Which of the following ICMPv6 neighbor discovery messages is sent by hosts to request an immediate router advertisement, instead of waiting for the next scheduled advertisement?
Peter works as a Computer Hacking Forensic Investigator. He has been called by an organization to conduct a seminar to give necessary information related to sexual harassment within the work place. Peter started with the definition and types of sexual harassment. He then wants to convey that it is important that records of the sexual harassment incidents should be maintained, which helps in further legal prosecution. Which of the following data should be recorded in this documentation?
Each correct answer represents a complete solution. Choose all that apply.
You are the Network Administrator for a large corporate network. You want to monitor all network traffic on your local network for suspicious activities and receive a notification when a possible attack is in process. Which of the following actions will you take for this?
You work as a Network Administrator for TechPerfect Inc. The company has a corporate intranet setup.
A router is configured on your network to connect outside hosts to the internetworking. For security, you want to prevent outside hosts from pinging to the hosts on the internetwork. Which of the following steps will you take to accomplish the task?
Which of the following statements about the traceroute utility are true?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following intrusion detection systems (IDS) produces the false alarm because of the abnormal behavior of users and network?
John, a malicious hacker, forces a router to stop forwarding packets by flooding it with many open connections simultaneously so that all hosts behind it are effectively disabled. Which of the following attacks is John performing?
At which of the following layers of the Open System Interconnection (OSI) model the Internet Control Message Protocol (ICMP) and the Internet Group Management Protocol (IGMP) work?
You work as a Network Administrator for Tech Perfect Inc. The office network is configured as an IPv6 network. You have to configure a computer with the IPv6 address, which is equivalent to an IPv4 publicly routable address. Which of the following types of addresses will you choose?
Which of the following attacks sends false ICMP packets in an attempt to cripple a system using random fake Internet source addresses?
Which of the following security protocols uses a single, manually configured, static key for data encryption that is shared by the client and the WAP?
In which of the following conditions is the SYN Protector rule base activated in passive mode?
Distributed Checksum Clearinghouse (DCC) is a hash sharing method of spam email detection.
Which of the following protocols does the DCC use?
John works as the Security Manager for PassGuide Inc. He wants to create the Profiler database that stores information about the network activity at Layer 3, Layer 4, and Layer 7. Which of the following will he use to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following Wireless LAN standard devices is least affected by interference from domestic appliances such as microwave ovens?
Which of the following Intrusion Detection Systems (IDS) is used to monitor rogue access points and the use of wireless attack tools?
Which of the following statements are true about an IPv6 network?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following steps are generally followed in computer forensic examinations?
Each correct answer represents a complete solution. Choose three.
John works as a professional Ethical Hacker. He has been assigned a project for testing the security of www.we-are-secure.com. He wants to corrupt an IDS signature database so that performing attacks on the server is made easy and he can observe the flaws in the We-are-secure server. To perform his task, he first of all sends a virus that continuously changes its signature to avoid detection from IDS. Since the new signature of the virus does not match the old signature, which is entered in the IDS signature database, IDS becomes unable to point out the malicious virus. Which of the following IDS evasion attacks is John performing?
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.we-are-secure.com. You have searched all open ports of the we-are-secure server. Now, you want to perform the next information-gathering step, i.e., passive OS fingerprinting. Which of the following tools can you use to accomplish the task?
You work as a Security Administrator for Tech Perfect Inc. You have implemented and configured a web application security scanner in the company ' s network. It helps in the automated review of
the web applications with the defined purpose of discovering security vulnerabilities. In order to perform this task, the web application security scanner examines a number of vulnerabilities. What are these vulnerabilities?
Each correct answer represents a complete solution. Choose three.
You are implementing passive OS fingerprinting in a network. Which of the following aspects are required to be configured there?
Each correct answer represents a part of the solution. Choose all that apply.
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based routed network. You have recently come to know about the Slammer worm, which attacked computers in 2003 and doubled the number of infected hosts every 9 seconds or so. Slammer infected 75000 hosts in the first 10 minutes of the attack. To mitigate such security threats, you want to configure security tools on the network. Which of the following tools will you use?
Peter works as a Technical Representative in a CSIRT for SecureEnet Inc. His team is called to investigate the computer of an employee, who is suspected for classified data theft. Suspect ' s computer runs on Windows operating system. Peter wants to collect data and evidences for further analysis. He knows that in Windows operating system, the data is searched in pre-defined steps for proper and efficient analysis. Which of the following is the correct order for searching data on a Windows based system?
Which of the following attacking methods allows the bypassing of access control lists on servers or routers, either hiding a computer on a network or allowing it to impersonate another computer by changing the Media Access Control address?
You work as a Network Administrator for NetTech Inc. You want to prevent your network from Ping flood attacks. Which of the following protocols will you block to accomplish this task?
Which of the following devices is used to identify out-of-date software versions, applicable patches, system upgrades, etc?
A packet filtering firewall inspects each packet passing through the network and accepts or rejects it based on user-defined rules. Based on which of the following information are these rules set to filter the packets?
Each correct answer represents a complete solution. Choose all that apply.
Windump is a Windows port of the famous TCPDump packet sniffer available on a variety of platforms. In order to use this tool on the Windows platform a user must install a packet capture library.
What is the name of this library?
A remote-access VPN offers secured and encrypted connections between mobile or remote users and their corporate network across public networks. Which of the following does the remote-access VPN use for offering these types of connections?
Each correct answer represents a complete solution. Choose two.
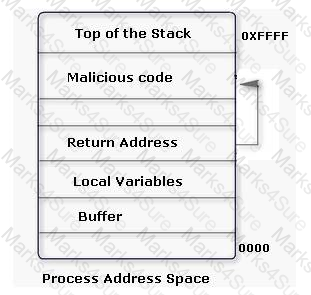
An attacker changes the address of a sub-routine in such a manner that it begins to point to the address of the malicious code. As a result, when the function has been exited, the application can be forced to shift to the malicious code. The image given below explains this phenomenon:
Which of the following tools can be used as a countermeasure to such an attack?
Which of the following monitors program activities and modifies malicious activities on a system?
You work as a Firewall Analyst in the Tech Perfect Inc. The company has a Linux-based environment. You have installed and configured netfilter/iptables on all computer systems. What are the main features of netfilter/iptables?
Each correct answer represents a complete solution. Choose all that apply.
Adam works as a professional Computer Hacking Forensic Investigator, a project has been assigned to him to investigate and examine files present on suspect ' s computer. Adam uses a tool with the help of which he can examine recovered deleted files, fragmented files, and other corrupted data. He can also examine the data, which was captured from the network, and access the physical RAM, and any processes running in virtual memory with the help of this tool. Which of the following tools is Adam using?
WinDump, tcpdump, and Wireshark specify which fields of information libpcap should record.
Which of the following filters do they use in order to accomplish the task?
What are the advantages of stateless autoconfigration in IPv6?
Each correct answer represents a part of the solution. Choose three.
You work as a Security Manger for Tech Perfect Inc. The company has a Windows-based network.
You want to scroll real-time network traffic to a command console in a readable format. Which of the following command line utilities will you use to accomplish the task?
You are the Network Administrator for a college. Wireless access is widely used at the college. You want the most secure wireless connections you can have. Which of the following would you use?
You work as a technician for Tech Perfect Inc. You are troubleshooting an Internet name resolution issue. You ping your ISP ' s DNS server address and find that the server is down. You want to continuously ping the DNS address until you have stopped the command. Which of the following commands will you use?
Adam works on a Linux system. He is using Sendmail as the primary application to transmit e-mails. Linux uses Syslog to maintain logs of what has occurred on the system. Which of the following log files contains e-mail information such as source and destination IP addresses, date and time stamps etc?
SSH is a network protocol that allows data to be exchanged between two networks using a secure channel. Which of the following encryption algorithms can be used by the SSH protocol?
Each correct answer represents a complete solution. Choose all that apply.
You work as the Security Administrator for Prodotxiss Inc. You want to ensure the security of your Wi- Fi enterprise network against the wireless snooping attacks. Which of the following measures will you take over the site network devices of the network?
You work as a Network Administrator for Blue Bell Inc. The company has a TCP-based network. The company has two offices in different cities. The company wants to connect the two offices by using a public network. You decide to configure a virtual private network ( VPN ) between the offices. Which of the following protocols is used by VPN for tunneling?
Session splicing is an IDS evasion technique in which an attacker delivers data in multiple small-sized packets to the target computer. Hence, it becomes very difficult for an IDS to detect the attack signatures of such attacks. Which of the following tools can be used to perform session splicing attacks?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following utilities provides an efficient way to give specific users permission to use specific system commands at the root level of a Linux operating system?
Which of the following IPv4 fields become obsolete while removing the hop-by-hop segmentation (fragmentation) procedure from the IP header?
Each correct answer represents a part of the solution. Choose three.
Which of the following TShark options is used to set capture buffer size in MB?
John works as a Network Administrator for Web Perfect Inc. The company has a wireless LAN network. John has configured shared key authentication on a client. The client and the AP start exchanging the frames to enable authentication. Which of the following vulnerabilities may occur while the client and the AP exchange the challenge text over the wireless link?
Fill in the blank with the appropriate tool name.
______________ is a network protocol analyzer tool that is used to capture packet data from an existing network or examine packet data from a pre-saved file.
This is a Windows-based tool that is used for the detection of wireless LANs using the IEEE 802.11a, 802.11b, and 802.11g standards. The main features of these tools are as follows:
l It displays the signal strength of a wireless network, MAC address, SSID, channel details, etc.
l It is commonly used for the following purposes:
a. War driving
b. Detecting unauthorized access points
c. Detecting causes of interference on a WLAN
d. WEP ICV error tracking
e. Making Graphs and Alarms on 802.11 Data, including Signal Strength
This tool is known as __________.
Which of the following is used for debugging the network setup itself by determining whether all necessary routing is occurring properly, allowing the user to further isolate the source of a problem?
Which of the following vulnerability scanners is used to test Web servers for dangerous files/CGIs, outdated server software, and other problems?
Adam works as a Security administrator for Umbrella Inc. He runs the following traceroute and notices that hops 19 and 20 both show the same IP address.
1 172.16.1.254 (172.16.1.254) 0.724 ms 3.285 ms 0.613 ms 2 ip68-98-176-
1.nv.nv.cox.net (68.98.176.1) 12.169 ms 14.958 ms 13.416 ms 3 ip68-98-176-
1.nv.nv.cox.net (68.98.176.1) 13.948 ms ip68-100-0-1.nv.nv. cox.net (68.100.0.1)
16.743 ms 16.207 ms 4 ip68-100-0-137.nv.nv.cox.net (68.100.0.137) 17.324 ms 13.933
ms 20.938 ms 5 68.1.1.4 (68.1.1.4) 12.439 ms 220.166 ms 204.170 ms
6 so-6-0-0.gar2.wdc1.Level3.net (67.29.170.1) 16.177 ms 25.943 ms 14.104 ms 7
unknown.Level3.net (209.247.9.173) 14.227 ms 17.553 ms 15.415 ms " PassGuide " -
8 so-0-1-0.bbr1.NewYork1.level3.net (64.159.1.41) 17.063 ms 20.960 ms 19.512 ms 9
so-7-0-0.gar1. NewYork1.Level3.net (64.159.1.182) 20.334 ms 19.440 ms 17.938 ms
10 so-4-0-0.edge1.NewYork1.Level3.
net (209.244.17.74) 27.526 ms 18.317 ms 21.202 ms 11 uunet-level3-
oc48.NewYork1.Level3.net
(209.244.160.12) 21.411 ms 19.133 ms 18.830 ms 12 0.so-6-0-0.XL1.NYC4.ALTER.NET
(152.63.21.78)
21.203 ms 22.670 ms 20.111 ms 13 0.so-2-0-0.TL1.NYC8.ALTER.NET (152.63.0.153)
30.929 ms 24.858 ms
23.108 ms 14 0.so-4-1-0.TL1.ATL5.ALTER.NET (152.63.10.129) 37.894 ms 33.244 ms
33.910 ms 15 0.so-7-0-0.XL1.MIA4.ALTER.NET (152.63.86.189) 51.165 ms 49.935 ms
49.466 ms 16 0.so-3-0-0.XR1.MIA4.ALTER.
NET (152.63.101.41) 50.937 ms 49.005 ms 51.055 ms 17 117.ATM6-
0.GW5.MIA1.ALTER.NET (152.63.82.73) 51.897 ms 50.280 ms 53.647 ms 18 PassGuidegw1.
customer.alter.net (65.195.239.14) 51.921 ms 51.571 ms 56.855 ms 19
www.PassGuide.com (65.195.239.22) 52.191 ms 52.571 ms 56.855 ms 20
www.PassGuide.com (65.195.239.22) 53.561 ms 54.121 ms 58.333 ms
Which of the following is the most like cause of this issue?
Which of the following wireless security features provides the best wireless security mechanism?
Which of the following is like a malicious cache poisoning where fake data is placed in the cache of the name servers?
As a professional hacker, you want to crack the security of secureserver.com. For this, in the information gathering step, you performed scanning with the help of nmap utility to retrieve as many different protocols as possible being used by the secureserver.com so that you could get the accurate knowledge about what services were being used by the secure server.com. Which of the following nmap switches have you used to accomplish the task?
Which of the following attacks allows an attacker to sniff data frames on a local area network (LAN) or stop the traffic altogether?
Which of the following features does the Nmap utility have?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following attacks generates falsified information within an IP header?
Which of the following applications cannot proactively detect anomalies related to a computer?
You work as a Forensic Investigator. Which of the following rules will you follow while working on a case?
Each correct answer represents a part of the solution. Choose all that apply.
Which of the following group management messages is used by routers to handle the IPv6 multicast routing?
Which of the following tools allows an attacker to intentionally craft the packets to gain unauthorized access?
Each correct answer represents a complete solution. Choose two.
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. A Cisco switch is configured on the network. You change the original host name of the switch through the hostname command. The prompt displays the changed host name. After some time, power of the switch went off due to some reason. When power restored, you find that the prompt is displaying the old host name. What is the most likely cause?
What is the easiest way to verify that name resolution is functioning properly on a TCP/IP network?
Which of the following are the reasons that network administrators use Access Control Lists?
Each correct answer represents a complete solution. Choose two.
A scenario involves a pool of users with private IP addresses who need to access the Internet; however, the company has a limited number of IP addresses and needs to ensure users occupy only one public IP address.
Which technology is used to allow a pool of users to share one global IP address for Internet access?
You are configuring a public access wireless connection. Which of the following is the best way to secure this connection?
In which of the following IDS evasion techniques does an attacker deliver data in multiple small sized packets, which makes it very difficult for an IDS to detect the attack signatures of such attacks?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has successfully completed the following steps of the preattack phase:
l Information gathering
l Determining network range
l Identifying active machines
l Finding open ports and applications
l OS fingerprinting
l Fingerprinting services
Now John wants to perform network mapping of the We-are-secure network. Which of the following tools can he use to accomplish his task?
Each correct answer represents a complete solution. Choose all that apply.
An organization has more than a couple of external business, and exchanges dynamic routing information with the external business partners. The organization wants to terminate all routing from a partner at an edge router, preferably receiving only summary routes from the partner. Which of the following will be used to change all partner addresses on traffic into a range of locally assigned addresses?
Adam works as a Network Administrator for PassGuide Inc. He wants to prevent the network from DOS attacks. Which of the following is most useful against DOS attacks?
You work as a professional Computer Hacking Forensic Investigator for DataEnet Inc. You want to investigate e-mail information of an employee of the company. The suspected employee is using an online e-mail system such as Hotmail or Yahoo. Which of the following folders on the local computer will you review to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following intrusion detection systems (IDS) monitors network traffic and compares it against an established baseline?
John, a malicious hacker, forces a router to stop forwarding packets by flooding it with many open connections simultaneously so that all hosts behind it are effectively disabled. Which of the following attacks is John performing?
You work as a Network Architect for Tech Perfect Inc. The company has a TCP/IP based network. You have established a remote-access VPN network between mobile users and the company ' s network. You want to implement the following features in the remote-access VPN network:
l Provide security for the web traffic.
l Browser clients can support the VPN connection to a host.
Which of the following will you configure to implement the given features in the network?
Which of the following is a Cisco IOS management term described in the statement below?
" It is the fourth digit in the configuration register and contains a hexadecimal value. The bootstrap program uses its value to choose which operating system to load into RAM. "
Which of the following ICMPv6 neighbor discovery messages is sent by hosts to request an immediate router advertisement, instead of waiting for the next scheduled advertisement?
A firewall is a combination of hardware and software, used to provide security to a network. It is used to protect an internal network or intranet against unauthorized access from the Internet or other outside networks. It restricts inbound and outbound access and can analyze all traffic between an internal network and the Internet. Users can configure a firewall to pass or block packets from specific IP addresses and ports. Which of the following tools works as a firewall for the Linux 2.4 kernel?
Passive OS fingerprinting (POSFP) is configured in an organization ' s network in order to improve the alert output by reporting some information. Which of the following information does it include?
Each correct answer represents a part of the solution. Choose all that apply.
Which of the following is a version of netcat with integrated transport encryption capabilities?
Adam works as a Senior Programmer for Umbrella Inc. A project has been assigned to him to write a short program to gather user input for a Web application. He wants to keep his program neat and simple. His chooses to use printf(str) where he should have ideally used printf( " %s " , str).
What attack will his program expose the Web application to?
Which of the following devices works as a transparent bridge between the wireless clients and the wired network?
You work as a Forensic Investigator. Which of the following rules will you follow while working on a case?
Each correct answer represents a part of the solution. Choose all that apply.
Which of the following wireless security policies helps to prevent the wireless enabled laptops from peer-topeer attacks when the laptops are used in public access network?
Which of the following files is a Cisco IOS configuration files that resides in RAM?
Fill in the blank with the appropriate utility.
________ is a table-based system or structure that defines the rulesets needed to transform or filter network packets.
The simplest form of a firewall is a packet filtering firewall. A packet filtering firewall filters packets at the Network layer and Transport layer. What are the types of information that are filtered at the Network layer of the OSI reference model?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tools is used to detect spam email without checking the content?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network.
You have configured an 802.11g Wireless LAN ( WLAN ) on your network. Which of the following factors can deteriorate the performance and range of the WLAN?
Each correct answer represents a complete solution. Choose all that apply.
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. John notices that the We-are-secure network is vulnerable to a man-inthe- middle attack since the key exchange process of the cryptographic algorithm it is using does not authenticate participants. Which of the following cryptographic algorithms is being used by the Weare- secure server?
Which of the following hexadecimal values in the boot field in the configuration register loads the first IOS file found in Flash memory?
Adam works as a Senior Programmer for Umbrella Inc. A project has been assigned to him to write a short program to gather user input for a Web application. He wants to keep his program neat and simple. His chooses to use printf(str) where he should have ideally used printf( " %s " , str).
What attack will his program expose the Web application to?
Which of the following techniques correlates information found on multiple hard drives?
Which of the following address translation types only translates one (and only one) IP address to another without using ports?
Which of the following types of firewalls increases the security of data packets by remembering the state of connection at the network and the session layers as they pass through the filter?
Which of the following tools detects certain types of packet filters and NAT setups?
Which of the following vulnerability scanners is used to test Web servers for dangerous files/CGIs, outdated server software, and other problems?
You work as a Network Administrator for Rick International. The company has a TCP/IP-based network. A user named Kevin wants to set an SSH terminal at home to connect to the company ' s network. You have to configure your company ' s router for it. By default, which of the following standard ports does the SSH protocol use for connection?
You work as a Network Adminstrator at PassGuide Inc. You want to implement a solution that will automatically disallow connections if an attack is suspected. Which of the following technologies will you choose to accomplish the task?
In which of the following attacks does an attacker change the MAC address on the sniffer to one that is the same in another system on the local subnet?