John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He performs a Teardrop attack on the we-are-secure server and observes that the server crashes. Which of the following is the most likely cause of the server crash?
Which of the following tools is a wireless sniffer and analyzer that works on the Windows operating system?
Which of the following layers of TCP/IP model is used to move packets between the Internet Layer interfaces of two different hosts on the same link?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He performs a Teardrop attack on the we-are-secure server and observes that the server crashes. Which of the following is the most likely cause of the server crash?
Which of the following tools allow you to perform HTTP tunneling?
Each correct answer represents a complete solution. Choose all that apply.
In which of the following attacks does an attacker use packet sniffing to read network traffic between two parties to steal the session cookie?
In which of the following attacks is a malicious packet rejected by an IDS, but accepted by the host system?
Which of the following is the correct sequence of packets to perform the 3-way handshake method?
Which of the following event logs contains traces of brute force attempts performed by an attacker?
Which of the following standards is used in wireless local area networks (WLANs)?
Which of the following wireless security standards supported by Windows Vista provides the highest level of security?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The description of the tool is as follows:
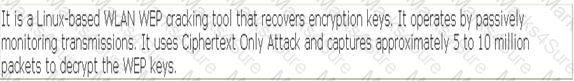
Which of the following tools is John using to crack the wireless encryption keys?
Which of the following penetration testing phases involves gathering data from whois, DNS, and network scanning, which helps in mapping a target network and provides valuable information regarding the operating system and applications running on the systems?
John, a novice web user, makes a new E-mail account and keeps his password as " apple " , his favorite fruit. John ' s password is vulnerable to which of the following password cracking attacks?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following types of Penetration testing provides the testers with complete knowledge of the infrastructure to be tested?
Which of the following tools is used for vulnerability scanning and calls Hydra to launch a dictionary attack?
Which of the following tools can be used to perform Windows password cracking, Windows enumeration, and VoIP session sniffing?
Which of the following describe the benefits to a pass-the-hash attack over traditional password cracking?
You are using the Nmap Scripting Engine and want detailed output of the script as it runs. Which option do you include in the command string?
As pan or a penetration lest, your team is tasked with discovering vulnerabilities that could be exploited from an inside threat vector. Which of the following activities fall within that scope?
Network mapping provides a security testing team with a blueprint of the organization. Which of the following steps is NOT a part of manual network mapping?
Which of the following statements are true about session hijacking?
Each correct answer represents a complete solution. Choose all that apply.
In which of the following scanning methods does an attacker send SYN packets and then a RST packet?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He successfully performs a brute force attack on the We-are-secure server. Now, he suggests some countermeasures to avoid such brute force attacks on the We-aresecure server. Which of the following are countermeasures against a brute force attack?
Each correct answer represents a complete solution. Choose all that apply.
Victor wants to use Wireless Zero Configuration (WZC) to establish a wireless network connection using his computer running on Windows XP operating system. Which of the following are the most likely threats to his computer?
Each correct answer represents a complete solution. Choose two.
Analyze the command output below. Given this information, which is the appropriate next step for the tester?
Starting Nmap4.53 (hnp://insecure.org I at2010-09-30 19:13 EDT interesting ports on 192.163.116.101:
PORT STATE SERVICE
130/tcp filtered cisco-fna
131/tcp filtered cisco-tna
132/tcp filtered cisco-sys
133/tcp filtered statsrv
134/tcp filtered Ingres-net
135/tcp filtered msrpc
136/tcp filtered profile
137/tcp filtered netbios-ns
138/tcp filtered netbios-dgm
139/tcp open netbios-ssn
140/tcp filtered emfis-data
MAC Address: 00:30:1 & :B8:14:8B (Shuttle)
warning: OSS can results may be unreliable because we could not find at least l open and l
closed port
Device type, general purpose
Running: Microsoft Windows XP
OS details: Microsoft Windows XP SP2
Network Distance : 1 hop
Nmap done: I IP address (I host up) scanned in l .263 seconds
When sniffing wireless frames, the interface mode plays a key role in successfully collecting traffic. Which of the mode or modes are best used for sniffing wireless traffic?
Fill in the blank with the appropriate word.
____is a port scanner that can also be used for the OS detection.
Which type of Cross-Sire Scripting (XSS > vulnerability is hardest for automated testing tools to detect, and for what reason?
A client has asked for a vulnerability scan on an internal network that does not have internet access. The rules of engagement prohibits any outside connection for the Nessus scanning machine. The customer has asked you to scan for a new critical vulnerability, which was released after the testing started, winch of the following methods of updating the Nessus plugins does not violate the rules of engagement?
Where are Netcat ' s own network activity messages, such as when a connection occurs, sent?
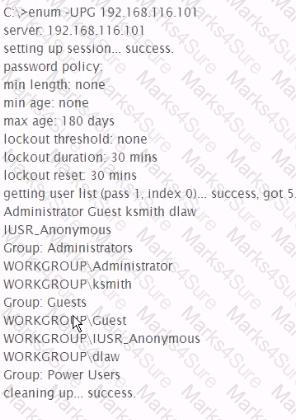
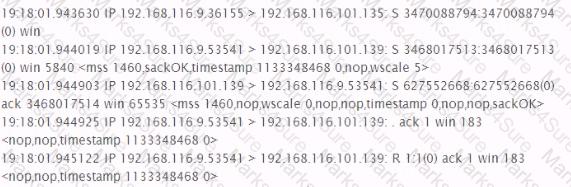
Analyze the command output below, what action is being performed by the tester?
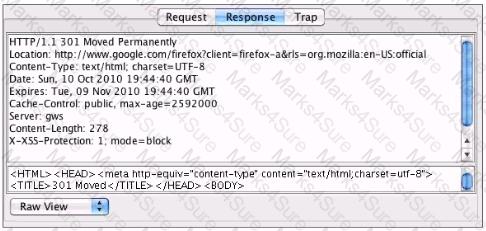
You ' ve been asked to test a non-transparent proxy lo make sure it is working. After confirming the browser is correctly pointed at the proxy, you try to browse a web site. The browser indicates it is " loading " but never displays any part the page. Checking the proxy, you see a valid request in the proxy from your browser. Checking the response to the proxy, you see the results displayed in the accompanying screenshot. Which of the following answers is the most likely reason the browser hasn ' t displayed the page yet?
What section of the penetration test or ethical hacking engagement final report is used to detail and prioritize the results of your testing?
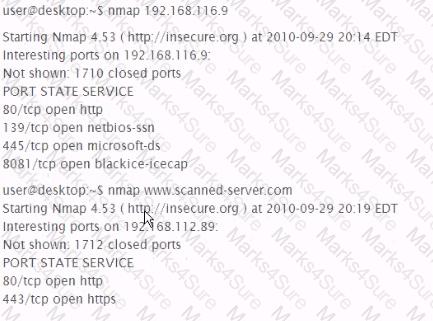
192.168.116.9 Is an IP address forvvww.scanned-server.com. Why are the results from the two scans, shown below, different?
Which of the following is a method of gathering user names from a Linux system?
Analyze the excerpt from a packet capture between the hosts 192.168.116.9 and 192.168.116.101. What factual conclusion can the tester draw from this output?
What command will correctly reformat the Unix passwordcopy and shadowcopy Tiles for input to John The Ripper?
Which of the following is a WEP weakness that makes it easy to Inject arbitrary clear text packets onto a WEP network?
Which of the following is possible in some SQL injection vulnerabilities on certain types of databases that affects the underlying server OS?
You successfully compromise a target system ' s web application using blind command injection. The command you injected is ping-n 1 192.168.1.200. Assuming your machine is 192.168.1 200, which of the following would you see?
A client with 7200 employees in 14 cities (all connected via high speed WAN connections) has suffered a major external security breach via a desktop which cost them more than SI 72.000 and the loss of a high profile client. They ask you to perform a desktop vulnerability assessment to identify everything that needs to be patched. Using Nessus you find tens of thousands of vulnerabilities that need to be patched. In the report you find workstations running several Windows OS versions and service pack levels, anti-virus software from multiple vendors several major browser versions and different versions of Acrobat Reader. Which of the following recommendations should you provide with the report?
You are conducting a penetration test for a private company located in Canada. The scope extends to all internal-facing hosts controlled by the company. You have gathered necessary hold-harmless and non-disclosure agreements. Which action by your group can incur criminal liability under Criminal Code of Canada Sections 184 and 542 CC 184?
You have forgotten your password of an online shop. The web application of that online shop asks you to enter your email so that they can send you a new password. You enter your email you@gmail.com ' and press the submit button. The Web application displays the server error.
What can be the reason of the error?
You have gained shell on a Windows host and want to find other machines to pivot to, but the rules of engagement state that you can only use tools that are already available. How could you find other machines on the target network?
You suspect that system administrators In one part of the target organization are turning off their systems during the times when penetration tests are scheduled, what feature could you add to the ' Rules of engagement ' that could help your team test that part of the target organization?
While reviewing traffic from a tcpdump capture, you notice the following commands being sent from a remote system to one of your web servers:
C:\ > sc winternet.host.com create ncservicebinpath- " c:\tools\ncexe -I -p 2222 -e cmd.exe "
C:\ > sc vJnternet.host.com query ncservice.
What is the intent of the commands?
When attempting to crack a password using Rainbow Tables, what is the output of the reduction function?
What is the impact on pre-calculated Rainbow Tables of adding multiple salts to a set of passwords?
You have been contracted to map me network and try to compromise the servers for a client. Which of the following would be an example of scope creep ' with respect to this penetration testing project?
You want to create a binary log file using tcpdump. Which of the following commands will you use?
Adam works as a professional Computer Hacking Forensic Investigator. He works with the local police. A project has been assigned to him to investigate an iPod, which was seized from a student of the high school. It is suspected that the explicit child pornography contents are stored in the iPod. Adam wants to investigate the iPod extensively. Which of the following operating systems will Adam use to carry out his investigations in more extensive and elaborate manner?
John works as a Professional Penetration Tester. He has been assigned a project to test the Website security of www.we-are-secure Inc. On the We-are-secure Website login page, he enters = ' or ' ' = ' as a username and successfully logs on to the user page of the Web site. Now, John asks the we-are-secure Inc. to improve the login page PHP script. Which of the following suggestions can John give to improve the security of the we-are-secure Website login page from the SQL injection attack?
What happens when you scan a broadcast IP address of a network?
Each correct answer represents a complete solution. Choose all that apply.
What happens when you scan a broadcast IP address of a network?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following attacks allows an attacker to sniff data frames on a local area network (LAN) or stop the traffic altogether?
Peter, a malicious hacker, obtains e-mail addresses by harvesting them from postings, blogs, DNS listings, and Web pages. He then sends large number of unsolicited commercial e-mail (UCE) messages on these addresses. Which of the following e-mail crimes is Peter committing?
John works as a Professional Penetration Tester. He has been assigned a project to test the Website security of www.we-are-secure Inc. On the We-are-secure Website login page, he enters= ' or ' ' = ' as a username and successfully logs on to the user page of the Web site. Now, John asks the we-are-secure Inc. to improve the login page PHP script. Which of the following suggestions can John give to improve the security of the we-are-secure Website login page from the SQL injection attack?
Which of the following Web attacks is performed by manipulating codes of programming languages such as SQL, Perl, Java present in the Web pages?
ACME corporation has decided to setup wireless (IEEE 802.11) network in it ' s sales branch at Tokyo and found that channels 1, 6, 9,11 are in use by the neighboring offices. Which is the best channel they can use?
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com network. Now, when you have finished your penetration testing, you find that the weare- secure.com server is highly vulnerable to SNMP enumeration. You advise the we-are-secure Inc. to turn off SNMP; however, this is not possible as the company is using various SNMP services on its remote nodes. What other step can you suggest to remove SNMP vulnerability?
Each correct answer represents a complete solution. Choose two.
LM hash is one of the password schemes that Microsoft LAN Manager and Microsoft Windows versions prior to the Windows Vista use to store user passwords that are less than 15 characters long. If you provide a password seven characters or less, the second half of the LM hash is always
__________.
Every network device contains a unique built in Media Access Control (MAC) address, which is used to identify the authentic device to limit the network access. Which of the following addresses is a valid MAC address?
You work as a Network Security Analyzer. You got a suspicious email while working on a forensic project. Now, you want to know the IP address of the sender so that you can analyze various information such as the actual location, domain information, operating system being used, contact information, etc. of the email sender with the help of various tools and resources. You also want to check whether this email is fake or real. You know that analysis of email headers is a good starting point in such cases. The email header of the suspicious email is given below:

What is the IP address of the sender of this email?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. On the We-are-secure login page, he enters = ' or ' ' = ' as a username and successfully logs in to the user page of the Web site. The We-are-secure login page is vulnerable to a __________.
Which of the following tools allow you to perform HTTP tunneling?
Each correct answer represents a complete solution. Choose all that apply.
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He enters the following command on the
Linux terminal:chmod 741 secure.c
Considering the above scenario, which of the following statements are true?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tools uses exploits to break into remote operating systems?
You have received a file named new.com in your email as an attachment. When you execute this file in your laptop, you get the following message:
' EICAR-STANDARD-ANTIVIRUS-TEST-FILE! '
When you open the file in Notepad, you get the following string:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
What step will you take as a countermeasure against this attack?
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com Web site. For this, you want to perform the idle scan so that you can get the ports open in the we-are-secure.com server. You are using Hping tool to perform the idle scan by using a zombie computer. While scanning, you notice that every IPID is being incremented on every query, regardless whether the ports are open or close. Sometimes, IPID is being incremented by more than one value. What may be the reason?
Which of the following standards is used in wireless local area networks (WLANs)?
Which protocol would need to be available on a target in order for Nmap to identify services like IMAPS and POP3S?
Which of the following tools can be used as a Linux vulnerability scanner that is capable of identifying operating systems and network services?
Each correct answer represents a complete solution. Choose all that apply.
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He performs Web vulnerability scanning on the We-are-secure server.
The output of the scanning test is as follows:
C:\whisker.pl -h target_IP_address
-- whisker / v1.4.0 / rain forest puppy / www.wiretrip.net -- = - = - = - = - =
= Host: target_IP_address
= Server: Apache/1.3.12 (Win32) ApacheJServ/1.1
mod_ssl/2.6.4 OpenSSL/0.9.5a mod_perl/1.22
+ 200 OK: HEAD /cgi-bin/printenv
John recognizes /cgi-bin/printenv vulnerability ( ' Printenv ' vulnerability) in the We_are_secure server. Which of the following statements about ' Printenv ' vulnerability are true?
Each correct answer represents a complete solution. Choose all that apply.
You want to scan your network quickly to detect live hosts by using ICMP ECHO Requests. What type of scanning will you perform to accomplish the task?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using the Linux operating system. He wants to use a wireless sniffer to sniff the We-are-secure network. Which of the following tools will he use to accomplish his task?
Fill in the blank with the appropriate act name.
The___ act gives consumers the right to ask emailers to stop spamming them.
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. Rick, your assistant, is configuring some laptops for wireless access. For security, WEP needs to be configured for wireless communication. By mistake, Rick configures different WEP keys in a laptop than that is configured on the Wireless Access Point (WAP). Which of the following statements is true in such situation?
Which of the following vulnerability scanner scans from CGI, IDA, Unicode, and Nimda vulnerabilities?
John works as a Penetration Tester in a security service providing firm named you-are-secure Inc.
Recently, John ' s company has got a project to test the security of a promotional Website
www.missatlanta.com and assigned the pen-testing work to John. When John is performing penetration testing, he inserts the following script in the search box at the company home page:
< script > alert( ' Hi, John ' ) < /script >
After pressing the search button, a pop-up box appears on his screen with the text - " Hi, John. "
Which of the following attacks can be performed on the Web site tested by john while considering the above scenario?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He uses a Windows XP operating system to do this. He enters the following command on the command prompt:
c:\tracert www.we-are-secure.com
However, he receives an incomplete traceroute result. What could be the reasons for getting an incomplete result for the tracert command?
Each correct answer represents a complete solution. Choose all that apply.
You have received a file named new.com in your email as an attachment. When you execute this file in your laptop, you get the following message:
' EICAR-STANDARD-ANTIVIRUS-TEST-FILE! '
When you open the file in Notepad, you get the following string:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
What step will you take as a countermeasure against this attack?
Which of the following password cracking tools can work on the Unix and Linux environment?
Which of the following are the drawbacks of the NTLM Web authentication scheme?
Each correct answer represents a complete solution. Choose all that apply.
The employees of EWS Inc. require remote access to the company ' s Web servers. In order to provide solid wireless security, the company uses EAP-TLS as the authentication protocol. Which of the following statements are true about EAP-TLS?
Each correct answer represents a complete solution. Choose all that apply.
Adam, a malicious hacker, hides a hacking tool from a system administrator of his company by using Alternate Data Streams (ADS) feature. Which of the following statements is true in context with the above scenario?
Which of the following techniques are NOT used to perform active OS fingerprinting?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following can be used as a countermeasure against the SQL injection attack?
Each correct answer represents a complete solution. Choose two.
Which of the following attacks allows an attacker to recover the key in an RC4 encrypted stream from a large number of messages in that stream?
When you conduct the XMAS scanning using Nmap, you find that most of the ports scanned do not give a response. What can be the state of these ports?
You want to perform passive footprinting against we-are-secure Inc. Web server. Which of the following tools will you use?
Which of the following laws or acts, formed in Australia, enforces prohibition against cyber stalking?
GSM uses either A5/1 or A5/2 stream cipher for ensuring over-the-air voice privacy. Which of the following cryptographic attacks can be used to break both ciphers?
You are concerned about attackers simply passing by your office, discovering your wireless network, and getting into your network via the wireless connection. Which of the following are
NOT steps in securing your wireless connection?
Each correct answer represents a complete solution. Choose two.