Which type of attack could be used to obtain IOS router configuration files without a valid user password?
Before re-assigning a computer to a new employee, what data security technique does the IT department use to make sure no data is left behind by the previous user?
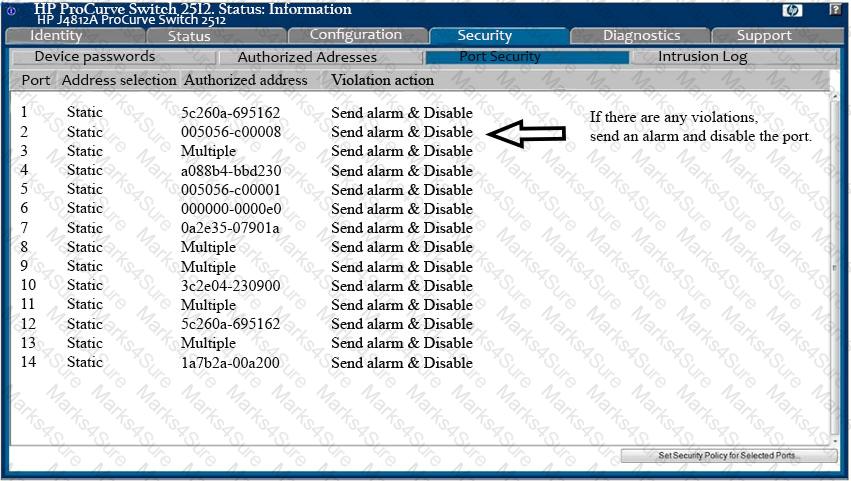
Analyze the screenshot below. Which of the following attacks can be mitigated by these configuration settings?
A company classifies data using document footers, labeling each file with security labels “Public”, “Pattern”, or “Company Proprietary”. A new policy forbids sending “Company Proprietary” files via email. Which control could help security analysis identify breaches of this policy?
The security team wants to detect connections that can compromise credentials by sending them in plaintext across the wire. Which of the following rules should they enable on their IDS sensor?
Which of the following is an outcome of the initial triage during incident response?
An analyst will capture traffic from an air-gapped network that does not use DNS. The analyst is looking for unencrypted Syslog data being transmitted. Which of the following is most efficient for this purpose?
An incident response team is handling a worm infection among their user workstations. They created an IPS signature to detect and block worm activity on the border IPS, then removed the worm’s artifacts or workstations triggering the rule. Despite this action, worm activity continued for days after. Where did the incident response team fail?
Requiring background checks for employees who access protected data is an example of which type of data loss control?
What should happen before acquiring a bit-for-bit copy of suspect media during incident response?
Requiring criminal and financial background checks for new employees is an example of what type of security control?
Michael, a software engineer, added a module to a banking customer’s code. The new module deposits small amounts of money into his personal bank account. Michael has access to edit the code, but only code reviewers have the ability to commit modules to production. The code reviewers have a backlog of work, and are often willing to trust the software developers’ testing and confidence in the code.
Which technique is Michael most likely to engage to implement the malicious code?
What does the following WMIC command accomplish?
process where name=’malicious.exe’ delete
Which Windows tool would use the following command to view a process:
process where name=’suspect_malware.exe’list statistics
Throughout the week following a new IPS deployment, nearly every user on the protected subnet submits helpdesk tickets regarding network performance and not being able to access several critical resources. What is the most likely reason for the performance issues?
Who is ultimately responsible for approving methods and controls that will reduce any potential risk to an organization?
Network administrators are often hesitant to patch the operating systems on CISCO router and switch operating systems, due to the possibility of causing network instability, mainly because of which of the following?
Why might an administrator not be able to delete a file using the Windows del command without specifying additional command line switches?