What defines who is accountable for contacting operational teams, managers, and others affected by a
localized, safety critical event?
What is concerned with availability, reliability, and recoverability of business processes and functions?
Your organization was breached. You informed the CSIRT and they contained the breach and eradicated the threat.
What is the next step required to ensure that you have an effective CSRL and a more robust cybersecurity posture in the future?
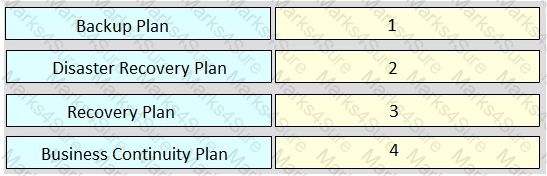
Rank order the relative severity of impact to an organization of each plan, where “1” signifies the most impact and “4” signifies the least impact.
Your firewall blocked several machines on your network from connecting to a malicious IP address. After
reviewing the logs, the CSIRT discovers all Microsoft Windows machines on the network have been affected based on a newly published CVE.
Based on the IRP, what should be done immediately?
A new employee is starting work at your company. When should they be informed of the company’s security policy?
Which NIST Cybersecurity Framework function should be executed before any others?
An incident has occurred. You restore backups onto mission/business critical assets. After restoration of the
backups your services are still inaccessible on numerous assets.
What could be the cause of the issue?
A security audit of the systems on a network must be performed to determine their compliance with security policies. Which control should be used for the audit?
What type of system processes information, the loss of which would have a debilitating impact to an
organization?
What procedure is designed to enable security personnel to detect, analyze, contain, eradicate, respond, and
recover from malicious computer incidents such as a denial-of-service attack?