Physical Analyzer provides a function to narrow down a search based on a timestamp, a type, a party or date.
What is the name of this advanced searching capability?
What is often more of a challenge with mobile forensics than other areas of forensics?
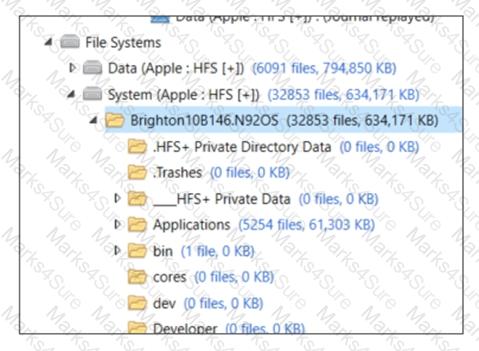
While conducting forensic analysis of an associated media card, one would most often expect to find this particular file system format?
When conducting forensic analysis of an associated media card, one would most often expect to find this
particular file system format?
Property list (Plist) files are used by iOS devices to store datA. Which of the file formats below is common to
plist files?
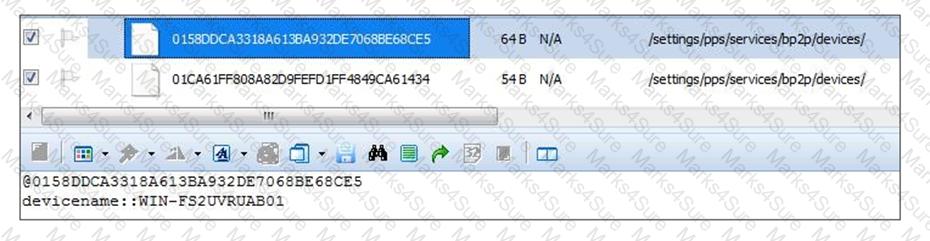
What information can you determine by reviewing the (bp2p) file from a BlackBerry OS10 handset?
Which of the following is one potential risk of using the ALWAYS OFF rule for handling cell phones?
Which artifact(s) can be extracted from a logical image only if the device the image was acquired from was jailbroken?
An Android device user is known to use Facebook to communicate with other parties under examination.
There is no evidence of the Facebook application on the phone. If there was Facebook usage where would an examiner expect to find these artifacts?
Which artifact must be carved out manually when examining a file system acquisition of an Android device?
Which of the following files contains details regarding the encryption state of an iTunes backup file?
Which file, found natively on most Android devices, will contain location history such as coordinates, physical addresses and timestamps?
What does the data string highlighted in blue represent in the File system path?
While analysis in BlackBerry application list it appears that no third-party applications were installed on the device. Which other file may provide you with additional information on applications that were accessed with the handset?
Which of the following files provides the most accurate reflection of the device’s date/timestamp related to the
last device wipe?
Cellebrite Physical Analyzer uses Bit Defender to scan for malware by flagging files who have known bad hash values. This is an example of which type of mobile malware detection?