CPC-CDE-RECERT CyberArk CDE-CPC Recertification Questions and Answers
What is a supported certificate format for retrieving the LDAPS certificate when not using the Cyberark provided LDAPS certificate tool?
An end user (external user account) has been removed from the Users tab in CyberArk Identity Administration and tries to log in to the CyberArk Privilege Cloud portal using the correct credentials. What will happen?
When installing PSM on a Windows 2019 Server, under which circumstances should the PSMConnect and PSMAdminConnect users be moved to the domain? (Choose two.)
In addition to the Vault Admins and Auditors , what are the default map roles in the Privilege Cloud LDAP Directory mapping function for the Privilege Cloud Standard Services Model? (Choose two.)
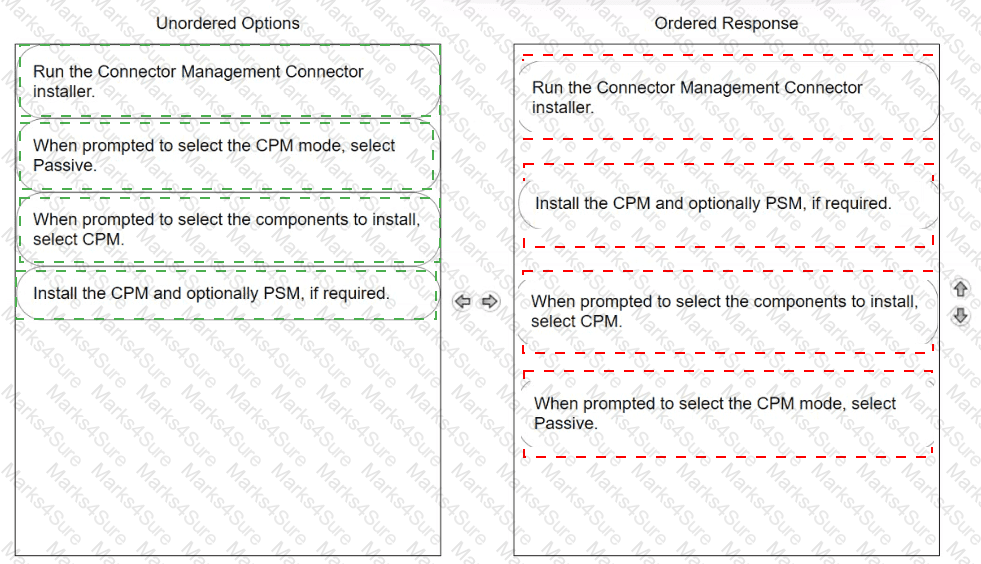
Arrange the steps to install passive CPM using Connector Management in the correct sequence
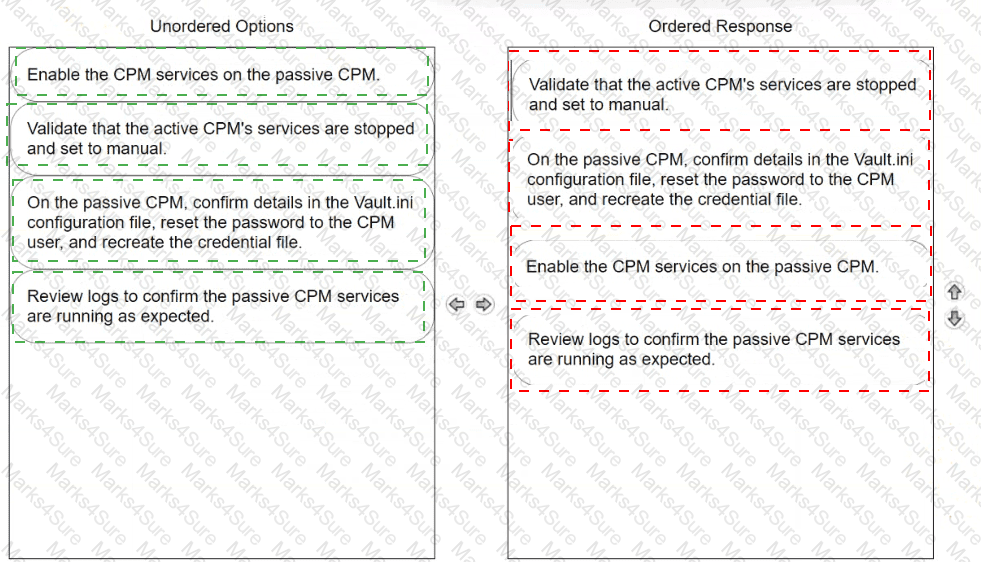
When using Connector Management, how do you configure a DR CPM in Privilege Cloud shared services? (Choose two.)
You want to add an additional maintenance user on the PSM for SSH. How can you accomplish this if InstallCyberArkSSHD is set to Integrated ?
In large-scale environments, it is important to enable the CPM to focus its search operations on specific Safes instead of scanning all Safes it sees in the Vault. How is this accomplished?
The System Health page shows the status of all components related to Privilege Cloud. Which components can administrators monitor on this page? (Choose two.)
Before installing the Privilege Cloud Connector using Connector Management , which network rules should be in place?
After a scripted installation has successfully installed the PSM, which post-installation task is performed?
Which file must you edit to ensure the PSM for SSH server is not hardened automatically after installation?
After the session has ended, where is the default final recording storage located?
Which method can be used to directly authenticate users to PSM for SSH? (Choose three.)
When creating a new Safe, if you select “Save account versions for a period of days” within Version Retention settings, what is the default number of days that password versions are saved?
Which actions must be performed when manually hardening a SUSE server with PSM for SSH ? (Choose two.)
What must be specified when authenticating to Privilege Cloud during the Secure Tunnel install?
You plan to install Privilege Cloud Connectors on your AWS and Azure environments.
What is the maximum number of concurrent RDP/SSH sessions that each connector can handle for Large Implementations?
Which statement is correct regarding the LDAP integration with CyberArk Privilege Cloud Standard?
Following the installation of the PSM for SSH server, which additional tasks should be performed? (Choose 2.)
CyberArk User Neil is trying to connect to the Target Linux server 192.168.1.164 using a domain user ACME\linuxuser01 on domain acme.corp using PSM for SSH server
192.168.65.145.
What is the correct syntax?