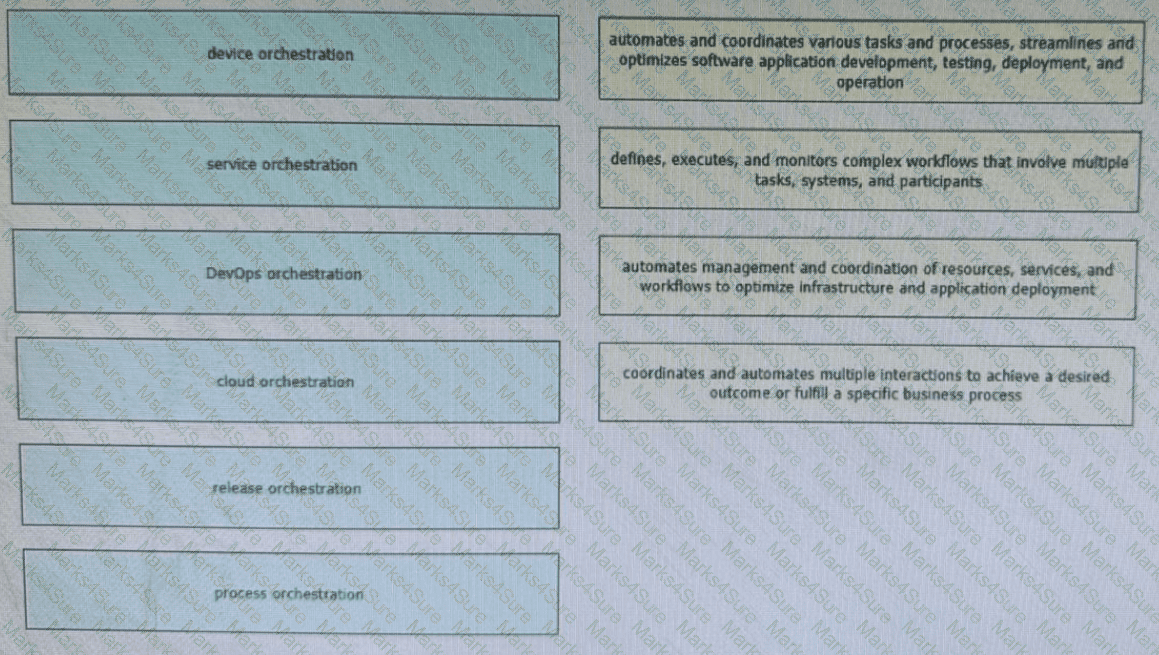
Network orchestration enables network administrators to focus on strategic initiatives, innovation, and value-added tasks rather than spending time on manual and repetitive network management activities. Drag and drop the orchestration types from the left onto the corresponding functions on the right. Not all options are used.
What is the primary benefit for an organization that dynamically can expand their private cloud capacity by allocating additional compute and/or storage resources using a third-party service provider or partner?
A network consists of multiple planes where each plane represents a different area of network operations and cames different types of network traffic Which two statements describe the concepts of assurance in the context of control planes ' ? (Choose two.)
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
Which redundancy element plays a crucial role in ensuring business continuity even in challenging situations?
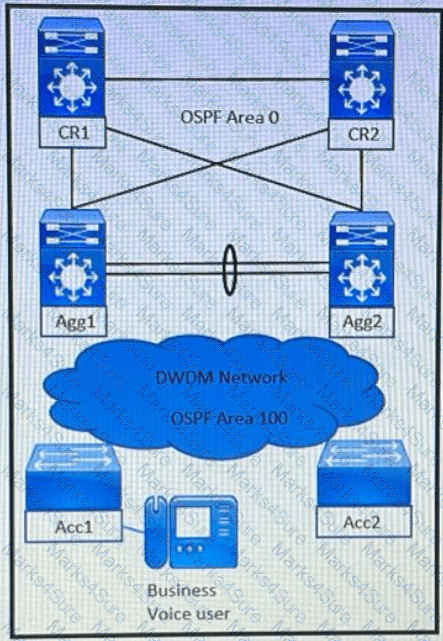
Refer to the exhibit A solution architect is tasked with designing a quick fault detection and convergence solution based on a set of requirements
•Due to the use of voice applications, users must ideally not experience traffic disruption in excess of 100 milliseconds in case of link or node failures in OSPF area 100. •The enterprise requires the network to be highly available
•Traffic must quickly switch to another path without waiting for the OSPF dead interval to kick in What can be included in the design in order to meet these requirements?
Company XYZ wants to improve the security design of their network to include protection from reconnaissance and DoS attacks on their sub interfaces destined toward next hop routers. Which technology can be used to prevent these types of attacks?
A bank recently had their security compromised during an initial key exchange between devices using a symmetric cryptography algorithm, and as a result the key was revealed/leaked. Going forward, they want to ensure that key exchanges are performed using asymmetric cryptography algorithms. Which algorithm offers the desired functionality?
Modem IT departments are more service oriented than they used to be To meet the needs oí their customers. IT departments are spending more time analyzing and documenting their processes for delivering services A focus on processes helps to ensure effective service delivery and to avoid wasted expenditures on technology that doesn ' t provide a needed service What defines frameworks and processes that can help an organization match the delivery of IT services with the business needs of the organization?
Which purpose of a dynamically created tunnel interface on the design of IPv6 multicast services Is true?
Company XYZ wants to implement an IPS device to detect and block well-known attacks against their network They want a design solution where all packets that are forwarded to the network are checked against a signature database before being allowed through This check must be done with the minimum effect on performance Which design is recommended?
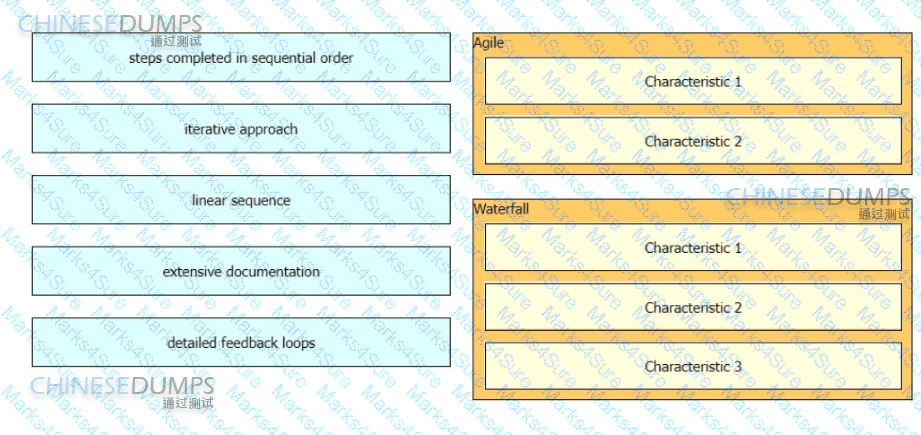
A consultant needs to explain different project management methodologies to a customer.
Drag and drop the characteristics from the left onto the corresponding methodologies on the right in no particular order.
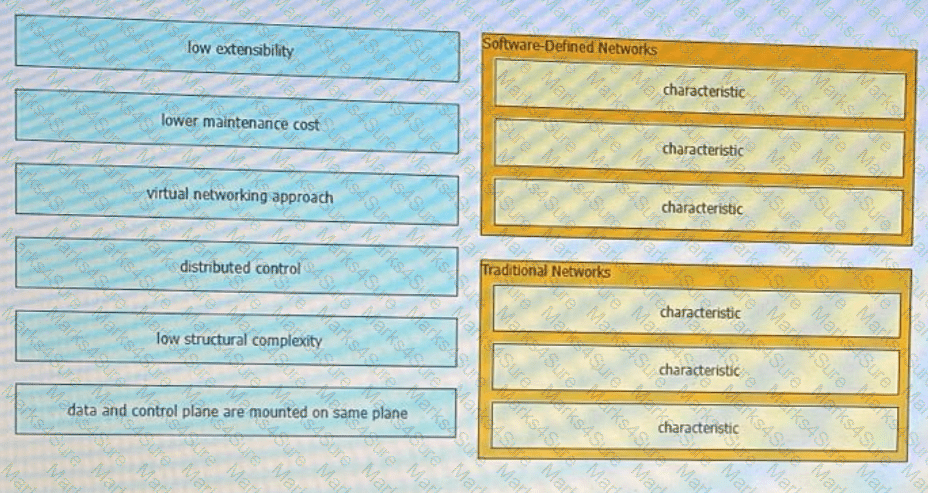
Comparing traditional networks with SDN, where the network is only application aware, what is the advantage of SDN architecture?
What is the best approach to ensure both scalability and high availability for a cloud-based storage solution over the IP network?
A customer migrates from a traditional Layer 2 data center network Into a new SDN- based, spine-and-leaf VXLAN EVPN data center within the same location. The networks are joined to enable host migration at Layer 2. Which activity should be completed each time a legacy network is migrated?
When a traditional network is transformed to a hierarchical network, the state information in the control plane is reduced so that changes in one area of the network do not result in changes in the routing table on devices half-way around the globe What is a potential trade off in these cases?
Company XYZ has implemented policy-based routing in their network. Which potential problem must be kept in mind about network reconvergence and PBR?
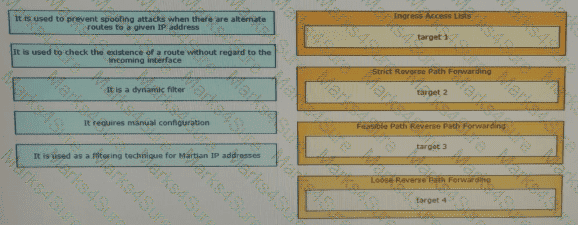
Drag and drop the design characteristics from the left onto the correct network filter techniques on the right. Not all options are used.
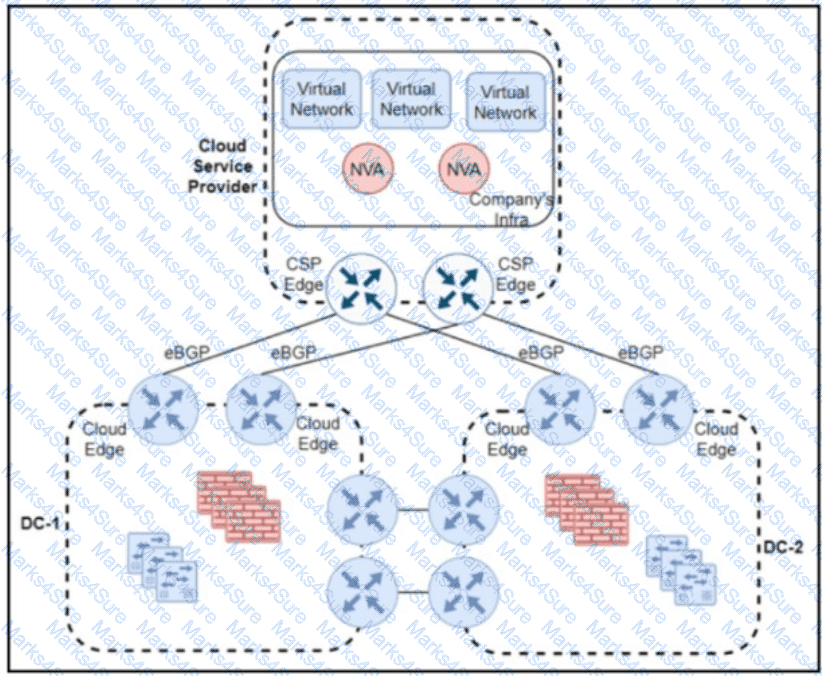
Refer to the exhibit A company has a hybrid cloud architecture with two on-premises data centers that connect to a public cloud service provider by using direct connect and eBGP routing. Encryption is unsupported by the cloud service provider, so the company plans to use an IPsec overlay network over its direct connects. Two virtual network appliances will be installed in the cloud infrastructure to establish tunnels and perform routing The company chose OSPF as the overlay routing protocol because the operations team is familiar with the protocol and because OSPF is the IGP on the on-premises network. The cloud network must be as isolated as possible from the on-premises network. What must be used for the OSPF overlay connectivity ?
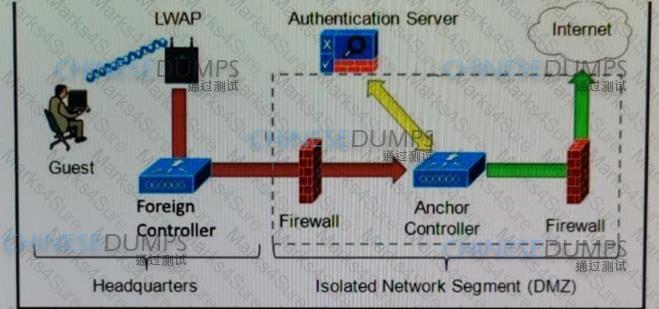
Refer to the diagram. Which solution must be used to send traffic from the foreign wireless LAN controller to the anchor wireless LAN controller?
As part of a design solution a consultant needs to describe the trade-offs between different SDN models Drag the characteristics on the left to the correct controller-based network designs on the right in no particular order.

A bank has two data centers (Primary and DR), and compliance policies mandate that services or servers can be moved seamlessly between the two data centers. Additionally, the technology cannot be locked to a specific vendor and must offer good scalability with broad support of layer 2 protocols. Which protocol meets these requirements?
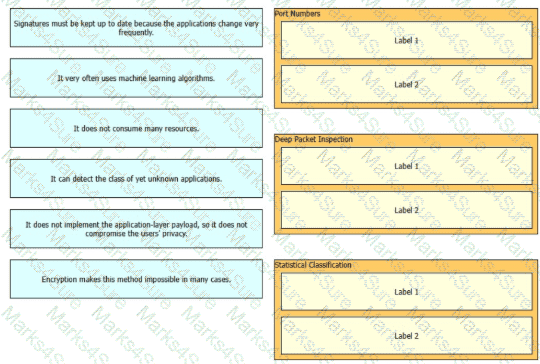
Drag and drop the descriptions from the left onto the corresponding categories on the right Not all options are used
A large enterprise customer is planning a new WAN connection to its headquarters The current architecture is dual homed with static routing but users complain when a specific link fails Failure of the other link does not affect any services or applications The new WAN connection must provide the headquarters with a resilient network design and increase the return on investment Which solution should be recommended to the customer?
Which technique facilitates analytics and knowledge discovery in big data systems to recognize hidden and complex patterns?
What are two reasons for a company to prefer a hybrid approach rather than a mixed approach while transitioning to a software-defined network? (Choose two.)
A large defense organization is planning their cloud migration journey, but they have high data sovereignty concerns, major regulation or compliance requirements, and very restrictive SLAs. Which cloud architecture model can be adopted?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
An engineer is designing a DMVPN network where OSPF has been chosen as the routing protocol A spoke-to-spoke data propagation model must be set up Which two design considerations must be taken into account ? (Choose two)
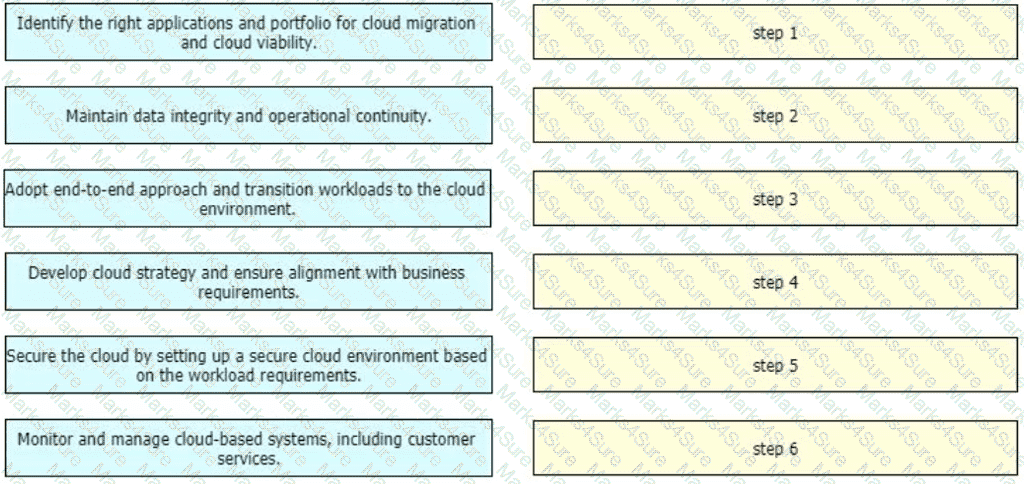
An enterprise wants to migrate an on-premises network to a cloud network, and the design team is finalizing the overall migration process. Drag and drop the options from the left into the correct order on the right.
What are two parameters that can be leveraged by SAML in mixed private/public cloud environments by using identity and asset management? (Choose two)
What are two advantages of the Agile project management methodology? (Choose two)
Which action must be taken before new VoIP systems are implemented on a network to ensure that the network is ready to handle the traffic?
Refer to the table. A customer investigates connectivity options for a DCI between two production data centers. The solution must provide dual 10G connections between locations with no single points of failure for Day 1 operations. It must also include an option to scale for up to 20 resilient connections in the second year to accommodate isolated SAN over IP and isolated, dedicated replication IP circuits. All connectivity methods are duplex 10 Gbps. Which transport technology costs the least over two years, in the scenario?
Organic growth or decline comes from a company ' s normal business activities, rather than through acquisitions or divestment. Changes in usage patterns can also cause organic change in network requirements Which tool is useful when designing and operationalizing a network that is in the process of change?
Drag and drop the right functional descriptions from the left onto the corresponding protocols on the right.

The development of a connected ecosystem of devices reflects manufacturers ' heightened focus on internal needs and issues as they work to increase product resiliency and improve customer experience In which two ways can network visibility contribute to resilient software defined networking? (Choose two.)
Most security monitoring systems use a signature-based approach to detect threats. In which two instances are systems based on Network Behavior Anomaly Detection better than signature-based systems when it comes to detecting security threat vectors? (Choose two.)
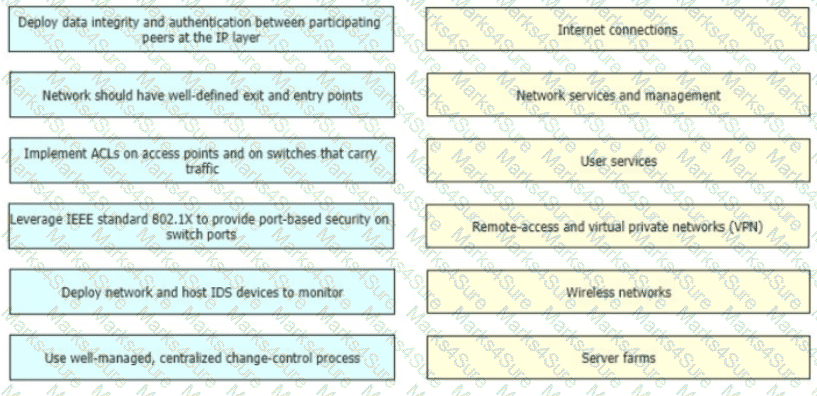
Security experts promote the security defense-m-depth principle which states that network security should be multilayered and modular and multiple methods should be designed and applied to different parts of the network Drag and drop the characteristics on the left to the matching enterprise network components on the right.
Company XYZ plans to run OSPF on a DMVPN network They want to use spoke-to-spoke tunnels in the design What is a drawback or concern in this type of design?
Software-defined network and traditional networks might appear the same to the end-user, but behind the scenes, each has unique sets of characteristics. Drag and drop these characteristic found on the left to the corresponding category on the right in no particular order?
An enterprise SDWAN customer based in the US has several branches in Europe Currently branches use the HQ in the US to access both internal and external services over an MPLS arcuit The design team has been tasked to suggest a solution allowing branches to access their cloud-based office productivity tools and services directly Since all their applications and services are hosted in the cloud, the design team has also been asked to come up with a solution, so branches can connect to the cloud directly from the branch as well Which two cost-effective and optimized solutions can be suggested? (Choose two)
cloud onRamp (SaaS)
Piggybank, a leading financial institution, is planning to migrate its business-critical operations to a hybrid cloud solution A recommendation of the most appropriate security measure to protect sensitive financial data during data transmission must be given to the board of directors Which solution will meet these requirements?
Company XYZ wants to redesign the Layer 2 part of their network and wants to use all available uplinks for increased performance They also want to have end host reachability supporting conversational learning However, due to design constraints, they cannot implement port-channel on the uplinks Which other technique can be used to make sure the uplinks are in active/active state?
A global e-commerce company is expanding its operations and planning to migrate its entire infrastructure to a hybrid cloud solution. They are concerned about data governance and want to ensure that their customers ' data is treated with utmost respect to sovereignty and privacy. What is an appropriate approach?
Virtualization pose a special challenges for NAC because virtual servers can move around a data center, and the VLAN can change as the servers move. What is an option that can be used to improve security in this condition?
A lead network architect is tasked with designing the optimal cloud-based solution for a rapidty growing e-commerce company that heavily relies on its online platform for sales and customer interactions The company’s business critical operations induce real time inventory management, order processing, and payment processing The executive team has decided to migrate their infrastructure to the cloud to improve scalability and recoce operational costs Which cloud service model(s) needs to considered?
Which interface between the controller and the networking device enables the two to communicate and allows the controller to program the data plane forwarding tables of the networking device?
A European government passport agency considers upgrading its IT systems to increase performance and workload flexibility in response to constantly changing requirements. The budget manager wants to reduce capital expenses and IT staff and must adopt the lowest-cost technology. Which technology choice is suitable?
There are varying requirements and motivations for improving the scalability and resilience of an enterprise application. The relative importance of these requirements and constraints varies depending on the type of app. the profile of the users, and the scale and maturity of the organization in which it is deployed. What are two common business drivers that deals with these aspects? (Choose two.)
A large enterprise cloud design team is evaluating different cloud consumption models What is an example of typical PaaS limitations or concerns that should be considered during service design?
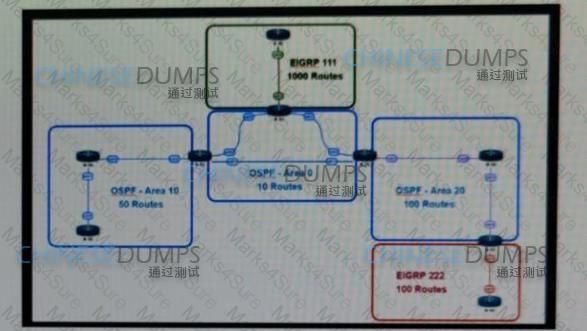
Reter to the exhibit This network is running OSPF and EIGRP as the routing protocols Mutual redistribution of the routing protocols has been contoured on the appropriate ASBRs The OSPF network must be designed so that flapping routes m EIGRP domains do not affect the SPF runs within OSPF The design solution must not affect the way EIGRP routes are propagated into the EIGRP domains Which technique accomplishes the requirement?
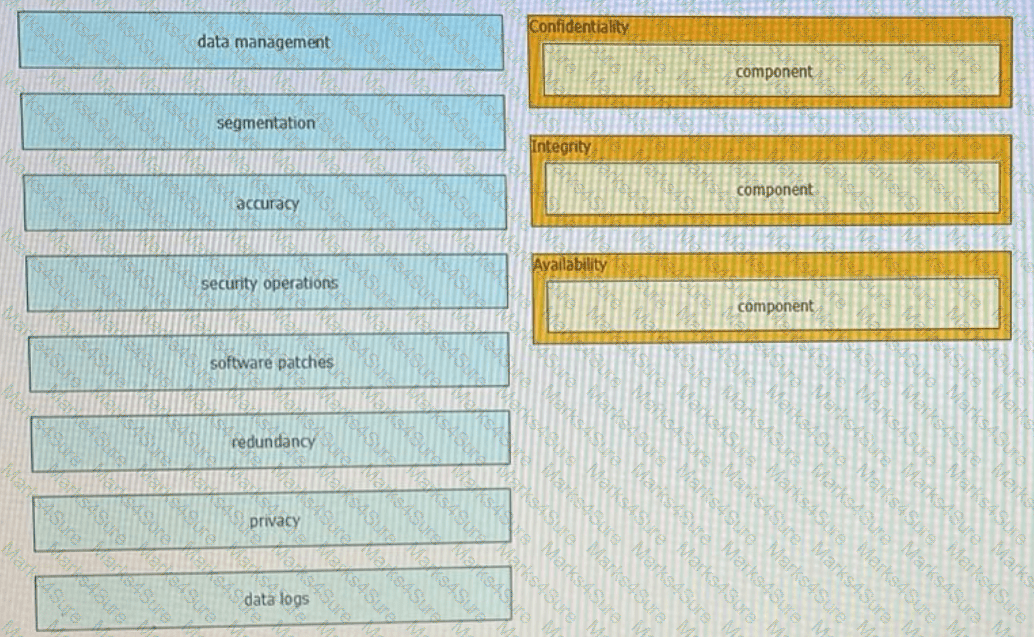
Drag t he components that are part of the CIA triad to the correct target on the right. Not all components are used.
Which CIA triad principle is used by social media platforms to constitute a standard procedure of user IDs and passwords requirements?
If the desire is to connect virtual network functions together to accommodate different types of
network service connectivity, what must be deployed?
The modular design model approach allows companies to have a network infrastructure that is better suited for scalable applications What is the benefit for companies that use this model?
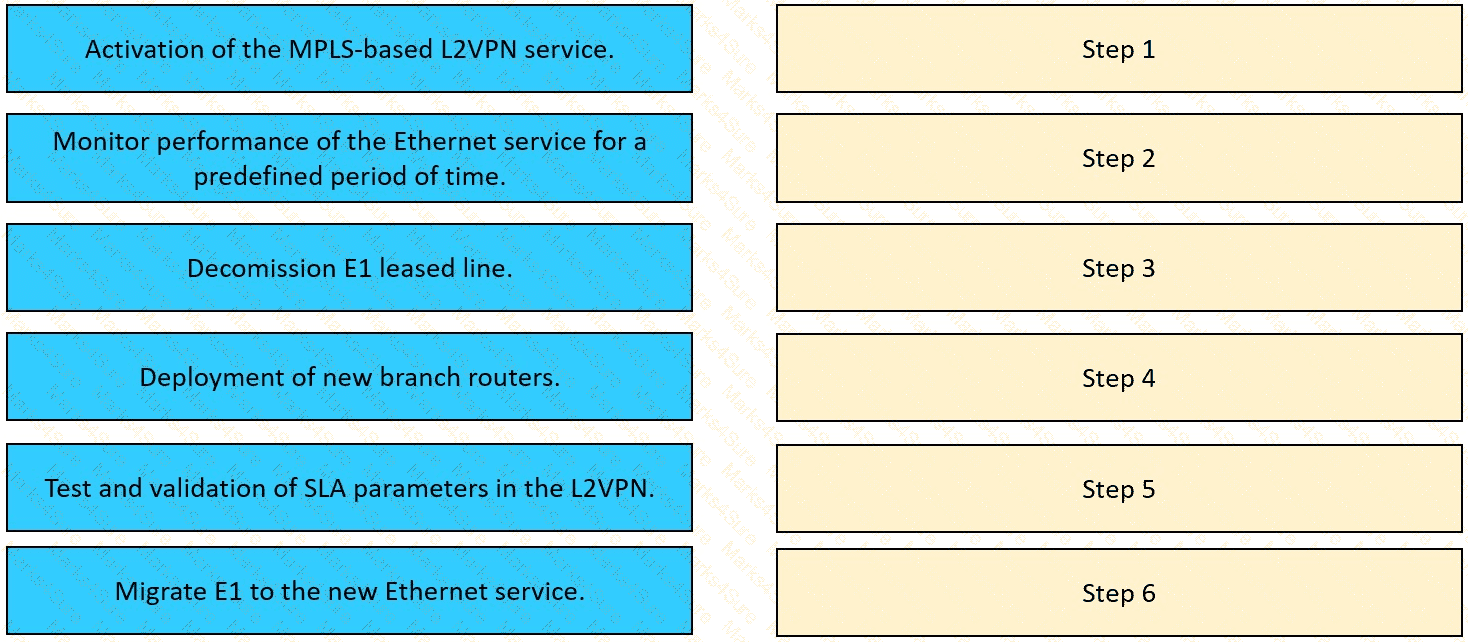
The network team in XYZ Corp wants to modernize their infrastructure and is evaluating an implementation and migration plan to allow integration MPLS-based, Layer 2 Ethernet services managed by a service provider to connect branches and remote offices. To decrease OpEx and improve
response times when network components fail, XYZ Corp decided to acquire and deploy new routers. The network currently is operated over E1 leased lines (2 Mbps) with a managed CE service provided by the telco.
Drag and drop the implementation steps from the left onto the corresponding targets on the right in the correct order.