Which type of NAT applies to the scenario where there are a small number of Internet access users and the number of public IP addresses is the same as the number of concurrent Internet access users?
Using the ___ method of the Web proxy, the virtual gateway will encrypt the real URL that the user wants to access, and can adapt to different terminal types.[fill in the blank]*
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
SSL VPN is a VPN technology that realizes remote secure access through SSL protocol. Which of the following software must be installed when using SSL VPN?
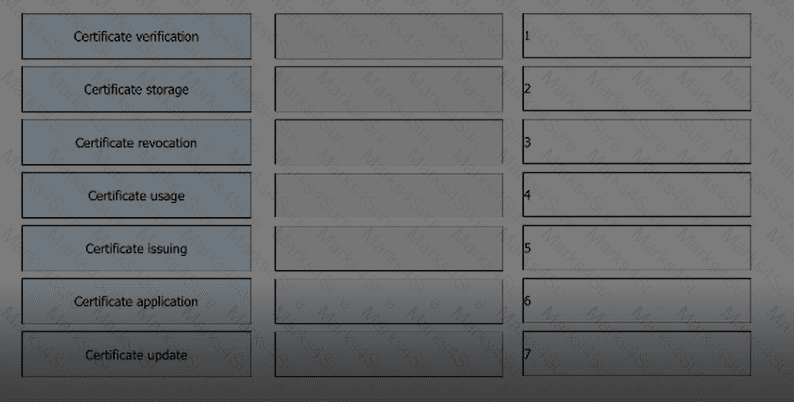
Please order the following steps in the PKI life cycle correctly, 1. Issued, 2. storage, 3. Update, 4. verify[fill in the blank]*
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
Arrange the following processes in the correct order based on the PKI lifecycle.
DES is a stream encryption algorithm, because the cipher capacity is only 56 bits, so it is not enough to deal with the weakness of insufficient security, and later 3DES was proposed.
Which of the following statements is correct about security zones on a Huawei firewall?
The RADIUS protocol specifies how to pass user information, billing information, authentication and billing results between the NAS and the RADIUS server, and the RADIUS server is responsible for receiving the user's connection request, completing the authentication, and returning the result to the NAS.
While working for a company, Tom receives an email with an attachment. Which of the following operations is correct?
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
Which of the following statements are correct about the status of the firewall VGMP group?
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
The trigger authentication method for firewall access user authentication does not include which of the following?
Which type of NAT translates both addresses and port numbers and uses the public IP address of the outbound interface as the post-NAT address?
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution. 1. Inhibition stage, 2. recovery phase, 3. Detection stage, 4. eradication phase[fill in the blank]*
Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
An enterprise wants to build a server system and requires the following functions: 1. The enterprise needs to have its own dedicated mailbox, and the sending and receiving of emails needs to go through the enterprise's server; 2. The server must provide file transfer and access services. Users in different departments of the enterprise provide accounts with different permissions: 3. When the enterprise accesses the internal webpage of the enterprise, the enterprise can directly enter the domain name in the browser to access. To meet the above requirements, which of the following servers do enterprises need to deploy? ( )*
The network environment is becoming more and more complex, and network security incidents occur frequently. While accelerating the construction of informatization, enterprises must not only resist external attacks, but also prevent internal management personnel from being involved in data leakage and operation and maintenance accidents due to operational errors and other issues. Which of the following options might reduce operational risk?
In hot standby networking, the heartbeat interfaces of the two firewalls must be directly connected.
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.
Social engineering is a means of harm such as deception, harm, etc. through psychological traps such as psychological weaknesses, instinctive reactions, curiosity, trust, and greed of victims ( )
Data monitoring can be divided into two types: active analysis and passive acquisition.
For which of the following parameters can the packet filtering firewall filter?
In the PKI certificate revocation process, a user needs to send a signed and encrypted email to the RA to apply for certificate revocation.