Which of the following tables is formed by NTFS file system to keep the track of files, to store metadata, and their location?
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.weare-secure.com. He enters a single quote in the input field of the login page of the We-are-secure Web site and receives the following error message:
Microsoft OLE DB Provider for ODBC Drivers error ' 0x80040E14 '
This error message shows that the We-are-secure Website is vulnerable to __________.
Which of the following directories contains administrative commands on a UNIX computer?
Which of the following Acts enacted in United States amends Civil Rights Act of 1964, providing technical changes affecting the length of time allowed to challenge unlawful seniority provisions, to sue the federal government for discrimination and to bring age discrimination claims?
Based on the case study, to implement more security, which of the following additional technologies should you implement for laptop computers?
(Click the Exhibit button on the toolbar to see the case study.)
Each correct answer represents a complete solution. Choose two.
Joseph works as a Software Developer for WebTech Inc. He wants to protect the algorithms and the techniques of programming that he uses in developing an application. Which of the following laws are used to protect a part of software?
Victor is a novice Ethical Hacker. He is learning the hacking process, i.e., the steps taken by malicious hackers to perform hacking. Which of the following steps is NOT included in the hacking process?
Which of the following statements about the NTDETECT.COM file is true?
Each correct answer represents a complete solution. Choose three.
Which of the following switches is used with Pslist command on the command line to show the statistics for all active threads on the system, grouping these threads with their owning process?
Peter, an expert computer user, attached a new sound card to his computer. He then restarts the computer, so that the BIOS can scan the hardware changes. What will be the memory range of ROM that the BIOS scan for additional code to be executed for proper working of soundcard?
Which of the following precautionary steps are taken by the supervisors or employers to avoid sexual harassment in workplace?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following terms refers to a mechanism which proves that the sender really sent a particular message?
Mark is the Administrator of a Linux computer. He wants to check the status of failed Telnet-based login attempts on the Linux computer. Which of the following shell commands will he use to accomplish the task?
Mark works as a security manager for SofTech Inc. He is using a technique for monitoring what the employees are doing with corporate resources. Which of the following techniques is being used by Mark to gather evidence of an ongoing computer crime if a member of the staff is e-mailing company ' s secrets to an opponent?
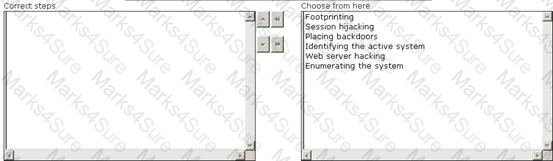
Maria works as a professional Ethical Hacker. She recently got a project to test the security of www.we-are-secure.com. Arrange the three pre-test phases of the attack to test the security of weare-secure.
Fill in the blank with the appropriate name.
_____is a list, which specifies the order of volatility of data in a Windows based system.
Which of the following directories cannot be placed out of the root filesystem?
Each correct answer represents a complete solution. Choose all that apply.
By gaining full control of router, hackers often acquire full control of the network. Which of the following methods are commonly used to attack Routers?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following file systems contains hardware settings of a Linux computer?
You are handling technical support calls for an insurance company. A user calls you complaining that he cannot open a file, and that the file name appears in green while opening in Windows Explorer.
What does this mean?
Adam works as a professional Penetration tester. A project has been assigned to him to employ penetration testing on the network of Umbrella Inc. He is running the test from home and had downloaded every security scanner from the Internet. Despite knowing the IP range of all of the systems, and the exact network configuration, Adam is unable to get any useful results.
Which of the following is the most like cause of this problem?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is the first computer virus that was used to infect the boot sector of storage media formatted with the DOS File Allocation Table (FAT) file system?
Nathan works as a Computer Hacking Forensic Investigator for SecureEnet Inc. He uses Visual TimeAnalyzer software to track all computer usage by logging into individual users account or specific projects and compile detailed accounts of time spent within each program. Which of the following functions are NOT performed by Visual TimeAnalyzer?
Each correct answer represents a complete solution. Choose all that apply.
Sandra, a novice computer user, works on Windows environment. She experiences some problem regarding bad sectors formed in a hard disk of her computer. She wants to run CHKDSK command to check the hard disk for bad sectors and to fix the errors, if any, occurred. Which of the following switches will she use with CHKDSK command to accomplish the task?
Which of the following tools can be used by a user to hide his identity?
Each correct answer represents a complete solution. Choose all that apply.
In which of the following access control models can a user not grant permissions to other users to see a copy of an object marked as secret that he has received, unless they have the appropriate permissions?
You work as the Network Administrator for McNeil Inc. The company has a Unix-based network. You want to allow direct access to the filesystems data structure. Which of the following Unix commands can you use to accomplish the task?
Nathan works as a professional Ethical Hacker. He wants to see all open TCP/IP and UDP ports of his computer. Nathan uses the netstat command for this purpose but he is still unable to map open ports to the running process with PID, process name, and path. Which of the following commands will Nathan use to accomplish the task?
Adam, a malicious hacker has successfully gained unauthorized access to the Linux system of
Umbrella Inc. Web server of the company runs on Apache. He has downloaded sensitive documents and database files from the computer. After performing these malicious tasks, Adam finally runs the following command on the Linux command box before disconnecting. for (( i = 0;i < 11;i++ )); do
dd if=/dev/random of=/dev/hda & & dd if=/dev/zero of=/dev/hda done
Which of the following actions does Adam want to perform by the above command?
Which of the following attacks saturates network resources and disrupts services to a specific computer?
You want to upgrade a partition in your computer ' s hard disk drive from FAT to NTFS. Which of the following DOS commands will you use to accomplish this?
Normally, RAM is used for temporary storage of data. But sometimes RAM data is stored in the hard disk, what is this method called?
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate the BlackBerry, which is suspected to be used to hide some important information. Which of the following is the first step taken to preserve the information in forensic investigation of the BlackBerry?
You are the Network Administrator and your company has recently implemented encryption for all emails. You want to check to make sure that the email packages are being encrypted. What tool would you use to accomplish this?
Which of the following statements about an extended partition are true?
Each correct answer represents a complete solution. Choose two.
Adam works as a professional Computer Hacking Forensic Investigator. He has been called by the FBI to examine data of the hard disk, which is seized from the house of a suspected terrorist. Adam decided to acquire an image of the suspected hard drive. He uses a forensic hardware tool, which is capable of capturing data from IDE, Serial ATA, SCSI devices, and flash cards. This tool can also produce MD5 and CRC32 hash while capturing the data. Which of the following tools is Adam using?
Which of the following two cryptography methods are used by NTFS Encrypting File System (EFS) to encrypt the data stored on a disk on a file-by-file basis?
You are reviewing a Service Level Agreement between your company and a Web development vendor.
Which of the following are security requirements you should look for in this SLA?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is a correct sequence of different layers of Open System Interconnection (OSI) model?
Which of the following directories contains administrative commands and daemon processes in the Linux operating system?
Brutus is a password cracking tool that can be used to crack the following authentications:
HTTP (Basic Authentication)
HTTP (HTML Form/CGI)
POP3 (Post Office Protocol v3)
FTP (File Transfer Protocol)
SMB (Server Message Block)
Telnet
Which of the following attacks can be performed by Brutus for password cracking?
Each correct answer represents a complete solution. Choose all that apply.
Adam works as a professional Computer Hacking Forensic Investigator. He has been assigned with a project to investigate a computer in the network of SecureEnet Inc. The compromised system runs on Windows operating system. Adam decides to use Helix Live for Windows to gather data and electronic evidences starting with retrieving volatile data and transferring it to server component via TCP/IP. Which of the following application software in Helix Windows Live will he use to retrieve volatile data and transfer it to the server component via TCP/IP?
Which of the following registry hives stores configuration information specific to a particular user who is currently logged on to the computer?
Which of the following tools is used to locate lost files and partitions to restore data from a formatted, damaged, or lost partition in Windows and Apple Macintosh computers?
Which of the following Windows XP system files handles memory management, I/O operations, and interrupts?
Which of the following representatives of incident response team takes forensic backups of the systems that are the focus of the incident?
Mark works as a Network administrator for SecureEnet Inc. His system runs on Mac OS X. He wants to boot his system from the Network Interface Controller (NIC). Which of the following snag keys will Mark use to perform the required function?
Your network has a Windows 2000 Server computer with FAT file system, shared by several users.
This system stores sensitive data. You decide to encrypt this data to protect it from unauthorized access. You want to accomplish the following goals:
Data should be secure and encrypted.
Administrative efforts should be minimum.
You should have the ability to recover encrypted files in case the file owner leaves the company.
Other permissions on encrypted files should be unaffected.
File-level security is required on the disk where data is stored.
Encrypting or decrypting of files should not be the responsibility of the file owner.
You take the following steps to accomplish these goals :
Convert the FAT file system to Windows 2000 NTFS file system.
Use Encrypting File System (EFS) to encrypt data.
Which of the following goals will you be able to accomplish?
Each correct answer represents a complete solution. Choose all that apply.
Convention on Cybercrime, created by the Council of Europe, is the treaty seeking to address
Computer crime and Internet crimes by harmonizing national laws, improving investigative techniques, and increasing cooperation among nations. Which of the following chapters of Convention of Cybercrime contains the provisions for mutual assistances and extradition rules related to cybercrimes?
What is the name of the group of blocks which contains information used by the operating system in Linux system?
You work as the Network Administrator for McNeil Inc. The company has a Unix-based network. You want to query an image root device and RAM disk size. Which of the following Unix commands can you use to accomplish the task?
You work as a Network Administrator for Net World International. You want to configure a Windows 2000 computer to dual boot with Windows 98. The hard disk drive of the computer will be configured as a single partition drive. Which of the following file systems will you use to accomplish this?
Trinity wants to send an email to her friend. She uses the MD5 generator to calculate cryptographic hash of her email to ensure the security and integrity of the email. MD5 generator, which Trinity is using operates in two steps:
Creates check file
Verifies the check file
Which of the following MD5 generators is Trinity using?
Which of the following Windows Registry key contains the password file of the user?
Which of the following tools is a wireless sniffer and analyzer that works on the Windows operating system?
Which of the following firewalls depends on the three-way handshake of the TCP protocol?
Joseph works as a Web Designer for WebTech Inc. He creates a Web site and wants to protect it from lawsuits. Which of the following steps will he take to accomplish the task?
Each correct answer represents a part of the solution. Choose all that apply.
Which of the following is the Windows feature on which the file management can be performed by a PC user?
An attacker attempts to gain information about a network by specifically targeting the network resources and applications running on a computer. This method for gaining information is known as ______.
Which of the following U.S. Federal laws addresses computer crime activities in communication lines, stations, or systems?
Which of the following graphical tools is used to navigate through directory structures?
Adam works as a Security Administrator for Umbrella Technology Inc. He reported a breach in security to his senior members, stating that " security defenses has been breached and exploited for 2 weeks by hackers. " The hackers had accessed and downloaded 50,000 addresses containing customer credit cards and passwords. Umbrella Technology was looking to law enforcement officials to protect their intellectual property. The intruder entered through an employee ' s home machine, which was connected to Umbrella Technology ' s corporate VPN network. The application called BEAST Trojan was used in the attack to open a " back door " allowing the hackers undetected access. The security breach was discovered when customers complained about the usage of their credit cards without their knowledge. The hackers were traced back to Shanghai, China through e-mail address evidence. The credit card information was sent to that same e-mail address. The passwords allowed the hackers to access Umbrella Technology ' s network from a remote location, posing as employees.
Which of the following actions can Adam perform to prevent such attacks from occurring in future?
You are a professional Computer Hacking forensic investigator. You have been called to collect the evidences of Buffer Overflows or Cookie snooping attack. Which of the following logs will you review to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
John used to work as a Network Administrator for We-are-secure Inc. Now he has resigned from the company for personal reasons. He wants to send out some secret information of the company. To do so, he takes an image file and simply uses a tool image hide and embeds the secret file within an image file of the famous actress, Jennifer Lopez, and sends it to his Yahoo mail id. Since he is using the image file to send the data, the mail server of his company is unable to filter this mail. Which of the following techniques is he performing to accomplish his task?
Which of the following is used to store configuration settings and options on Microsoft Windows operating systems?
Which of the following is described in the following statement?
" It is a 512 bytes long boot sector that is the first sector of a default boot drive. It is also known as Volume Boot Sector, if the boot drive is un-partitioned. "
You work as the Network Administrator for McNeil Inc. The company has a Unix-based network. You want to run a command that forces all the unwritten blocks in the buffer cache to be written to the disk. Which of the following Unix commands can you use to accomplish the task?
Adam works as a Computer Hacking Forensic Investigator. He has been assigned a project to
investigate child pornography. As the first step, Adam found that the accused is using a Peer-to-peer application to network different computers together over the internet and sharing pornographic materials of children with others. Which of the following are Peer-to-Peer applications?
Each correct answer represents a complete solution. Choose all that apply.
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He wants to test the effect of a virus on the We-are-secure server. He injects the virus on the server and, as a result, the server becomes infected with the virus even though an established antivirus program is installed on the server. Which of the following do you think are the reasons why the antivirus installed on the server did not detect the virus injected by John?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following files in LILO booting process of Linux operating system stores the location of Kernel on the hard drive?
You work as a professional Computer Hacking Forensic Investigator. A project has been assigned to you to investigate Plagiarism occurred in the source code files of C#. Which of the following tools will you use to detect the software plagiarism?
Peter works as a Security Administrator for SecureEnet Inc. He observes that the database server of the company has been compromised and the data is stolen. Peter immediately wants to report this crime to the law enforcement authorities. Which of the following organizations looks after the computer crimes investigations in the United States?
John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. He wants to forward all the kernel messages to the remote host having IP address 192.168.0.1. Which of the following changes will he perform in the syslog.conf file to accomplish the task?
Fill in the blank with the appropriate file system.
Alternate Data Streams (ADS) is a feature of the_____ file system, which allows more than one data stream to be associated with a filename.
Which of the following files starts the initialization process in booting sequence of the Linux operating system?
Victor works as a professional Ethical Hacker for SecureEnet Inc. He has been assigned a job to test an image, in which some secret information is hidden, using Steganography. Victor performs the following techniques to accomplish the task:
1. Smoothening and decreasing contrast by averaging the pixels of the area where significant color transitions occurs.
2. Reducing noise by adjusting color and averaging pixel value.
3. Sharpening, Rotating, Resampling, and Softening the image.
Which of the following Steganography attacks is Victor using?
A Web-based credit card company had collected financial and personal details of Mark before issuing him a credit card. The company has now provided Mark ' s financial and personal details to another company. Which of the following Internet laws has the credit card issuing company violated?
Your Windows XP hard drive has 2 partitions. The system partition is NTFS and the other is FAT. You wish to encrypt a folder created on the system partition for the purpose of data security. Which of the following statements is true about this situation?
Which of the following can be monitored by using the host intrusion detection system (HIDS)?
Each correct answer represents a complete solution. Choose two.
Which of the following statements is NOT true about FAT16 file system?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is a formula, practice, process, design, instrument, pattern, or compilation of information which is not generally known, but by which a business can obtain an economic advantage over its competitors?
You work as the Network Administrator for McNeil Inc. The company has a Unix-based network. You want to set the hard disk geometry parameters, cylinders, heads, and sectors. Which of the following Unix commands can you use to accomplish the task?
Every network device contains a unique built in Media Access Control (MAC) address, which is used to identify the authentic device to limit the network access. Which of the following addresses is a valid MAC address?
Which of the following articles defines illegal access to the computer or network in Chapter 2 of Section 1, i.e., Substantive criminal law of the Convention on Cybercrime passed by the Council of Europe?