During the identification phase, it is discovered that port 23 is being used maliciously. Which of the following system hardening techniques should be used to remediate the issue?
Which of the following is the reason that out-of-band communication is used during a security incident?
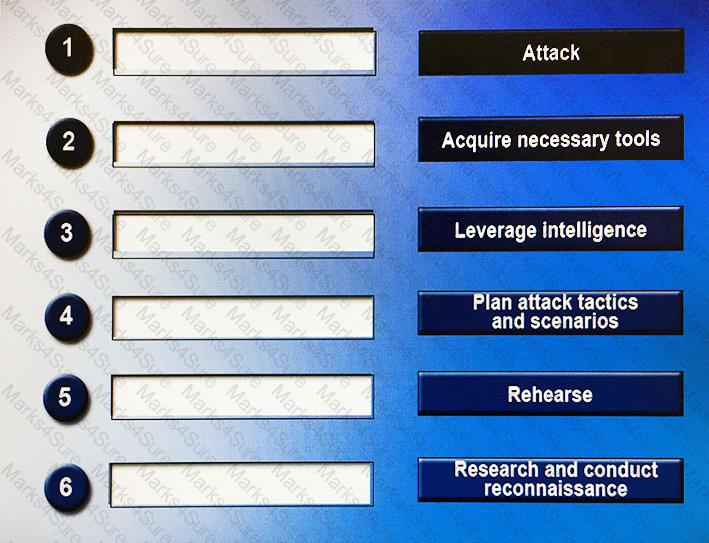
Drag and drop the following steps to perform a successful social engineering attack in the correct order, from first (1) to last (6).
A security professional has been tasked with the protection of a specific set of information essential to a corporation’s livelihood, the exposure of which could cost the company billions of dollars in long-term revenue. The professional is interested in obtaining advice for preventing the theft of this type of information. Which of the following is the BEST resource for finding this material?
While reviewing some audit logs, an analyst has identified consistent modification of the sshd_config file for an organization’s server. The analyst would like to investigate and compare contents of the current file with archived versions of files that are saved weekly. Which of the following tools will be MOST effective during the investigation?
A security analyst would like to parse through several SQL logs for indicators of compromise. The analyst is aware that none of the fields should contain a string of text longer than 30 characters; however, the analyst is unaware if there are any implemented controls to prevent such an overflow. Which of the following BEST describes the regular expression the analyst should use to find any alphanumeric character string?
A forensics analyst is analyzing an executable and thinks it may have some text of interest hidden within it. Which of the following tools can the analyst use to assist in validating the suspicion?
A hacker’s end goal is to target the Chief Financial Officer (CFO) of a bank. Which of the following describes this social engineering tactic?
An attacker has exfiltrated the SAM file from a Windows workstation. Which of the following attacks is MOST likely being perpetrated?
An attacker has decided to attempt a brute force attack on a UNIX server. In order to accomplish this, which of the following steps must be performed?
An outside organization has reported to the Chief Information Officer (CIO) of a company that it has received attack from a Linux system in the company’s DMZ. Which of the following commands should an incident responder use to review a list of currently running programs on the potentially compromised system?
A malicious attacker has compromised a database by implementing a Python-based script that will automatically establish an SSH connection daily between the hours of 2:00 am and 5:00 am. Which of the following is the MOST common motive for the attack vector that was used?
An incident responder suspects that a host behind a firewall is infected with malware. Which of the following should the responder use to find the IP address of the infected machine?
A SOC analyst reviews vendor security bulletins and security blog articles against the company’s deployed system and software base. Based on current attack patterns, three vulnerabilities, including a zero-day vulnerability, have been upgraded to high priority. Which of the following should the SOC analyst recommend? (Choose two.)
An analyst would like to search for a specific text string at the beginning of a line that begins with four capital alphabetic characters. Which of the following search operators should be used?
Organizations should exercise their Incident Response (IR) plan following initial creation. The primary objective for this first IR plan exercise is to identify:
An incident responder is investigating a Linux server reported to be “behaving strangely”. Which of the following commands should the incident responder use to identify any users currently logged into the system? (Choose two.)
Which of the following is an automated password cracking technique that uses a combination of upper and lower case letters, 0-9 numbers, and special characters?
Which of the following enables security personnel to have the BEST security incident recovery practices?
While a network administrator is monitoring the company network, an unknown local IP address is starting to release high volumes of anonymous traffic to an unknown external IP address. Which of the following would indicate to the network administrator potential compromise?
During a malware outbreak, a security analyst has been asked to capture network traffic in hourly increments for analysis by the incident response team. Which of the following tcpdump commands would generate hourly pcap files?
During an annual penetration test, several rootkit-enabled systems are found to be exfiltrating data. The penetration test team and the internal incident response team work to begin cleanup. The company’s operations team offers a new emails server to use for communications during the incident. As cleanup continues, the attackers seem to know exactly what the incident response plan is. Which of the following will prevent the attackers from compromising cleanup activities?
A malicious actor sends a crafted email to the office manager using personal information collected from social media. This type of social engineering attack is known as:
Which of the following can hackers use to gain access to a system over the network without knowing the actual password?