Rick works as a Computer Forensic Investigator for BlueWells Inc. He has been informed that some confidential information is being leaked out by an employee of the company. Rick suspects that someone is sending the information through email. He checks the emails sent by some employees to other networks. Rick finds out that Sam, an employee of the Sales department, is continuously sending text files that contain special symbols, graphics, and signs. Rick suspects that Sam is using the Steganography technique to send data in a disguised form. Which of the following techniques is Sam using?
Each correct answer represents a part of the solution. Choose all that apply.
You work as an Information Security Manager for uCertify Inc. You need to make the documentation on change management. What are the advantages of change management?
Each correct answer represents a complete solution. Choose all that apply.
You work as an Information Security Officer for uCertify Inc. You need to create an asset management plan differentiating fixed assets from inventory items. How will you differentiate assets from inventory items?
Which of the following persons is responsible for testing and verifying whether the security policy is properly implemented, and the derived security solutions are adequate or not?
Which of the following statements are true about security risks?
Each correct answer represents a complete solution. Choose three.
Qualitative risk analysis includes judgment, intuition, and experience. Which of the following methods are used to perform qualitative risk analysis?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is a formal state transition model of computer security policy that is used to describe a set of access control rules which use security labels on objects and clearances for subjects?
You work as a Network Administrator for Net Perfect Inc. The company has a TCP/IP-based Windows NT network. You are configuring a computer that will be used as a file server on the network. You have to decide the disk configuration for the computer to obtain better performance.
A fault tolerant disk configuration is not a requirement. Which of the following RAID levels will you choose to fulfil the requirement?
Single Loss Expectancy (SLE) represents an organization ' s loss from a single threat. Which of the following formulas best describes the Single Loss Expectancy (SLE)?
Which of the following international information security standards is concerned with anticipating and responding to information security breaches?
Which of the following is an authentication scheme used by Point to Point Protocol (PPP) servers to validate the identity of remote clients?
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You need to differentiate various assets of your organization. Which of the following are information assets?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following plans provides measures and capabilities for recovering a major application or general support system?
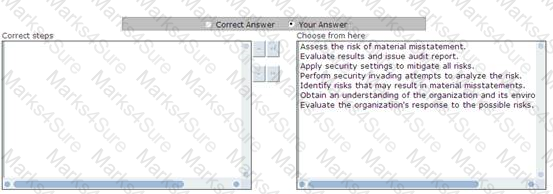
Choose and reorder the appropriate steps that you will take to perform auditing.
Which of the following is an anomaly where a program, while writing data to a buffer, overruns the buffer ' s boundary and overwrites adjacent memory?
Which of the following are computer clusters that are implemented primarily for the purpose of providing high availability of services which the cluster provides?
Victor wants to send an encrypted message to his friend. He is using a steganography technique to accomplish his task. He takes a cover object and changes it accordingly to hide information.
This secret information is recovered only when the algorithm compares the changed cover with the original cover. Which of the following steganography methods is Victor using to accomplish his task?
Which of the following is a fast-emerging global sector that advises individuals and corporations on how to apply the highest ethical standards to every aspect of their business?
You work as a Network Security Administrator for uCertify Inc. You feel that someone has accessed your computer and used your e-mail account. To check whether there is any virus installed into your computer, you scan your computer but do not find any illegal software. Which of the following types of security attacks generally runs behind the scenes on your computer?
You work as a Security Administrator for uCertify Inc. You are concerned about the password security. Therefore, you have decided to apply a policy that will be helpful for others to create strong passwords. Which of the following are the important things that should be remembered to create a strong password?
Each correct answer represents a complete solution. Choose all that apply.
You work as the Network Security Administrator for uCertify Inc. You are responsible for protecting your network from unauthorized access from both inside and outside the organization. For outside attacks, you have installed a number of security tools that protect your network. For internal security, employees are using passwords more than 8 characters; however, a few of them having the same designation often exchange their passwords, making it possible for others to access their accounts. There is already a policy to stop this practice, but still employees are doing so. Now, you want to stop this and ensure that this never happens again. Which of the following will be the best step to stop this practice?
You work as a Network Security Administrator for uCertify Inc. Your organization has set up a new Internet connection in place of the previous one. It is your responsibility to ensure that employees use the Internet only for official purposes. While reviewing Internet usages, you find that a few people have traversed and downloaded some inappropriate and illegal information. You want to make a policy to stop all these activities in the future. Which of the following policies will you implement to accomplish the task?
Which formula will you use to calculate the estimated average cost of 1 hour of downtime?
Which of the following is the method of hiding data within another media type such as graphic or document?
Which of the following indicates that the project team has decided not to change the project management plan to deal with a risk?
You work as a Security Administrator for uCertify Inc. You have been assigned the task to apply a data availability solution based on a striped disk array without redundancy. Which of the following will you use to accomplish the task?
Which of the following policies is a set of rules applied by the owner/manager of a network, Website or large computer system that restrict the ways in which the network site or system may be used?
You work as a Security Professional for uCertify Inc. You have been assigned the task to calculate the Recovery Time Objective for particular outage duration. Which of the following should be included in the Recovery Time Objective?
Each correct answer represents a complete solution. Choose all that apply.
David works as the Chief Information Security Officer for uCertify Inc. Which of the following are the responsibilities that should be handled by David?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are the primary rules defined for RBAC?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are the various domains in the ISO/IEC 27002?
Each correct answer represents a complete solution. Choose all that apply.
A helpdesk technician received a phone call from an administrator at a remote branch office. The administrator claimed to have forgotten the password for the root account on UNIX servers and asked for it. Although the technician didn ' t know any administrator at the branch office, the guy sounded really friendly and since he knew the root password himself, he supplied the caller with the password.
What type of attack has just occurred?
You work as a Security Administrator for uCertify Inc. You observe that an employee is spreading personal data of your organization. Which of the following standards of information security deals with the employees handling personal data in an organization?
What is the name given to the system that guarantees the coherence of information security in the organization?
Which of the following are features of protocol and spectrum analyzers?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are responsibilities of the Service Level Manager?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following activities are performed by the ' Do ' cycle component of PDCA (plan-docheck- act)?
Each correct answer represents a complete solution. Choose all that apply.
David works as the Manager for Tech Mart Inc. An incident had occurred ten months ago due to which the company suffered too much losses. David has been assigned the task to submit a report on the losses incurred by the company in a year. Which of the following should David calculate in order to
submit the report containing annualized loss expectancy?
Each correct answer represents a complete solution. Choose all that apply.
A Web-based credit card company had collected financial and personal details of Mark before issuing him a credit card. The company has now provided Mark ' s financial and personal details to another company. Which of the following Internet laws has the credit card issuing company violated?
Sam is the CEO of Gentech Inc. The company is located in New York. He has to start a new project in order to increase the overall revenue of the company. Sam has to develop an ISMS policy. In which of the following phases of the PDCA cycle will Sam accomplish the task?
You work as a System Administrator for uCertify Inc. You have been given the task to create a new corporate policy. Which of the following approaches must be followed to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Rick works as a Computer Forensic Investigator for BlueWells Inc. He has been informed that some confidential information is being leaked out by an employee of the company. Rick suspects that someone is sending the information through email. He checks the emails sent by some employees to other networks. Rick finds out that Sam, an employee of the Sales department, is continuously sending text files that contain special symbols, graphics, and signs. Rick suspects that Sam is using the Steganography technique to send data in a disguised form. Which of the following techniques is Sam using?
Each correct answer represents a part of the solution. Choose all that apply.
You work as a Security Administrator for uCertify Inc. You have been assigned a task for helping employees in determining appropriate technical security measures available for electronic information that is deemed sensitive. Which of the following policies will you apply to accomplish the task?
Which of the following paragraphs of the Turnbull Report stated that a company ' s system of internal control will include information and communication processes?
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You need to make a document on the classification of information assets. Which of the following controls of the ISO standard provides guidelines on the classification of information?
As an attacker, you are sending very small sized packets with durations of 15 minutes per packet to the IIS Web server. Since an IIS session remains alive for a long time, the IDS may be tricked into accepting them as regular packet transformations. Which of the following types of attacking methods are you using?
In which of the following social engineering attacks does an attacker first damage any part of the target ' s equipment and then advertise himself as an authorized person who can help fix the problem.
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You need to differentiate various assets of your organization. Which of the following is an intangible asset?
You work as an Information Security Manager for uCertify Inc. You are working on a software asset management plan to provide backup for Active Directory. Which of the following data is required to be backed up for this purpose?
Which of the following needs to be documented to preserve evidences for presentation in court?
Which of the following are the elements of Information Security Management System framework?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following standards was concerned with corporate governance and directors ' remuneration and issued in 1998?
You work as a Security Administrator for uCertify Inc. You have been assigned the task to provide a solution based on high reliability combined with high performance. Which of the following will you use to accomplish the task?
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You need to differentiate various assets of your organization. Which of the following is an intangible asset?
David has identified a technical risk in his project and has been assigned a contingency for that. Which part of the risk response strategy does planning contingency reserves come under?
Which of the following identifies a company ' s exposure to threats and provides effective prevention and recovery for the company?
Peter works as a Security Administrator for SecureEnet Inc. He observes that the database server of the company has been compromised and the data is stolen. Peter immediately wants to report this crime to the law enforcement authorities. Which of the following organizations looks after computer crime investigations in the United States?
You work as an Information Security Officer. You are working on an asset management plan. You need to assign ownership of some assets to an employee. You are making a documentation to explain the responsibilities of an owner of the business asset. Which of the following areas should you include in your documentation?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are elements of an information security policy document?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are social engineering techniques?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following plans provides measures for disseminating status report to personnel and the public?
Which of the following is used for improving the security of Microsoft Windows by limiting application software to standard user privileges until an administrator authorizes an increase or elevation?
Which of the following best describes the identification, analysis, and ranking of risks?
Sam works as a Project Manager for Blue Well Inc. He is working on a new project. He wants to access high level risks for the project. Which of the following steps should Sam take in order to accomplish the task?
You work as a Security Administrator for uCertify Inc. You have made a plan to increase the security of the organization and you want to show this to the CEO of the organization. But, you do not want to share this information with others. Therefore, you want to classify this information.
Which of the following will be the suitable classification to accomplish the task?
Which of the following Acts, enacted in the United States, amends Civil Rights Act of 1964, providing technical changes affecting the length of time allowed to challenge unlawful seniority provisions, to sue the federal government for discrimination and to bring age discrimination claims?
Which of the following security design principles supports comprehensive and simple design and implementation of protection mechanisms, so that an unintended access path does not exist or can be readily identified and eliminated?
Which of the following is a structured approach to transitioning individuals, teams, and organizations from a current state to a desired future state?
Which of the following formulas is used to represent the annualized loss expectancy (ALE)?
Mark works as a Webmaster for Infonet Inc. He sets up an e-commerce site. He wants to accept online payments through credit cards on this site. He wants the credit card numbers to be encrypted. What will Mark do to accomplish the task?
Fill in the blank with the appropriate term.
______is the process of managing user authorizations based on the ITU-T Recommendation X.509.
You work as a Network Security Administrator for uCertify Inc. You feel that someone has accessed your computer and used your e-mail account. To check whether there is any virus installed into your computer, you scan your computer but do not find any illegal software. Which of the following types of security attacks generally runs behind the scenes on your computer?
Which of the following is the basic requirement to install WinDump on a Windows computer system?
David works as the Manager for Tech Mart Inc. An incident had occurred ten months ago due to which the company suffered too much losses. David has been assigned the task to submit a report on the losses incurred by the company in a year. Which of the following should David calculate in order to submit the report containing annualized loss expectancy?
Each correct answer represents a complete solution. Choose all that apply.
What are the basic steps involved in Continuity Management?
1. Prioritizing the businesses to be recovered by conducting a Business Impact Analysis (BIA).
2. Performing a Risk Assessment (aka Risk Analysis) for each of the IT Services to identify the assets, threats, vulnerabilities, and countermeasures for each service.
3. Evaluating the options for recovery.
4. Producing the Contingency Plan.
5. Testing, reviewing, and revising the plan on a regular basis.
Each correct answer represents a complete solution. Choose two.
How can you calculate the Annualized Loss Expectancy (ALE) that may occur due to a threat?
You work as an Information Security Manager for uCertify Inc. You need to create the documentation on information security management system (ISMS). Which of the following elements are included in ISMS?
Each correct answer represents a complete solution. Choose all that apply.
You work as an Information Security Manager for uCertify Inc. You have been assigned the task to list down all procedures included in control A.7.2.2 of the ISO standard. Which of the following procedures are included in control A.7.2.2?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following concepts or terms states that changes related to one requirement, i.e., scope, time, or cost, will at least influence one other element?
Which of the following are the purposes of security awareness, training, and education?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following types of software is used by organizations to arrange for different passwords on different systems to have the same value when they belong to the same person?
Which of the following is an anomaly where a program, while writing data to a buffer, overruns the buffer ' s boundary and overwrites adjacent memory?
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You are making the documentation on control A.7.2. Which of the following are the main objectives of control A.7.2?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are security design principles required for information protection?
Each correct answer represents a complete solution. Choose all that apply.
Single Loss Expectancy (SLE) represents an organization ' s loss from a single threat. Which of the following formulas best describes the Single Loss Expectancy (SLE)?
Peter works as a Security Administrator for SecureEnet Inc. He observes that the database server of the company has been compromised and the data is stolen. Peter immediately wants to report this crime to the law enforcement authorities. Which of the following organizations looks after computer crime investigations in the United States?
Rick works as a Computer Forensic Investigator for BlueWells Inc. He has been informed that some confidential information is being leaked out by an employee of the company. Rick suspects that someone is sending the information through email. He checks the emails sent by some employees to other networks. Rick finds out that Sam, an employee of the Sales department, is continuously sending text files that contain special symbols, graphics, and signs. Rick suspects that Sam is using the Steganography technique to send data in a disguised form. Which of the following techniques is Sam using?
Each correct answer represents a part of the solution. Choose all that apply.
You work as a Security Administrator for uCertify Inc. You observe that an employee is spreading personal data of your organization. Human resource security deals with the employees handling personal data in an organization. Which section of ISO 27002 describes human resource security?
Which of the following procedures is to reduce the risk to personnel, property, and other assets while minimizing work disorders in the event of an emergency?
You work as a Security Administrator for uCertify Inc. You have been assigned the task to verify the identity of the employees recruited in your organization. Which of the following components of security deals with an employee ' s verification in the organization?
An Active Attack is a type of steganography attack in which the attacker changes the carrier during the communication process. Which of the following techniques is used for smoothing the transition and controlling contrast on the hard edges, where there is significant color transition?
You work as an Information Security Manager for uCertify Inc. You need to create the documentation on information security management system (ISMS). Which of the following is the governing principle behind ISMS?
Sam uses Monte Carlo simulation to quantitatively assess cost and schedule risks of his project during planning processes. During risk monitoring and control, Sam repeats the technique, but it leads to different results. Which of the following cannot be the reason for the difference in results?
You work as an Information Security Manager for uCertify Inc. You are working on the documentation of ISMS. Which of the following steps are concerned with the development of ISMS?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following states that a user should never be given more privileges than are required to carry out a task?
Which of the following terms refers to the time duration during which a system or service is unavailable?
In which of the following mechanisms does an authority, within limitations, specify what objects can be accessed by a subject?
You work as a Security Administrator for uCertify Inc. You need to install a honeypot inside network firewalls to monitor and track hackers. What should you install on the system before deploying the honeypot?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is used to align and realign IT Services to changing business needs by identifying and implementing improvements to IT services?
The usage of pre-numbered forms for initiating a transaction is an example of which of the following types of control?
You are consulting with a small budget conscious accounting firm. Each accountant keeps individual records on their PC and checks them in and out of a server. They are concerned about losing data should the server hard drive crash. Which of the following RAID levels would you recommend?
Which of the following are computer clusters that are implemented primarily for the purpose of providing high availability of services which the cluster provides?
Which of the following is a legal system that gives great precedential weight to common law, on the principle that it is unfair to treat similar facts differently on different occasions?
You work as a Security Administrator for uCertify Inc. You observe that an employee is spreading personal data of your organization. Which of the following standards of information security deals with the employees handling personal data in an organization?
The usage of pre-numbered forms for initiating a transaction is an example of which of the following types of control?
Which of the following is used to shift the impact of a threat to a third party, together with the ownership of the response?
Which of the following sections come under the ISO/IEC 27002 standard?
Each correct answer represents a complete solution. Choose all that apply.
Fill in the blank with an appropriate phrase.
_________accord describes the minimum regulatory capital to be allocated by each bank based on its risk profile of assets.
In which of the following does CRAMM provide assistance?
Each correct answer represents a complete solution. Choose all that apply.
You work as an Information Security Manager for uCertify Inc. You are working on a project related to communications and operations management. Which of the following controls of the ISO standard is concerned with operational procedures and responsibilities?
The Information Security Officer (ISO) of Blue Well Inc. wants to have a list of security measures put together. What should be done before security measures are selected by the Information Security Officer?
Which of the following are the sub-elements of environmental security?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is the process of removing sensitive information from a document or any other medium, so that it may be distributed to a broader audience?
You work as the Network Security Administrator for uCertify Inc. You are responsible for protecting your network from unauthorized access from both inside and outside the organization. For outside attacks, you have installed a number of security tools that protect your network. For internal security, employees are using passwords more than 8 characters; however, a few of them having the same designation often exchange their passwords, making it possible for others to access their accounts.
There is already a policy to stop this practice, but still employees are doing so. Now, you want to stop this and ensure that this never happens again. Which of the following will be the best step to stop this practice?
John works as an IT Technician for uCertify Inc. One morning, John receives an e-mail from the company ' s Manager asking him to provide his logon ID and password, but the company policy restricts users from disclosing their logon IDs and passwords. Which type of possible attack is this?
Which of the following is a Restrict Anonymous registry value that allows users with explicit anonymous permissions?
You work as the Human Resource Manager for uCertify Inc. You need to recruit some candidates for the marketing department of the organization. Which of the following should be defined to the new employees of the organization before they have joined?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are the perspectives considered to ensure the confidentiality, integrity, and availability of an organization ' s assets, information, data, and IT services?
Each correct answer represents a complete solution. Choose all that apply.