You are responsible for network security at a defense contractor. You are very concerned about sensitive data not getting out of your network. You have specific concerns about employees or contractors sending out files via FTP, or even spyware sending out data. You have blocked and monitored ports (as many as you can) on your firewall, and of course, run an anti spyware package.
Which of the following is another step you should take in preventing sensitive data from being sent out of your network without authorization?
Adam works as a Professional Penetration Tester for Umbrella Inc. A project has been assigned to him to carry out a Black Box penetration testing as a regular evaluation of the system security and integrity of the company ' s network. Which of the following statements are true about the Black Box penetration testing?
Each correct answer represents a complete solution. Choose all that apply.
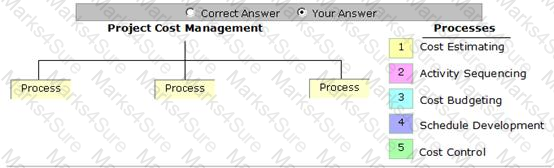
Place the processes that are grouped under the Project Cost Management Knowledge Area in the image below.

Which of the following can be used as a countermeasure against the SQL injection attack?
Each correct answer represents a complete solution. Choose two.
Which of the following contract types is described in the statement below?
" This contract type provides no incentive for the contractor to control costs and hence is rarely utilized. "
Wired Equivalent Privacy (WEP) is a security protocol for wireless local area networks (WLANs). It has two components, authentication and encryption. It provides security equivalent to wired networks for wireless networks. WEP encrypts data on a wireless network by using a fixed secret key. Which of the following statements are true about WEP?
Each correct answer represents a complete solution. Choose all that apply.
All of the following are the password cracking attacks performed by the cain tool except for which one?
In which of the following does a Web site store information such as user preferences to provide customized services to users?
John is a malicious attacker. He illegally accesses the server of We-are-secure Inc. He then places a backdoor in the We-are-secure server and alters its log files. Which of the following steps of malicious hacking includes altering the server log files?
David works as a Network Administrator for NetTech Inc. The company has a Windows Server 2008 domain-based network. The network has a print server with two hard disks as basic disks, and 120 Windows XP Professional client computers. Users complain that printing is slow. To improve the printing performance, David wants to create a dynamic volume. Which of the following dynamic volumes will he create to enhance the performance?
Which of the following functions can you use to mitigate a command injection attack?
Each correct answer represents a complete solution. Choose all that apply.
John works as a network security officer in Gentech Inc. The company uses a TCP/IP network. While working on the network, a problem occurs related to the DNS resolution. Which of the following utilities can he use to diagnose the problem?
Which function of incident handling involves in-depth investigation of the incident report or incident activity to establish the priority and threat of the incident?
Every network device contains a unique built in Media Access Control (MAC) address, which is used to identify the authentic device to limit the network access. Which of the following addresses is a valid MAC address?
Rick works as the Network Administrator of a Windows 2000 network. The network consists of 30 domain controllers, 65 member servers, and 5000 workstations. All the computers on the network use Windows 2000 Advanced Server, Windows 2000 Server, and Windows 2000 Professional operating systems. The Windows 2000 Advanced Server computers are running the Cluster Service. The network uses TCP/IP as its only protocol. Once a week Rick works from home. But rest of the weekdays, he has to travel. Rick wants to be able to remotely administer each Windows 2000 server on his network with the following considerations:
• He must be able to establish a VPN connection to the Windows 2000 Server computers on the network from his home, so that the data remain encrypted and encapsulated during data transfer.
• While traveling , he must be able to connect to the network from a laptop computer via remote access connection, so that he can perform any task on the main Windows 2000 domain controller.
• While traveling, he must be able to edit the registry of the Windows 2000 Server computer.
• During the migration process to Windows 2000, he depleted all the financial resources for licensing. Therefore, he must not be required to add additional licenses to the network.
Rick takes the following actions:
• He implements the VPN connection on the proper server, the laptop computer, and the home computer.
• He configures the VPN connection to use the IPSec protocol in Encapsulating Security Payload (ESP) Tunnel Mode.
• He implements Windows 2000 Terminal Services using the Remote Administration mode on the Windows 2000 servers.
• He installs and configures Routing and Remote Access properly.
Which of the following goals will be accomplished by these actions?
Each correct answer represents a complete solution. Choose all that apply.
John works as an IT Technician for PassGuide Inc. One morning, John receives an e-mail from the company ' s Manager asking him to provide his logon ID and password, but the company policy restricts users from disclosing their logon IDs and passwords. Which type of possible attack is this?
Which of the following programs collects email addresses of users and creates a mailing list?
Which of the following statements about Digest authentication are true?
Each correct answer represents a complete solution. Choose two.
Which of the following statements are true about WPA?
Each correct answer represents a complete solution. Choose all that apply.
You discover that all available network bandwidth is being used by some unknown service. You discover that UDP packets are being used to connect the echo service on one machine to the chargen service on another machine. What kind of attack is this?
You are a project manager who is completing a project for another organization. The project you are managing will have phased deliverables throughout the project. Stakeholders are required to complete scope validation at the end of each phase so that the project can move forward. Your payment requests will also be attached to the approval of each phase so it is important to you, on several levels, that the stakeholders participate in scope validation as soon as they are requested. You have documented the process for reviewing the product acceptance criteria with the stakeholders.
What project document details the product acceptance criteria in all the projects?
An executive in your company reports odd behavior on her PDA. After investigation you discover that a trusted device is actually copying data off the PDA. The executive tells you that the behavior started shortly after accepting an e-business card from an unknown person. What type of attack is this?
Which of the following is a cryptographic approach employed by many cryptographic algorithms and cryptosystems?
Which of the following statements about Digest authentication are true?
Each correct answer represents a complete solution. Choose two.
In which type of person-to-person attack does an attacker pretend to be someone else?
Which of the following is a computer file used in an operating system to map hostnames to IP addresses?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He finds that the We-are-secure server is vulnerable to attacks. As a countermeasure, he suggests that the Network Administrator should remove the IPP printing capability from the server. He is suggesting this as a countermeasure against __________.
Which of the following types of attacks occurs when an attacker successfully inserts an intermediary software or program between two communicating hosts?
This type of virus infects programs that can execute and load into memory to perform predefined steps for infecting systems. It infects files with the extensions .EXE, .COM, .BIN, and .SYS. As it can replicate or destroy these types of files, the operating system becomes corrupted and needs reinstallation. This type of virus is known as __________.
Which of the following is a process of monitoring data packets that travel across a network?
You work as a technician for Secure Net Inc. You receive an e-mail from your software vendor.
The e-mail contains information about a critical fix that needs to be installed on your computer. It further states that if this patch is not installed right away, your system will crash and you will lose all your data. Now they require your maintenance account password.
Which of the following types of security attacks do you think it is?
Which of the following statements about Public Key Infrastructure (PKI) are true?
Each correct answer represents a complete solution. Choose two.
Mark works as a Network Administrator for BlueWell Inc. While surfing the Internet, he enters a URL http://www.ciw.com/web/learning in the Web browser. A Web page appears after entering the URL. Which of the following protocols can be used to resolve www.ciw.com into the correct IP address?
Which of the following statements are true about worms?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following exists between the client and the server system to provide security and allows customized NAT traversal filters to be plugged into the gateway to support address and port translation for certain application layer protocols?
Roberta is the project manager of the KJL Project for her company. She is creating a chart that will help categorize the problems discovered during the quality control inspection process. She wants to create a chart where she can categorize the number of instances of problems and rank the problems based on frequency. Which chart should Roberta create?
You are responsible for security on your network. One particular concern is the theft of sensitive data. You want to make sure that end users do not (purposefully or accidentally) take data off the premises. Which of the following should you be concerned about?
Each correct answer represents a complete solution. Choose all that apply.
In which of the following attacks does an attacker create the IP packets with a forged (spoofed) source IP address with the purpose of concealing the identity of the sender or impersonating another computing system?
The Klez worm is a mass-mailing worm that exploits a vulnerability to open an executable attachment even in Microsoft Outlook ' s preview pane. The Klez worm gathers email addresses from the entries of the default Windows Address Book (WAB). Which of the following registry values can be used to identify this worm?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He successfully performs a brute force attack on the We-are-secure server.
Now, he suggests some countermeasures to avoid such brute force attacks on the We-are-secure server. Which of the following are countermeasures against a brute force attack?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following generates MD5 hashes to check the MD5 value for each file processed and compares it with other MD5 strings?
Which of the following is a method of defeating a cryptographic scheme by trying a large number of possibilities?
Which of the following is a read-only copy of a zone and obtains its resource records from other name servers?
Which of the following viruses infects Word 97 documents and the NORMAL.DOT file of Word 97 and Word 2000?
Which of the following is a type of encryption that uses a single key to encrypt and decrypt data?
You are concerned about attackers simply passing by your office, discovering your wireless network, and getting into your network via the wireless connection. Which of the following are NOT steps in securing your wireless connection?
Each correct answer represents a complete solution. Choose two.
Which of the following malware spread through the Internet and caused a large DoS attack in
1988?
Which of the following algorithms can be used to check the integrity of a file?
Each correct answer represents a complete solution. Choose two.
Which of the following wireless standards has a transmission speed of up to 720 Kbps?
Victor works as a network administrator for DataSecu Inc. He uses a dual firewall Demilitarized Zone (DMZ) to insulate the rest of the network from the portions that is available to the Internet. Which of the following security threats may occur if DMZ protocol attacks are performed?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following authentication methods is used to enable a Web browser to provide credentials when making a request during an HTTP transaction?
You work as an Incident handling manager for a company. The public relations process of the company includes an event that responds to the e-mails queries. But since few days, it is identified that this process is providing a way to spammers to perform different types of e-mail attacks. Which of the following phases of the Incident handling process will now be involved in resolving this process and find a solution?
Each correct answer represents a part of the solution. Choose all that apply.
Andrew works as a Software Developer for Mansoft Inc. The company ' s network has a Web server that hosts the company ' s Web site. Andrew wants to enhance the security of the Web site by implementing Secure Sockets Layer (SSL). Which of the following types of encryption does SSL use?
Each correct answer represents a complete solution. Choose two.
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.weare-secure.com. He enters a single quote in the input field of the login page of the We-are- secure Web site and receives the following error message:
Microsoft OLE DB Provider for ODBC Drivers error ' 0x80040E14 '
This error message shows that the We-are-secure Website is vulnerable to __________.
Which of the following are the automated tools that are used to perform penetration testing?
Each correct answer represents a complete solution. Choose two.
Rick is the project manager for TTM project. He is in the process of procuring services from vendors. He makes a contract with a vendor in which he precisely specify the services to be procured, and any changes to the procurement specification will increase the costs to the buyer. Which type of contract is this?
Which of the following intrusion detection systems (IDS) monitors network traffic and compares it against an established baseline?
Which of the following statements about a certification authority (CA) is true?
You have inserted a Trojan on your friend ' s computer and you want to put it in the startup so that whenever the computer reboots the Trojan will start to run on the startup. Which of the following registry entries will you edit to accomplish the task?
Your company network has been infected with a virus. You have cleaned all PCs, workstations, and servers. However your network still keeps getting re-infected with the same virus. Which of the following could NOT be a cause for this?
Each correct answer represents a complete solution. Choose two.
Maria works as a Network Security Officer for Gentech Inc. She wants to encrypt her network traffic. The specific requirement for the encryption algorithm is that it must be a symmetric key block cipher.
Which of the following techniques will she use to fulfill this requirement?
You are the project manager of the NJJ project. Your enterprise environmental factors require that you establish certain risk management rules regarding low risks within your project. What is the best policy for risks with low probability and low impact in the project management?
Which of the following penetration testing phases involves reconnaissance or data gathering?
Which of the following are types of access control attacks?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following attacks does Management Frame Protection help to mitigate?
Each correct answer represents a complete solution. Choose two.
These are false reports about non-existent viruses. In these reports, the writer often claims to do impossible things. Due to these false reports, the network administrator shuts down his network, which in turn affects the work of the company. These reports falsely claim to describe an extremely dangerous virus, and declare that the report is issued by a reputed company. These reports are known as __________.
Which of the following DNS servers provides fault tolerance, load distribution, and easier remote name resolution for the primary DNS server?
Which key of the Asymmetric encryption is used to encrypt the data when a user sends a message or data to another user?
A helpdesk technician received a phone call from an administrator at a remote branch office. The administrator claimed to have forgotten the password for the root account on UNIX servers and asked for it. Although the technician didn ' t know any administrator at the branch office, the guy sounded really friendly and since he knew the root password himself, he supplied the caller with the password.
What type of attack has just occurred?
Which of the following terms related to risk management represents the estimated frequency at which a threat is expected to occur?
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Active Directory-based single domain single forest network. The company ' s network is connected to the Internet through a T1 line. The firewall is configured on the network for securing the internal network from the intruders on the Internet. The functional level of the forest is Windows Server 2008. You are designing a public key infrastructure (PKI) for the network. The network will use a root enterprise certificate authority (CA) and a subordinate CA. The root CA will be used to issue certificates to the subordinate CA, and the subordinate CA will be used to issue certificates to the clients.
The management of the company wants to ensure that the security of high-level CAs is not compromised. Which of the following steps will you take to accomplish the task?
Maria works as a Risk Analysis Manager for Gentech Inc. She starts a new IT project. Which of the following phases of her project development process is most suitable for including risk analysis?
Which of the following security protocols can be used to support MS-CHAPv2 for wireless client authentication?
Each correct answer represents a complete solution. Choose two.
In which of the following social engineering attacks does an attacker first damage any part of the target ' s equipment and then advertise himself as an authorized person who can help fix the problem.
Which of the following technologies is used to detect unauthorized attempts to access and manipulate computer systems locally or through the Internet or an intranet?
In which of the following does a project manager assign certain points towards various categories to judge the vendors?
Victor wants to use Wireless Zero Configuration (WZC) to establish a wireless network connection using his computer running on Windows XP operating system. Which of the following are the most likely threats to his computer?
Each correct answer represents a complete solution. Choose two.
Which of the following port numbers is used by the LDAP protocol when it is secured?
Which of the following attacks can be performed by Brutus for cracking a password?
Each correct answer represents a complete solution. Choose two.
All of the following are the outputs of the Acquire Project Team process except for which one?
Which of the following are symptoms of a virus attack on your computer?
Each correct answer represents a complete solution. Choose two.
An IPS sensor triggers an alarm known as " signature firing " . What events may occur in response?
Each correct answer represents a complete solution. Choose all that apply.
All of the following steps should be taken to prevent a Web server from IIS buffer overflow attacks except for which one?
Which of the following protocols uses a combination of public key and symmetric encryption to provide communication privacy, authentication, and message integrity for secure browsing on the Internet?
Which of the following protocols is used as a transport protocol for Internet dial-up connections?
A user has opened a Web site that automatically starts downloading malicious code onto his computer. What should he do to prevent this?
Each correct answer represents a complete solution. Choose two.
You work as a Network Administrator for Tech Perfect Inc. The company has a Linux-based network. You have configured a VPN server for remote users to connect to the company ' s network. Which of the following encryption types will Linux use?
Which of the following are countermeasures to prevent unauthorized database access attacks?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for NetTech Inc. You want to have secure communication on the company ' s intranet. You decide to use public key and private key pairs. What will you implement to accomplish this?
You have been asked to create a project charter for a new database project. Management has stressed that in order to effectively create a project charter, you ' ll first need to understand all of the following except for which one?
Fill in the blank with the appropriate word.
________ is also used to refer to any attempt to circumvent the security of other types of cryptographic algorithms and protocols in general, and not just encryption.
Which of the following standards is used in wireless local area networks (WLANs)?
Rick, the Network Administrator of the Fimbry Hardware Inc., wants to design the initial test model for Internet Access. He wants to fulfill the following goals:
No external traffic should be allowed into the network.
Administrators should be able to restrict the websites which can be accessed by the internal users.
Which of the following technologies should he use to accomplish the above goals? (Click the Exhibit button on the toolbar to see the case study.)
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.weare-secure.com. He installs a rootkit on the Linux server of the We-are-secure network. Which of the following statements are true about rootkits?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following options is an approach to restricting system access to authorized users?
Which of the following applications would be considered a data warehousing application?
Which of the following are the countermeasures against WEP cracking?
Each correct answer represents a part of the solution. Choose all that apply.
You and your project team are just starting the risk identification activities for a project that is scheduled to last for 18 months. Your project team has already identified a long list of risks that need to be analyzed. How often should you and the project team do risk identification?
Which of the following tools monitors the radio spectrum for the presence of unauthorized, rogue access points and the use of wireless attack tools?
Which of the following is a virus that can redirect the disk head to read another sector instead of the one in which it resides?
You are responsible for security at a company that specializes in e-commerce. You realize that given the high volume of Web traffic, there is a significant chance of someone being able to breach your perimeter. You want to make sure that should this occur, you can redirect the attacker away from sensitive data. How would you best accomplish this?
You work as a project manager for TYU project. You are planning for risk mitigation. You need to identify the risks that will need a more in-depth analysis. Which of the following activities will help you in this?
You are the project manager for the TTR project. You are in the process of gathering information for risk identification. You ask experts to participate in the process through their emails for maintaining anonymity. You collect the responses, summarize them, and are then re-circulated to the experts for further comment. Which of the following techniques are you using for risk identification?
The Project Procurement Management knowledge area focuses on which of the following processes?
Each correct answer represents a complete solution. Choose two.
Which of the following statements are true about MS-CHAPv2?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following types of cryptography algorithms is a symmetric key cipher which operates on fixed-length groups of bits, termed blocks, with an unvarying transformation?
Which of the following tools can be used for stress testing of a Web server?
Each correct answer represents a complete solution. Choose two.
Which of the following tools is based on Linux and used to carry out the Penetration Testing?
Which of the following processes is described in the statement below?
" It is a process of developing an approximation of the costs of the resources needed to complete project activities. "
Which of the following password authentication schemes enables a user with a domain account to log on to a network once, using a password or smart card, and to gain access to multiple computers in the domain without being prompted to log in again?
An intruder is trying to get user passwords by pretending to be help desk staff. Which of the following types of security attacks do you think it is?
Which of the following statements is true about the difference between worms and Trojan horses?
Which of the following cryptographic system services ensures that information will not be disclosed to any unauthorized person on a local network?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He wants to use Kismet as a wireless sniffer to sniff the We-are-secure network. Which of the following IEEE-based traffic can be sniffed with Kismet?
Each correct answer represents a complete solution. Choose all that apply.
You are taking over the security of an existing network. You discover a machine that is not being used as such, but has software on it that emulates the activity of a sensitive database server. What is this?
Mark works as a Network Administrator for Perfect Inc. The company has both wired and wireless networks. An attacker attempts to keep legitimate users from accessing services that they require. Mark uses IDS/IPS sensors on the wired network to mitigate the attack. Which of the following attacks best describes the attacker ' s intentions?
Which of the following is a complete indexed set of records of the procurement process incorporated into the administrative closure process?
You want to use PGP files for steganography. Which of the following tools will you use to accomplish the task?
Victor works as a professional Ethical Hacker for SecureEnet Inc. He has been assigned a job to test an image, in which some secret information is hidden, using Steganography. Victor performs the following techniques to accomplish the task:
1. Smoothening and decreasing contrast by averaging the pixels of the area where significant color transitions occurs.
2. Reducing noise by adjusting color and averaging pixel value.
3. Sharpening, Rotating, Resampling, and Softening the image.
Which of the following Steganography attacks is Victor using?
An attacker makes an attempt against a Web server. The result is that the attack takes the form of URLs. These URLs search for a certain string that identifies an attack against the Web server. Which IDS/IPS detection method do the URLs use to detect and prevent an attack?
You are implementing wireless access at a defense contractor. Specifications say, you must implement the AES Encryption algorithm. Which encryption standard should you choose?
Olive is the program manager for her organization. She has created a request for proposal for a large portion of her program. In this work to be procured she has set several requirements for the vendors to participate. The chief among these requirements is a vendor must have at least four licensed electricians in his team. This requirement for four licensed electricians is an example of which one of the following terms?
Which interface does an IPS sensor use to communicate with a security appliance for management purposes?
John visits an online shop that stores the IDs and prices of the items to buy in a cookie. After selecting the items that he wants to buy, the attacker changes the price of the item to 1.
Original cookie values:
ItemID1=2
ItemPrice1=900
ItemID2=1
ItemPrice2=200
Modified cookie values:
ItemID1=2
ItemPrice1=1
ItemID2=1
ItemPrice2=1
Now, he clicks the Buy button, and the prices are sent to the server that calculates the total price.
Which of the following hacking techniques is John performing?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The description of the tool is as follows:
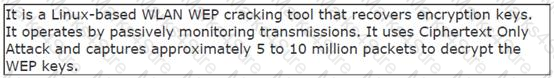
Which of the following tools is John using to crack the wireless encryption keys?
Which of the following statements about a host-based intrusion prevention system (HIPS) are true?
Each correct answer represents a complete solution. Choose two.
Which of the following evidences are the collection of facts that, when considered together, can be used to infer a conclusion about the malicious activity/person?
Which of the following processes is described in the statement below?
" It is the process of implementing risk response plans, tracking identified risks, monitoring residual risk, identifying new risks, and evaluating risk process effectiveness throughout the project. "
You work as a Network Administrator for Infonet Inc. The company has a Windows Server 2008 domain-based network. The network has three Windows Server 2008 member servers and 150 Windows Vista client computers. The network contains a Windows Server 2008 Core computer named SERVER1 with NTFS file system. SERVER1 has a 802.11 wireless LAN adapter. The Wireless LAN Service is installed on SERVER1. You want to know about the 802.11 wireless LAN interface information, network information, and wireless settings on the system on SERVER1.
Which of the following commands will you use to accomplish the task?
You work as a Network Administrator for Net World Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. A Public Key Infrastructure (PKI) is installed on a server in the domain. You are planning to go on vacation for two weeks. Your team has three assistant administrators. You are required to accomplish the following tasks:
• Delegate the authority to the assistant administrators to issue, approve, and revoke certificates.
• The solution must involve least administrative burden.
Which of the following steps will you take to accomplish the tasks?
Donna is the project manager for her organization. She is preparing a plan to manage changes to the project should changes be requested. Her change management plan defines the process for documenting, tracking, and determining if the changes should be approved or declined. What system is considered the parent of the change control system documented in Donna ' s plan?
Which of the following are the benefits of information classification for an organization?
Each correct answer represents a complete solution. Choose two.
You have been hired as a project manager for a project. The initial project planning predicts a benefitcost ratio ( BCR ) of the project as 3.5. What does this figure mean?
What course of action can be taken by a party if the current negotiations fail and an agreement cannot be reached?
Which of the following types of security will be the cause of concern if the server has been stolen from the organization ' s premises?
You work as a Network Administrator for Net World International. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. All client computers on the network run Windows XP Professional.
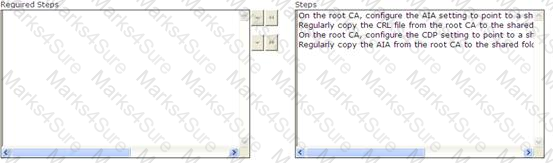
You configure a public key infrastructure ( PKI ) on the network. You configure a root CA and a subordinate CA on the network. For security reasons, you want to take the root CA offline. You are required to configure the CA servers to support for certificate revocation. Choose the steps you will require to accomplish the task.
You work as a project manager for an IT project. You are analyzing activity sequences, durations, resource requirements, and schedule constraints to create the project schedule. In which of the following Knowledge Areas are you working on?
Which of the following protocols is used for destination and error reporting functions in datagram processing?
Ryan wants to create an ad hoc wireless network so that he can share some important files with another employee of his company. Which of the following wireless security protocols should he choose for setting up an ad hoc wireless network?
Each correct answer represents a part of the solution. Choose two.
Which type of virus is able to alter its own code to avoid being detected by anti-virus software?
You are the Network Administrator for a company that frequently exchanges confidential emails without outside parties (clients, vendors, etc.). You want those emails to be encrypted; however, you want the least difficulty in the encryption process. Which of the following should you choose?
In which of the following Person-to-Person social engineering attacks does an attacker pretend to be an outside contractor, delivery person, etc., in order to gain physical access to the organization?
Which of the following is responsible for maintaining certificates in a public key infrastructure (PKI)?
Which model is a software development process combining elements of both design and prototyping-in-stages, in an effort to combine advantages of top-down and bottom-up concepts?
Managerial wisdom is the combination of knowledge as well as experience. It is the ability of the leaders to understand the members of the team. Which of the following are the characteristics that come under managerial wisdom?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following refers to the process of verifying the identity of a person, network host, or system process?
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. The company ' s headquarters is located at Los Angeles. A branch office of the company is located at Denver. You are about to send a message to Rick who is a Network Administrator at Denver. You want to ensure that the message cannot be read by anyone but the recipient. Which of the following keys will you use to encrypt the message?
You and your project team have identified the project risks and now are analyzing the probability and impact of the risks. What type of analysis of the risks provides a quick and high-level review of each identified risk event?
You work as a Network Administrator for Net Perfect Inc. The company has a Windows Server 2008 network environment. The network is configured as a Windows Active Directory-based single forest network. You have recently added three new SCSI hard disk drives to a domain controller that already has two physical disk drives. The new SCSI disk drives are configured in a RAID-5 array. You are required to enhance the performance of the Active Directory database on the domain controller. Which of the following steps will you take to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
John is a black hat hacker. FBI arrested him while performing some email scams. Under which of the following US laws will john be charged?
Which of the following types of attacks cannot be prevented by technical measures only?