You are designing an optical network. Your goal is to ensure that your design contains the highest degree of resiliency. In which two ways should you leverage a wavelength-switched optical network solution in your network design? (Choose two.)
A regional ISP is running MPLS TE. These tunnels are configured manually using paths. Which technology centralizes the traffic engineering decisions to reduce operational complexity?
Which three network management requirements are common practices in network design? (Choose three)
Refer to the exhibit.
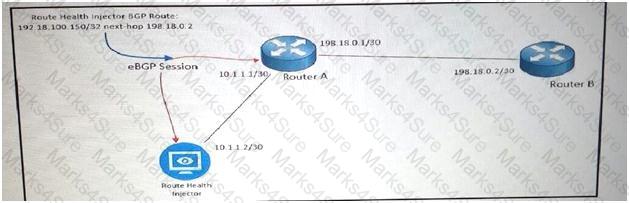
As part of your design to monitor reachable services, a route health injector has just been deployed on the network. The route health injector injects /32 host routes into BGP with the next hop of 192.18.0.2, but the /32 routes are not being installed into the RIB or FIB of Router A. Which BGP feature must be deployed to make be deployed to make the design to work?
You are designing a solution to connect a primary data center to a disaster recovery site, The hosted applications will be web and email servers that are provided through a virtualized environment. Which connectivity technology should you consider for this design?
An enterprise customer A with provider-independent address space is dual-homed to two ISP. Which two options , when combined, allow for customer A to efficiently achieve out-bond traffic load-balancing? ( Choose two)
What are two possible drawbacks of ending Loop-Free Alternate to support fast convergence for most destination IGP prefixes? (Choose two)
A service provider must provide Internet connectivity to an MPLS Layer 3 VPN customer. Which solution allows this customer to have Internet access?
A financial trading organization plans to monitor the network latency for multicast data feeds on a hop-by-hop basis. Which technology should be added to their design to support this requirement?
After a large EIGRP network had automatic summarization enabled throughout, it started experiencing routing loops. Which action should you take to quickly resolve the routing loops yet to perform summarization?
Which two functions are performed at the distribution layer of the three-layer hierarchical network design model? (Choose two)
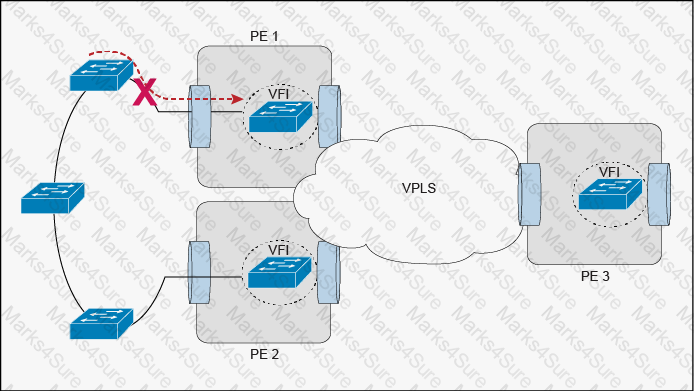
Refer to the exhibit,
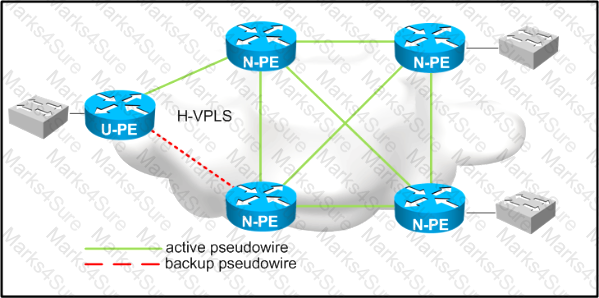
Which two design considerations should be implemented on the pseudowire between N-PE and U-PE routers for a loop-free hierarchical VPLS service? (Choose two)
Which DCI technology utilizes a “flood and learn” technique to populate the Layer 2 forwarding table?
You are working on a network design plan for a company with approximately 2000 sites. The sites will be connected using the public Internet. You plan to use private IP addressing in the network design, which will be routed without NAT through an encrypted WAN network. Some sites will be connected to the Internet with dynamic public IP addresses, and these addresses may change occasionally. Which VPN solution will support these design requirements?
You must make IGP redesign recommendations for a client that has old equipment, with low CPU power and memory, that they do not have budget replace. They are very concerned about CPU load on routers. They are using IS-IS as the IGP in a single l1 area and all routers are connected to each other with point-to-point links. Which method do you recommend to reduce or limit CPU overhead caused by IS-IS?
Which option is a design consideration when using routers in a distributed hardware architecture?
Which two functions are performed at the distribution layer of the three-layer hierarchical network design model? (Choose two).
In which two ways is a network design improved by including IP Event Dampening? (Choose two)
You are redesigning a high-speed transit network due to congestion-related issues. Which congestion avoidance mechanism can you apply to the existing network?
Which two reasons for implementing Cisco MPLS TE in a service provider MPLS backbone are valid? (Choose two.)
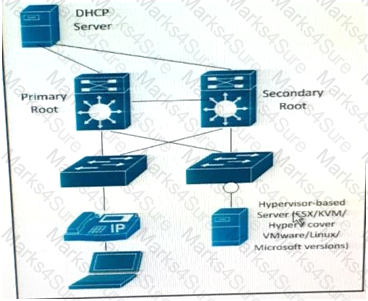
Refer to the exhibit.
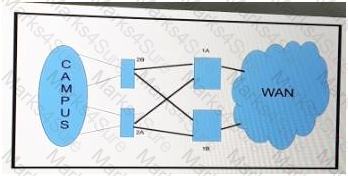
How should you redesign this network running BGP to improve availability of the routers 1A and 1B at the core site?
How must queue sizes be designed to ensure that an application functions correctly?
A small local business recently had an outage after an employee plugged a switch into the corporate network, which caused the traffic pattern in the network to change. You have been tasked to redesign the network so that this does not happen again. From the left side to the right side, drag the PVRST+ features that should be implemented to prevent the corresponding root cause. Not all sources will be used.

Which option is a critical mechanism to optimize convergence speed when using MPLS FRR?
Which IEEE standard is commonly used at the data link layer for an access network, in an IoT environment?
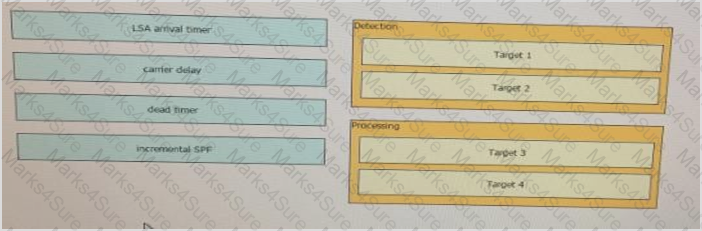
Classify the OSPF Fast Network Convergence technique by dragging the techniques on the left and dropping them into the corresponding categories on the right.
Which three network management requirements are common practices in network design? (Choose three)
Refer to the exhibit.

A customer currently has a large EIGRP-based network with several remote sites attached. All remote sites connect to the two corporate data centers, depicted as 10.1.1.0 and 10.1.2.0. The customer has experienced several network-wide failures where neighbors were stuck-in-active and had other network stability issues due to some links flapping. Which two redesign options increase stability and reduce the load on the remote site routers, still maintaining optimal routing between remote sites and the two data centers? (Choose two)
Refer to the exhibit.
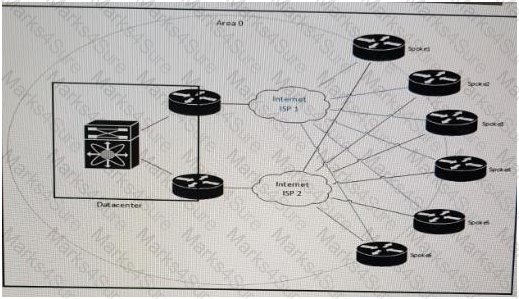
You must review this single OSPF area, DMVPN network because the company has noticed a few area 0 convergence and stability issues. Also, traffic destined to the data center from one of the spokes as the next hop on the path. The company prefers that all traffic destined to the data center uses the least amount of hops. Which solution resolves these issues with the minimum amount of changes on the network?
In a design around fast convergence in case of a link failure, what is the justification for using a point-to-point OSPF network type on the Ethernet links between leaf-and-spine switches on a data center fabric?
Which three options are important design functions of IPv6 first-hop security? (Choose three)
Refer to the exhibit.
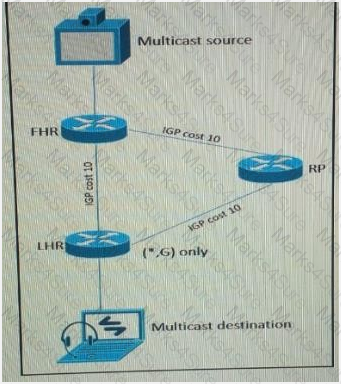 As part of a redesign project, you must predict multicast behavior. What is the resultant multicast traffic receiving on the shared tree( , G), if it is received on the LHR interface indicated?
As part of a redesign project, you must predict multicast behavior. What is the resultant multicast traffic receiving on the shared tree( , G), if it is received on the LHR interface indicated?
You are hired to assist an enterprise customer to design their global WAN network. A protected DWDM circuit with disjoint fiber routes and guaranteed restoration times is ordered to connect two hub sites. Which option is a BFD design consideration in relation to protected DWDM?
A DMVPN network is being deployed for 10 branch sites to connect to the central headquarters over the Internet. Each branch site connects to the internet via a 1.5 Mb/s ADSL line, and the headquarters connects to the Internet over a 100Mb/s circuit limited to 20 Mb/s by the service provider. Which QoS mechanism if any, do you recommend at the headquarters location?
Refer to the exhibit.
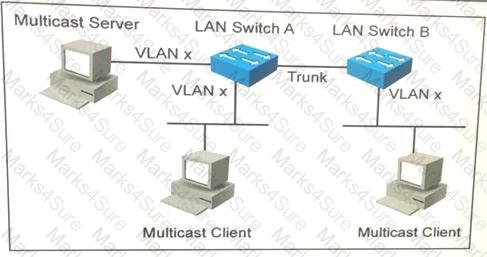
Assume that no multicast optimization is done on LAN switches A and B. Which two features can be used to optimize multicast traffic forwarding in this situation? (Choose two.)
An enterprise customer has a national WAN network based on DMVPN over the Internet, with sites located throughout the country. The customer has recently deployed VoIP throughout the entire network , and users report that it takes up to 2 seconds to establish a telephone call to an IP telephone at another office network. Drag and drop the root cause and the corresponding design solution from the left onto the correct targets on the right Not all options are used
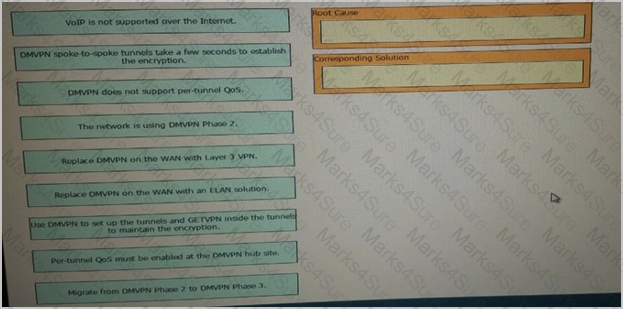
Refer to the exhibit.
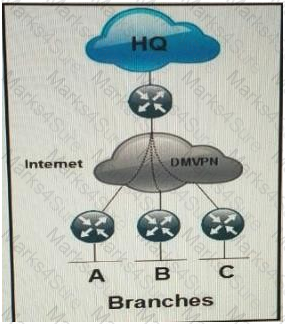
Which routing solution is the most scalable to connect the branches to the HQ and to connect the branches together over the internet using DMVPN?
Which two options are considered risks or concerns when both the Internet and VPN service functions are on the same PE router? (Choose two.)
In an OSPF network with 20 routers connected together with Ethernet cabling , which topology typically takes the longest to converge?
A large ISP is analysing which IGP meets these following requirements
Network must be resilient against unstable MTU in one side of newly released transmission pieces of equipment
Network must support MPLS traffic engineering solution for future use
Which IGP must be selected and why?
Which network topology is characterized by a link fate-sharing situation?
A)
B) 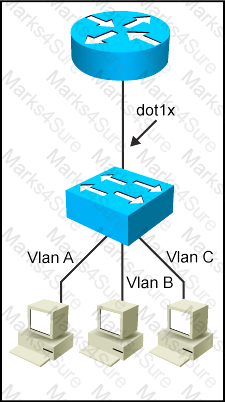
C) 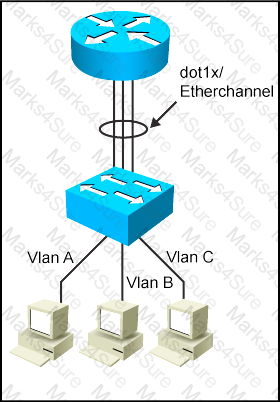
D) 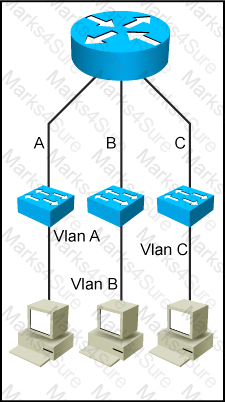
ACME Agricultural requires that access to all network devices is granted based on identify validation, and an authentication server was installed for this purpose. Currently the network team uses a list of passwords based on regions to access the internal corporate network devices. Which protocol do you recommend to ensure identify validation from the authentication server to the corporate directory?
The enterprise customer ABC Corp will deploy a centralized unified communications application to provide voice, and instant messaging to their branch offices. Some of the branch offices are located in remote locations and are connected via a 1.5 Mb/s Layer 3 VPN connection. Which two ways are the most cost-effective to ensure that this new application is implemented properly? (Choose two)
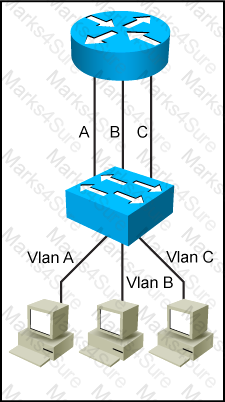
Refer to the Exhibit.
The server is running multiple VLANs on its NIC. Which two Layer 2 features should be applied to the network location identified by a circle? (Choose two)
Which two techniques are used in an OSPF network design to slow down the distribution of topology information caused by a rapidly flapping link? (Choose two)
Refer to the exhibit.
This Layer 2 ring has 10 VLANs with 1000 MAC addresses in each VLAN. Which protocol or mechanism provides the shortest traffic outage if the link marked with “X” fails?
Which two application requirements are mandatory for traffic to receive proper treatment when placed in the priority queue? (Choose two)
Which two options are design considerations when introducing FCoE into an existing network? (Choose two)
Which two functions are performed at the core layer of the three-layer hierarchical network design model? (Choose two).
An operations engineer asks for your help with a new switching deployment. The engineer confirms that STP is enabled on an edge switch, and a particular port is connected to another switch. The switch is not receiving configuration BPDUs, although it appears that everything is functioning correctly in the network. What is the design explanation?
An enterprise campus is adopting a network virtualization design solution with these requirements
It must include the ability to virtualize the data plane and control plane by using VLANs and VRFs
It must maintain end-to-end logical path transport separation across the network
resources available grouped at the access edge
Which two primary models can this network virtualization design be categorized? (Choose two)
As a part of a network design, you should tighten security to prevent man-in-the-middle. Which two security options ensure that authorized ARP responses take place according to know IP-to-MAC address mapping? (Choose two)
A new video multicast application is deployed in the network. The application team wants to use the 239.0.0.1 multicast group to stream the video to users. They want to know if this choice will impact the existing multicast design. What impact will their choice have on the existing multicast design?
Refer to the exhibit.
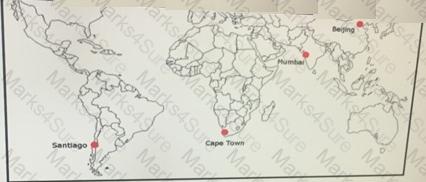
ACME Mining has four data centers in Santiago, Cape Town, Mumbai, and Beijing. They are full-mesh connected via a 400 Mb/s EVP-LAN. A 1-TB transfer occurs daily via FTP between the Santiago and Mumbai data centers. When testing, the data transfer took an ' ' unexpected and outrageous, with an average transfer rate of 47 KB/s. The team provided this information.
LAN bandwidth usage below 5% at both data centers during transfer.
WAN bandwidth usage was between 20-30% at both data centers during transfer.
The only QoS on WAN is KB/s strict priority configured for other types of traffic.
There is no QoS on LAN.
The ping RTT average between data centers is 378 milliseconds.
Which action improves the file transfer rate?
How can a network designer reduce the amount of LSA flooding occurring in a large, single area fully-meshed OSPF topology?
A healthcare customer requested that health statistics from their infrastructure devices are to be sent over their service provider MPLS network. Which protocol must be enabled?