H12-722_V3.0 HCIP-Security-CSSN V3.0 Questions and Answers
In the big data intelligent security analysis platform, it is necessary to collect data from data sources, and then complete a series of actions such as data processing, detection and analysis, etc.
do. Which of the following options does not belong to the action that needs to be completed in the data processing part?
155955cc-666171a2-20fac832-0c042c0422
Regarding the processing flow of file filtering, which of the following statements is wrong?
In the deployment of Huawei NIP6000 products, only port mirroring can be used for streaming replication.
Which of the following technologies can achieve content security? (multiple choice)
The anti-virus feature configured on the Huawei USG6000 product does not take effect. Which of the following are the possible reasons? (multiple choice)
Regarding traditional firewalls, which of the following statements are correct? (multiple choice)
Which of the following protocols can be used to construct attack messages for special control message attacks? (multiple choice)
A ICMP protocol
B. UDP protocol
C. CIP protocol
D. FTP protocol
IPS is an intelligent intrusion detection and defense product. It can not only detect the occurrence of intrusions, but also can respond in real time through certain response methods.
Stop the occurrence and development of intrusions, and protect the information system from substantial attacks in real time. According to the description of PS, the following items are wrong?
When the device recognizes a keyword during content filtering detection, which response actions can the device perform? (multiple choice)
For special message attacks, which of the following option descriptions is correct?
A Special control packet attack is a potential attack and does not have direct destructive behavior
B. The attacker probes the network structure by sending special control messages to launch a real attack.
C. Special control message attacks do not have the ability to detect the network structure. Only scanning attacks can detect the network.
D. Special control message items can only use ICMP to construct attack messages.
Which of the following behaviors is a false positive of the intrusion detection system?
Among the following options, which attack is a malformed packet attack based on the TCR protocol?
Regarding the processing process of file overwhelming, which of the following statements is correct?
Regarding the sequence of the mail transmission process, which of the following is correct?
1. The sender PC sends the mail to the designated SMTP Server.
2. The sender SMTP Server encapsulates the mail information in an SMTP message and sends it to the receiver SMTP Server according to the destination address of the mail
3. The sender SMTP Server encapsulates the mail information in an SMTP message according to the destination address of the mail and sends it to the receiver POP3/MAP Senver
4. The recipient sends an email.
USG6000V software logic architecture is divided into three planes: management plane, control plane and
The whitelist rule of the firewall anti-virus module is configured as ( " *example*, which of the following matching methods is used in this configuration?
Which of the following is the default port number of Portal authentication service?
What content can be filtered by the content filtering technology of Huawei USG6000 products? (multiple choice)
Intrusion detection is a network security technology used to detect any damage or attempt to damage the confidentiality, integrity or availability of the system. Which of the following
What is the content of the intrusion detection knowledge base?
Regarding the mail content filtering configuration of Huawei USG6000 products, which of the following statements is wrong?.
The results of the RBL black and white list query on the firewall are as follows:
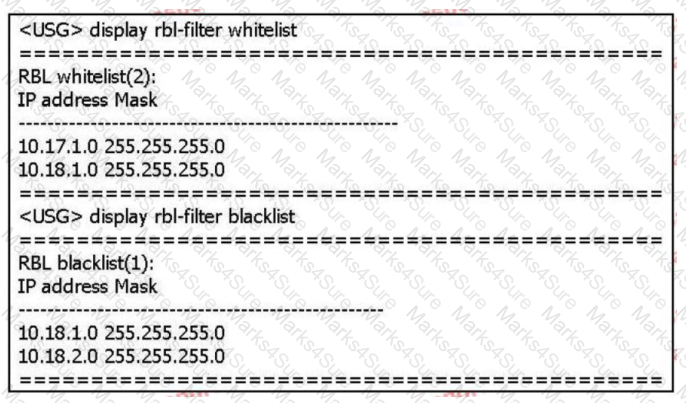
Based on the above information only, which of the following statements is correct? (multiple choice)
Abnormal detection is to establish the normal behavior characteristic profile of the system subject through the analysis of the audit data of the system: check if the audit data in the system
If there is a big discrepancy with the normal behavior characteristics of the established subject, it is considered an intrusion. Nasu must be used as the system subject? (multiple choice)
Regarding the description of intrusion detection technology, which of the following statements is correct?
Regarding the mail content filtering configuration of Huawei USG6000 products, which of the following statements is wrong?.
Tianyu Nei answered the role of safety filtering technology, which of the following is still correct? (multiple choice)
When configuring the URL filtering configuration file, www.bt.com is configured in the URL blacklist-item: At the same time, set it in the custom URL category.
A URL is set as bt.com, and the action of customizing URL classification is a warning. Regarding the above configuration, which of the following statements are correct? (More
select)
If the user ' s FTP operation matches the FTP filtering policy, what actions can be performed? (multiple choice)
Regarding the strong statement of DNS Request Flood attack, which of the following options is correct?
Which of the following is the correct configuration idea for the anti-virus strategy?
1. Load the feature library
2. Configure security policy and reference AV Profile
3. Apply and activate the license
4. Configure AV Profile
5. Submit
Under the CLI command, which of the following commands can be used to view the AV engine and virus database version?
In Huawei USG6000 products, IAE provides an integrated solution, all content security detection functions are integrated in a well-designed
In the high-performance engine. Which of the following is not the content security detection function supported by this product?
Viruses can damage computer systems. v Change and damage business data: spyware collects, uses, and disperses sensitive information of corporate employees.
These malicious pastoral software seriously disturb the normal business of the enterprise. Desktop anti-disease software can solve the problem of central virus and indirect software from the overall situation.
In the following options, which of the two attacks use similar attack methods, they will generate a large number of useless response packets, occupying network bandwidth,
Consume equipment resources?
Anti DDoS seven-layer defense can work from the dimensions of interface-based defense, global defense and defense object-based defense.
Which of the following options are the possible reasons why a certain signature is not included after the IPS policy configuration is completed? (multiple choice)
If the Huawei USG600 product uses its own protocol stack cache for all files passing through the device and then performs a virus scan, then the device uses
It is the stream scanning method.
Which of the following descriptions are correct for proxy-based anti-virus gateways? (multiple choice)
The following figure is a schematic diagram of the detection file of the firewall and the sandbox system linkage.
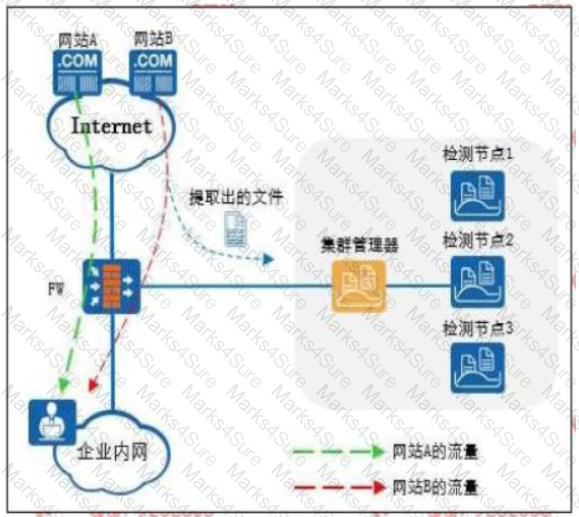
The Web reputation function is enabled on the firewall, and website A is set as a trusted website and website B is set as a suspicious website.
Which of the following statements is correct
The realization of content security filtering technology requires the support of the content security combination license.
Which of the following technology, administrators can according to business requirements, to scale to achieve load sharing of business flow?
Threats detected by the big data intelligent security analysis platform will be synchronized to each network device at the same time C and then collected from the network device
Collect it in the log for continuous learning and optimization.
Since the sandbox can provide a virtual execution environment to detect files in the network, the sandbox can be substituted when deploying security equipment
Anti-Virus, IPS, spam detection and other equipment.
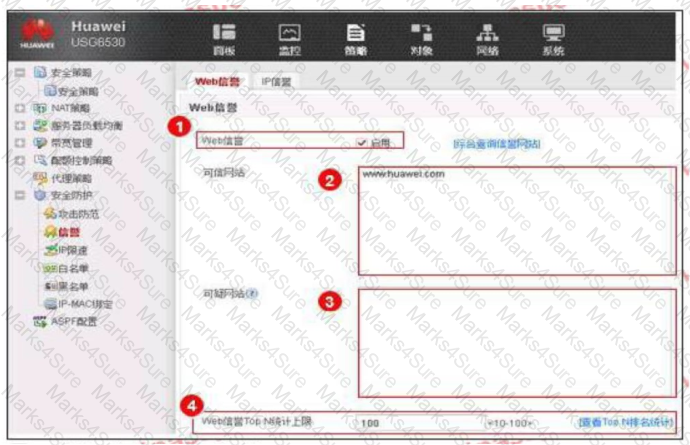
An enterprise administrator configures the Web reputation system as shown in the figure. Regarding the configuration, which of the following statements is correct?
The administrator has made the following configuration:
1. The signature set Protect_ all includes the signature ID3000, and the overall action of the signature set is to block.
2. The action of overwriting signature ID3000 is an alarm.
Place refers to the terminal environment when end-user use strategy management center access to
controlled network office, which options are correct about place? (Choose 2 answers)
URL filtering technology can perform URL access control on users according to different time objects and address objects to achieve precise management of users.
The purpose of the Internet behavior.
Regarding the sequence of file filtering technology processing flow, which of the following is correct?
(1) The security policy is applied as permit
(2) Protocol decoding
(3) File type recognition
(4) Application recognition
(5) File filtering
Huawei NIP6000 products provide carrier-class high-reliability mechanisms from multiple levels to ensure the stable operation of equipment.
Which of the following options belong to the network reliability? (multiple choice)
The administrator has configured file filtering to prohibit internal employees from uploading development files, but internal employees can still upload development files. Which of the following is not allowed Can the reason?
Which of the following options is not a cyber security threat caused by weak personal security awareness?


