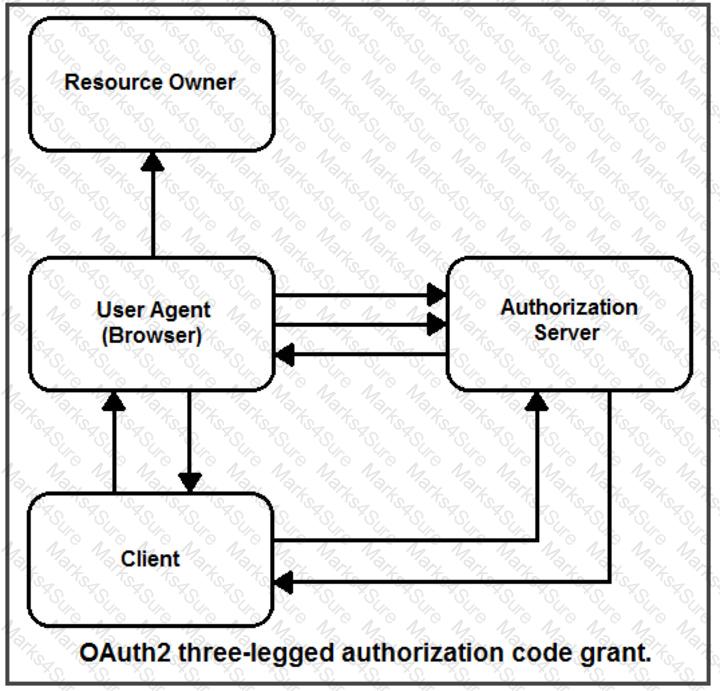
Drag and drop the steps from the left into the correct order of operation on the right for a successful OAuth2 three-legged authorization code grant flow.
Which two statements describe advantages of static code analysis over unit tests? (Choose two.)
What are two advantages of using model-driven telemetry, such as gRPC. instead of traditional telemetry gathering methods? (Choose two.)
A local Docker image has an image ID of 386231131. Fill in the blanks to complete the command in order to tag the image into the " cisco " repository with " version1 0’ " .

What securely stores and encrypts the API keys and tokens that are used for an application deployment?
Refer to the exhibit.
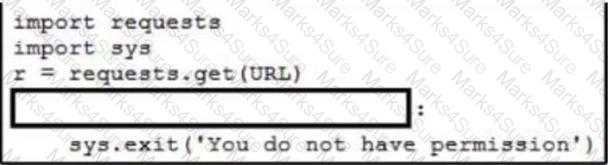
A network engineer needs to handle API errors in their requests when users do not have permission to access the resource, even if they are authenticated and authorized. Which line of code needs to be placed on the snippet where the code is missing to handle these API errors?
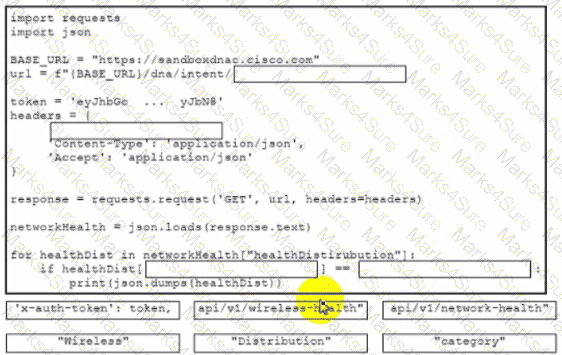
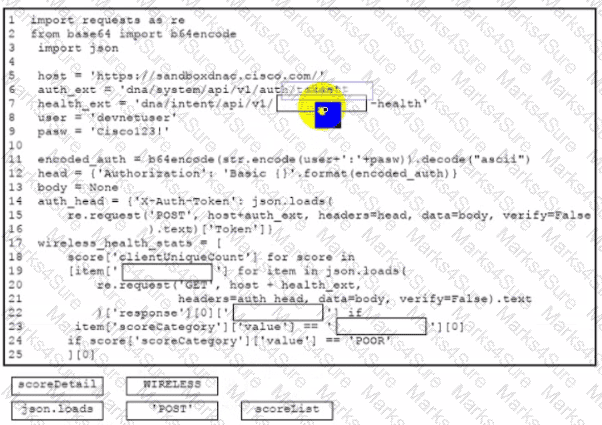
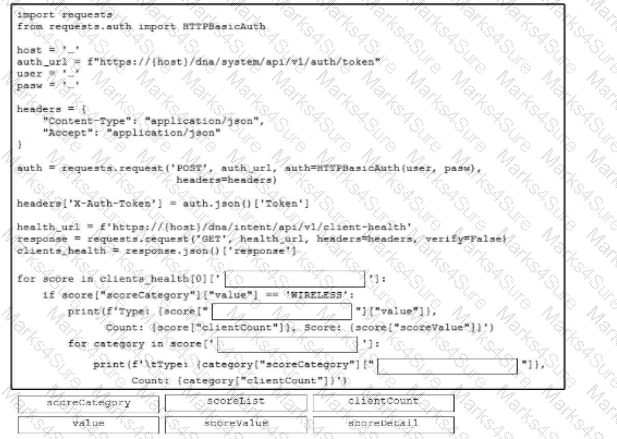
Drag and drop the code from the bottom onto the box where the code is missing to retrieve and display wireless network hearth information. The wireless network devices are being managed by Cisco DNA Center and are compatible with REST API Not all options are used.
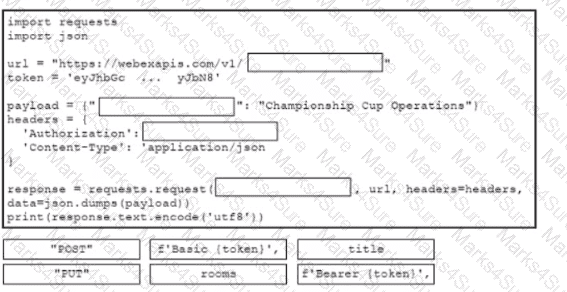
Drag and drop the code from the bottom onto the box where the code is missing to create a Webex space Not all options are used.
Which two principles are included in the codebase tenet of the 12-factor app methodology? (Choose two.)
Refer to the exhibit.
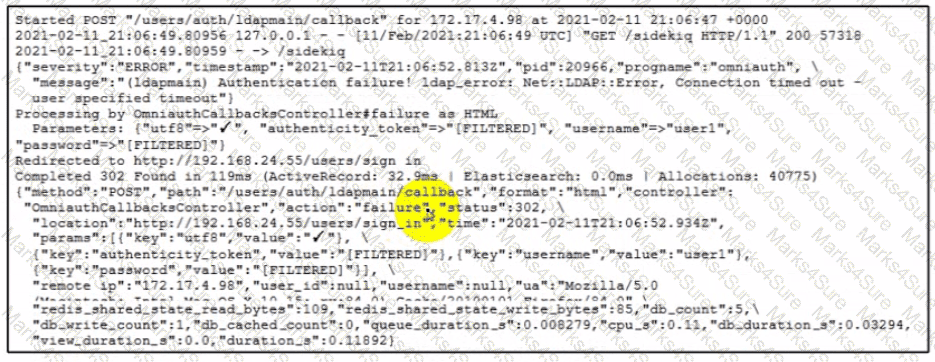
Recently, users have reported problems logging into an application with their usernames and passwords. The logs have captured an authentication attempt. Based on the messages and errors contained, what is the cause of the problem?
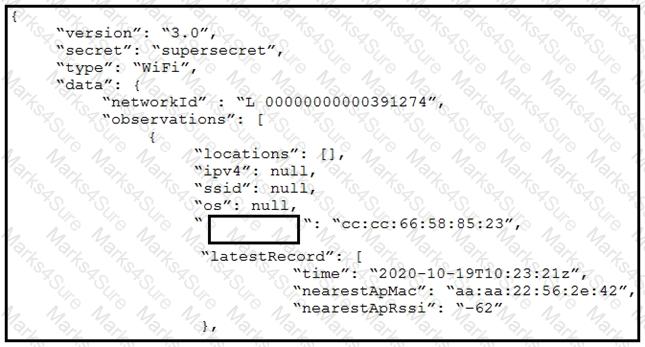
Refer to the exhibit. The JSON response is received from the Meraki location API. Which parameter is missing?
Which two statements are considered best practices according to the 12-factor app methodology for application design? (Choose two.)
A Python script must query the Cisco DNA center API for the number of unique wireless clients that are exhibiting poor health behavior. Drag and drop the code from the bottom onto the box where the code is missing to complete the script Not all options are used.
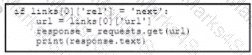
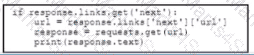
Refer to the exhibit.
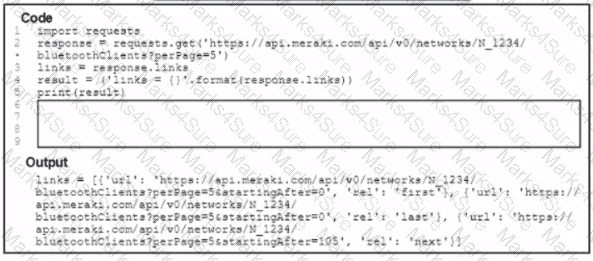
A Python script has these requirements
• Retrieve a list of Bluetooth clients seen by the access pants on a network.
• Print the content of the response
• Retrieve the next page only if it is available in the response headers
What must be added where the code is missing to get the remaining pages by using the next link from the link response header of the last request?
A)
B)
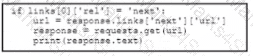
C)
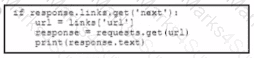
D)
A developer corrects an application bug with ID buglDa98416945110x and then installs it on a Cisco Catalyst 9300 series switch. Which command will enable the application called myapp?
Which OAuth mechanism enables clients to continue to have an active access token without further interaction from the user?
When end-to-end encryption is implemented, which area is most vulnerable to exploitation?
Refer to the exhibit. Drag and drop the code snippets from the bottom onto the blanks in the Python scrip; to retrieve wireless c lent health data by using the Cisco Catalyst Center (formerly DNA Center) API. Not all options are used.
A developer has created a local Docker alpine image that has the image ID ' dockapp432195596ffr ' and tagged as ‘new’. Which command creates a running container based on the tagged image, with the container port 80 bound to port 8080 on the host?
A web application is susceptible to cross-site scripting. Which two methods allow this issue to be mitigated? (Choose two.)
Which data encoding format uses gRPC by default for serializing structured sets of information?
Refer to the exhibit.
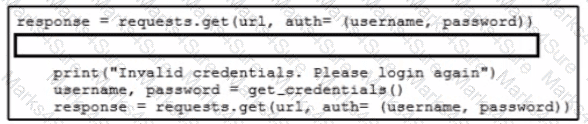
Which code snippet must be added to the blank in the code to automate the evaluation and handling of errors due to wrong credentials when Basic Authorization is used?
A)

B)

C)

D)

An application has been developed for monitoring rooms in Cisco Webex. An engineer uses the application to
retrieve all the messages from a Cisco Webex room, but the results are slowly presented. Which action
optimizes calls to retrieve the messages from the /v1/messages endpoint?
Refer to the exhibit.
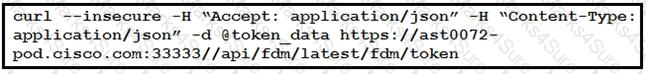
The cURL POST request creates an OAuth access token for authentication with FDM API requests. What is the purpose of the file “@token_data” that cURL is handling?
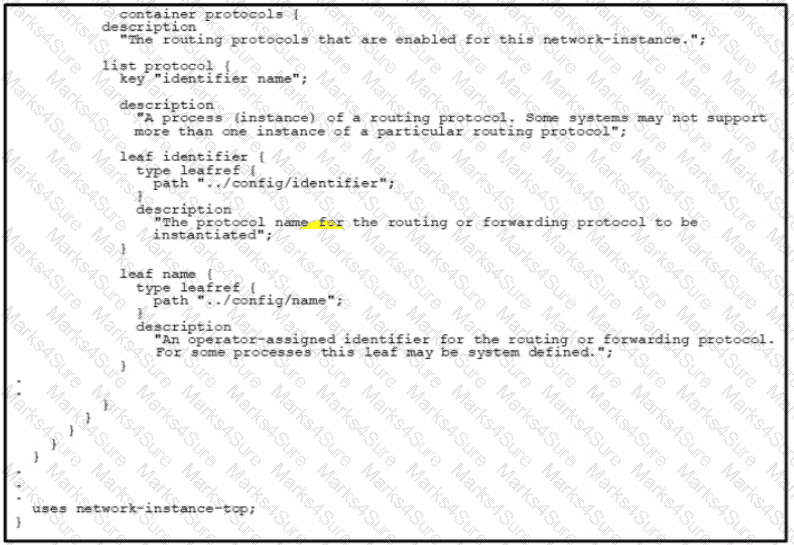
Refer to the exhibit. Which URI string retrieves configured static routes in a VRF named CUSTOMER from a RESTCONF-enabled device?
A)

B)
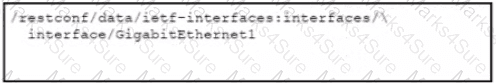
C)
D)

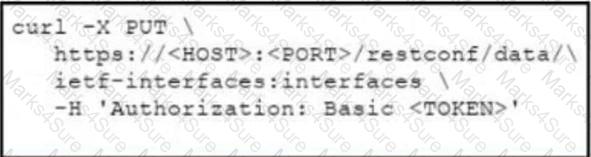
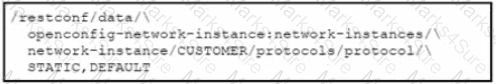
Refer to the exhibit.
Which RESTCONF verb changes the GigabitEthernet2 interface from 192.168.100.1/24 to 10.10.10.1/24
A developer is deploying an application to automate the configuration and management of Osco network files and routers The application must use REST API interface lo achieve programmability. The security team mandates that the network must be protected against DDoS attacks What mitigates the attacks without impacting genuine requests?
A developer has just completed the configuration of an API that connects sensitive internal systems. Based on company policies, the security of the data is a high priority.
Which approach must be taken to secure API keys and passwords?
A new record-keeping application for employees to track customer orders must be deployed to a company ' s existing infrastructure. The host servers reside in a data center in a different country to where the majority of users work. The new network configuration for the database server is: •IP: 10.8.32.10
• Subnet Mask: 255.255.255.0
• Hostname: CustOrd423320458-Prod-010
• MAC: 18-46-AC-6F-F4-52.
The performance of the client-side application is a priority due to the high demand placed on it by employees. Which area should the team consider in terms of impact to application performance due to the planned deployment?
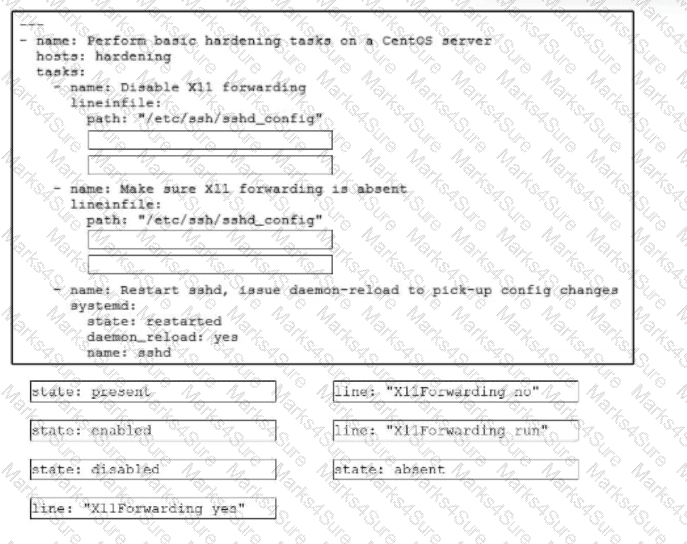
Drag and drop the code snippets from the bottom onto the blanks in the code to disable X11Forwarding on the SSH service of a CentOS server. Not all options are used.
Which type of file is created from issued intermediate, root, and primary certificates for SSL installation on a server?
A user is receiving a 429 Too Many Requests error. Which scheme is the server employing that causes this error?
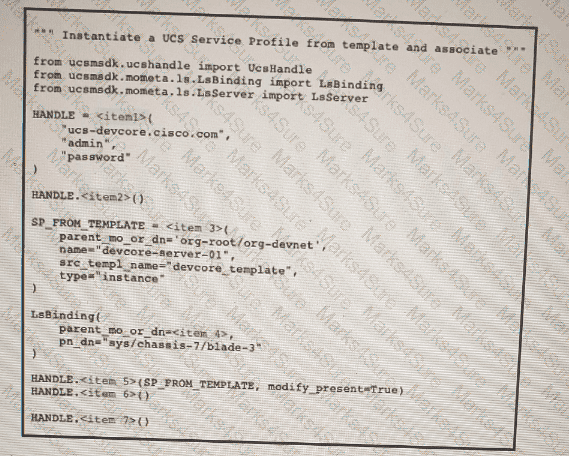
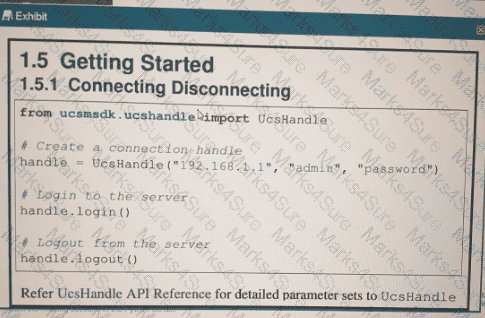
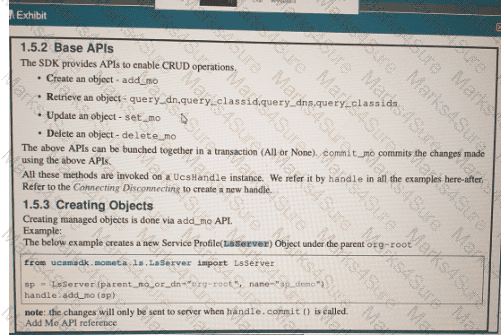
Refer to the exhibit above and click on the resource tabs in the top left corner to view resources to help with this question. Python code that uses the UCS Python SDK is instantiating a service profile named ' ' devcore-server-01 ' ' from service profile template ' ' device-template ' ' , then associating the service profile instance to blade 3 in chassis 7. Drag and drop the code snippets from the left onto the item numbers on the right that match the missing sections in the Python exhibit.