After a switch restarts, static MAC address entries saved on the switch remain in the MAC address table.
An ACL rule is as follows. Which of the following IP addresses can be matched by the permit rule?
Rule: rule 5 permit ip source 10.0.2.0 0.0.254.255
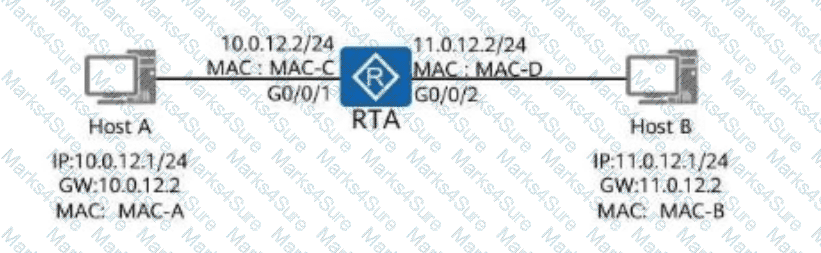
As shown in the figure, the host has ARP cache. Host A sends a data packet to host B. Which of the following are the destination MAC address and destination IP address of the data packet?
Which of the following IPv6 addresses can be abbreviated as 2FFF:DAC:ABEF::CDAA:732?
It is advised to assign static IP addresses to servers during campus network planning.
An ACL rule is as follows. Which of the following IP addresses can be matched by the permit rule?
rule 5 permit ip source 10.0.2.0 0.0.254.255
When a switch port receives a frame that does not carry a VLAN tag, it must add a PVID to the frame.
The following configuration commands implement route backup on RTA for a route to the same destination 10.1.1.0.
[RTA] ip route-static 10.1.1.0 24 12.1.1.1 permanent
[RTA] ip route-static 10.1.1.0 24 13.1.1.1
A network administrator uses the ping command to check for points of failure in the network. Which protocols will be used during this process?
Which of the following statements about encapsulation and decapsulation are true?
The LACP priority is shown in the figure. Switch A and Switch B adopt link aggregation in LACP mode, all interfaces are added to the link aggregation group (LAG), and the maximum number of active ports is set to 3.
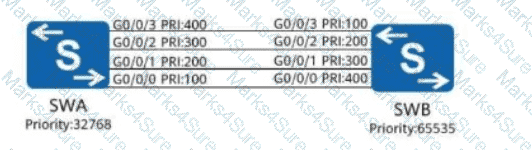
Which port of Switch A is NOT an active port?
Options:
When a switch receives a unicast data frame, if the destination MAC address of the data frame can be found in the MAC address table of the switch, the data frame is definitely forwarded through the port corresponding to the MAC address.
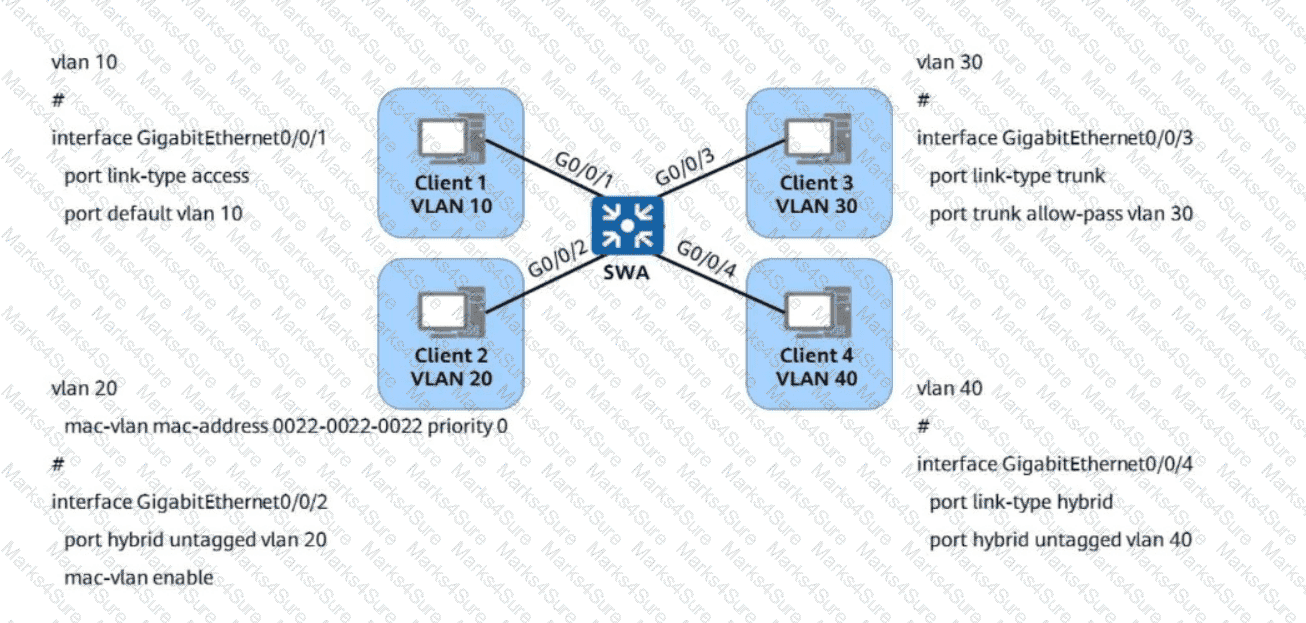
Refer to the following VLAN configurations on a Huawei switch. Which of the following statements are true?
Which of the following statements are true about the shortcut keys of the Versatile Routing Platform (VRP)?
(When a network engineer enters a command, the following information is displayed:
Error: Unrecognized command found at ' A ' position. Which of the following statements is true about such information?)
How many VLANs are created when using the following commands?
vlan batch 10 20
vlan batch 10 to 20
Which of the following MAC addresses cannot be used as the MAC address of host network adapters?
For an STP-enabled switch, a port in any state can transition to the Disabled state.
On the VRP CLI, files cannot be permanently deleted using the delete or delete /unreserved command. To permanently delete them, you need to delete the files in the recycle bin.
On Huawei routers, which of the following is the default preference of static routing?
If a device running STP receives an RSTP configuration BPDU, it discards the BPDU.
Network devices running SNMP can proactively report traps to help network administrators detect faults in a timely manner.
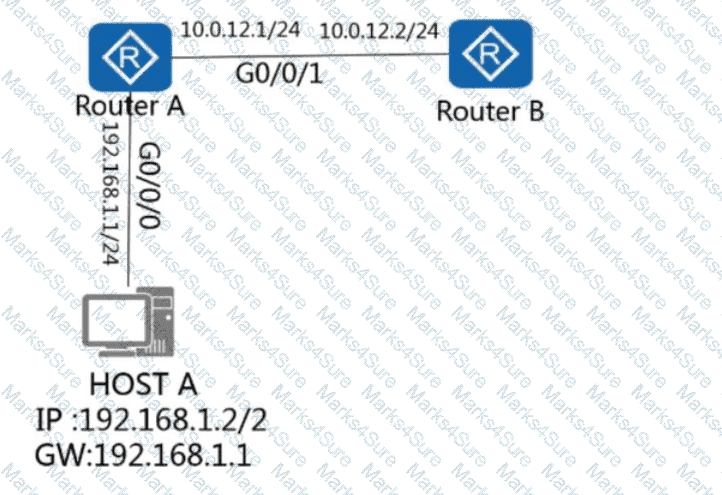
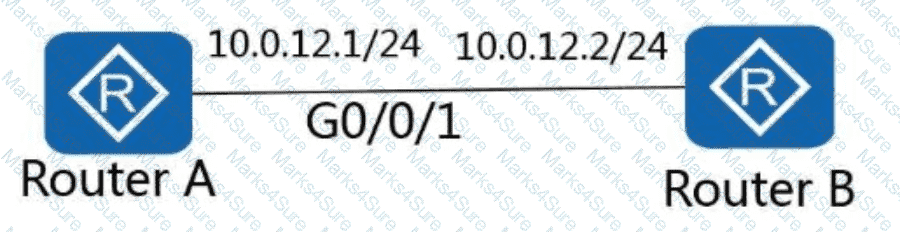
On the network shown in the figure, host A logs in to router A through Telnet and obtains the configuration file of router B through FTP on the remote CLI. How many TCP connections exist on router A?
What is the total length of the interface ID in each link-local unicast address?
Network Address and Port Translation (NAPT) allows multiple private IP addresses to be mapped to the same public IP address through different port numbers. Which of the following statements about port numbers in NAPT is true?
UDP is connectionless. As such, which of the following must be used to ensure transmission reliability?
Which of the following statements is true about the Forward Delay timer of STP?
For the Versatile Routing Platform (VRP), the login timeout period can be set only on a VTY interface.
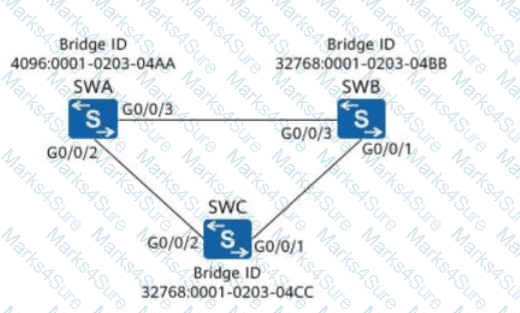
As shown in the figure, which of the following ports will be in a blocking state?
If the value of the " Type/Length " field of an Ethernet data frame is 0x0800, the length range of the upper-layer packet header carried by the data frame is from 20B to 60B.
The router that runs OSPF first enters the Full state and then synchronizes the LSDB.
Which statement is true regarding the following command?
ip route-static 10.0.12.0 255.255.255.0 192.168.1.1
When an AP and an AC are located on different Layer 3 networks, which of the following methods is recommended for the AP when discovering the AC?
Which of the following commands can be used to change the device name to huawei?
If PPP authentication fails, which type of packet will be sent to the authenticated peer by the authenticator?
If Spanning Tree Protocol (STP) is disabled on the network consisting of switches, a Layer 2 loop will definitely occur.
Which of the following authentication modes does/do not require a user name and a password?
By default, it takes at least 30 seconds for an STP-enabled port to transition from Disabled to Forwarding.
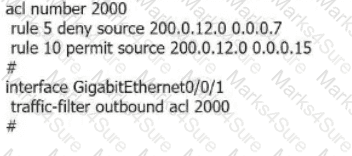
When the ACL in the following figure is configured on a Telnet server, only the device with an IP address of 172.16.105.2 can remotely log in to the Telnet server.
bash
Copy code
acl number 2000
rule 5 permit source 172.16.105.2 0
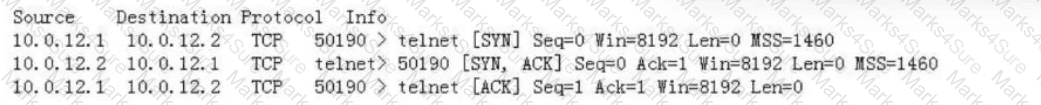
Refer to the captured three packets shown in the figure. Which of the following statements is false?
In RSTP mode, both alternate and backup ports cannot forward user traffic and cannot receive, process, and send BPDU.
When IPv4 is used as the network layer protocol, which of the following fields is not contained in the network layer header?
As shown in the figure, router A has successfully telneted to router B using 10.0.12.2. Which of the following operations will interrupt the Telnet session between router A and router B?
Assuming that an administrator is running the command shown in the figure on an AR2200 router, which of the following statements about the configuration is true?
< Huawei > reset saved-configuration
Warning: The action will delete the saved configuration in the device.
The configuration will be erased to reconfigure. Continue? [Y/N]:
On VRP, the command lines are classified into four levels in increasing priority: Visit level, Monitoring level, Configuration level, and Management level. At which level, the operator is permitted to configure service but is not permitted to operate the file system?
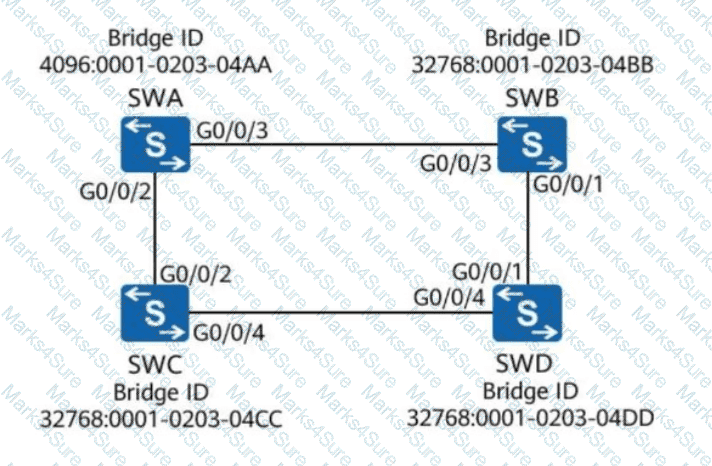
As shown in the figure, all switches run STP. Assume that the path cost of all ports is 200. What is the root path cost contained in the configuration BPDU received by G0/0/4 on SWD?
According to the VTY user interface configuration shown in the following figure, the user level is set to 3.
You want to check the running configuration on a device by running a Python script to telnet to the device. Which of the following statements is true?
For multiple paths to the same destination network, the router needs to compare the preference values of the paths. If the preference values are the same, the router selects the paths based on the cost value.
The following figure shows the configuration of a sub-interface on a router. For which VLAN does the sub-interface receive tagged data frames?
Which of the following is the default port number for network devices running SNMPv2c to send messages to an NMS?
The authentication, authorization, and accounting schemes and HWTACACS or RADIUS server templates created on AR routers take effect only after being applied to a domain.
When a host uses the stateless address autoconfiguration solution to obtain an IPv6 address, the host cannot obtain the DNS server address.
Which of the following advantages is/are provided by inter-VLAN routing in one-arm routing mode?
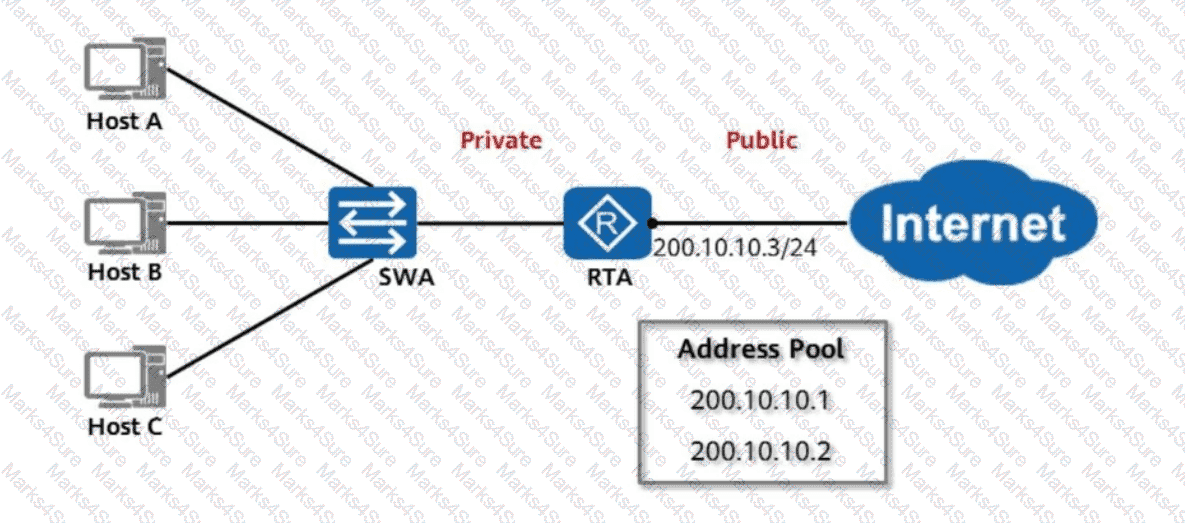
As shown in the figure, RTA uses NAT and has an address pool configured to implement many-to-many non-NAPT address translation, so that hosts on the private network can access the public network. Assume that the address pool has only two public IP addresses, which are translated for Host A and Host B. If Host C wants to access the public network, which of the following statements is true?
A Layer 2 ACL can match information such as the source MAC address, destination MAC address, source IP address, and destination IP address.
(You can run the " pwd " and " dir " commands on the Versatile Routing Platform (VRP) to view file information in the current directory.)
In STP, the bridge ID on the switching network is as follows. With which of the following bridge IDs is the switch selected as the root bridge?
Which of the following packets is used by network devices running SNMPv1 to proactively send alarm information?
A company applies for a class C IP address for subnetting. It has eight branches, and the largest branch has a subnet that should support at least 14 hosts. What would be an appropriate subnet mask?
Refer to the following configuration of an interface on a switch. For which VLAN does the interface remove VLAN tags before forwarding data frames?
interface GigabitEthernet 0/0/1
port hybrid tagged vlan 2 to 3 100
port hybrid untagged vlan 4 6
During STP calculation, the port cost is associated with the port bandwidth by default. Which of the following statements about the relationship between port cost and port bandwidth is true?
Which of the following WLAN security policies support open link authentication?
On the network shown in the figure, when planning traffic, the network administrator requires that the data packets sent from host A to host B pass through G0/0/3 on the router, and the packets sent from host B to host A pass through G0/0/4.
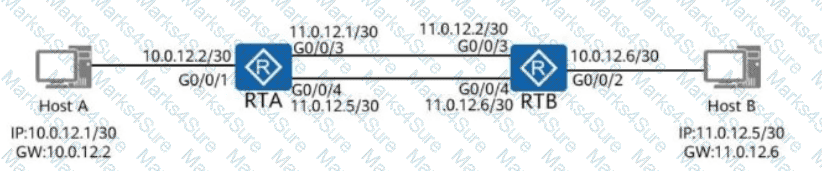
Which of the following commands can be used to meet this requirement?
Options:
A company applies for a class C IP address for subnetting. It has six branches and the largest branch should have 26 hosts. What would be an appropriate subnet mask for the largest branch?
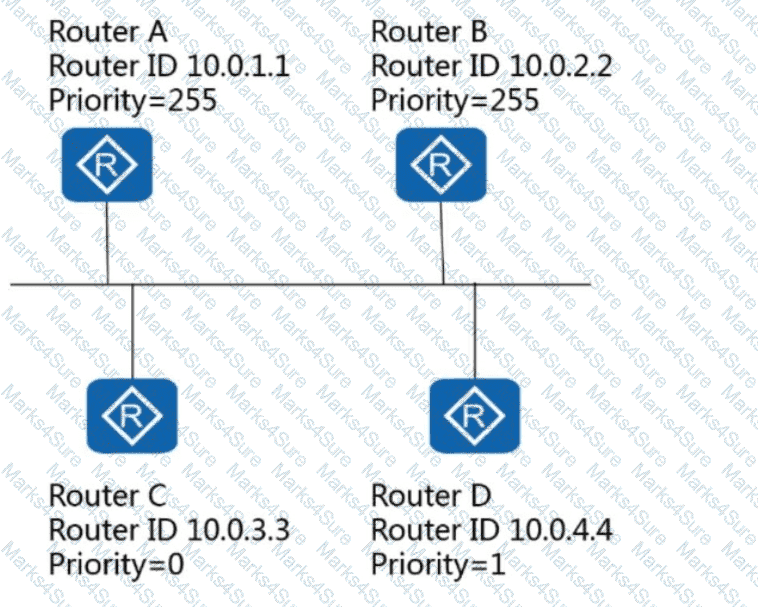
Assuming that OSPF has been enabled on all routers in the following figure, which router is the BDR on this network?
(Network Functions Virtualization (NFV) implements software-based network application deployment.)
Which of the following are advantages of stacking and CSS (Cluster Switch System) technologies?
A router that runs OSPF can enter the Full state only after Link-State Database (LSDB) synchronization is completed.
While inspecting packets in the network, a network administrator discovers a frame with the destination MAC address of 01-00-5E-A0-B1-C3. What can the administrator determine from this?
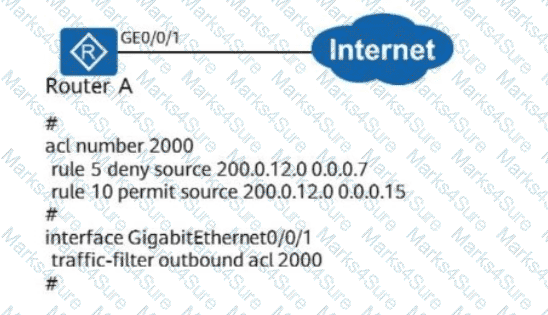
As shown in the figure, the configuration of Router A is as follows. Which of the following statements is/are incorrect?
Which of the following commands is used to configure the country code on an AC?
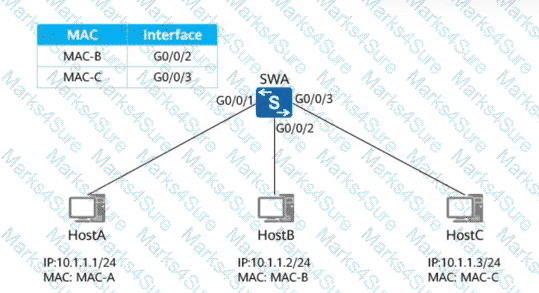
As shown in the figure, the MAC address table of SWA is as follows. The switch cannot learn the MAC address of HOST A. Which of the following reasons is impossible?
After an Eth-Trunk in LACP mode is created, devices on both ends send LACPDUs to elect the Actor. Which of the following parameters in LACPDUs determine the Actor election?
Which of the following does not change for APs associated with a STA during WLAN roaming?
In standard STP mode, which of the following ports on non-root switches forward the BPDUs with TC bits set generated by the root switch?