If the interval for two consecutive packets of a TCP session reaching the firewall is longer than the aging time of the session, the firewall deletes the session information from the session table to ensure network security.
Which of the following statements regarding the firewall zone security level is false?
An edge port is a new port role added to RSTP to overcome the disadvantages of STP. Which of the following statements is false about this port role?
An IP prefix list is a common matching tool used in routing policies. Which of the following cannot be configured as matching conditions in an IP prefix list on a Huawei router?
In which of the following scenarios can a neighbor relationship not be established between two directly connected Huawei routers after IS-IS is configured?
Which of the following statements regarding routing policy and policy-based routing are true?
On an RSTP network, you can set the STP priority of a switch to specify the switch as the root bridge.
Which of the following values is the default STP priority of a Huawei switch?
When IPv4 unicast packets are transmitted over Ethernet, their destination MAC address is also a multicast MAC address. If the IP address of a multicast group is 224.0.1.1, which of the following is the corresponding multicast MAC address?
The Origin attribute is used to define the origin of BGP path information. There are three types of Origin attributes. Which of the following lists the Origin attributes in descending order of priority?
By default, some security zones are created when Huawei firewalls are enabled. Which of the following security zones is created by users?
When receiving a packet, a router matches the packet against ACL rules . The ACL matching result is either Matched or Unmatched . If the matching result is Unmatched , which of the following are possible causes?
A switch runs MSTP. The configuration is shown in the figure. What is the role of this switch in MSTI 1?
On an OSPF network, an algorithm is used to prevent loops within an area, but loops may occur between areas. Therefore, OSPF defines a loop prevention mechanism for inter-area routes. Which of the following statements are true about the loop prevention mechanism?
Typically, a protocol that occupies two ports during communication is called a multi-channel protocol. For such protocols, the ASPF function must be enabled on the firewall to ensure smooth setup of the data channel and reduce the risk of attacks. Which of the following protocols is not a multi-channel protocol?
When an SSH client accesses an SSH server for the first time and the SSH server ' s public key is not configured on the SSH client, you can enable first-time authentication on the SSH client. This allows the SSH client to access the SSH server and saves the SSH server ' s public key on the SSH client. In this way, the next time the SSH client accesses the SSH server, the SSH client can use the saved public key to authenticate the SSH server.
On an OSPF network, if two indirectly connected routers with the same router ID run in the same area, Type 1 LSA calculation fails.
In addition to a route reflector, the confederation is another method that reduces the number of IBGP connections in an AS.
Which of the following statements are true about the confederation technology? (Choose all that apply)
As shown in the figure, R1 imports the direct route 10.1.1.0/24 to OSPF. An engineer enables bidirectional route re-advertisement on R2 and R3, and configures the following commands on R3. After the network becomes stable, which of the following is the Pre value of the route 10.1.1.0/24 in the routing table of R4?
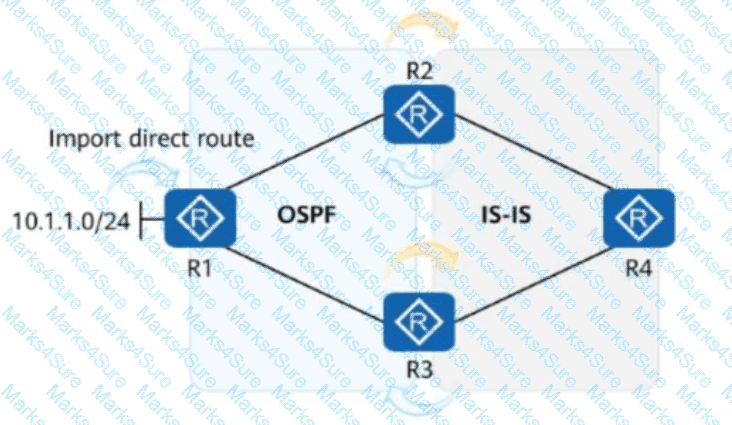
[R3]acl 2000
[R3-acl-basic-2000] rule permit source 10.1.1.0 0
[R3-acl-basic-2000] quit
[R3]route-policy hcip permit node 10
[R3-route-policy-10] if-match acl 2000
[R3-route-policy-10] apply pr eference 14
[R3-route-policy-10] quit
[R3]ospf 1
[R3-ospf-1] preference ase route-policy hcip
A monitoring plane usually comprises the monitoring units of main control boards and interface boards. This plane can monitor the system environment independently. Which of the following environment monitoring functions can be provided by the monitoring plane?
In inter-AC roaming scenarios, an AC can function as the mobility server of multiple mobility groups, but can be added only to one mobility group.
A BGP device receives a route carrying an unknown attribute from a peer but does not know whether other devices need the attribute. In this case, the BGP device retains this attribute when advertising the route to other peers. Which of the following attributes is of this type?
On an OSPF network, if the network type is NBMA , a router unicasts all protocol packets; if the network type is broadcast , a router multicasts all protocol packets.
IGMP group entries play an important role in multicast forwarding. An administrator runs a command to view information about a multicast entry. The information is as follows:
sql
Copy
< HUAWEI > display igmp group
Interface group report information
Vlanif100(10.1.6.2):
Total 1 IGMP Group reported
Group Address Last Reporter Uptime Expires
225.1.1.2 10.1.6.10 00:02:04 00:01:17
Given this, which of the following statements are true?
On the OSPF network shown in the figure, an adjacency has been established between R1 and R2. An engineer configures the commands in the figure on R2. In this case, which of the following routing entries may exist in the routing table of R2?
On a WLAN, MAC address authentication controls network access rights of a user based on the user ' s access interface and terminal MAC address.
Which of the following statements is false about MAC address authentication?
On a network, some switches are enabled with RSTP and some switches are enabled with STP. What will happen?
ACLs are a common matching tool in routing policies. An ACL can be configured on a router to match routes.
OSPF has several types of special areas, which are used to reduce the LSDB size and improve device performance.
Which of the following LSAs cannot be in a totally stub area?
Which of the following parameters are compared during designated port election on an STP network?
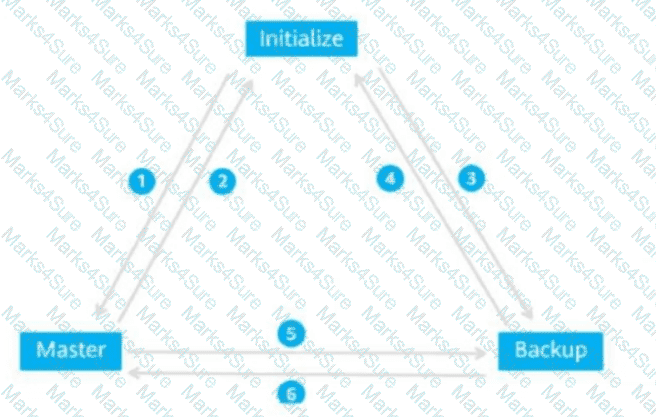
The figure shows the VRRP status switchover events . Match these events with their sequence numbers.
On an enterprise WLAN where Portal authentication is deployed, an AC functions as an access device and communicates with a Portal server using the Portal protocol. Which of the following statements are true about the Portal protocol?
In VRRP networking, if VRRP is not configured to track an uplink interface and the uplink interface or link of the master device in a VRRP group fails, no switchover will be triggered. As a result, a traffic blackhole occurs.
A filter named si is configured on a device using the as-path-filter command and is applied to a specified BGP peer. The detailed configurations are as follows:
csharp
Copy
[SW1] ip as-path-filter si permit _65500$
[SW1] bgp 65100
[SW1-bgp] ipv4-family unicast
[SW1-bgp-af-ipv4] peer 10.1.1.2 as-path-filter si import
After the configuration is complete, which of the following statements is true about the way the local device processes the routes received from the peer?
On an OSPF network, if a router functions as an ABR, the router must also be a BR.
OSPF has five types of packets, which have the same header format. If the Auth Type field in the packet header is 1, which of the following authentication modes is used?
Roaming technology is typically used on a large WLAN to ensure that STA (station) services are not interrupted when STAs move between coverage areas of different APs.
On an IS-IS network, routers send LSPs to exchange link state information. LSPs are classified into Level-1 LSPs and Level-2 LSPs and have the same format. Which of the following parts constitute the LSP ID in an LSP?
Similar to the OSPF DR, the IS-IS DIS needs to be elected on a broadcast network. However, the OSPF DR is preemptive by default, whereas the IS-IS DIS is not preemptive by default.
BGP is generally applied to complex networks where routes change frequently. Frequent route flapping consumes a large number of bandwidth and CPU resources, and even affects the normal operation of the network. This is an unavoidable problem that cannot be solved in BGP.
As shown in the figure, VRRP is associated with a BFD session. When a backup device detects a fault through BFD, the backup device immediately assumes the master role after the Master_Down_Timer timer expires.
When two routers exchange LSDB information using DD packets, a master/slave relationship is formed first, the router with a larger router ID is the master, and determine the MS bit.
As shown in the figure, the stateful inspection firewall forwards the packet because the packet matches the session status of the firewall.
On an enterprise network, the directly connected interfaces of two OSPF routers are on different network segments and have different masks. To establish an OSPF neighbor relationship between the two interfaces, you can change their network types to which of the following?
Which of the following fields in DD packets is used for implicit acknowledgment to ensure the reliability and integrity of DD packet transmission on an OSPF network?
A route-policy consists of one or more nodes. What is the maximum number of nodes in a route-policy?
In BGP, the origin attribute of the routes imported using the import-route command is incomplete.
On an OSPF network, if a router receives an update of an LSA that exists in the local LSDB, the router updates the LSDB and floods the LSA.
On an OSPF network, interfaces are classified into four types based on link layer protocols. Which of the following types can interfaces on an IS-IS network be classified into based on physical links?
BGP itself does not discover routes. Therefore, other routes need to be imported to the BGP routing table for route exchanges between ASs. In import mode, routes are imported to the BGP routing table by protocol. Which of the following routes can be imported to the BGP routing table using the import mode?
On a Huawei router, if no ACL is configured or an ACL is configured but no ACL rule is configured, the ACL matching result is Unmatched.
An enterprise uses Huawei routers to deploy an IS-IS network for network-wide communication. An engineer wants to change the interface cost to control route selection. By default, which of the following values is the maximum cost that can be configured?
BFD can associate with multiple protocols to quickly detect faults.
Which of the following functions are supported? (Select all that apply)
To reduce the workload of configuring VPN instances, the administrator can import interface IP addresses and features to the device in batches using a script, and then manually bind the interfaces to VPN instances.
PBR is a mechanism for selecting routes based on user-defined policies. There are two types of PBR: interface-based PBR and local PBR. Which of the following statements is false about these two types of PBR?
RSTP provides different functions in different scenarios. Which of the following statements Is false?
In the SNMP management model, which of the following elements defines the attributes of a managed device?
In the OSPF protocol, intra-area route calculation involves only Router LSA, Network LSA, and Summary LSA.
After the administrator of an enterprise deploys a DHCP server, employees complain that their clients cannot obtain IP addresses from the DHCP server. Which of the following may cause this problem?
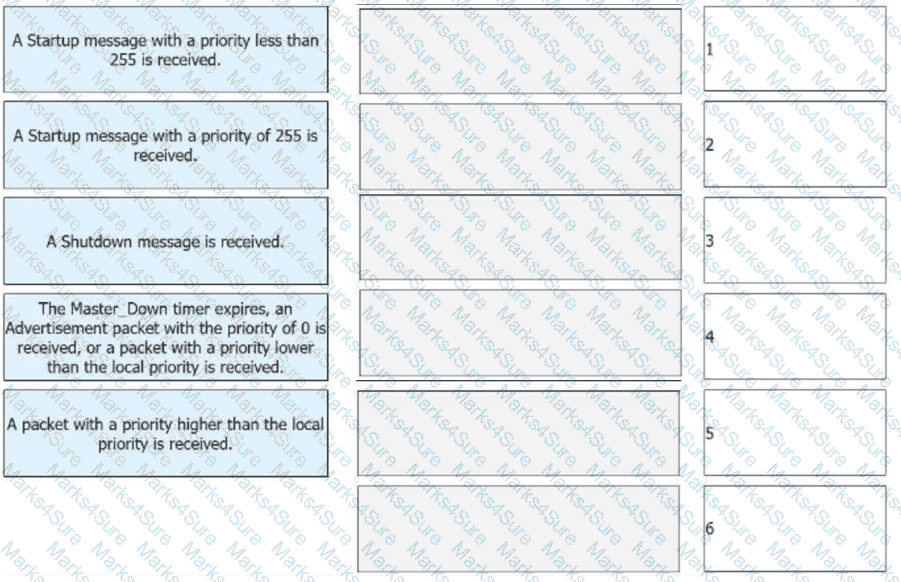
The following figure shows the OSPF network of an enterprise and the OSPF configurations of R1. Which of the following statements is false about the network?
iMaster NCE-Campus can be used as an authentication server on a WLAN to authenticate STAs.
Which of the following routing protocols support the default route through command configuration?
In IP multicast, RPF routes can be elected only from among unicast routes and multicast static routes.
VRRP defines three states. Only the device in which state can forward packets destined for a virtual IP address?
(Write in full and capitalize the first letter.)
Which of the following statements regarding the BGP error display of a router is false?
On an STP network, only the designated port processes inferior BPDUs. On an RSTP network, a port with any role processes inferior BPDUs.
BFD for OSPF is deployed on a directly connected link. If the physical link is disconnected, drag the following BFD processes to the corresponding sequence numbers.
This configuration is part of RTA configuration. Which of the following statements regarding the configuration are true?
[RTA] ospf 100
[RTA-ospf-100]silent-interface GigabitEthernet 1/0/0
Which of the following community attributes enables a device to send a received route with this attribute to any BGP peer ?
When a BGP device sends an Open message to establish a peer connection, which of the following information is carried?
In BGP, the Origin attribute is used to identify the origin of a route. Which of the following statements are true about the Origin attribute?
Security policy is the core feature of firewalls. Only valid traffic that complies with security policies can be forwarded by firewalls. Which of the following statements are true about security policy matching rules?
An ACL can be used to match routes or data, but cannot be used to match both the IP address prefix length and mask length.
Multicast applies to any point-to-multipoint data transmission. Which of the following types of application data can be forwarded in multicast mode?
On the network shown in the following figure, the management VLAN is VLAN 10, and the AP is configured to obtain an IP address on the network segment 10.1.1.0/24 through DHCP. The AP, AC, and AR function as the DHCP client, DHCP relay agent, and DHCP server, respectively. Which of the following configurations for the DHCP relay agent and DHCP server are correct?
Which of the following statements about the forwarding plane of a switch is false?
When creating a single-hop BFD session for the first time, bind the single-hop BFD session to the peer IP address and the local address. To modify a configured BFD session, delete it and create a new one.
Preferences of routing protocols determine the sequence In which a router selects a route among routes to the same destination /earned through different routing protocols.
In BGP, Notification messages are used to request peers to resend routing information after routing policies are changed.
A session is an entry used to record the connection status of a protocol and is fundamental for the firewall to forward packets. Which of the following protocol packets will the firewall create sessions for?
An enterprise network runs OSPF to implement network communication. Which of the following types of LSAs may be generated by an ABR?
See the command output of a router below. Which of the following statements is true?
< R2 > display ospf interface GigabitEthernet 0/0/0 verbose
OSPF Process 1 with Router ID 10.0.2.2
Interface: 10.0.12.2 (GigabitEthernet 0/0/0)
Cost: 1 State: BDR Type: Broadcast MTU: 1500
Priority: 1
Designated Router: 10.0.12.1
Backup Designated Router: 10.0.12.2
Timers: Hello 10 , Dead 40 , Poll 120 , Retransmit 5 , Transmit Delay 1
In VRRP networking, devices assume the Master and Backup roles after election. Match the two roles with their working mechanisms.(Token is reusable)
An enterprise office network runs OSPF and is divided into multiple OSPF areas. Enterprise network engineers can configure route summarization on ASBRs to reduce the number of inter-area Type 3 LSAs, which in turn reduces the routing table size and improves device resource utilization.
In BGP, Keepalive messages are used to maintain BGP peer relationships. When a BGP router receives a Keepalive message from a peer, the BGP router sets the state of the peer to Established and periodically sends Keepalive messages to maintain the connection. By default, the device sends Keepalive messages every seconds.
When deploying a VRRP network, an enterprise administrator sets the virtual IP address to 192.168.1.254 and VRID to 1. Which of the following is the virtual MAC address after the network becomes stable?
The VRID of the VRRP virtual router is 3 and the virtual IP address is 100.1.1.10. What is the virtual MAC address?
A large shopping mall configures a VLAN pool to prevent network performance deterioration caused by potentially large broadcast domains. A network engineer runs the display vlan pool name STA command to check information about the VLAN pool. The following command output is displayed:
< AC > display vlan pool name STA Name : STA Total : 2 Assignment: hash Threshold Notify Count: 3 Threshold Notify time(min): 3 VLAN ID : 2 4
Which of the following statements are true?
The BFD Echo function checks the connectivity of the forwarding link by looping back packets. Which of the following statements are true about this function?
In addition to numerous normal service packets, the CPUs of devices on a network may also receive large numbers of attack packets. To ensure that the CPUs can properly respond to normal services, the devices provide the local attack defense function.
Which of the following statements are true about this function? (Select all that apply)
Which of the following statements regarding multicast MAC addresses are false?
In IP multicast transmission , packets are transmitted from a source to a group of receivers . Which of the following statements are true about IP multicast technologies?