Adam works as a Security Administrator for Umbrella Inc. A project has been assigned to him to secure access to the network of the company from all possible entry points. He segmented the network into several subnets and installed firewalls all over the network. He has placed very stringent rules on all the firewalls, blocking everything in and out except ports that must be used.
He does need to have port 80 open since his company hosts a website that must be accessed from the Internet. Adam is still worried about programs like Hping2 that can get into a network through covert channels.
Which of the following is the most effective way to protect the network of the company from an attacker using Hping2 to scan his internal network?
When no anomaly is present in an Intrusion Detection, but an alarm is generated, the response is known as __________.
Which of the following proxy servers is also referred to as transparent proxies or forced proxies?
Which of the following techniques is used to identify attacks originating from a botnet?
Which of the following applications cannot proactively detect anomalies related to a computer?
Which of the following types of Intrusion detection systems (IDS) is used for port mirroring?
Which of the following is a technique of attacks in which the attacker secretly listens to the private conversation between victims?
Which of the following tools is described below?
It is a set of tools that are used for sniffing passwords, e-mail, and HTTP traffic. Some of its tools include arpredirect, macof, tcpkill, tcpnice, filesnarf, and mailsnarf. It is highly effective for sniffing both switched and shared networks. It uses the arpredirect and macof tools for switching across switched networks. It can also be used to capture authentication information for FTP, telnet, SMTP, HTTP, POP, NNTP, IMAP, etc.
Which of the following tools is used to detect wireless LANs using the 802.11b, 802.11a, and 802.11g WLAN standards on the Windows platform?
Which of the following would allow you to automatically close connections or restart a server or service when a DoS attack is detected?
Fill in the blank with the appropriate facts regarding IP version 6 ( IPv6 ).
IP addressing version 6 uses_____ -bit address. Its____ IP address assigned to a single host allows the host to send and receive data.
John enters a URL http://www.cisco.com/web/learning in the web browser. A web page appears after he enters the URL. Which of the following protocols is used to resolve www.cisco.com into the correct IP address?
Which of the following password cracking tools can work on the Unix and Linux environment?
In which of the following IDS evasion techniques does an attacker deliver data in multiple small sized packets, which makes it very difficult for an IDS to detect the attack signatures of such attacks?
What is the name of the first computer virus that infected the boot sector of the MS-DOS operating system?
Which of the following can be monitored by using the host intrusion detection system (HIDS)?
Each correct answer represents a complete solution. Choose two.
Which of the following ports is used by e-mail clients to send request to connect to the server?
The Intrusion Detection System (IDS) instructs the firewall to reject any request from a particular IP address if the network is repeatedly attacked from this address. What is this action known as?
John works as a Network Security Administrator for NetPerfect Inc. The manager of the company has told John that the company ' s phone bill has increased drastically. John suspects that the company ' s phone system has been cracked by a malicious hacker. Which attack is used by malicious hackers to crack the phone system?
Which of the following log files are used to collect evidences before taking the bit-stream image of the BlackBerry?
Each correct answer represents a complete solution. Choose all that apply.
You are the Administrator for a corporate network. You are concerned about denial of service attacks.
Which of the following would be the most help against Denial of Service (DOS) attacks?
Victor works as a professional Ethical Hacker for SecureEnet Inc. He has been assigned a job to test an image, in which some secret information is hidden, using Steganography. Victor performs the following techniques to accomplish the task:
1. Smoothening and decreasing contrast by averaging the pixels of the area where significant color transitions occurs.
2. Reducing noise by adjusting color and averaging pixel value.
3. Sharpening, Rotating, Resampling, and Softening the image.
Which of the following Steganography attacks is Victor using?
Which of the following statements are true about UDP?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following commands will you use with the tcpdump command to capture the traffic from a filter stored in a file?
You work as a professional Computer Hacking Forensic Investigator. A project has been assigned to you to investigate Plagiarism occurred in the source code files of C#. Which of the following tools will you use to detect the software plagiarism?
In which of the following attacks does a hacker imitate a DNS server and obtain the entire DNS database?
John works as a Network Security Administrator for NetPerfect Inc. The manager of the company has told John that the company ' s phone bill has increased drastically. John suspects that the company ' s phone system has been cracked by a malicious hacker. Which attack is used by malicious hackers to crack the phone system?
You work as a desktop administrator for BlueSkwer.com. You are logged on to a Windows 7 computer with administrator rights. You have run the ' netsh interface IPv6 show interface ' command which displays the following:
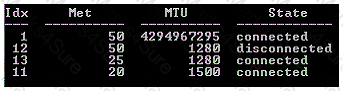
What is the first interface index used for?
Which of the following tools can be used to check whether the network interface is in promiscuous mode or not?
Mark works as a Network Security Administrator for BlueWells Inc. The company has a Windowsbased network. Mark is giving a presentation on Network security threats to the newly recruited employees of the company. His presentation is about the External threats that the company recently faced in the past. Which of the following statements are true about external threats?
Each correct answer represents a complete solution. Choose three.
Which of the following statements are true about routers?
Each correct answer represents a complete solution. Choose all that apply.
Andrew, a bachelor student of Faulkner University, creates a gmail account. He uses ' Faulkner ' as the password for the gmail account. After a few days, he starts receiving a lot of e-mails stating that his gmail account has been hacked. He also finds that some of his important mails have been deleted by someone. Which of the following methods has the attacker used to crack Andrew ' s password?
Each correct answer represents a complete solution. Choose all that apply.
Peter, a malicious hacker, wants to perform an attack. He first compromises computers distributed across the internet and then installs specialized software on these computers. He then instructs the compromised hosts to execute the attack. Every host can then be used to launch its own attack on the target computers. Which of the following attacks is Peter performing?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. John wants to redirect all TCP port 80 traffic to UDP port 40, so that he can bypass the firewall of the We-are-secure server. Which of the following tools will John use to accomplish his task?
Which of the following can be applied as countermeasures against DDoS attacks?
Each correct answer represents a complete solution. Choose all that apply.
Ryan, a malicious hacker submits Cross-Site Scripting (XSS) exploit code to the Website of Internet forum for online discussion. When a user visits the infected Web page, code gets automatically executed and Ryan can easily perform acts like account hijacking, history theft etc. Which of the following types of Cross-Site Scripting attack Ryan intends to do?
John works as a Network Security Professional. He is assigned a project to test the security of www.we-are-secure.com. He is working on the Linux operating system and wants to install an Intrusion Detection System on the We-are-secure server so that he can receive alerts about any hacking attempts. Which of the following tools can John use to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following information must the fragments carry for the destination host to reassemble them back to the original unfragmented state?
Each correct answer represents a complete solution. Choose all that apply.
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate a compromised system of a cyber criminal, who hides some information in his computer. This computer runs on Linux operating system. Adam wants to extract the data units of a file, which is specified by its meta-data address. He is using the Sleuth Kit for this purpose. Which of the following commands in the Sleuth kit will he use to accomplish the task?
Andrew, a bachelor student of Faulkner University, creates a gmail account. He uses ' Faulkner ' as the password for the gmail account. After a few days, he starts receiving a lot of e-mails stating that his gmail account has been hacked. He also finds that some of his important mails have been deleted by someone. Which of the following methods has the attacker used to crack Andrew ' s password?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tools in Helix Windows Live is used to reveal the database password of password protected MDB files created using Microsoft Access or with Jet Database Engine?
Which method would provide the highest level of protection for all data transmitted on the internal network only? (Click the Exhibit button on the toolbar to see the case study.)
You work as a Network Administrator for Tech Perfect Inc. The office network is configured as an IPv6 network. You have to configure a computer with the IPv6 address, which is equivalent to an IPv4 publicly routable address. Which of the following types of addresses will you choose?
Which of the following tools allows an attacker to intentionally craft the packets to gain unauthorized access?
Each correct answer represents a complete solution. Choose two.
Which of the following are core TCP/IP protocols that can be implemented with Windows NT to connect computers and internetworks?
Each correct answer represents a complete solution. Choose all that apply.
Andrew works as a System Administrator for NetPerfect Inc. All client computers on the network run on Mac OS X. The Sales Manager of the company complains that his MacBook is not able to boot. Andrew wants to check the booting process. He suspects that an error persists in the bootloader of Mac OS X. Which of the following is the default bootloader on Mac OS X that he should use to resolve the issue?
Which of the following commands will you use to display ARP packets in the snort-output?
A firewall is a combination of hardware and software, used to provide security to a network. It is used to protect an internal network or intranet against unauthorized access from the Internet or other outside networks. It restricts inbound and outbound access and can analyze all traffic between an internal network and the Internet. Users can configure a firewall to pass or block packets from specific IP addresses and ports. Which of the following tools works as a firewall for the Linux 2.4 kernel?
Windump is a Windows port of the famous TCPDump packet sniffer available on a variety of platforms. In order to use this tool on the Windows platform a user must install a packet capture library.
What is the name of this library?
Which of the following ports is used by e-mail clients to send request to connect to the server?
Which of the following are the two sub-layers present in Data Link layer of the OSI Reference model?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has written the following snort signature:
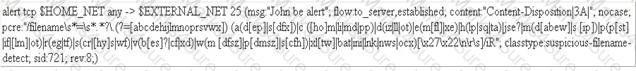
Which of the following statements about this snort signature is true?
You work as a Network Administrator for NetTech Inc. The company has a Windows Server 2008 domain-based network. The network contains four Windows Server 2008 member servers and 120 Windows Vista client computers. You are implementing a caching-only DNS server on one of the member servers. Your assistant wants to know about the caching-only DNS server. Which of the following statements about the caching-only DNS server are correct?
Each correct answer represents a complete solution. Choose three.
An attacker makes an attempt against a Web server. The result is that the attack takes the form of URLs. These URLs search for a certain string that identifies an attack against the Web server.
Which IDS/IPS detection method do the URLs use to detect and prevent an attack?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based routed network. You have recently come to know about the Slammer worm, which attacked computers in 2003 and doubled the number of infected hosts every 9 seconds or so. Slammer infected 75000 hosts in the first 10 minutes of the attack. To mitigate such security threats, you want to configure security tools on the network. Which of the following tools will you use?
Which of the following commands will you use with the tcpdump command to display the contents of the packets?
You work as a professional Computer Hacking Forensic Investigator for DataEnet Inc. You want to investigate e-mail information of an employee of the company. The suspected employee is using an online e-mail system such as Hotmail or Yahoo. Which of the following folders on the local computer will you review to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Adam works as a professional Computer Hacking Forensic Investigator. He has been called by the FBI to examine data of the hard disk, which is seized from the house of a suspected terrorist.
Adam decided to acquire an image of the suspected hard drive. He uses a forensic hardware tool, which is capable of capturing data from IDE, Serial ATA, SCSI devices, and flash cards. This tool can also produce MD5 and CRC32 hash while capturing the data. Which of the following tools is Adam using?
Which of the following tools works by using standard set of MS-DOS commands and can create an MD5 hash of an entire drive, partition, or selected files?
You work as a network administrator for Tech Perfect Inc. Rick, your assistant, requires information regarding his computer ' s IP address lease start date and expiry date. Which of the following commands will help him?
Mark works as a Network Security Administrator for BlueWells Inc. The company has a Windowsbased network. Mark is giving a presentation on Network security threats to the newly recruited employees of the company. His presentation is about the External threats that the company recently faced in the past. Which of the following statements are true about external threats?
Each correct answer represents a complete solution. Choose three.
Which of the following utilities allows to view all files including invisible files and folders on a Macintosh OS X?
Which of the following statements are true about snort?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for a bank. For securing the bank ' s network, you configure a firewall and an IDS. In spite of these security measures, intruders are able to attack the network.
After a close investigation, you find that your IDS is not configured properly and hence is unable to generate alarms when needed. What type of response is the IDS giving?
Which of the following two cryptography methods are used by NTFS Encrypting File System (EFS) to encrypt the data stored on a disk on a file-by-file basis?
Which of the following components are usually found in an Intrusion detection system (IDS) ?
Each correct answer represents a complete solution. Choose two.
Peter works as a Technical Representative in a CSIRT for SecureEnet Inc. His team is called to investigate the computer of an employee, who is suspected for classified data theft. Suspect ' s computer runs on Windows operating system. Peter wants to collect data and evidences for further analysis. He knows that in Windows operating system, the data is searched in pre-defined steps for proper and efficient analysis. Which of the following is the correct order for searching data on a Windows based system?
You work as a Network Administrator for TechPerfect Inc. The company has a corporate intranet setup. A router is configured on your network to connect outside hosts to the internetworking. For security, you want to prevent outside hosts from pinging to the hosts on the internetwork. Which of the following steps will you take to accomplish the task?
Which of the following standard file formats is used by Apple ' s iPod to store contact information?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. John wants to redirect all TCP port 80 traffic to UDP port 40, so that he can bypass the firewall of the We-are-secure server. Which of the following tools will John use to accomplish his task?
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate a multimedia enabled mobile phone, which is suspected to be used in a cyber crime. Adam uses a tool, with the help of which he can recover deleted text messages, photos, and call logs of the mobile phone. Which of the following tools is Adam using?
You are the Network Administrator for a large corporate network. You want to monitor all network traffic on your local network for suspicious activities and receive a notification when a possible attack is in process. Which of the following actions will you take for this?
Which of the following NETSH commands for interface Internet protocol version 4 (IPv4) is used to delete a DNS server or all DNS servers from a list of DNS servers for a specified interface or for all interfaces?
Which of the following DoS attacks points the Central Processing Unit (CPU) to a non-existent memory location causing the running process to end abruptly?
Which of the following forensic tool suite is developed for Linux operating system?
Which of the following commands is used to flush the destination cache for IPv6 interface?
In which of the following attacks does a hacker imitate a DNS server and obtain the entire DNS database?
Which of the following Web attacks is performed by manipulating codes of programming languages such as SQL, Perl, Java present in the Web pages?
What is the name of the group of blocks which contains information used by the operating system in Linux system?
Allen works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate a computer, which is used by the suspect to sexually harass the victim using instant messenger program. Suspect ' s computer runs on Windows operating system. Allen wants to recover password from instant messenger program, which suspect is using, to collect the evidence of the crime. Allen is using Helix Live for this purpose. Which of the following utilities of Helix will he use to accomplish the task?
Which of the following types of attacks uses ICMP to consume bandwidth and crash sites?
Adam works as a Computer Hacking Forensic Investigator in a law firm. He has been assigned with his first project. Adam collected all required evidences and clues. He is now required to write an investigative report to present before court for further prosecution of the case. He needs guidelines to write an investigative report for expressing an opinion. Which of the following are the guidelines to write an investigative report in an efficient way?
Each correct answer represents a complete solution. Choose all that apply.
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate a multimedia enabled mobile phone, which is suspected to be used in a cyber crime. Adam uses a tool, with the help of which he can recover deleted text messages, photos, and call logs of the mobile phone. Which of the following tools is Adam using?
Which of the following Windows XP system files handles memory management, I/O operations, and interrupts?
Which of the following fields of the IPv6 header is similar to the TTL field of IPv4?
Mark works as a Network Administrator for Infonet Inc. The company has a Windows 2000 domainbased network. Mark wants to block all NNTP traffic between the network and the Internet. How will he configure the network?
Which of the following is an open-source Web server scanner that tests Web servers for dangerous files/CGIs, outdated server software?
Which of the following cryptographic methods are used in EnCase to ensure the integrity of the data, which is acquired for the investigation?
Each correct answer represents a complete solution. Choose two.
For a host to have successful Internet communication, which of the following network protocols are required? You should assume that the users will not manually configure the computer in anyway and that the measure of success will be whether the user can access Web sites after powering the computer and logging on.
Each correct answer represents a complete solution. Choose all that apply.
Which of the following protocols is used to translate IP addresses to Ethernet addresses?
Which of the following partitions contains the system files that are used to start the operating system?
Which of the following DNS records is used for host name to IPv6 address resolution?
Which of the following Linux/UNIX commands is used to delete files permanently so that the files cannot be recovered?
Which of the following distributes incorrect IP address to divert the traffic?
Which of the following switches is used with Pslist command on the command line to show the statistics for all active threads on the system, grouping these threads with their owning process?
You work as a Network Administrator for McRobert Inc. Your company has a TCP/IP-based network.
You want to know the statistics of each protocol installed on your computer. Which of the following commands will you use?
Which of the following utilities is used for decrypting WEP encryption on an 802.11b network?
Sandra, an expert computer user, hears five beeps while booting her computer that has AMI BIOS; and after that her computer stops responding. Sandra knows that during booting process POST produces different beep codes for different types of errors. Which of the following errors refers to this POST beep code?
Which of the following methods is used by forensic investigators to acquire an image over the network in a secure manner?
Which of the following password cracking attacks is based on a pre-calculated hash table to retrieve plain text passwords?
Which of the following monitors program activities and modifies malicious activities on a system?
You work as a Desktop Support Technician for umbrella Inc. The company uses a Windows-based network. An employee from the sales department is facing problem in the IP configuration of the network connection. He called you to resolve the issue. You suspect that the IP configuration is not configured properly. You want to use the ping command to ensure that IPv4 protocol is working on a computer. While running the ping command from the command prompt, you find that Windows Firewall is blocking the ping command. What is the cause of the issue?
Which of the following techniques allows the existence of both the Ipv6 and Ipv4 protocols in a device or network?
Sandra, an expert computer user, hears five beeps while booting her computer that has AMI BIOS; and after that her computer stops responding. Sandra knows that during booting process POST produces different beep codes for different types of errors. Which of the following errors refers to this POST beep code?
What are the limitations of the POP3 protocol?
Each correct answer represents a complete solution. Choose three.
In a complex network, Router transfers data packets by observing some form of parameters or metrics provided in the routing table. Which of the following metrics is NOT included in the routing table?
Which of the following statements is NOT true about FAT16 file system?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is the default port for Hypertext Transfer Protocol (HTTP)?
Victor works as a professional Ethical Hacker for SecureNet Inc. He wants to use Steganographic file system method to encrypt and hide some secret information. Which of the following disk spaces will he use to store this secret information?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for McRobert Inc. You plan to configure your Windows Vista computer for Internet access. To achieve this, which of the following communication protocols needs to be bound to the dial-up adapter?
Adam works as a professional Computer Hacking Forensic Investigator. He has been assigned with a project to investigate a computer in the network of SecureEnet Inc. The compromised system runs on Windows operating system. Adam decides to use Helix Live for Windows to gather data and electronic evidences starting with retrieving volatile data and transferring it to server component via TCP/IP. Which of the following application software in Helix Windows Live will he use to retrieve volatile data and transfer it to the server component via TCP/IP?
Which of the following units of data does the data-link layer send from the network layer to the physical layer of the OSI model ?
You work as a Network Administrator for McRobert Inc. Your company has a TCP/IP-based network. You want to get the protocol statistics and the active TCP/IP network connections of your computer. Which of the following will you use?
You work as a Network Administrator for Net Perfect Inc. The company has a Windows Server 2008- based network. You have created a test domain for testing IPv6 addressing. Which of the following types of addresses are supported by IPv6?
Each correct answer represents a complete solution. Choose all that apply.
Fill in the blank with the appropriate term.
___________ is a technique used to make sure that incoming packets are actually from the networks that they claim to be from.
Peter works as a professional Computer Hacking Forensic Investigator for eLaw-Suit law firm. He is working on a case of a cyber crime. Peter knows that the good investigative report should not only communicate the relevant facts, but also present expert opinion. This report should not include the cases in which the expert acted as a lay witness. Which of the following type of witnesses is a lay witness?
You are using a Windows-based sniffer named ASniffer to record the data traffic of a network. You have extracted the following IP Header information of a randomly chosen packet from the sniffer ' s log:
45 00 00 28 00 00 40 00 29 06 43 CB D2 D3 82 5A 3B 5E AA 72
Which of the following TTL decimal values and protocols are being carried by the IP Header of this packet?
Which of the following is the process of categorizing attack alerts produced from an IDS in order to distinguish false positives from actual attacks?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He wants to send malicious data packets in such a manner that one packet fragment overlaps data from a previous fragment so that he can perform IDS evasion on the We-are-secure server and execute malicious data. Which of the following tools can he use to accomplish the task?
Maria works as the Chief Security Officer for passguide Inc. She wants to send secret messages to the CEO of the company. To secure these messages, she uses a technique of hiding a secret message within an ordinary message. The technique provides ' security through obscurity ' . What technique is Maria using?
Web applications are accessed by communicating over TCP ports via an IP address. Choose the two most common Web Application TCP ports and their respective protocol names.
Each correct answer represents a complete solution. Choose two.
You are implementing a host based intrusion detection system on your web server. You feel that the best way to monitor the web server is to find your baseline of activity (connections, traffic, etc.) and to monitor for conditions above that baseline. This type of IDS is called __________.
Adam, an expert computer user, doubts that virus named love.exe has attacked his computer. This virus acquires hidden and read-only attributes, so it is difficult to delete it. Adam decides to delete virus file love.exe from the command line. He wants to use del command for this purpose. Which of the following switches will he use with del command to delete hidden and read only-files?