The function of journaling in the Mac OS Extended (Journaled) file system is to ________.
When an OS X computer starts up and a standard user logs in, in what order do the three components below launch?
In OS X Mountain Lion, where do most applications that are NOT sandboxed store their user-specific preferences?
How can you find out which application the Finder will use to open a specific document?
How can a user with the short name anna exclude the /Users/anna/Downloads/ folder from Time Machine backups?
Which folder contains items that instruct the launchd process what to launch during OS X Mountain Lion startup?
You have a user account on an OS X Mountain Lion computer that has multiple user accounts. How can you interact with another user ' s Dropbox folder that has default permissions?
You want to delete several applications by dragging them to the Trash. What fact should you be aware of?
Which of these is a recovery key storage location that FileVault 2 offers when you enable it?
Which statement best describes how Time Machine stores files from an OS X Mountain Lion computer, when backing up to a directlyconnected FireWire hard disk drive?
You can deselect the option to " Reopen windows when logging back in " from the logout verification dialog. You can deselect the option to " Close windows when quitting an application " from General preferences. Also from General preferences, you can select the option to " Ask to keep changes when closing documents, " which turns off the Auto Save feature.
The Setup Assistant process guides a user through initial configuration of OS X Mavericks.
If an issue disappears when a Safe Boot is successful, you must find and remove the third-party startup resource that caused the issue. The best way to isolate the problem is to start up the Mac in Verbose mode and then observe where the startup process fails. Verbose mode is initiated by holding down Command-V during system startup.
Metadata is information stored outside of a file or folder. It provides additional information about files and folders. Examples include: file flags, extended file attributes, and permissions.
(No Answer)
What are the primary user session stages in OS X? What are the visual and audible cues of these items?
Any account password reset process won ' t change any keychain passwords. Therefore, the user ' s keychains won ' t automatically open when the user logs in with her new password. The user will have to manually change her keychain passwords using the Keychain Access utility.
Client software is used to access network services provided by server software. The connection is established using a common network protocol known by both the client and server software. Thus, the client and server software can be from different sources.
The OS X Mavericks installer can be downloaded from the Mac App Store for free.
The Privacy pane of Security & Privacy preferences can be used to allow or disallow applications ' access to Location Services, Contacts, Calendars, Reminders, social network services, and Accessibility application access.
How does the default organization of the file system allow users to safely share local files and folders?
The Font Book application shows a small dot next to the name of any font that has duplicate resources.
How can you verify that the system can establish a connection to a remote network host?
The minimum requirements for upgrading OS X Mavericks are:
• OS X v10.6.8 or later
• 2 GB of memory
• 8 GB of available space
• Some features require an Apple ID
• Some features require a compatible Internet service provider
• Compatible Mac model (as listed on www.apple.com/osx/specs/)
FileVault 2 protects the entire system volume and all its data by using strong XTS- AES 128 encryption. During system startup, a FileVault-enabled user must enter her password to decrypt the system volume.
Additional Apple devices must be authorized to use the iCloud Keychain service using a combination of the Apple ID password and another method. One method involves using an iCloud Security Code; the other method is to authorize access from another Apple device that has already been configured for the iCloud Keychain service.
Bluetooth devices must be paired to each other for communication to occur. Bluetooth preferences in the System Preference application is responsible for pairing your Mac with Bluetooth peripherals. You can quickly open Bluetooth preferences from the Bluetooth status menu.
The system version, build number, and hardware serial number are located in the About This Mac dialog or the login screen. The system version number defines the specific version of OS X currently installed. The system build number is an even more specific identifier used primarily by developers. Finally, the hardware serial number is a unique number used to identify your specific Mac.
The Finder populates the Network folder using information provided by the dynamic network services discovery protocols. Computers providing services appear as resources inside the Network folder, and service discovery zones or workgroups appear as folders. Any currently connected servers also appear in the Network folder.
Sandboxed applications are only allowed access to specific items. They ' re otherwise completely cut off from the rest of the system, so they can ' t cause harm. All Mac App Store applications are required to be sandboxed.
If it appears that all configured printers are having problems, what ' s a potential quick fix?
Most common IP addresses and subnet masks share the same IPv4 formatting. An IPv4 address is a 32-bit number represented in four groups of three-digit numbers, known as octets, separated by periods. Each octet has a value between 0 and 255. An IPv6 address is a 128-bit number that ' s presented in eight groups of four-digit hexadecimal numbers separated by colons. This allows for a huge range of addresses, and as a result IPv6 addressing essentially includes subnet information.
On an optional configuration step in the Setup Assistant in OS X Mountain Lion, pressing Command-Q lets you skip the step.
Which of these must you know about a corporate VPN server before you can configure the VPN software on an OS X computer to access the corporate network?
Which folder contains instructions for the launchd process to start certain items when a user logs in to an OS X Mountain Lion computer?
A new 5 MB file was backed up by Time Machine yesterday. Today the file was edited, and has grown to 6 MB. It is about to be backed up by Time Machine again. How does Time Machine perform this backup?
Review the screenshot, and then answer the question below.
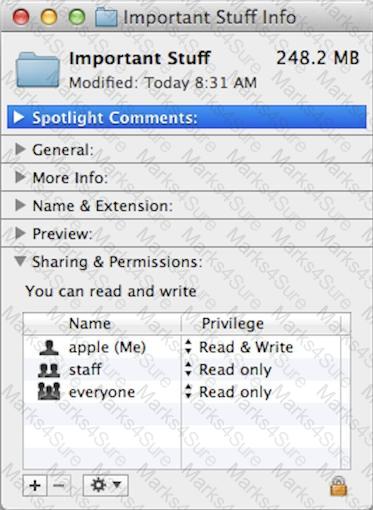
If you change the folder privilege for " everyone " to Read & Write, Finder, by default, will change the permissions of items inside the folder to match.
In OS X, which is a valid method to reset permissions and ACLs on a home folder to their default settings?
Which steps will let you retrieve a file from a Time Machine backup on an external hard disk connected to your Mac?
On a Mac running OS X Mountain Lion, how can you display a list of installed software updates?
What is the role of the launchd process in the startup of an OS X Mountain Lion computer?
Which statement is TRUE of file and folder permissions in the Finder in OS X Mountain Lion?
You upgrade a Snow Leopard Mac that has legacy FileVault encryption to Mountain Lion. If a user forgets his login password, how can you help him regain access to his encrypted home folder?
How can you display the contents of a hidden folder on a mounted volume in Finder?
In a default OS X Mountain Lion installation, which permission is assigned to the top level of each user ' s home folder to make it accessible to Guest users who log in locally?