Which method automatically allocates a large capacity secondary cache using SSD and SCM?
In an SDS environment, which protocol supports the resource-oriented architecture for the development of scalable and lightweight web applications while adhering to a set of constraints?
Refer to the Exhibit:
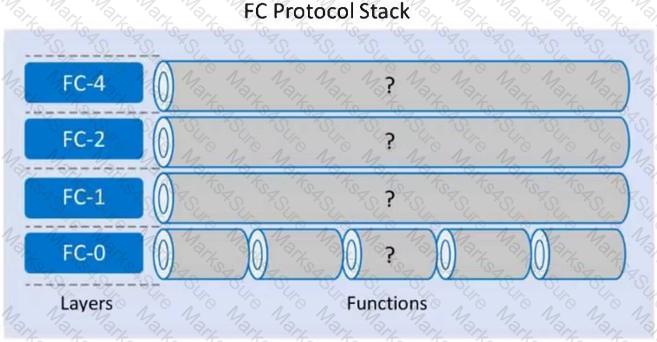
Which functions align with each layer of the FC Protocol Stack using the following order: FC-4, FC-2, FC-1, and FC-0?
Which loT architecture component provides the connection to monitor and control user devices? (First Choose Correct option and give detailed explanation delltechnologies.com)
What is a benefit of including a Defense-in-depth strategy as part of the data center security strategy?
What functionality does the control layer provide in a software-defined networking architecture?
Which file system provides a streaming interface using the MapReduce framework?
What is a key benefit for deploying a remote data protection and recovery solution in a data center environment?
What is a key function of the orchestration layer in a modern data center architecture?
Which data protection solution provides the ability to select a backup technology based on demand?
What is a benefit of using an existing Ethernet network infrastructure for storage connectivity?
Why is it important to automate the operations management process in a data center environment?
Which Connectrix FC switch model supports NVMe in a 32Gb/s SAN fabric exclusively?
If the erasure coding technique used divides data into 12 data segments and 5 coding segments, what is the maximum number of disk drive failures against which data is protected by the configuration?
An Ethernet switch has eight ports and all ports must be operational for 24 hours; from Monday through Friday. However, a failure of Port 5 occurs as follows:
Tuesday = 6 AM to 7 AM Thursday = 5 PM to 9 PM Friday = 8 AM to 9 AM
What is the MTBF of Port 5?
Which layer of the OSI reference model is responsible for logical addressing and routing?
Which data deduplication method increases the probability of identifying duplicate data even when there is only a minor difference between two documents?
An organization wants to replicate their data by extending the local network across a public network. Prior to implementing replication, they need to secure the network.
Which security control mechanism is recommended?
In a software-defined networking architecture, which layer is responsible for handling data packet forwarding or dropping?
Which network performance attribute is achieved when using flow control in FOP?
Why is it important for organizations to implement a multi-site remote replication solution?
Which Dell EMC product is a software-defined storage platform that abstracts, pools, and automates a data center’s physical storage infrastructure?
Which modern technology enables data to be securely collected and processed at point of creation to create new value?
A user lost access to a key VM due to a hardware failure. A proxy server regularly takes PIT snapshots of the VM to protect the data.
What type of data protection method is this called'?
Refer to the exhibit.
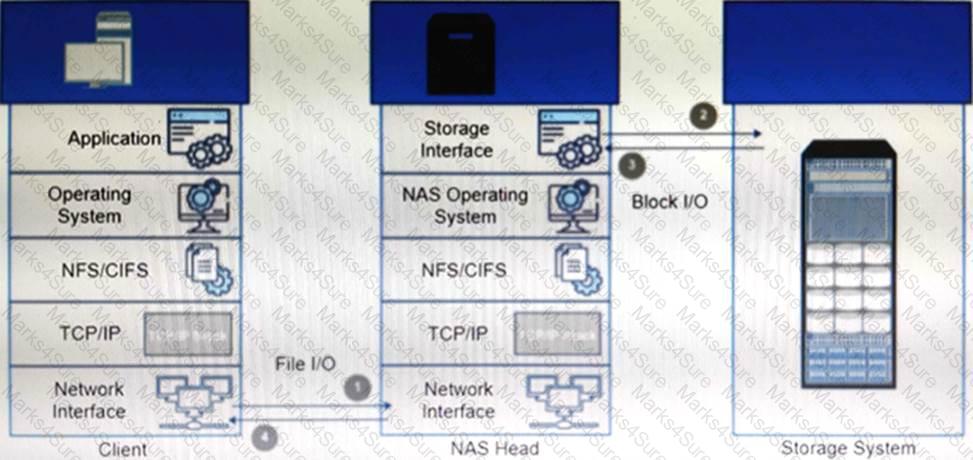
What type of NAS system(s) processes file write and read operations as described in the example?
A Fibre Channel switch has eight ports and all ports must be operational from 6 AM to 6 PM, Monday through Friday.
However, a failure of Port 4 occurs with the week as follows:
Monday= 11 AM to 1 PM
Wednesday= 5 PM to 10 PM
Thursday= 7 AM to 10 AM
Saturday= 11 AM to 1 PM
What is the availability of Port 4 in that week?
A Fibre Channel switch has eight ports and all ports must be operational from 8 AM to 8 PM, Monday through Friday. However, a failure of Port 2 occurs on a particular week as follows:
Monday = 10 AM to 12 PM Wednesday = 4 PM to 9 PM Thursday = 4 PM to 7 PM
Friday = 3 PM to 6 PM Saturday = 9 AM to 1 PM
What is the availability of Port 2 in that week?