How should you confrere the release retention policy for the investment planning depletions suite? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Which branching strategy should you recommend for the investment planning applications suite?
You are using GitHub as a source code repository.
You create a client-side Git hook on the commit-msg event. The hook requires that each commit message contain a custom work item tag.
You need to make a commit that does not have a work item tag.
Which git commit parameter should you use?
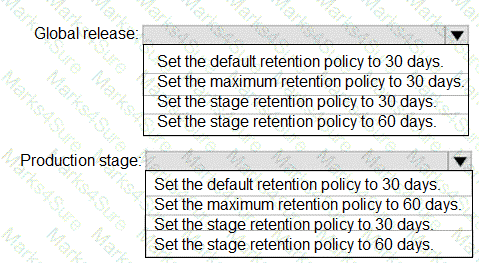
How should you configure the release retention policy for the investment planning applications suite? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
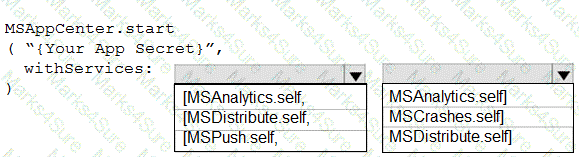
How should you complete the code to initialize App Center in the mobile application? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection a worth one point.
You have a project in Azure DevOps.
You plan to deploy a self-hosted agent by using an unattended configuration script.
Which two values should you define in the configuration script? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
To resolve the current technical issue, what should you do to the Register-AzureRmAutomationDscNode command?
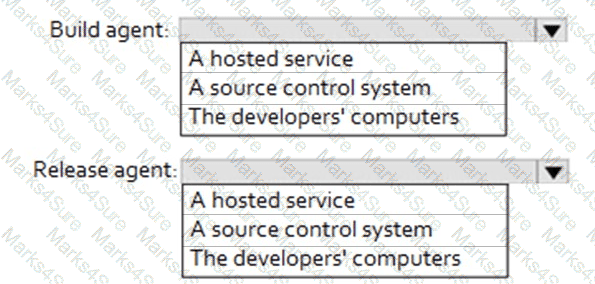
Where should the build and release agents for the investment planning application suite run? To answer, select the appropriate options in the answer area.
NOTE : Each correct selection is worth one point.
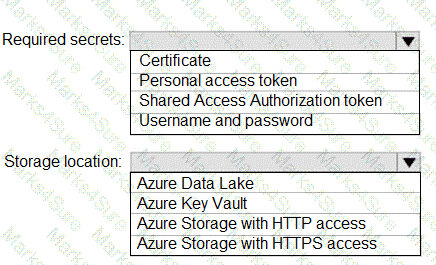
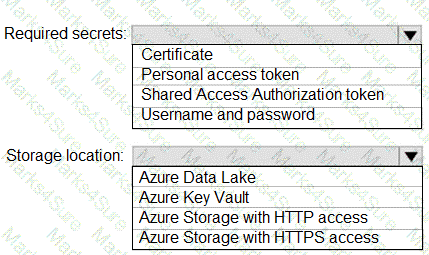
You need to configure a cloud service to store the secrets required by the mobile applications to call the share.
What should you include in the solution? To answer, select the appropriate options m the answer area, NOTE: Each correct selection is worth one point.
You have Azure Pipelines and GitHub integrated as a source code repository.
The build pipeline has continuous integration enabled.
You plan to trigger an automated build whenever code changes are committed to the repository.
You need to ensure that the system will wait until a build completes before queuing another build.
What should you implement?
You need to the merge the POC branch into the main branch. The solution must meet the technical requirements.
Which command should you run?
You need to configure Azure Pipelines to control App2 builds.
Which authentication method should you use?
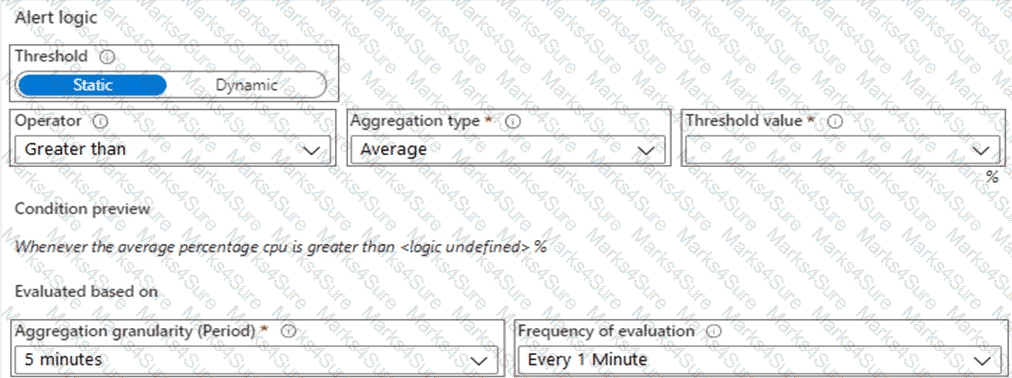
You need to configure the alert for VM1. The solution must meet the technical requirements.
Which two settings should you configure? To answer, select the appropriate settings in the answer area.
NOTE: Each correct selection is worth one point.
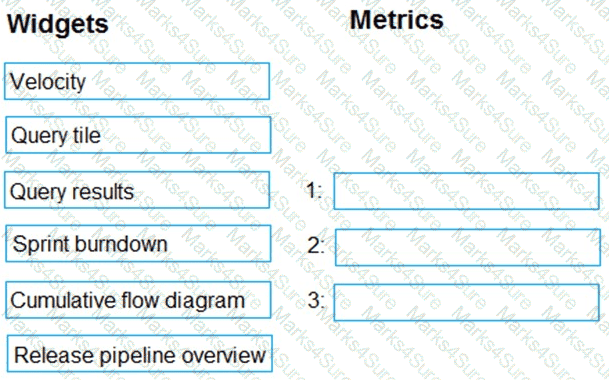
You are configuring the Azure DevOps dashboard. The solution must meet the technical requirements.
Which widget should you use for each metric? To answer, drag the appropriate widgets to the correct metrics. Each widget may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You manage package feeds by using Azure Artifacts.
You plan to create a new package feed that will include the following views:
• @ Local
• ©Latest
• @Release
• ©Prerelease
Which view should you create manually '
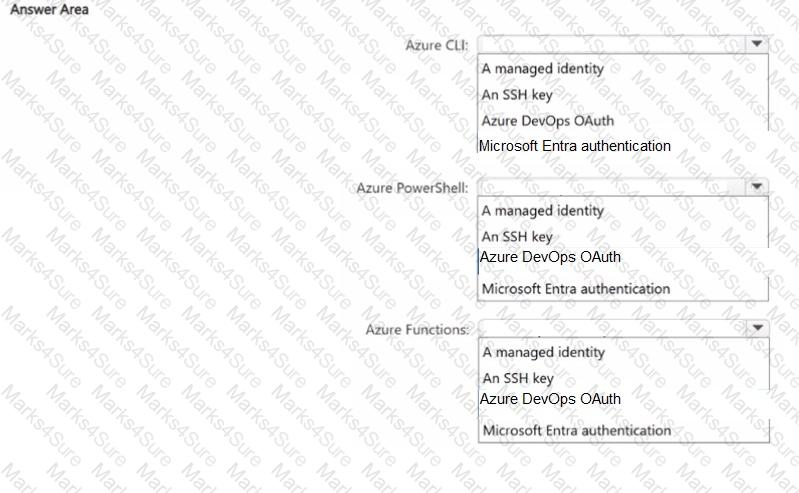
You have multiple automated workflows that interact with Azure DevOps and use the following services:
• Azure Command-Line Interface (CLI)
• Azure PowerShell
• Azure Functions
You need to recommend which authentication method to use for each service. The solution must minimize the risk of compromising credentials.
What should you recommend for each service? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Task 2
You need to log all audit events for the Azure DevOps organization in the Log Analytics! Logs Analytics workspace.
You have an Azure subscription.
You create two Bicep templates named Template1 and Template2 that will be used to create a virtual machine and a website.
You need to create a template named Template3 that will reuse logic from Template1 and Template2.
What should you define first?
You need to create and configure an Azure Storage account named az400lod11566895stor in a resource group named RG1lod11566895 to store the boot diagnostics for a virtual machine named VM1.
To complete this task, sign in to the Microsoft Azure portal.
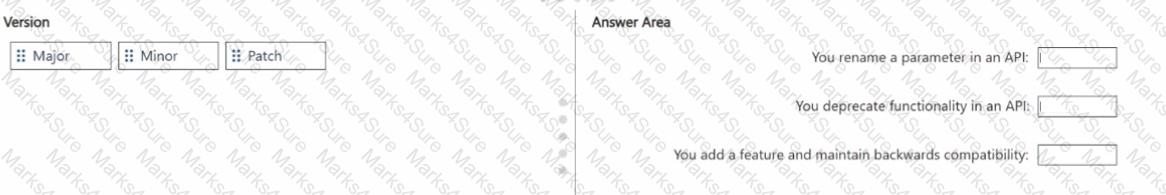
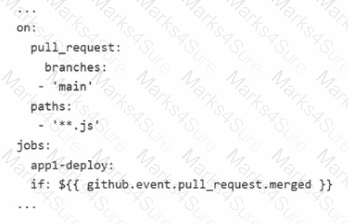
You have an Azure Pipelines pipeline named Pipeline1 that has the following YAML definition.
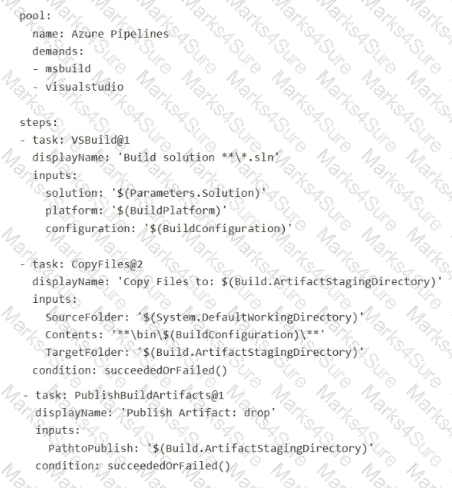
For each of the following statements, select Yes if True. Otherwise select No.
NOTE: Each correct selection is worth one point.
Task 7
You need to prepare a network security group (NSG) named az400 38443478 nsgl to host an Azure DevOps pipeline agent. The solution must allow only the required outbound port for Azure DevOps and deny all other inbound and outbound access to the Internet
You need to prepare a network security group (NSG) named az400-9940427-nsg1 to host an Azure DevOps pipeline agent. The solution must allow only the required outbound port for Azure DevOps and deny all other inbound and outbound access to the Internet.
To complete this task, sign in to the Microsoft Azure portal.
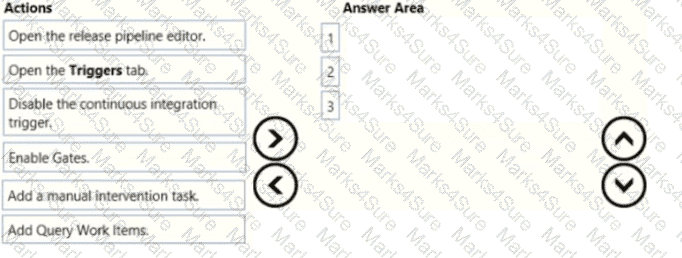
You have a widget named Appl and an Azure DevOps YAML pipeline named Pipelinel. App1 is released by using Pipelined Pipeline1 contains a single stage and a single job. You need to ensure that Appl is approved before the app is released. Which two actions should you perform? Each correct answer presents part of the solution. NOTE; Each correct selection is worth one point.
You plan to deploy a template named D:\Deploy.json to a resource group named Deploy-lod9940427.
You need to modify the template to meet the following requirements, and then to deploy the template:
The address space must be reduced to support only 256 total IP addresses.
The subnet address space must be reduced to support only 64 total IP addresses.
To complete this task, sign in to the Microsoft Azure portal.
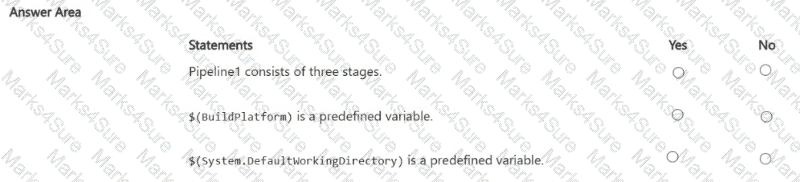
You have a GitHub Actions workflow named workflow1 that is used to deploy an app name Appl. You need to ensure that App1 is deployed only when the following conditions are met:
• A pull request is merged to the main branch.
• The change includes a JavaScript file.
Solution. You configure the YAML file of workflow1 to include the following.
Does this meet the goal?
You plan to implement a CI/CD strategy for an Azure Web App named az400-11566895-main.
You need to configure a staging environment foraz400-11566895-main.
To complete this task, sign in to the Microsoft Azure portal.
You plan to deploy a runbook that will create Azure AD user accounts.
You need to ensure that runbooks can run the AzurePowerShell cmdlets for Azure Active Directory.
To complete this task, sign in to the Microsoft Azure portal.
You have a GitHub repository named repol.
You commit a change to repol.
You need to update the commit message. The solution must ensure that the version number remains the same.
Which command should you run?
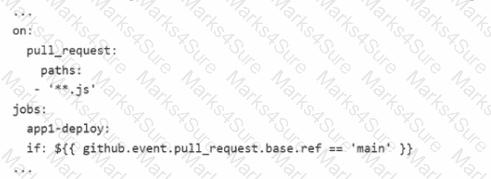
You are designing a versioning strategy for Git-based packages
You plan to use a Semantic Versioning (SemVer)-based strategy.
You need to identify when to change the build version.
What should you identify for each scenario? To answer, drag the appropriate versions to the correct scenarios. Each version may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You need to configure an Azure web app named az400-9940427-main to contain an environmental variable named “MAX_ITEMS”. The environmental variable must have a value of 50.
To complete this task, sign in to the Microsoft Azure portal.
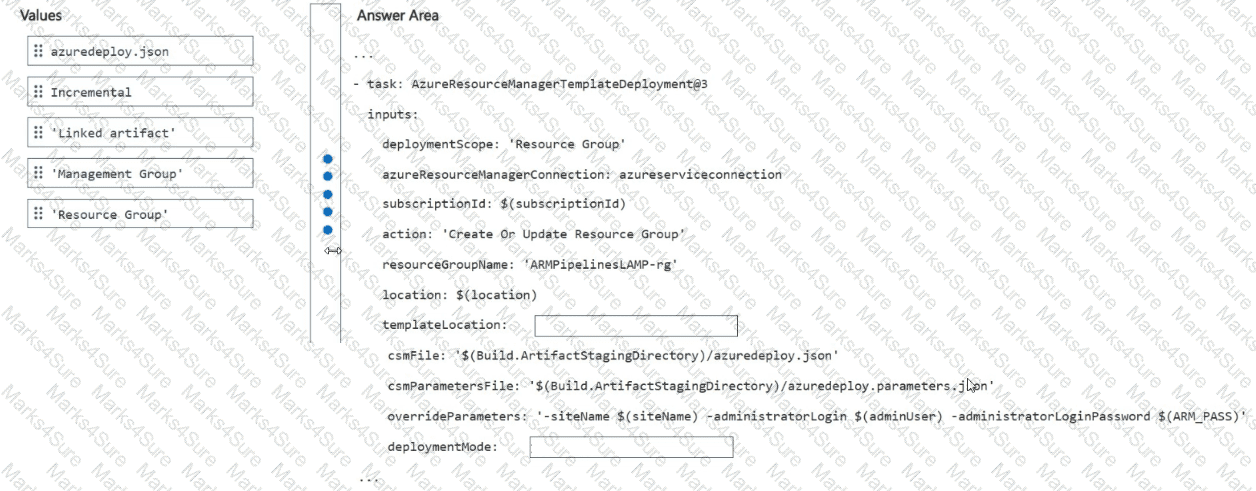
You have an Azure subscription that contains a resource group named RG1.
You have a template artifact named template1.
You plan to use Azure Pipelines to deploy an app named App1 to RG1. App1 requires template1.
You need to deploy template1 to RG1.
How should you configure the pipeline task? To answer, drag the appropriate values to the correct targets. Each value may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Task 5
For Project1, you need to create a project wiki named Wiki1 that uses the Mermaid syntax to render a diagram A sample of the desired output is stored in C:\Resources\TCPHandshake.png.
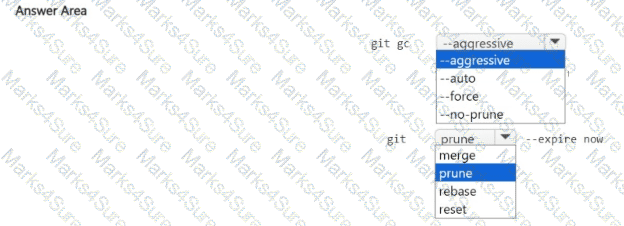
You manage the Git repository for a large enterprise application.
You need to reduce the data size of the repository.
How should you complete the commands? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
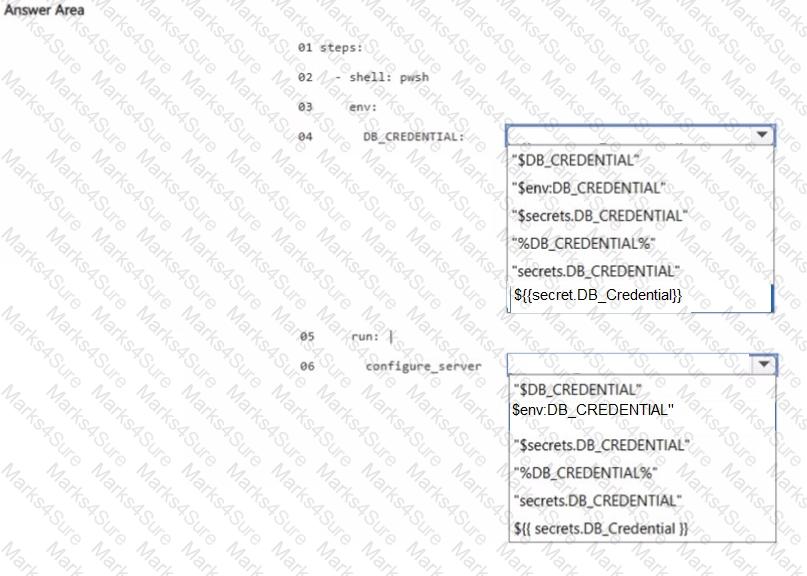
You have a GitHub organization that contains a repository and an organizational secret named DB.Credential. You need to build a workflow that will configure a server by using PowerShell and DB.Credential. How should you complete the code? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
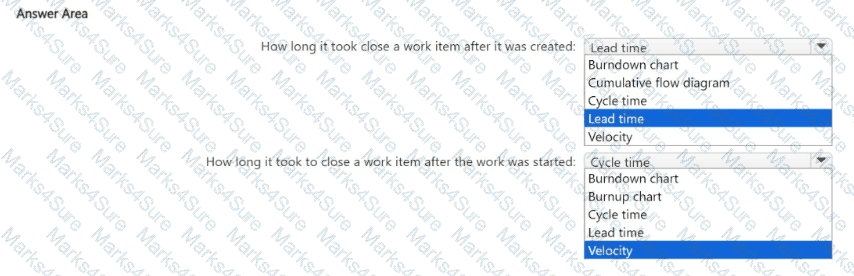
You ate using Agile process methodologies in Azure DevOps.
You need to deploy a dashboard that will provide progress reports for the following work items:
• How long it took to close a work item after it was created.
• How long it took to close a work item after the work was started.
Which type of widget should you use for each work item? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Task 6
You have an Azure function hosted in an App Service plan named az400-38443478-funct
You need to configure az400 38443478-funcl lo update the functions automatically whenever new code is committedto the main branch of https://githubcom/Azure-Samples/functions-quickstart.
NOTE: Access to GitHub is blocked in the exam environment. Access to GitHub is NOT required to complete the task successfully.
You have an Azure subscription.
The development department at your company plans to build web apps that will use multiple Azure resources. You need to recommend a development solution that meets the following requirements:
• Provides a development environment for each developer
• Supports the use of custom sandbox environments for testing
• Ensures that the environments can be embedded into CI/CD pipelines
• Minimizes administrative effort
What should you include in the recommendation?
Task 10
You need to create a variable group named varGroup1 that will contain the following variables and default values:
• username: Userl-48901628
• password: aFpJ2j+6M!
The PASSWORD variable must be secret.
You have an Azure DevOps organization.
You need to recommend a solution for managing packages. The solution must meet the following requirements:
• Host private packages.
• Publish packages to a feed.
• Support the creation and publishing of new packages.
• Ensure that the package feed can be consumed by Azure DevOps pipelines.
What should you include in the recommendation?
Task 6
Initialize the default main branch, if it does not exist already.
For Project 1, you need to implement branch merging restrictions to enable squash merge for all changes merged into the main branch.
Task 4
Initialize the default main branch, if it does not exist already.
In the Userl-42147509 Azure DevOps project, you need to implement an approval process for the default main branch.
The process must use the four-eyes principle and have at least one approval on every iteration.
You need to create a notification if the peak averageresponse time of an Azure web app named az400-9940427-main is more than five seconds when evaluated during a five-minute period. The notification must trigger the “https://contoso.com/notify” webhook.
To complete this task, sign in to the Microsoft Azureportal.
Task 7
You need to create a pipeline to deploy a Docker image. The commit must be created in a new branch named azure-pipelines.
The pipeline must be created by using the predefined Docker template.
You have a GitHub Actions workflow named workflow! that is used to deploy an app name Appl. You need to ensure that App1 is deployed only when the following conditions are met:
• A pull request is merged to the main branch.
• The change includes a JavaScript file.
Solution. You configure the YAML file of workflowl to include the following.
Does this meet the goal?
You use GitHub Enterprise to manage source code and deployments.
From GitHub Actions, you create a reusable workflow named workflow 1.
You need to ensure that the secrets defined in the calling workflow are passed to workflow1.
What should you include in the YAML file for the calling workflow?
Task 12
You need to create a personal access token (PAT) named Token! that has only the following capabilities
• Read write, andmanage code
• Read and execute builds
• Read releases
Token1 must expire in 60 days.
Task 4
For Project1, you need to create a self-hosted agent pod named Pool1.
All the pipelines in Project1 must have access to Pool1.
Task 11
You need to write a KQL query that will count the number of inbound requests for each source IP address, for any connection made during the last three months of 2021.
Open Azure Data Explorer by using the following link:
https//dataexploter azure.com/clusters/help/databases/Securiitylogs
The requests are contained in a table named InboundBrowsing in the Securitylogs connection.
The query must return two columns named NumberOfRequests and SourcelP.
Export the query result to C:\Samples
You have a project in Azure DevOps
You build an app named Appl that will be used on devices that run either MacOS, Linux, or Windows.
You need to create an Azure DevOps YAML pipeline to build App1 on the three operating systems. The solution must meet the following requirements:
• Minimize code duplication in the pipeline configuration.
• Minimize maintenance effort.
What should you use?
You have an Azure functionhosted in an App Service plan named az400-9940427-func1.
You need to configure az400-9940427-func1 to upgrade the functions automatically whenever new code is committed to the master branch of https://github.com/Azure-Samples/functions-quickstart.
To complete this task, sign in to the Microsoft Azure portal.
You need to implement Project6.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them m the correct order.
You add the virtual machines as managed nodes in Azure Automation State Configuration.
You need to configure the computer in Group7.
What should you do?
You need to implement the code flow strategy for Project2 in Azure DevOps.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange in the correct order.
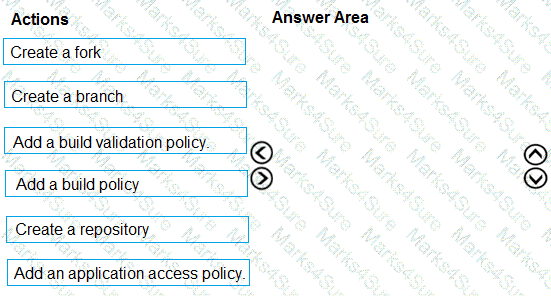
You need to implement the code flow strategy for Project2 in Azure DevOps.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
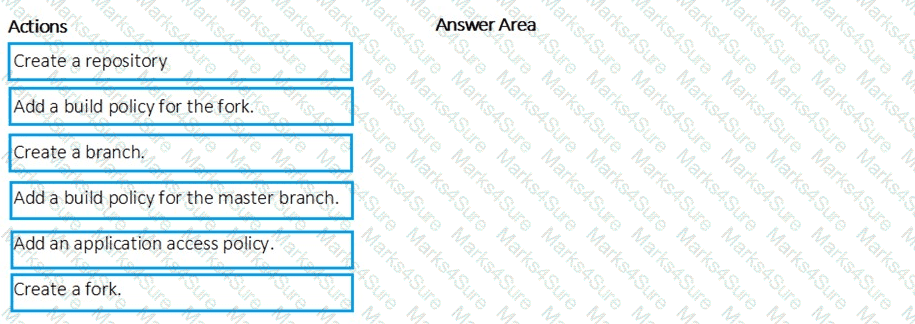
In Azure DevOps, you create Project3.
You need to meet the requirements of the project.
What should you do first?
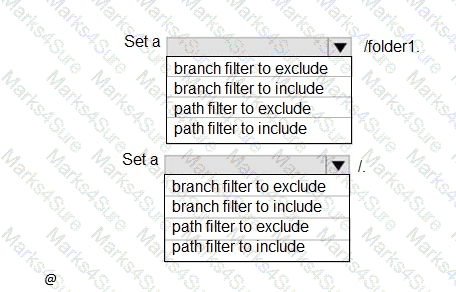
How should you configure the filters for the Project5 trigger? To answer, select the appropriate option in the answer area.
NOTE: Each correct selection is worth one point.
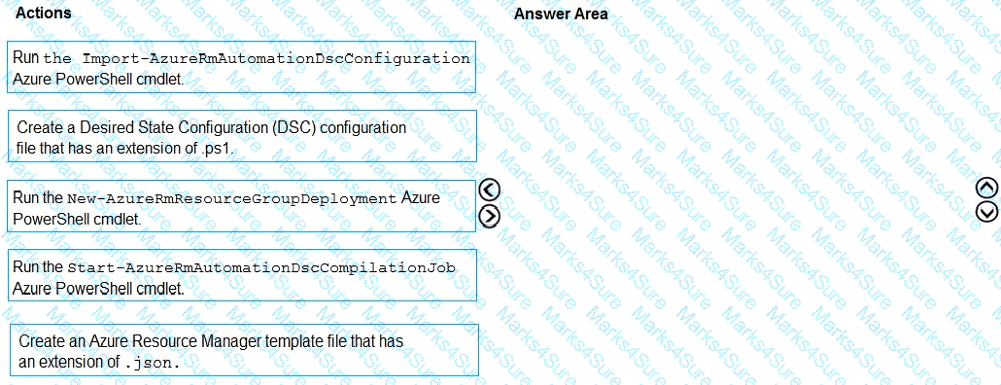
You need to configure Azure Automation for the computer in Group7.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You plan to deploy a new database environment. The solution must meet the technical requirements. You need to prepare the database for the deployment. How should you format the export?
You need !0 the merge the POC branch into the default branch. The solution must meet the technical requirements. Which command should you run?
You need to meet the technical requirements for controlling access to Azure DevOps.
What should you use?
You need to meet the technical requirements for monitoring App1.
What should you use?
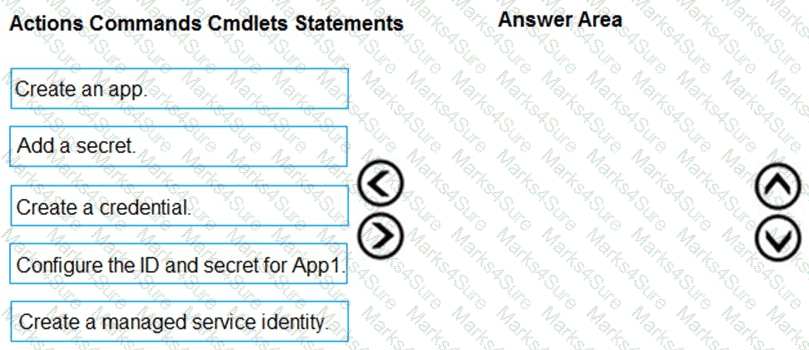
You need to configure authentication for App1. The solution must support the planned changes.
Which three actions should you perform in sequence? To answer, move all actions from the list of actions to the answer area and arrange them in the correct order.
You need to perform the GitHub code migration. The solution must support the planned changes for the DevOps environment.
What should you use?
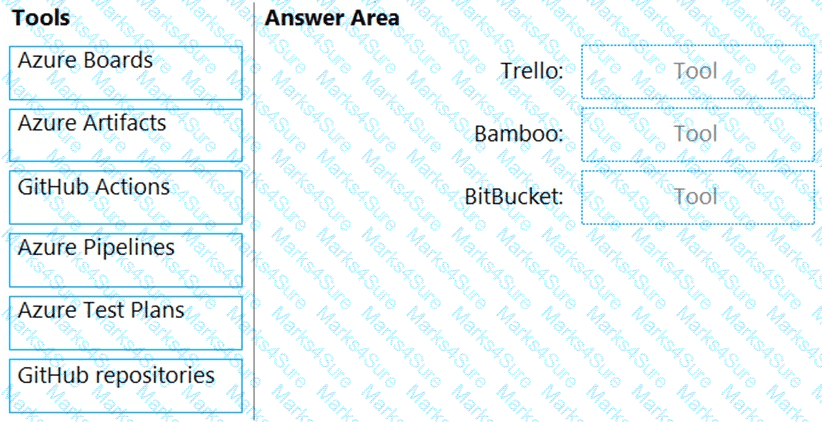
You need to replace the existing DevOps tools to support the planned changes.
What should you use? To answer, drag the appropriate tools to the correct targets. Each tool may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
What should you use to implement the code quality restriction on the release pipeline for the investment planning applications suite?
HOTSPOT
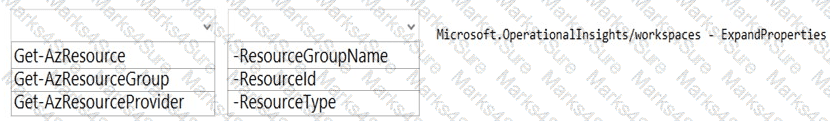
You are using PowerShell to administer Azure Log Analytics workspaces.
You need to list the available workspaces and their properties.
How should you complete the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
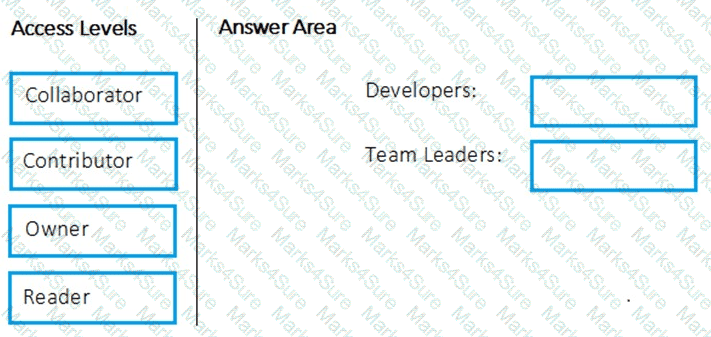
Which package feed access levels should be assigned to the Developers and Team Leaders groups for the investment planning applications suite? To answer, drag the appropriate access levels to the correct groups. Each access level may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
HOTSPOT
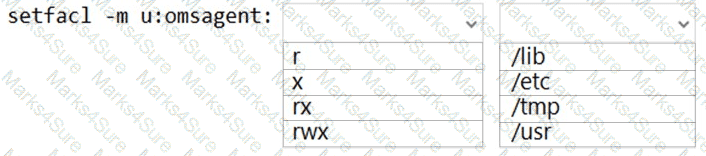
You have an Azure virtual machine named VM1 that runs Linux.
You plan to deploy the Desired State Configuration (DSC) extension to VM1.
You need to grant the Log Analytics agent the appropriate directory permissions.
How should you complete the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a project in Azure DevOps named Project1. Project1 contains a published wiki.
You need to change the order of pages in the navigation pane of the published wiki in the Azure DevOps portal.
What should you do?
You have 50 Node.js-based projects that you scan by using WhiteSource. Each project includes Package.json, Package-lock.json, and Npm-shrinkwrap.json files.
You need to minimize the number of libraries reports by WhiteSource to only the libraries that you explicitly reference.
What should you do?