A user dials to the LNS of the company through L2TP over IPSec using the VPN client, and the final dialup fails. However, the debug ike all and debug l2tp all did not see any information on the LNS. The two stages of establishing ike failed. What are the reasons for the failure?
The Tracert packet attack is an ICMP timeout packet returned by the attacker when the TTL is ____, and the ICMP port unreachable packet returned when the destination address is reached to find the path through which the packet arrives at the destination. Spying on the structure of the network
What are the scenarios in which the USG series firewall service port sends gratuitous ARPs when the following configurations are performed?
Which of the following IKE Negotiation Phase 1 main mode negotiation processes is the role of Message 5 and Message 6?
Which of the following technologies can enhance the security of mobile users accessing the company ' s intranet VPN solution?
When there are a large number of BFD sessions in a system, what mode can be used to prevent BFD detection when the cost of sending BFD control packets periodically affects the normal operation of the system?
The malformed packet attack technology uses some legitimate packets to perform reconnaissance or data detection on the network. These packets are legal application types, but they are rarely used in normal networks.
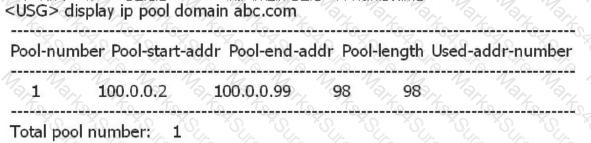
As shown below, the domain abc address pool is the address pool where the L2TP VPN user is located. What is wrong with the following statement?
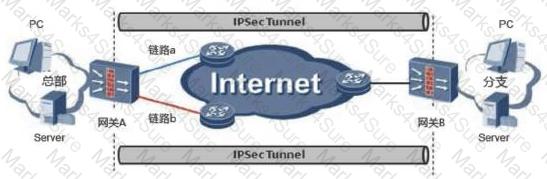
Which of the following methods is used to switch between active and standby links in the IPSec backup and backup system?
Networking as shown in the figure: PC1--USG--Router--PC2. If PC1 sends a packet to PC2, what are the three modes for the USG to process fragmented packets?
SSL works at the application layer and encrypts specific applications. Which layer does IPSec work on and provides transparent encryption protection for this layer and above?
In the abnormal traffic cleaning solution, to ensure that the attack traffic can be imported into the cleaning center for cleaning, the VRRP is implemented in Step 12 as shown in the figure. The management center adopts the following configuration: Select Configuration-- > Anti-DDoS- - > " Drainage management " , create a drainage task, configure the protected IP address to 10.1.3.10/32. What kind of route will the cleaning center generate after the above steps are configured?

In IPSec VPN, which one is incorrect about the difference between the barbaric mode and the main mode?
The console port password can be restored to the factory settings by pressing and holding the USG device Reset button for 1-3 seconds.
A certain network is as follows: LAN----G0/0/0 USG G0/0/1 ----Server. After the administrator analyzes the Attarcker on the LAN network connected to G0/0/0, if you want to prevent ARP flood attacks, limit the ARP traffic to 100 packets/minute. Which is the correct configuration?
The Haiwei Secoway VPN client initiates an L2TP connection. The source port of the L2TP packet is 1710 and the port 1710 of the destination port.
The management control information and service information of the out-of-band management interface are sent on the same channel.
In the firewall DDoS attack defense technology, the data packet of the session table is not defended. If the data packet of the session has been established, it is directly released.
Because the policy in the traffic limiting policy does not restrict the deny rule, you do not need to use the deny rule.
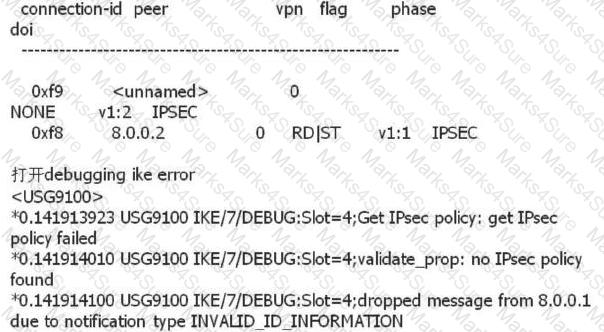
An administrator can view the IPSec status information and Debug information as follows. What is the most likely fault?
When using manual IPSec negotiation, NAT traversal is also required if there is a NAT device on the network.
Three physical interfaces have been added to the link-group group. When any one of the interfaces fails, what are the following descriptions correct?
What actions will be performed when the firewall hot standby sends the active/standby switchover?
The topology diagram of the BFD-bound static route is as follows: The administrator has configured the following on firewall A: [USG9000_A] bfd [USG9000_A-bfd] quit [USG9000_A] bfd aa bind peer-ip 1.1.1.2 [USG9000_A- Bfd session-aa] discriminator local 10 [USG9000_A-bfd session-aa] discriminator remote 20 [USG9000_A-bfd session-aa] commit [USG9000_A-bfd session-aa] quit What are the correct statements about this segment?

Which of the following statements is correct about the IKE main mode and the aggressive mode?
When the ip-link link health check is performed, if it is unable to receive the message several times in the absence of the link, it will be considered as a link failure.
By default, GigabitEthernet0/0/0 can be used as an out-of-band management interface in the USG2200 series.
The SSL VPN authentication is successful, but the Web-link resources cannot be accessed. What is the correct one?
In the IPSec active/standby link backup application scenario, gateway B uses IPSec tunneling technology and gateway A to establish an IPSec VPN.
SSL VPN authentication is successful. Using the file sharing function, you can view directories and files, but you cannot upload, delete, and rename files. What are the possible reasons?
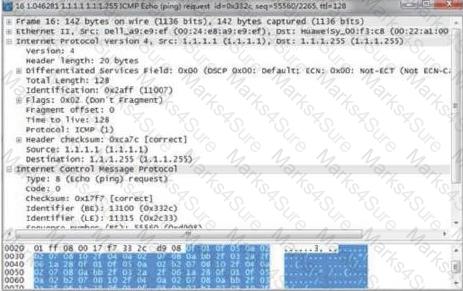
When an attack occurs, the result of packet capture on the attacked host (1.1.1.1) is as shown in the figure. What kind of attack is this attack?
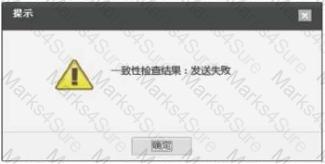
On the web configuration page, choose System -- > High Reliability -- > Hot Standby and click Check for HRP Configuration Consistency. Button. The following window pops up. Which of the following configurations can solve the problem (assuming the heartbeat is added to the DMZ area)?
The load balancing function is configured on the USG firewall for three FTP servers. The IP addresses and weights of the three physical servers are 10.1.13/24 (weight 16); 10.1.1.4/24 (weight 32); 10.1.1.5 /24 (weight 16), and the virtual server address is 202.152.26.123/24. A PC with the host address of 202.152.26.3/24 initiates access to the FTP server. Run the display firewall session table command on the firewall to check the configuration. Which of the following conditions indicates that the load balancing function is successfully implemented?
The ACK flood attack is defended by the load check. The principle is that the cleaning device checks the payload of the ACK packet. If the payloads are all consistent (if the payload content is all 1), the packet is discarded.
The constraints of the policy in the traffic limiting policy include quintuple, time period, user identity, and application protocol.
In the L2TP over IPSec application scenario, the USG device encrypts the original data packet with IPSec and then encapsulates the packet with L2TP.
The attacker sends a large number of invite messages to the SIP server, causing the SIP server to refuse service. Which layer of the OSI model is this attack based on?
The SSL VPN authentication login is unsuccessful and the message " Bad username or password " is displayed. Which one is wrong?
Virtual firewall virtualizes multiple logical firewalls on a physical firewall device and implements multiple instances?
What are the correct statements about the IP address scanning attack and prevention principles?
An enterprise network is as follows. At this time, server A cannot access server B. The administrator performs troubleshooting. It finds that server A can access firewall A, but cannot access firewall B. What is the method for administrators to use to troubleshoot problems?

A network is as follows: The l2tp vpn is established through the VPN Client and the USG (LNS). What are the reasons for the dialup failure?

Regarding the Radius authentication process, there are the following steps: 1. The Radius client (network access server) in the network device receives the username and password, and sends an authentication request to the Radius server; 2 the user logs in to the USG access server, etc. When the network device sends the username and password to the network access server; 3. After receiving the legitimate request, the Radius server completes the authentication and returns the required user authorization information to the client. What is the correct order?
When an IPSec VPN is set up on both ends of the firewall, the security ACL rules of both ends are mirrored.
The topology of the BFD-bound static route is as follows: The administrator has configured the following on firewall A: [USG9000_A] bfd [USG9000_A-bfd] quit [USG9000_A] bfd aa bind peer-ip 1.1.1.2 [USG9000_A- Bfd session-aa] discriminator local 10 [USG9000_A-bfd session-aa] discriminator remote 20 Which of the following configurations can be added to the firewall to implement BFD-bound static routes?

The hot standby and IPSec functions are combined. Which of the following statements is correct?
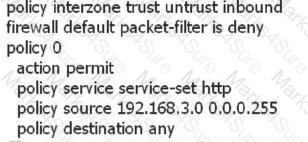
The PC A in the Trust zone is 192.168.3.1. You cannot access the Internet server in the Untrust zone. The configuration between the Trust zone and the Untrust zone is as follows. What are the most likely causes of the following faults?
The USG_B status is HRP_M[USG_A], and the USG_B status is HRP_S[USG_B] . The status of the USG_A is HRP_M[USG_A]. However, all traffic did not pass USG_A completely, and half of the traffic also passed USG_B.
Which of the following is correct about the configuration of the firewall interface bound to the VPN instance?
The virtual firewall forwards multiple instances. The firewall has multiple routing tables and forwarding tables. The addresses are overlapped and are implemented on the same configuration interface. Users with configuration rights can configure and view all data.
On the USG, you need to delete sslconfig.cfg in the hda1:/ directory. Which of the following commands can complete the operation?
Which part of the attack packet is matched by the blacklist to achieve attack prevention?