3V0-24.25 Advanced VMware Cloud Foundation 9.0 vSphere Kubernetes Service Questions and Answers
What tool can be used to back up and restore workloads on clusters provisioned by vSphere Supervisor?
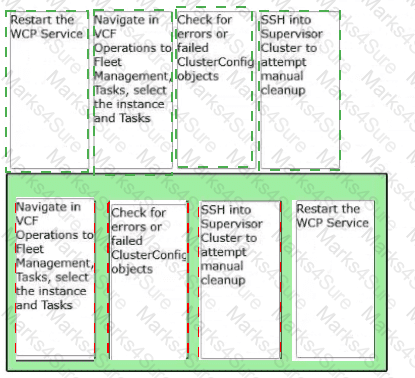
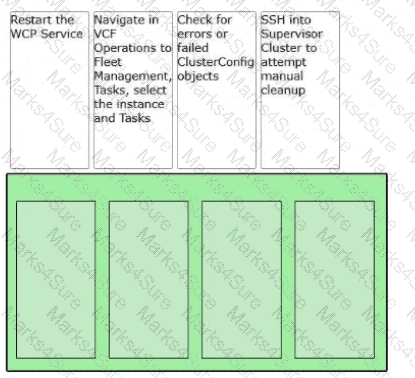
An administrator upgrades a VMware Cloud Foundation (VCF) Supervisor and the upgrade fails. Order the steps the administrator should take to determine the cause of the failure.
An administrator is tasked with making an existing vSphere Supervisor highly available by adding two additional vSphere Zones. How should the administrator perform this task?
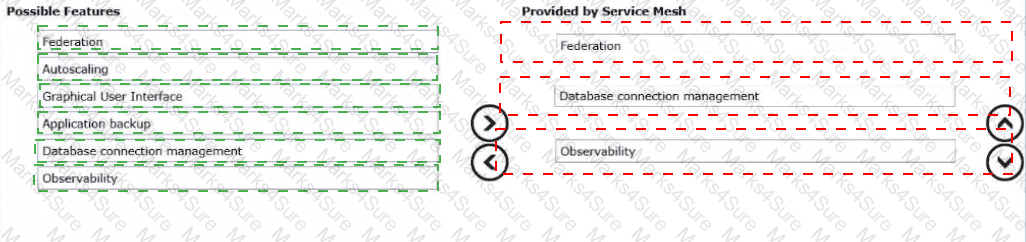
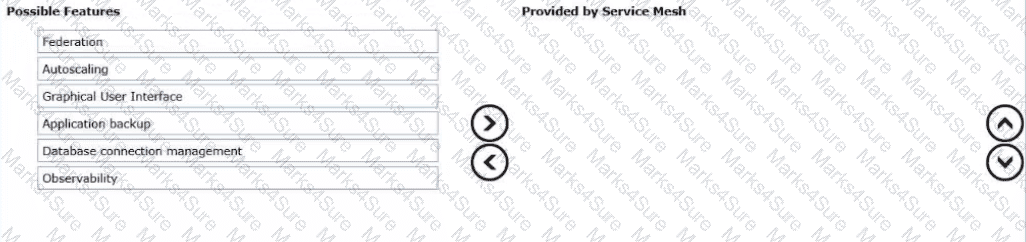
Drag and drop the three features into the correct order from Possible Features list on the left and place them into the Provided by Service Mesh on the right side. (Choose three.)
What three components run in a VMware vSphere Kubernetes Service (VKS) cluster? (Choose three.)
An administrator is upgrading an existing VMware vSphere Kubernetes Service (VKS) cluster and receives the following errors:
kubectl get nodes fails with memcache.go and “server is currently unable to handle the request”
couldn ' t get resource list for stats.antrea.tanzu.vmware.com/v1alpha1
yaml: mapping values are not allowed in this context
The administrator successfully updated the Supervisor, but an attempt to update the VKS cluster failed. Based on the scenario, what is the cause of the problem?
A VKS administrator is tasked to leverage day-2 controls to monitor, scale, and optimize Kubernetes clusters across multiple operating systems and workload characteristics.
What two steps should the administrator take? (Choose two.)
An administrator is maintaining several Kubernetes clusters deployed through a Supervisor Namespace in a vSphere Kubernetes Service environment. One of the microservices, a containerized API gateway, has started failing intermittently after a recent configuration update. Initial investigation shows that the pod is entering a CrashLoopBackOff state. The administrator needs to collect detailed runtime information directly from the pod, including both the standard output (STDOUT) and standard error (STDERR) streams, to analyze the application ' s behavior before the crash. Which command produces the required output?
A company standardized on the following configurations:
• vSphere Kubernetes Service (VKS) upgrade is separate from vCenter upgrades.
• A private registry will be utilized.
How should an administrator adhere to these standards?
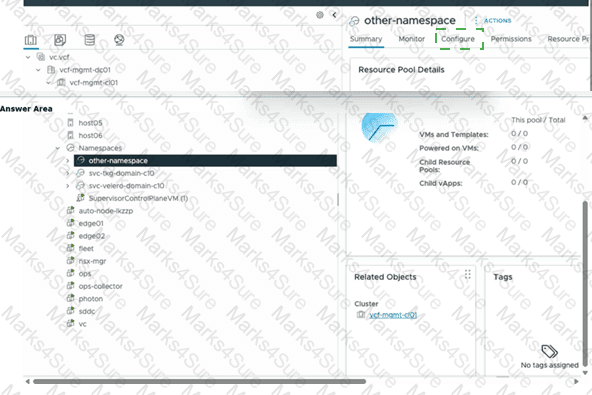
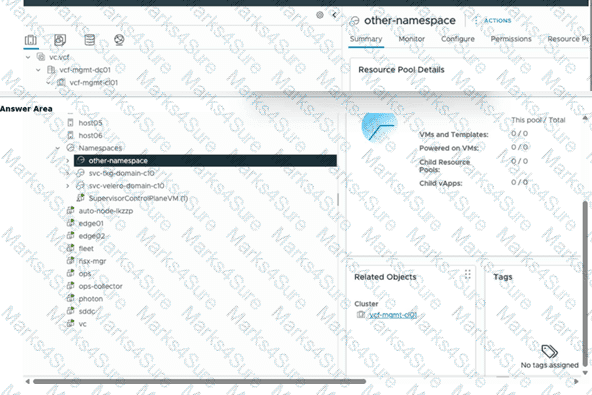
An administrator is tasked to create a new vSphere Zone for the highlighted namespace. Click the section of the interface where the administrator would navigate to start creating a new zone.
An administrator must create amulti-zone vSphere Supervisor deployment in a VMware Cloud Foundation (VCF) environment. What is the primary purpose of this configuration?
An administrator is configuring the Supervisor Service in vCenter.
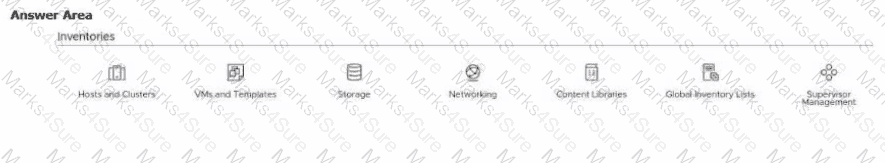
Click the option an administrator uses to begin creating a vSphere Supervisor Zone.
An administrator is adding a kubernetes cluster to an existing namespace. Click where the administrator navigates to create the cluster.
An administrator is tasked with installing Istio Service Mesh for VMware vSphere Kubernetes Service (VKS). Which command installs Istio?
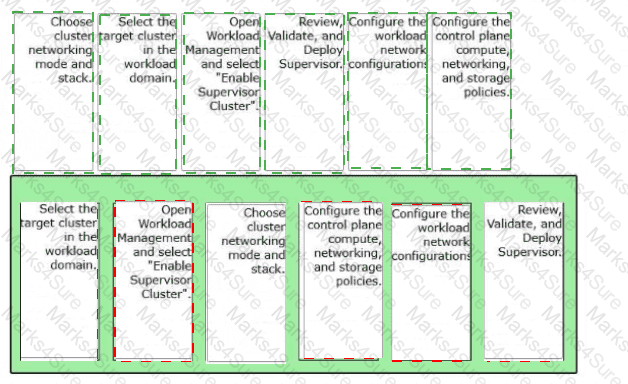
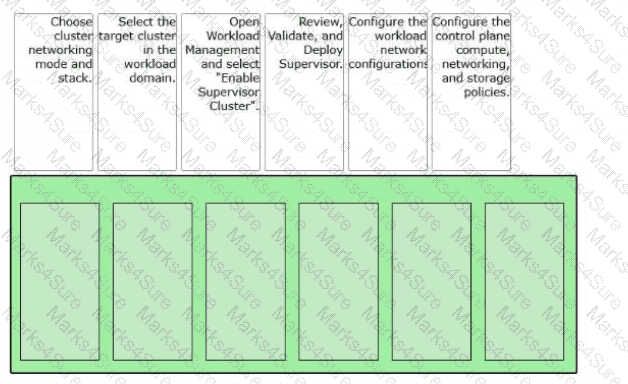
An administrator is tasked with enabling a Supervisor cluster in VMware Cloud Foundation (VCF).
Arrange the steps below In the correct order to complete the process of enabling a Supervisor In the environment.
An architect is working on the data protection design for a VMware Cloud Foundation (VCF) solution. The solution consists of a single Workload Domain that has vSphere Supervisor activated. During a customer workshop, the customer requested thatvSphere Podsmust be used for a number of third-party applications that have to be protected via backup.
Which backup method or tool should be proposed by the architect to satisfy this requirement?
A cloud operations team is managing multiple Supervisor Clusters across two regions. Each region hosts its own vSphere Kubernetes clusters, integrated through a federated service mesh to enable consistent service connectivity and policy enforcement across environments.
The application team wants to expose a multi-tier microservice named “GovApp”, which includes front-end, API, and database services distributed between the two regions. Uniform traffic routing, identity, and security policies are also needed for these workloads regardless of the cluster or region in which they are deployed.
To meet these requirements, the architects decide to create a Global Namespace that spans both Supervisor Clusters.
Which two statements describe the requirements for a Global Namespace in a vSphere Kubernetes Service Mesh deployment? (Choose two.)
What are three benefits of VMware vSphere Kubernetes Service (VKS)? (Choose three.)
What statement describes the vSphere Supervisor in VMware Cloud Foundation (VCF)?