According to the AAPCS, how many bytes are used to store a C variable of type ' int ' in memory?
Which of the following statements is TRUE with respect to the power consumption related to memory accesses?
A Just-In-Time compiler writes instructions to a region of memory that is configured using a writeback cache strategy. For the locations that have been written, what is the MINIMUM cache maintenance that MUST be performed before the new instructions can be reliably executed?
In an ARMv7-A processor with Security Extensions, which of the following mechanisms best describes the way Secure memory is protected from access by software running in a Non-secure privileged mode?
The following pseudocode sequence shows a flag being set to indicate that new data is ready to be read by another thread:
data = 123;
ready = true;
Assuming that the reader threads may execute on any other core of a multicore system, which of the following is the most efficient memory barrier to place between the two writes to prevent them being observed in the opposite order?
Consider the following instruction sequence:
STR r0, [r2] ; instruction A
DSB
ADD r0, r1, r2 ; instruction B
LDR r3, [r4] ; instruction C
SUB r5, r6, #3 ; instruction D
At what point will execution pause until the STR access is complete?
If the performance of an application remains unchanged when the core clock speed of a Cortex-A9 processor is reduced, what can you deduce about the system?
Consider a sequence of five independent instructions running on a pipelined processor. There are no interlocks and no data dependencies between instructions, and each instruction takes one cycle to execute. The processor has three pipeline stages and is not superscalar.
How many cycles does it take to fetch, decode and execute all five instructions in sequence, assuming that there are no pipeline stalls?
When linking with the standard C library, which library functions MUST be redefined in order to port your code to a new piece of production hardware?
In a system using the Security Extensions, how does the Secure Monitor execute a switch from Secure to Non-secure state?
In the Generic Interrupt Controller (GIC), when an interrupt is requested, but is not yet being handled, it is in which of the following states?
Assuming a 4-core Cortex-A9 SMP system which does not use the Accelerator Coherency Port (ACP). and operates the L1 caches in writeback mode, in which of the following situations is a cache clean operation required?
In a single-processor system, which of these operations requires a barrier instruction to guarantee correct operation?
Which of these instructions is a correct translation of the body of function f?
struct T { char a; int b; };
int f(struct T *p) { return p- > b; }
Which of the following statements best describes a Board Support Package (BSP)?
Which one of these statements is TRUE about code running on final hardware without a debugger attached?
In which type of storage will the compiler preferentially place frequently accessed variables?
A deeply embedded real-time industrial control system is missing some hard real-time interrupt deadlines. Which of the following performance analysis techniques is the most suitable for identifying which routines are causing the problem?
The disassembly of a program written in C shows calls to the function__aeabi_fadd. Which one of these compiler floating point options could have been used?
Which THREE of the following items should be preserved by software when entering dormant mode? (Choose three)
When developing a product using the standard ARM C library, what is the minimum effort required to re-target all platform-specific functions in the library?
A function written in C has the prototype:
void my_function(float a. double b, float c);
The function is built and linked into an application using hard floating-point linkage. What registers are used to pass arguments to the function?
Assume a Big-Endian (BE) memory system with the following memory contents.
Byte Address Contents
0x100 0x11
0x101 0x22
0x102 0x33
0x103 0x44
If R5 = 0x100, what are the contents of R4 after performing the following operation?
LDR R4, [R5]
A program running on a development board that is connected to a host using a debugger can access a file on the host by using:
On a processor supporting the Security Extensions, what sequence of operations is required to move from Non-secure User mode to Secure state?
According to the AAPCS, which of the following statements is TRUE with regard to preservation of register values by a function?
In a Cortex-A processor, assume an initial value of R1 =0x80004000.
If the following instruction causes a data abort, what value will R1 contain on entry to the abort handler?
LDR R0, [R1, #8]!
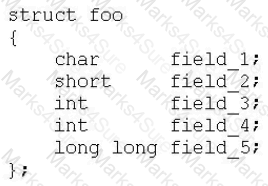
According to the EABI. what would the C size of () operator return when given the following structure?
Which of the following would enable the use of a symmetric multiprocessing (SMP) operating system?
In Architecture ARMv7-A which one of the following has a known physical address at power-on reset?
Which one of the following statements best describes the function of vector catch logic?
In an ARMv7-A processor that includes the Advanced SIMD extension (NEON), where are the data values operated on by NEON instructions stored?
A C code segment contains three calls to a function, foobar ().
This code segment is to be linked with a static library that defines foobar ().
Ignoring inlining, how many copies of foobar () will the ARM linker place in the output?
An ARM processor connected to a Generic Interrupt Controller (GIC) is handling an active interrupt 11. A new interrupt 12 that is received at the GIC is forwarded to the processor, and the active interrupt 11 is preempted. Which of the following possible values of 11 ' s priority (P1), 12 ' s priority (P2) and the processor’s priority mask (PM) permit this to happen? Assume there are 256 priority levels implemented.
When using a Generic Interrupt Controller (GIC), how does code cause a software-generated interrupt?
Which of the following pairs of statements about the difference between a Memory Management Unit (MMU) and a Memory Protection Unit (MPU) is correct?
Which of the following operations would count as intrusive to normal processor operation?
Which privileged mode can kernel code use to get direct access to the User mode registers R13 and R14?
When using the default ARM tool-chain libraries for bare-metal applications. I/O functionality is rerouted and handled by a connected debugger. This is often referred to as semihosting. Which one of the following explanations BEST describes how this feature can be implemented by a debugger?
What is the value of r0 after executing the following instruction sequence?
MOV r0, #200
MOV r5, #1
STR r3, [r0, r5, LSL#3]!
Which of the following processor resources do NOT have to be saved or modified by the Linux scheduler during context switch?
Which one of the following features must any processor support to conform to the ARMv7-A architecture?
When using the ARM Compiler (armcc), which of the following possible keywords can be used to remove padding bytes from a structure?
When using the Performance Monitoring Unit to count runtime events the counter registers are limited to 32-bits. How can more than 2A32 events be counted without significantly impacting the software performance?
Before execution:
R0=0xFFFFFFFF
R1 = ?
EOR R0, R0, R1
If R0=0x00000000 after executing the EOR instruction above, what was the value in R1 before the instruction executed?