===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Modify file content.
------------------------
Create a playbook called /home/admin/ansible/modify.yml as follows:
* The playbook runs on all inventory hosts
* The playbook replaces the contents of /etc/issue with a single line of text as
follows:
-- > On hosts in the dev host group, the line reads: “Development”
-- > On hosts in the test host group, the line reads: “Test”
-- > On hosts in the prod host group, the line reads: “Production”
Create a file called mysecret.yml on the control host using ansible vault in home/bob/ansible. Set the password to ' notasafepass ' and inside the file create a variable called dev_pass with the value of devops. Save the file. Then go back in the file and change dev_pass value to devops123. Then change the vault password of mysecret.yml to verysafepass
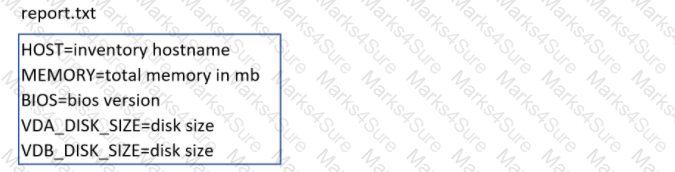
Create a file in /home/sandy/ansible/ called report.yml. Using this playbook, get a file called report.txt (make it look exactly as below). Copy this file over to all remote hosts at /root/report.txt. Then edit the lines in the file to provide the real information of the hosts. If a disk does not exist then write NONE.
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Create a playbook called hwreport.yml that produces an output file called /root/
hwreport.txt on all managed nodes with the following information:
------------------------------------------------------------------------------------------------------
-- > Inventory host name
-- > Total memory in MB
-- > BIOS version
-- > Size of disk device vda
-- > Size of disk device vdb
Each line of the output file contains a single key-value pair.
* Your playbook should:
-- > Download the file hwreport.empty from the URL http://classroom.example.com/
hwreport.empty and
save it as /root/hwreport.txt
-- > Modify with the correct values.
note: If a hardware item does not exist, the associated value should be set to NONE
----------------------------------------------------------------------------------------------
while practising you to create these file hear. But in exam have to download as per
questation.
hwreport.txt file consists.
my_sys=hostname
my_BIOS=biosversion
my_MEMORY=memory
my_vda=vdasize
my_vdb=vdbsize
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Create a playbook called balance.yml as follows:
* The playbook contains a play that runs on hosts in balancers host group and uses
the balancer role.
-- > This role configures a service to loadbalance webserver requests between hosts
in the webservers host group.curl
-- > When implemented, browsing to hosts in the balancers host group (for example
http://node5.example.com) should produce the following output:
Welcome to node3.example.com on 192.168.10.z
-- > Reloading the browser should return output from the alternate web server:
Welcome to node4.example.com on 192.168.10.a
* The playbook contains a play that runs on hosts in webservers host group and uses
the phphello role.
-- > When implemented, browsing to hosts in the webservers host group with the URL /
hello.php should produce the following output:
Hello PHP World from FQDN
-- > where FQDN is the fully qualified domain name of the host. For example,
browsing to http://node3.example.com/hello.php, should produce the following output:
Hello PHP World from node3.example.com
* Similarly, browsing to http://node4.example.com/hello.php, should produce the
following output:
Hello PHP World from node4.example.com
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Rekey an existing Ansible vault as follows:
-----------------------------------------------
* Download Ansible vault from http:// classroom.example.com /secret.yml to /home/
admin/ansible/
* The current vault password is curabete
* The new vault password is newvare
* The vault remains in an encrypted state with the new password
Create a playbook called timesvnc.yml in /home/sandy/ansible using rhel system role timesync. Set the time to use currently configured nip with the server 0.uk. pool.ntp.org . Enable burst. Do this on all hosts.
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Create an Ansible vault to store user passwords as follows:
* The name of the vault is valut.yml
* The vault contains two variables as follows:
- dev_pass with value wakennym
- mgr_pass with value rocky
* The password to encrypt and decrypt the vault is atenorth
* The password is stored in the file /home/admin/ansible/password.txt
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Create and run an Ansible ad-hoc command.
-- > As a system administrator, you will need to install software on the managed
nodes.
-- > Create a shell script called yum-pack.sh that runs an Ansible ad-hoc command to
create yum-repository on each of the managed nodes as follows:
-- > repository1
-----------
1. The name of the repository is EX407
2. The description is " Ex407 Description "
3. The base URL is http://content.example.com/rhel8.0/x86_64/dvd/BaseOS/
4. GPG signature checking is enabled
5. The GPG key URL is http://content.example.com/rhel8.0/x86_64/dvd/RPM-GPG-KEYredhat-
release
6. The repository is enabled
-- > repository2
-----------
1. The name of the repository is EXX407
2. The description is " Exx407 Description "
3. The base URL is http://content.example.com/rhel8.0/x86_64/dvd/AppStream/
4. GPG signature checking is enabled
5. The GPG key URL is http://content.example.com/rhel8.0/x86_64/dvd/ RPM-GPG-KEYredhat-
release
6. The repository is enabled