During the analysis, the threat intelligence team disclosed a possible threat which went unnoticed when an A .R.T.I.E. employee sent their friend a slide deck containing the personal information of a colleague. The exposed information included employee first and last names, date of birth and employee ID.
What kind of attack occurred?
The cybersecurity team created a detailed security incident management procedures training program to manage any probable incidents at A .R.T.I.E.
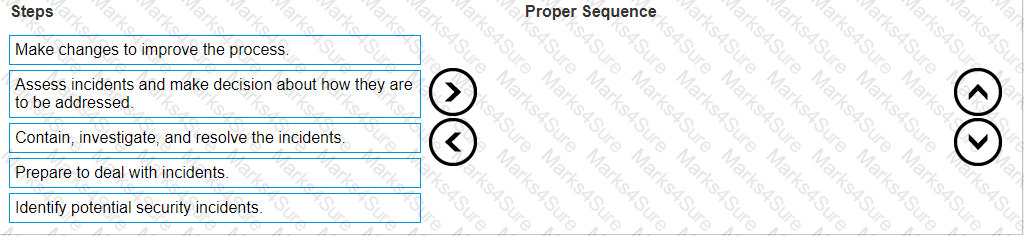
Arrange the steps in the proper sequence to best manage cybersecurity incidents.
To optimize network performance and reliability, low latency network path for customer traffic, A.R.T.I.E created a modern edge solution. The edge solution helped the organization to analyze and process diverse data and identify related business opportunities. Edge computing also helped them to create and distribute content and determine how the users consume it. But as compute and data creation becomes more decentralized and distributed, A .R.T.I.E. was exposed to various risks and security challenges inevitably became more complex. Unlike the cloud in a data center, it is physically impossible to wall off the edge.
Which type of edge security risk A .R.T.I.E. is primarily exposed?