A company is creating a new department for Security Engineering and needs to create a segregated network segment with only 24 IPS.
What should be configured?
What advantage does an active-standby configuration have over an active-active configurations?
Which protocol is used for control and session establishment for streaming media?
In the Network Map a red diamond appears next to the three member servers in the Virtual Server’s pool. The nodes in the pool each show a green circle. What is the most likely reason for this scenario?
An administrator points the browser at h.tp://www mydomain com. The destination server listens on TCP port 8080 Which feature must be enabled on the virtual server for this configuration to work?
A BIO IP Administrator is troubleshooting a slow web application. A packet capture shows that some of the packets coming from a window size of zero A packet capture shows that som a window size of zero
What does this mean?

An administrator sets up a web server for a new web application. The administrator cannot access the web server at is causing this issue?
AD VLAN must be created with an 802.19 tag of 705 on interface 11. What is the proper TSH command to create this new VLAN on the BIG-IP?
An administrator deploys a site in which the load balancer only sees the ingress traffic from the client All egress traffic from the server bypasses the load balancer.
Which type of solution is this?
A new virtual server is being tested to replace http://myapp.mydomain.com. The original virtual server is still on use. And the new virtual server is on a different ip address. What should be done to test this new virtual server using the fully quailed domain name for this application?
A BIG IP Administrator wants to add a new VLAN (VLAN 40) to an LACP trunk (named LACP01) connected to the BIG-IP device Mufti VLANS exist on LACPO1. Which TMSH command should the BIG IP Administrator issue to add the new VLAN to the existing LACP trunk?
What is a benefit of configuring BIG-IP devices in active-active high availability mode?
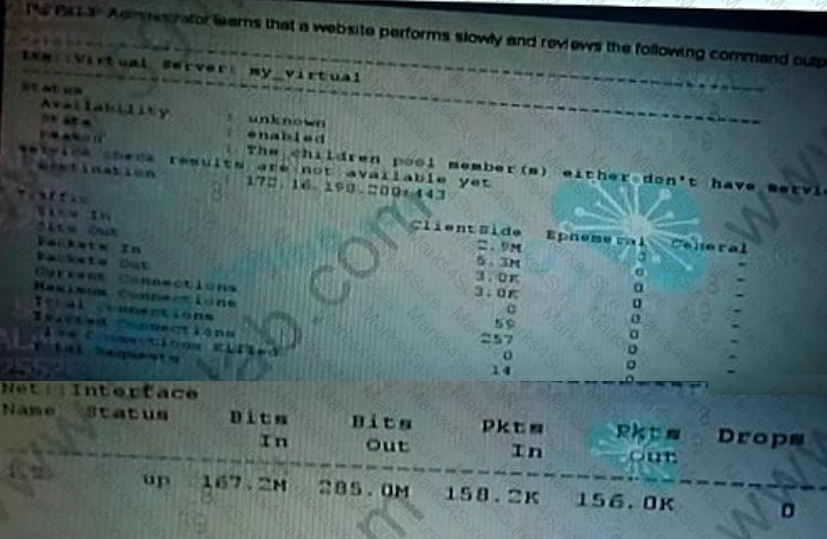
What should the administrator investigate first to address this traffic slownes
An administrator needs to load balance connections to the application server with the lowest number of
Which load balancing method meets these requirements?
The use of attack signature within an intrusion Detection System (IDS) is an application of which security model?
What should the BIG-IP Administrator configure to perform SSL offloading when the certificate is already imported on the BIG-IP device?
Host A sends 10 TCP packets to Host B. All packets arrive at Host B quickly, but some arrive out of order.
What will Host B do?
A BIG-IP Administrator needs to make sure that requests from a single user are directed to the server that was initially selected (unless that server is marked down). What should the administrator configure?
The administrator wants client request to be directed to the same pool member through the session based on the client IP address.
Which persistence method should the administrator choose?
Which Datalink sublayer has the primary funcl.cn of proving node lo node flow and error control?
End users report widespread issues accessing multiple network resources
What tool should the BIG IP Administrator use to view the status of all virtual servers and associated resources in one place?
in which scenario would an SSL VPN solution have an advantage over an IPSec VPN?
What command sends an "Echo Request' message and expects an "Echo Reply" message?
Which Transport Layer Security (TLS) extension can be used to enable a single virtual server to serve multiple HTTPS websites in different can be used to enable a single virtual server to server domains?
A BIG IP administrator recently reset statistics for interfaces 1. 1 and 1. 2. The administrator notices that traffic appears on a data plane interface without receiving any client requests All nodes and pools have monitoring enabled, and all routes are locally defined on the device All management traffic is sent over the mgmt interface. What is the nature of this traffic?
A BIG-IP Administrator needs to upgrade an HA pair to a more recent TMOS version. The administrator is unsure if the BlG-IP is currently supported How should the administrator verity that the HA pair is under a valid support contract?
ATP administrator recently added a new VLAN and needs to confirm that the BIG IP sees traffic on this VLAN. The VLAN is untagged on interface 1.1 and is named VLAN704 in the BIG IP Configuration Unity.
Which tool should be used to generate a packet capture that shows all traffic on this VLAN?
A device needs to decrypt traffic and send unencrypted traffic to the web server. Which method should the BIG-IP Administrator use?
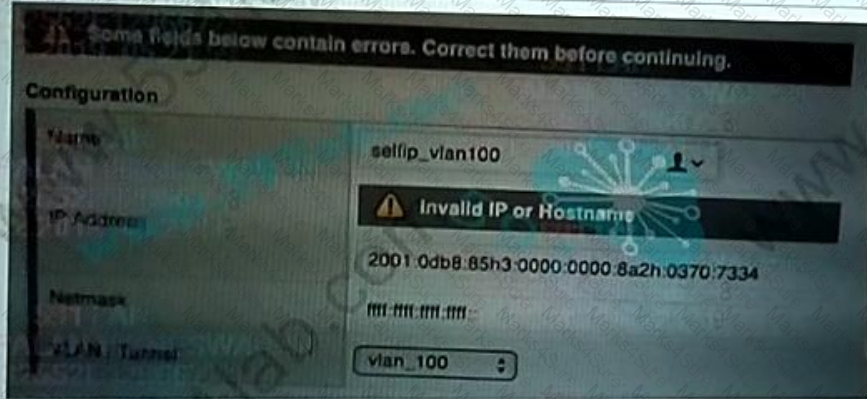
An administrate receives an error message when attempting to create a self-IP address on a BIG-IP appliance Which address should the administrator use to resolve the issue?
A 2001 0db8.85a3 0000 0000 8a2e 0370 7334
B. 2001:db8:85a3 Bd3.Ba2e.370 7334
C. 2001:0db8:85i3:0000:0000: : 8a2i:0370:7334
What should a BIG-IP Administrator configure to minimize impact during a failure?
What is one way that a application delivery controller lowers the CPU-load on web servers?
An administrator needs to allow secure access to application within the corporate data center for remote office, branch office and mobile employees.
Which F5 product provides this functionally?
A company deploys F5 load balancers to manage a large number of secure applications. The company manage certificates. Which F5 provides this functionality?
The HTTP 1.1 standard is being used as part of communication to a server. The client fails to maintain the session within the maximum timeout defined by the server. Which device is responsible for ending the HTTP session?
An application has a mix of both and short and long lived connections. Which algorithm would provide and event distribution of all connections across the pool?
Which protocol data unit (PDU) is associated with the OSI model’s Physical layer?
A BIG-IP Administrator needs to configure a MAC masquerade address for traffic-group 1.
Where on the GUI should this configuration be performed?
An administrator is performing a capture from a lagged port on an Ethernet SWITCH.
Which OSI layer should be inspected to determine with which VLAN a datagram is associated?
A client is transmitting a large amount of data to a server During this process, the server sets the window size to zero What is the likely cause of this issue?
An IPv4 client tries to access to http://www myserver com
Which type of DNS request should the client send to its configured DNS server?
Web application http://www example.com at 10.10.1.1.10 is unresponsive. A recent change installed new firewalls in the network. Which command should be used to locate where data loss has occurred within the network?
A)
B)
C)
D)
A BIG-IP Administrator wants to send packets from one subnet to another. What device is required to allow this to function?
In which FTP mode is the serve, responsible for initiating the data correction back to the client?
Which method should an administrator of the BIG-IP use to sync the configuration to only certain other BIG-IPs?
An administrator needs to provide access to corporate resources for remote users. The administrator also needs to verify that the remote use has anti-virus software installed. Which F5 product provides this functionality?
Which two functions of AAA does Security Assertion Markup Language (SAML) identity Provider (IdP) offer (Choose two)?
A BIG-IP Administrator configures three Network Time Protocol servers to keep the time of the devices in sync. Which tool should the administrator use to show the synchronization status with the Network Time Protocol servers ?