When configuring the terminal visits, we put some equipment configured exception equipment ,which of the following statements are true about the exception equipment?
In the anti-virus policy configuration of Huawei USG6000 product, what are the response methods of HTTP protocol? (multiple choice)
There is a three-layer forwarding device between the authentication client and the admission control device:If at this time Portal The certified three-layer authentication device can also obtain the authentication client's MAC address,So you can use IP Address and MC The address serves as the information to identify the user.
Configure the following commands on the Huawei firewall:
[USG] interface G0/0/1
[USG] ip urpf loose allow-defult-route acl 3000
Which of the following options are correct? (multiple choice)
Information security is the protection of information and information systems to prevent unauthorized access, use, leakage, interruption, modification, damage, and to improve
For confidentiality, integrity and availability. ,
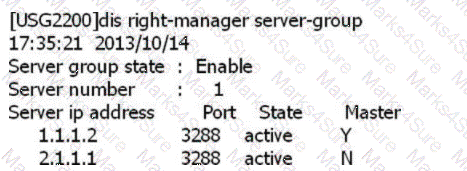
SACG query right-manager information as follows, which options are correct? (Select 2 answers)
Which of the following is the default port number of Portal authentication service?
When the license of Huawei USG6000 product expires, the RBL function will be unavailable, and users can only use the local black and white list to filter junk mail.
155955cc-666171a2-20fac832-0c042c0435
Agile Controller-Campus The department includes four parts of the management center(MC)Business manager(SM)And business controller(SC)And client network access equipment (NAD)As a component of the solution, it is linked with the service controller to realize user access control and free mobility.
Due to differences in network environment and system security strategies, intrusion detection systems are also different in specific implementation. From the perspective of system composition, the main
Which four major components are included?
The visitor management process includes page customization, account application, user authentication, audit, and logout. After the user successfully applies for an account, he needs to change.
When the account is distributed to users, what stage does the distribution of the account belong to?
The administrator has made the following configuration:
1. The signature set Protect_ all includes the signature ID3000, and the overall action of the signature set is to block.
2. The action of overwriting signature ID3000 is an alarm.
Part of the reason why the APT attack becomes difficult to defend is that it uses the vulnerabilities to attack. This kind of zero-day hole usually requires flowers
A lot of time to research and analyze and produce corresponding defense methods.
Deploying on Windows platform, using SQL Server database About the HA function of Agile Cotoller-Campus, which of the following descriptions Is it correct? (multiple choice)
Use the command on the switch to view the status of free mobility deployment, the command is as follows:
For the above command, which of the following descriptions is correct?
Which of the following options are common reasons for IPS detection failure? (multiple choices)
VIP Experience guarantee, from which two aspects are the main guarantees VIP User experience? (Multiple choice)
Regarding uninstalling the Agile Controller-Campus in Windows and Linux systems, which of the following descriptions is correct?
After the user deploys the firewall anti-virus strategy, there is no need to deploy anti-virus software
A network adopts 802. 1X To authenticate access users, the access control equipment is deployed at the convergence layer, and after the deployment is completed, it is used on the access control equipment t-aa The command test is successful, but the user cannot access the network. The failure may be caused by the following reasons? (Multiple choice)
Terminal fault diagnosis tool can diagnose fault, also can collect terminal information.
Regarding patch management and Windows patch checking strategies, which of the following descriptions is wrong?
Which of the following options is for Portal The statement of the gateway access process is correct?
Regarding the sequence of the mail transmission process, which of the following is correct?
1. The sender PC sends the mail to the designated SMTP Server.
2. The sender SMTP Server encapsulates the mail information in an SMTP message and sends it to the receiver SMTP Server according to the destination address of the mail
3. The sender SMTP Server encapsulates the mail information in an SMTP message according to the destination address of the mail and sends it to the receiver POP3/MAP Senver
4. The recipient sends an email.
An enterprise has a large number of mobile office employees, and a mobile office system needs to be deployed to manage the employees. The number of employees in this enterprise exceeds 2000 People, and the employees’ working areas are distributed all over the country. In order to facilitate management, which deployment method is adopted?
What content can be filtered by the content filtering technology of Huawei USG6000 products? (multiple choice)
How to check whether the SM and SC silverware start normally after installing the Agile Controller-Campus) (multiple delivery)
UDP is a connectionless protocol. UDP Flood attacks that change sources and ports will cause performance degradation of network devices that rely on session forwarding.
Even the session table is exhausted, causing the network to be paralyzed. Which of the following options is not a preventive measure for UDP Flood attacks?
In the Policy Center strategy configuration, how many violations rating of definition are there?
In the terminal host check strategy, you can check whether the important subkeys and key values of the registry meet the requirements to control the terminal host's Access, which of the following check results will be recorded as violations? (multiple choice)
After an enterprise deployed antivirus software, it was discovered that virus infections still occurred on a large scale. In addition to the limitations of the product's own technology, the reason for the problem is weak personal terminal security protection, which is also an important factor.
Which of the following behaviors is a false positive of the intrusion detection system?
When using local guest account authentication, usually use(Portal The authentication method pushes the authentication page to the visitor. Before the user is authenticated, when the admission control device receives the HTTP The requested resource is not Portal Server authentication URL When, how to deal with the access control equipment.
Import the user information of the AD server on the Agile Controller-Campus to realize the user's access authentication. If the user is in the Agile.
The user information is not found on the Controller-Campus. Which of the following actions will be performed in the next step?
Web Standards that come with the client and operating system 8021 The instrument client only has the function of identity authentication: It does not support the execution of inspection strategies and monitoring strategies. Any Office The client supports all inspection strategies and monitoring strategies.
When managing guest accounts, you need to create a guest account policy and set the account creation method. For the account creation method, which of the following descriptions is wrong?
In centralized networking, database,SM server,SC server\ AE Servers are centrally installed in the corporate headquarters. This networking method is suitable for companies with a wide geographical distribution of users and a large number of users.
The user access security solution is one-kind"End to end"Security architecture. The user access security architecture includes three key components:Terminal equipment, network access equipment and access server.
Regarding the description of the security zone in the Agile Controller-Campus, which of the following options are correct? (multiple choice)
Business accompanying is-A special access control method, according to the user's access location, access time, access method and terminal use to grant designated investment limits, among which the physical connection can be divided into 3 Class, excluding which of the following access methods?
When the -aa command is used on the access control device to test the connectivity with the Radius server, the running result shows success, but the user cannot Normal access, the possible reason does not include which of the following options?
In WPA2, because of the more secure encryption technology-TKIP/MIC, WPA2 is more secure than WPA.
For SYIN Flood attacks, TCP source authentication and TCP proxy can be used for defense. Which of the following descriptions is correct?
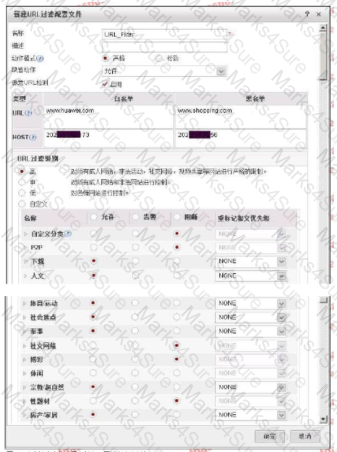
The following figure shows the configuration of the URL filtering configuration file. Regarding the configuration, which of the following statements is correct?
Anti-DDoS defense system includes: management center, detection center and cleaning center.
Portal authentication on the Agile Controller-Campus has been configured and is correct.
Configure the following commands on the access control switch:
[S5720] authentication free-rule 1 destination ip 10.1.31.78 mask 255.255. 255.255
Which of the following options are correct? (multiple choice)
Regarding the mail content filtering configuration of Huawei USG6000 products, which of the following statements is wrong?.
SQl injection attacks generally have the following steps:
①Elevate the right
②Get the data in the database
③Determine whether there are loopholes in the webpage
④ Determine the database type
For the ordering of these steps, which of the following options is correct?
The access control server is the implementer of the corporate security policy, responsible for implementing the corresponding access control in accordance with the security policy formulated by the customer's network(Allow, deny, leave or restrict).
In enterprises where terminal host access control management is relatively strict, administrators hope to bind terminal hosts and accounts to prevent terminal users from accessing the controlled network from unauthorized terminal hosts at will. Regarding the description of binding the terminal host and account, which of the following is correct?
Regarding the definition of WIPS/WIDS, which of the following statements is correct?
The most common form of child-like attack is to send a large number of seemingly legitimate packets to the target host through Flood, which ultimately leads to network bandwidth.
Or the equipment resources are exhausted. Which of the following options is not included in traffic attack packets?
Regarding the use of MAC authentication to access the network in the WLAN networking environment, which of the following statements is wrong en.
In the terminal security management, the black and white list mode is used to check the terminal host software installation status. Which of the following situations is a compliant behavior?
Regarding MAC authentication and MAC bypass authentication, which of the following descriptions are correct? (multiple choice)
According to different reliability requirements, centralized networking can provide different reliability networking solutions. Regarding these solutions, which of the following descriptions are correct? (Multiple choice)
Viruses can damage computer systems. v Change and damage business data: spyware collects, uses, and disperses sensitive information of corporate employees.
These malicious pastoral software seriously disturb the normal business of the enterprise. Desktop anti-disease software can solve the problem of central virus and indirect software from the overall situation.
Traditional network single--The strategy is difficult to cope with the current complex situations such as diversified users, diversified locations, diversified terminals, diversified applications, and insecure experience.
The terminal host access control function does not take effect, the following is SACG View information on:
< FW > display right- manager role-id rule
Advanced ACL 3099 ,25 rules,not bingding with vpn-instance Ad's step is 1
rule 1000 permit ip (1280 times matched)
rule 1001 permit ip destination 172.18.11.2210 (581 times matched)
rule 1002 permit ip destination 172:18.11.2230 (77 times matched)
rule 1003 permit ip destination 172.19.0.0 0.0 255.255 (355 Book times matched)
rule 1004 deny ip (507759 times matched)
Which of the following statements is correct?
The processing flow of IPS has the following steps;
1. Reorganize application data
2. Match the signature
3. Message processing
4. Protocol identification
Which of the following is the correct order of the processing flow?
Install Agile Controller-Campus Which of the following steps do not need to be completed before?
USG6000V software logic architecture is divided into three planes: management plane, control plane and
The relationship between user groups and accounts in user management is stored in a tree on the Agile Controller-Campus. An account belongs to only one user group.
Consistent with the corporate organizational structure: If the OU (OnizbonUnit) structure stored in the AD/LDAP server is consistent with the corporate organizational structure, users are stored Under 0OU, when the Agile Controller-Campus synchronizes AD/LDAP server accounts, which synchronization method can be used?
Analysis is the core function of intrusion detection. The analysis and processing process of intrusion detection can be divided into three phases; build an analyzer to perform analysis on actual field data.
Which of the analysis, feedback and refinement is the function included in the first two stages?
Which of the following options are right 802. 1X The description of the access process is correct? (Multiple choice).
When using the misuse check technology, if the normal user behavior is successfully matched with the intrusion feature knowledge base, it will be falsely reported.
Regarding intrusion detection I defense equipment, which of the following statements are correct? (multiple choice)
Which of the following is not an abnormal situation of the file type recognition result?
Regarding the description of the ACL used in the linkage between SACG equipment and the TSM system, which of the following statements is correct!?
Tianyu Nei answered the role of safety filtering technology, which of the following is still correct? (multiple choice)
Which of the following options is right PKI The sequence description of the work process is correct?
1. PKI Entity direction CA ask CA Certificate. .
2. PKI Entity received CA After the certificate, install CA Certificate.
3. CA receive PKI Entity CA When requesting a certificate, add your own CA Certificate reply to PKI entity.
4. PKI Entity direction CA Send a certificate registration request message.
5. PKI When the entities communicate with each other, they need to obtain and install the local certificate of the opposite entity.
6. PKI Entity received CA The certificate information sent.
7. PKI After the entity installs the local certificate of the opposite entity,Verify the validity of the local certificate of the peer entity. When the certificate is valid,PC The public key of the certificate is used for encrypted communication between entities.
8. CA receive PKI The entity's certificate registration request message.
User access authentication technology does not include which of the following options?
Deployed by an enterprise network managerAgile Controller-Campus withSACG Later;Identity authentication is successful but cannot access the post-authentication domain, This phenomenon may be caused by any reason? (Multiple choice)
Location refers to the end user's use AC-Campus The terminal environment when accessing the controlled network office. Which of the following options is correct for the description of the place?
Regarding intrusion prevention, which of the following option descriptions is wrong
The anti-virus feature configured on the Huawei USG6000 product does not take effect. Which of the following are the possible reasons? (multiple choice)
Regarding the mail content filtering configuration of Huawei USG6000 products, which of the following statements is wrong?.
The IPS function of Huawei USG6000 supports two response methods: blocking and alarming.
Regarding the anti-spam local black and white list, which of the following statements is wrong?
Which of the following options is correct for the sequence of the flow-by-stream detection of AntiDDoS?
1. The Netflow analysis device samples the current network flow;
2. Send a drainage command to the cleaning center;
3. Discover the DDoS attack stream;
4.Netior: analysis equipment sends alarms to ATIC management center
5. The abnormal flow is diverted to the cleaning center for further inspection and cleaning;
6. The cleaning center sends the host route of the attacked target IF address server to the router to achieve drainage
7. The cleaning log is sent to the management center to generate a report;
8. The cleaned traffic is sent to the original destination server.
Huawei's USG000 product can identify the true type of common files and over-check the content. Even if the file is hidden in a compressed file, or change the extension
The name of the exhibition can't escape the fiery eyes of the firewall.
Which of the following options belongs to MC prioritized pail Authentication application scenarios?
Threats detected by the big data intelligent security analysis platform will be synchronized to each network device at the same time C and then collected from the network device
Collect it in the log for continuous learning and optimization.
For the description of the principles of HTTP Flood and HTTPS Flood blow defense, which of the following options are correct? (multiple choice)
Place refers to the terminal environment when end-user use strategy management center access to
controlled network office, which options are correct about place? (Choose 2 answers)
For the basic mode of HTTP Flood source authentication, which of the following options are correct? (multiple choice)
Misuse detection is through the detection of similar intrusions in user behavior, or those that use system flaws to indirectly violate system security rules
To detect intrusions in the system. Which of the following is not a feature of misuse detection 2
According to the user’s access5W1H Conditions determine access rights andQoS Strategy for5W1Ho[Which of the following descriptions are correct? (Multiple choice)
MAC Certification refers to 802.1x In the protocol authentication environment, the terminal does not respond to the connection control device after accessing the network 802.1x When protocol authentication is requested, the access control does not automatically obtain the terminal’s MAC The address is sent as a credential to access the network RADIUS The server performs verification.
The security management system is only optional, and anti-virus software or anti-hacking technology can be a good defense against network threats.
In the security protection system of the cloud era, reforms need to be carried out in the three stages before, during and after the event, and a closed-loop continuous improvement should be formed.
And development. Which of the following key points should be done in "things"? (multiple choice)
If a company wants to detect image files, Shellcode code files and PDF files, which of the following types of sandboxes can be used? (More
155955cc-666171a2-20fac832-0c042c0420
select)
The user accesses the network through the network access device, and the third-party RADIUS server authenticates and authorizes the user. Regarding the certification process, which of the following options is wrong?
Which of the following methods can be used to protect enterprise terminal security?
If the Huawei USG600 product uses its own protocol stack cache for all files passing through the device and then performs a virus scan, then the device uses
It is the stream scanning method.