You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to query an image root device and RAM disk size. Which of the following Unix commands can you use to accomplish the task?
Which of the following standards is used in wireless local area networks (WLANs)?
Many organizations create network maps of their network system to visualize the network and understand the relationship between the end devices and the transport layer that provide services. Which of the following are the techniques used for network mapping by large organizations? Each correct answer represents a complete solution. Choose three.
Which of the following are the disadvantages of Dual-Homed Host Firewall Architecture?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. Rick, your assistant, is configuring some laptops for wireless access. For security, WEP needs to be configured for wireless communication. By mistake, Rick configures different WEP keys in a laptop than that is configured on the Wireless Access Point (WAP). Which of the following statements is true in such situation?
You want to change the number of characters displaying on the screen while reading a txt file. However, you do not want to change the format of the txt file. Which of the following commands can be used to view (but not modify) the contents of the text file on the terminal screen at a time?
You have an online video library. You want to upload a directory of movies. Since this process will take several hours, you want to ensure that the process continues even after the terminal is shut down or session is closed. What will you do to accomplish the task?
Which of the following is Microsoft ' s implementation of the file and application server for the Internet and private intranets?
You work as a Network Administrator of a TCP/IP network. You are having DNS resolution problem. Which of the following utilities will you use to diagnose the problem?
You work as a Network Administrator for XYZ CORP. The company has a Linux-based network. The company needs to provide secure network access. You have configured a firewall to prevent certain ports and applications from forwarding the packets to the company ' s intranet. What does a firewall check to prevent these ports and applications from forwarding the packets to the intranet?
You work as the Project Engineer for XYZ CORP. The company has a Unix-based network. Your office consists of one server, seventy client computers, and one print device. You raise a request for printing a confidential page. After 30 minutes, you find that your print request job is not processed and is at the seventh position in the printer queue. You analyze that it shall take another one hour to print. You decide to remove your job from the printer queue and get your page printed outside the office. Which of the following Unix commands can you use to remove your job from the printer queue?
You run the wc -c file1.txt command. If this command displays any error message, you want to store the error message in the error.txt file. Which of the following commands will you use to accomplish the task?
Which of the following attacks allows the bypassing of access control lists on servers or routers, and helps an attacker to hide? (Choose two)
Which of the following are the limitations for the cross site request forgery (CSRF) attack?
Which of the following types of audit constructs a risk profile for existing and new projects?
Which of the following tools is a Windows-based commercial wireless LAN analyzer for IEEE 802.11b and supports all high level protocols such as TCP/IP, NetBEUI, and IPX?
Data mining is a process of sorting through data to identify patterns and establish relationships. Which of the following data mining parameters looks for patterns where one event is connected to another event?
You are tasked with creating an ACL to apply to Fa0/0 based on the following requirements: The ACL must be protocol specific. All traffic from host 10.10.45.2 and subnet 10.10.1.32/27 must be denied access through the router. Telnet and SSH must be denied for ALL hosts except the management host with the IP address of 10.10.0.100. This management host must not only have Telnet and SSH access, but access to any port in the TCP and UDP suite to any destination. HTTP, HTTPS, and DNS requests must be allowed for all hosts on subnets 10.10.2.0/24 and 10.10.3.0/24 to any destination. All remaining traffic must be denied. Cisco IOS applies an implied deny all at the end of an ACL. However, you must provide this configuration manually so that engineers can see hit counts on the deny all traffic when running the show ip access-lists command. Which of the following sets of commands will you choose to complete the configuration on Router A?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He finds that the We-are-secure server is vulnerable to attacks. As a countermeasure, he suggests that the Network Administrator should remove the IPP printing capability from the server. He is suggesting this as a countermeasure against __________.
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to fix partitions on a hard drive. Which of the following Unix commands can you use to accomplish the task?
Which of the following techniques are used after a security breach and are intended to limit the extent of any damage caused by the incident?
You work as a Web Deployer for UcTech Inc. You write the < security constraint > element for an application in which you write the < auth-constraint > sub-element as follows: < auth- constraint > < role-name > * < /role-name > < /auth-constraint > Who will have access to the application?
You work as a Network Administrator for Infonet Inc. The company ' s network has an FTP server. You want to secure the server so that only authorized users can access it. What will you do to accomplish this?
You work as a Network Administrator for NTY Inc. The company has a secure wireless network. While auditing the network for maintaining security, you find an unknown node. You want to locate that node. Which tool will you use to pinpoint the actual physical location of the node?
Web mining allows a user to look for patterns in data through content mining, structure mining, and usage mining. What is the function of structure mining?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. You have configured a firewall on the network. A filter has been applied to block all the ports. You want to enable sending and receiving of emails on the network. Which of the following ports will you open? (Choose two)
You work as a Database Administrator for XYZ CORP. The company has a multi-platform network. The company requires a database that can receive data from various types of operating systems. You want to design a multidimensional database to accomplish the task. Which of the following statements are true about a multidimensional database?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He successfully performs a brute force attack on the We-are-secure server. Now, he suggests some countermeasures to avoid such brute force attacks on the We-are-secure server. Which of the following are countermeasures against a brute force attack?
John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. He executes the following command in the terminal: echo $USER, $UID Which of the following will be displayed as the correct output of the above command?
Which of the following can be the countermeasures to prevent NetBIOS NULL session enumeration in Windows 2000 operating systems?
Which of the following wireless security features provides the best wireless security mechanism?
You check performance logs and note that there has been a recent dramatic increase in the amount of broadcast traffic. What is this most likely to be an indicator of?
Anonymizers are the services that help make a user ' s own Web surfing anonymous. An anonymizer removes all the identifying information from a user ' s computer while the user surfs the Internet. It ensures the privacy of the user in this manner. After the user anonymizes a Web access with an anonymizer prefix, every subsequent link selected is also automatically accessed anonymously. Which of the following are limitations of anonymizers?
You work as a Network Administrator for XYZ CORP. The company has a Linux-based network. You need to configure a firewall for the company. The firewall should be able to keep track of the state of network connections traveling across the network. Which of the following types of firewalls will you configure to accomplish the task?
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to set some terminal characteristics and environment variables. Which of the following Unix configuration files can you use to accomplish the task?
eBox Platform is an open source unified network server (or a Unified Network Platform) for SMEs. In which of the following forms can eBox Platform be used?
Which of the following encryption encoding techniques is used in the basic authentication method?
You work as a Network Administrator for Tech Perfect Inc. For security issues, the company requires you to harden its routers. You therefore write the following code: Router#config terminal Router(config) #no ip bootp server Router(config) #no ip name-server Router(config) #no ntp server Router(config) #no snmp server Router(config) #no ip http server Router(config) #^Z Router# What services will be disabled by using this configuration fragment?
You work as a Network Administrator for BetaTech Inc. You have been assigned the task of designing the firewall policy for the company. Which of the following statements is unacceptable in the ' acceptable use statement ' portion of the firewall policy?
You work as a Network Auditor for XYZ CORP. The company has a Windows-based network. While auditing the company ' s network, you are facing problems in searching the faults and other entities that belong to it. Which of the following risks may occur due to the existence of these problems?
Sarah works as a Web Developer for XYZ CORP. She is creating a Web site for her company. Sarah wants greater control over the appearance and presentation of Web pages. She wants the ability to precisely specify the display attributes and the appearance of elements on the Web pages. How will she accomplish this?
Mark implements a Cisco unified wireless network for Tech Perfect Inc. Which functional area of the Cisco unified wireless network architecture includes intrusion detection and prevention?
You have just installed a Windows 2003 server. What action should you take regarding the default shares?
Which of the following tools works both as an encryption-cracking tool and as a keylogger?
You work as a Java Programmer for JavaSkills Inc. You are working with the Linux operating system. Nowadays, when you start your computer, you notice that your OS is taking more time to boot than usual. You discuss this with your Network Administrator. He suggests that you mail him your Linux bootup report. Which of the following commands will you use to create the Linux bootup report?
Patricia joins XYZ CORP., as a Web Developer. While reviewing the company ' s Web site, she finds that many words including keywords are misspelled. How will this affect the Web site traffic?
You are the project manager of a Web development project. You want to get information about your competitors by hacking into their computers. You and the project team determine should the hacking attack not be performed anonymously, you will be traced. Hence, you hire a professional hacker to work on the project. This is an example of what type of risk response?
Which of the following wireless security standards supported by Windows Vista provides the highest level of security?
Which of the following is a type of web site monitoring that is done using web browser emulation or scripted real web browsers?
Mark works as the Network Administrator for XYZ CORP. The company has a Unix-based network. Mark wants to scan one of the Unix systems to detect security vulnerabilities. To accomplish this, he uses TARA as a system scanner. What can be the reasons that made Mark use TARA?
Which of the following Web attacks is performed by manipulating codes of programming languages such as SQL, Perl, Java present in the Web pages?
You work as a professional Ethical Hacker. You are assigned a project to test the security of www.we-are-secure.com. You are working on the Windows Server 2003 operating system. You suspect that your friend has installed the keyghost keylogger onto your computer. Which of the following countermeasures would you employ in such a situation?
Data access auditing is a surveillance mechanism that watches over access to all sensitive information contained within the database. What are the questions addressed in a perfect data access auditing solution?
You have been assigned a project to develop a Web site for a construction company. You plan to develop a Web site and want to get more control over the appearance and presentation of the Web pages. You also want to increase your ability to precisely specify the position and appearance of the elements on a page and create special effects. You plan to use cascading style sheets (CSS). You want to define styles only for the active page. Which type of style sheet will you use?
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to identify the list of users with special privileges along with the commands that they can execute. Which of the following Unix configuration files can you use to accomplish the task?
The employees of CCN Inc. require remote access to the company ' s proxy servers. In order to provide solid wireless security, the company uses LEAP as the authentication protocol. Which of the following is supported by the LEAP protocol?
Mark works as a Web Developer for XYZ CORP. He is developing a Web site for the company. The Manager of the company requires Mark to use tables instead of frames in the Web site. What is the major advantage that a table-structured Web site has over a frame-structured Web site?
Which of the following functions are performed by methods of the HttpSessionActivationListener interface?
In a network, a data packet is received by a router for transmitting it to another network. For forwarding the packet to the other available networks, the router is configured with a static or a dynamic route. What are the benefits of using a static route?
You have purchased a laptop that runs Windows Vista Home Premium. You want to protect your computer from malicious applications, such as spyware, while connecting to the Internet. You configure Windows Defender on your laptop to schedule scan daily at 2 AM as shown in the image below:
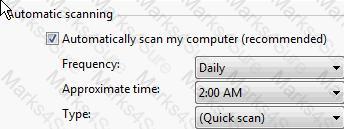
You want Windows Defender to scan the laptop for all the known spyware and other potentially unwanted software, including the latest one. You do not want to manually perform this task. Which of the following actions will you perform to accomplish the task?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The description of the tool is as follows: Which of the following tools is John using to crack the wireless encryption keys?
Which of the following are the drawbacks of the NTLM Web authentication scheme?
You work as a Network Auditor for XYZ CORP. The company has a Windows-based network. You use DumpSec as an auditing and reporting program for security issues. Which of the following statements is true about DumpSec? (Choose three)
You are concerned about rogue wireless access points being connected to your network. What is the best way to detect and prevent these?
Which of the following text editing tools can be used to edit text files without having to open them?
Mark works as a Network Administrator for NetTech Inc. The company has a Windows 2003 Active Directory domain-based network. The domain consists of a domain controller, two Windows 2003 member servers, and one hundred client computers. The company employees use laptops with Windows XP Professional. These laptops are equipped with wireless network cards that are used to connect to access points located in the Marketing department of the company. The company employees log on to the domain by using a user name and password combination. The wireless network has been configured with WEP in addition to 802.1x. Mark wants to provide the best level of security for the kind of authentication used by the company. What will Mark do to accomplish the task?
Which of the following commands can be used to find out where commands are located?
You work as a Software Developer for Mansoft Inc. You create an application and use it to create users as members of the local Users group. Which of the following code snippets imperatively demands that the current user is a member of the local Users group?
You have to ensure that your Cisco Router is only accessible via telnet and ssh from the following hosts and subnets: 10.10.2.103 10.10.0.0/24 Which of the following sets of commands will you use to accomplish the task?
You work as a Network Administrator for Tech Perfect Inc. You need to configure the company firewall so that only Simple Network Management Protocol (SNMP) and Secure HTTP (HTTPS) traffic is allowed into the intranet of the company. No other traffic should be allowed into the intranet. Which of the following rule sets should you use on your firewall to accomplish the task? (Assume left to right equals top to bottom.)
Which of the following commands can be used to intercept and log the Linux kernel messages?
You work as a Web Developer for XYZ CORP. The company has a Windows-based network. You have been assigned the task to secure the website of the company. To accomplish the task, you want to use a website monitoring service. What are the tasks performed by a website monitoring service?
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to see the username, real name, home directory, encrypted password, and other information about a user. Which of the following Unix configuration files can you use to accomplish the task?
You want to repeat the last command you entered in the bash shell. Which of the following commands will you use?
You have just set up a wireless network for customers at a coffee shop. Which of the following are good security measures to implement? (Choose two)
You are concerned about war driving bringing hackers attention to your wireless network. What is the most basic step you can take to mitigate this risk?
Mark works as a Network Administrator for Infonet Inc. The company has a Windows 2000 Active Directory domain-based network. The domain contains one hundred Windows XP Professional client computers. Mark is deploying an 802.11 wireless LAN on the network. The wireless LAN will use Wired Equivalent Privacy (WEP) for all the connections. According to the company ' s security policy, the client computers must be able to automatically connect to the wireless LAN. However, the unauthorized computers must not be allowed to connect to the wireless LAN and view the wireless network. Mark wants to configure all the wireless access points and client computers to act in accordance with the company ' s security policy. What will he do to accomplish this? (Choose three)
You have made a program secure.c to display which ports are open and what types of services are running on these ports. You want to write the program ' s output to standard output and simultaneously copy it into a specified file. Which of the following commands will you use to accomplish the task?
Which of the following tools can be used to perform ICMP tunneling? (Choose two)
Which of the following recovery plans includes specific strategies and actions to deal with specific variances to assumptions resulting in a particular security problem, emergency, or state of affairs?
Which of the following is a method of the HttpSession interface and is used to retrieve the time when the session was created?
Which of the following techniques can be used to determine the network ranges of any network?
Martha works as a Web Developer for XYZ CORP. She is developing a Web site for the company. In the Web site, she uses multiple and overlapping style definitions to control the appearance of HTML elements. What is this technique known as?
A Cisco router can have multiple connections to networks. These connections are known as interfaces for Cisco Routers. For naming each interface, Cisco generally uses the type of interface as part of the name. Which of the following are true about the naming conventions of Cisco Router interfaces?
Which of the following protocols are used to provide secure communication between a client and a server over the Internet? (Choose two)
Mike works as a Network Engineer for XYZ CORP. The company has a multi-platform network. Recently, the company faced lots of blended threat issues that lead to several drastic attacks. Mike has been assigned a project to manage the resources and services of the company through both Intranet and Internet to protect the company from these attacks. Mike needs a system that provides auto-discovering and network topology building features to allow him to keep an intuitive view of the IT infrastructure. What will Mike use to meet the requirement of the project?
What will happen if you write the following parameters in the web.xml file?
< session-config >
< session-timeout > 0 < /session-timeout >
< /session-config >
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He performs Web vulnerability scanning on the We-are-secure server. The output of the scanning test is as follows: C.\whisker.pl -h target_IP_address -- whisker / v1.4.0 / rain forest puppy / www.wiretrip.net -- = - = - = - = - = = Host: target_IP_address = Server: Apache/1.3.12 (Win32) ApacheJServ/1.1 mod_ssl/2.6.4 OpenSSL/0.9.5a mod_perl/1.22 + 200 OK: HEAD /cgi-bin/printenv John recognizes /cgi-bin/printenv vulnerability ( ' Printenv ' vulnerability) in the We_are_secure server. Which of the following statements about ' Printenv ' vulnerability are true?
You work as a programmer for uCertify.Inc. You have a session object named session1 with an attribute named Attribute1, and an HttpSessionBindingEvent object binding1 bound to session1. Which of the following will be used to retrieve Attribute1?
Which of the following tools monitors the radio spectrum for the presence of unauthorized, rogue access points and the use of wireless attack tools?
You work as a Network Architect for Tech Perfect Inc. The company has a TCP/IP based Enterprise network. The company uses Cisco IOS technologies in the Enterprise network. You have enabled system message logging (syslog) service on all the routers that are currently working in the network. The syslog service provides all the reports, and important error and notification messages. You want to store all the reports and messages. Choose the locations where you can store all of these.
Which of the following evidences are the collection of facts that, when considered together, can be used to infer a conclusion about the malicious activity/person?
Which of the following NFS mount options specifies whether a program using a file via an NFS connection should stop and wait for the server to come back online, if the host serving the exported file system is unavailable, or if it should report an error?
You work as a Network Administrator for Tech-E-book Inc. You are configuring the ISA Server 2006 firewall to provide your company with a secure wireless intranet. You want to accept inbound mail delivery though an SMTP server. What basic rules of ISA Server do you need to configure to accomplish the task.
A sequence number is a 32-bit number ranging from 1 to 4,294,967,295. When data is sent over the network, it is broken into fragments (packets) at the source and reassembled at the destination system. Each packet contains a sequence number that is used by the destination system to reassemble the data packets in the correct order. The Initial Sequence Number of your computer is 24171311 at login time. You connect your computer to a computer having the IP address 210.213.23.21. This whole process takes three seconds. What will the value of the Initial Sequence Number be at this moment?
Which of the following is an Internet mapping technique that relies on various BGP collectors that collect information such as routing updates and tables and provide this information publicly?
Adam works as a Security Analyst for Umbrella Inc. He is retrieving large amount of log data from syslog servers and network devices such as Router and switches. He is facing difficulty in analyzing the logs that he has retrieved. To solve this problem, Adam decides to use software called Sawmill. Which of the following statements are true about Sawmill?
You work as a Software Developer for UcTech Inc. You want to create a new session. Which of the following methods can you use to accomplish the task?