H12-891_V1.0 HCIE-Datacom V1.0 Questions and Answers
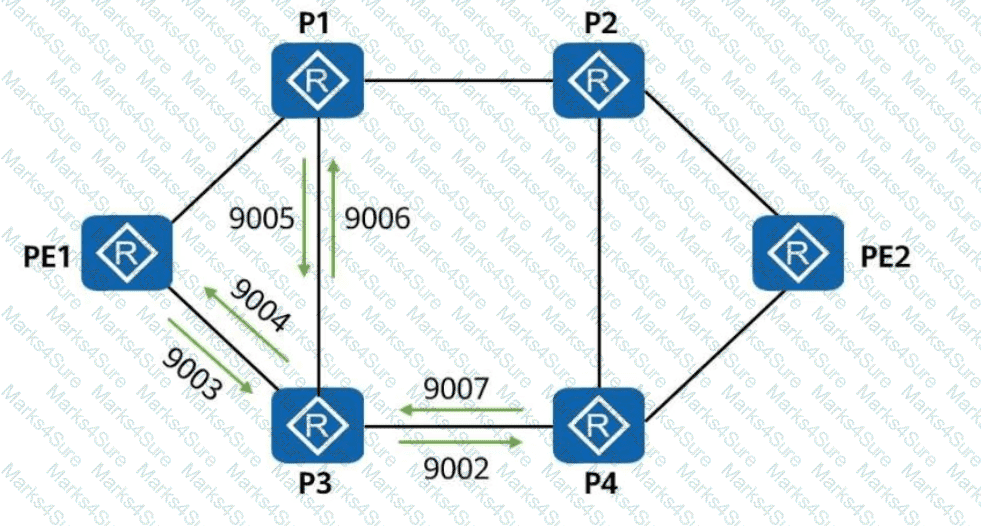
The following figure shows the inter-AS MPLS L3VPN Option C (Solution 2). ASBR-PE2 is connected to CE3 and runs eBGP.
To enable all CEs to communicate with each other, which of the following address families must peer relationships be enabled in the BGP process of ASBR-PE2?
iMaster NCE-Campus provides the terminal identification function to display the terminal type, operating system, and manufacturer information.
A network administrator runs the display telemetry destination command on a device to check information about a destination group that sampled data is sent to. The command output is as follows. Which of the following statements is incorrect?
[~CE-telemetry-sensor-group-Sensor1]display telemetry destination
Dest-name Dest-addr Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20000 RESOLVED - GRPC
In the Huawei SD-WAN Solution, which of the following routing protocols is used to advertise VPN routes between CPEs?
IPsec SAs can be established in either manual mode or IKE auto-negotiation mode. Which of the following statements about the two modes is incorrect?
Which of the following statements regarding OSPF neighbor relationship faults is incorrect?
iMaster NCE-WAN is the core component of the Huawei SD-WAN Solution and is responsible for SD-WAN network management and service orchestration.
Which of the following statements about SR-MPLS Policy path planning are correct?
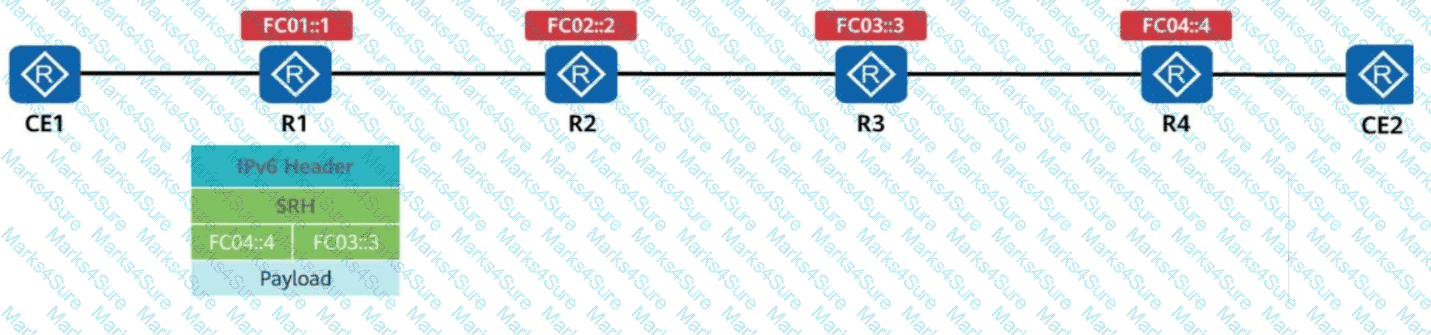
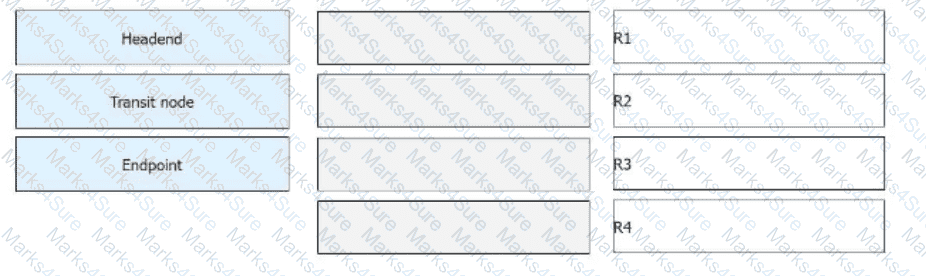
SR-MPLS is enabled on all routers. The label information encapsulated by R1 into a data packet is shown in the figure.
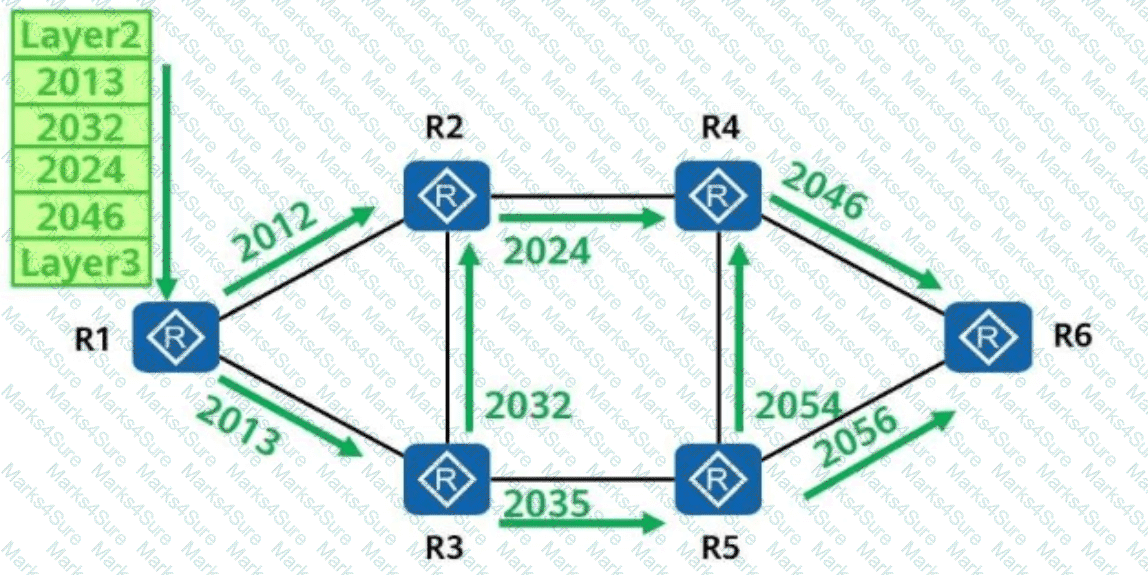
Which of the following is the forwarding path of the data packet?
Which of the following is the purpose of configuring IS-IS fragmentation on an IS-IS device?
In an MPLS domain, LSRs can be classified into ingress, transit, and egress LSRs based on how they process data. For the same FEC, an LSR can be both an ingress and a transit LSR of the FEC.
Which of the following statements are correct about the command:
ping -aX -cY -sZ -vpn-instance M 10.5.16.2
The figure shows an L3VPN over an SRv6 BE (Best Effort) network. According to the information displayed on PE2, which of the following statements is incorrect?
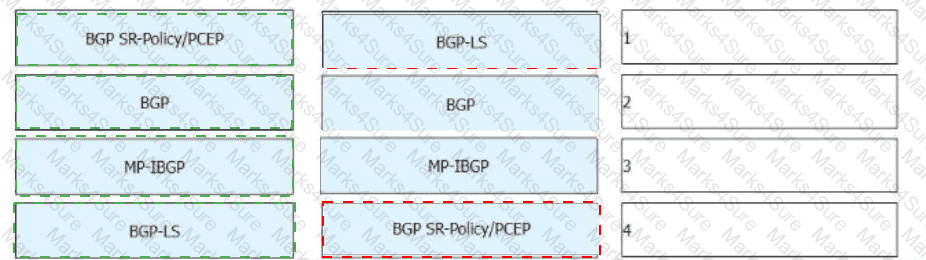
In a scenario where SR Policies are dynamically established through the controller, which of the following statements about the SR Policy solution architecture is incorrect?
IPsec uses an asymmetric encryption algorithm to encrypt the symmetric algorithm key, which it uses to encrypt/decrypt data, ensuring security and performance.
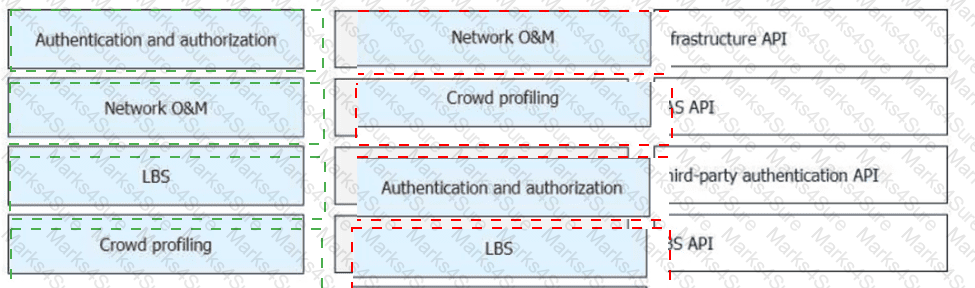
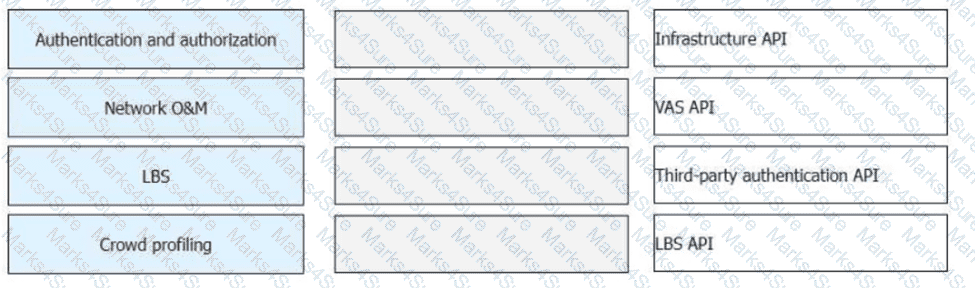
Huawei CloudCampus Solution has multiple application scenarios, and iMaster NCE-Campus provides different APIs for each application scenario. Match the following application scenarios with the open APIs provided by iMaster NCE-Campus.
In the LDP session establishment process, the initiator sends an Initialization message for parameter negotiation. Which message will be sent by the responder if it does not accept negotiation parameters?
For telemetry data push, data can be transferred between devices and collectors using the TLS protocol. TLS must be configured for data encryption if data is pushed based on gRPC.
On the network shown in the following figure, a remote LDP session needs to be established between SWA and SWC. Which of the following statements is correct?
[SWA] mpls lsr-id 1.1.1.1
[SWA] mpls
[SWA-mpls] mpls ldp
[SWC] mpls lsr-id 33.3.3.3
[SWC] mpls
[SWC-mpls] mpls ldp
SWA ---- SWB ---- SWC
< ------ Remote LDP Session ------ >
An SRLB is a set of user-specified local labels reserved for SR-MPLS. These labels are locally configured and have only local significance. Therefore, they are not advertised through the IGP.
Which of the following statements about configuring user access authentication is incorrect?
According to the following information displayed on a router, which of the following are the causes of the failure in establishing an OSPF adjacency relationship?
OSPF error statistics:
1: Hello timer mismatch
0: Netmask mismatch
0: Bad checksum
0: Bad authentication type
0: Unknown neighbor
0: Extern option mismatch
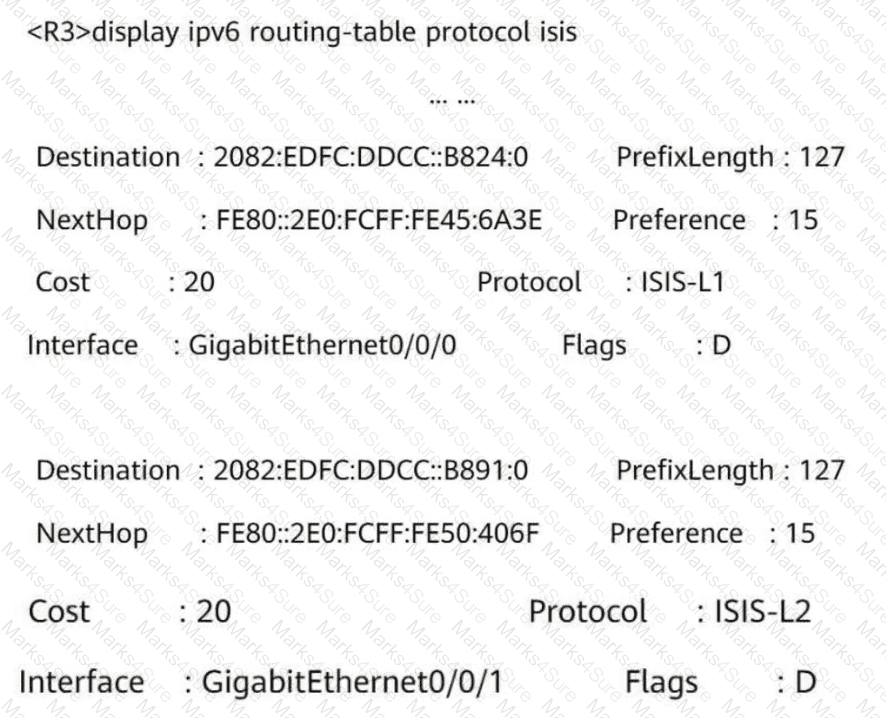
What can be determined from the following figure?
< R1 > display ipv6 routing-table protocol isis
Public Routing Table : ISIS
Summary Count: 6
ISIS Routing Table ' s Status : < Active >
Summary Count: 6
Destination : 3000:FDEA::4
NextHop : FE80::2E0:FCFF:FE98:2577
Cost : 20
Interface : GigabitEthernet0/0/1
PrefixLength : 128
Preference : 15
Protocol : ISIS-L2
Flags : D
Which of the following can be used to transmit traffic to a VXLAN network and implement intra-subnet communication on the same VXLAN network?
The display current-configuration command displays the running configurations in memory.
Which of the following statements about static VXLAN tunnel configuration are correct?
When static IPsec VPN is used for WAN interconnection in the Huawei CloudCampus Solution, the AP, Router, and ____ can be used as egress devices.
Free mobility implements policy management and permission control based on users ' VLAN IDs and IP addresses.
On a broadcast network, if the DR priorities of two interfaces connecting two routers are set to 0, in which of the following states will the OSPF neighbor relationship stay?
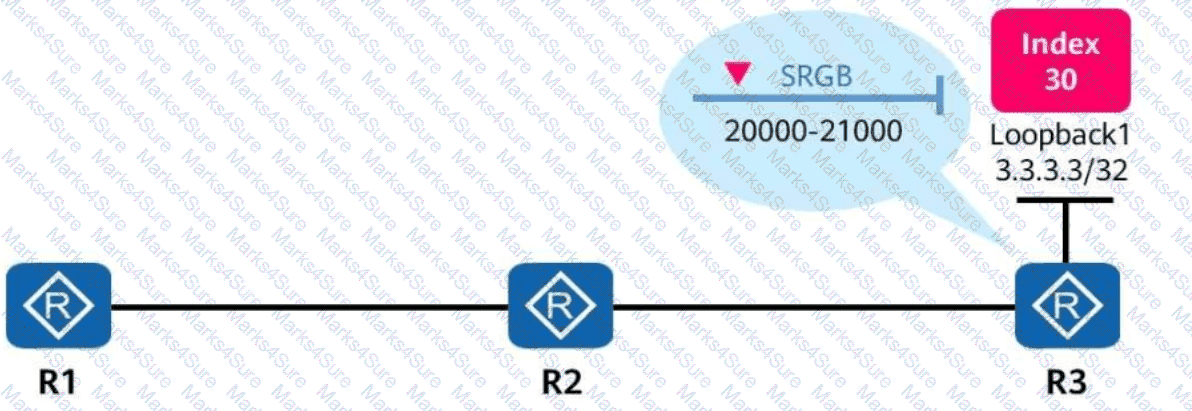
In the figure, SR-MPLS is enabled on R1, R2, and R3. The SRGB (Segment Routing Global Block) range on R3 is from 20000 to 21000, and the prefix SID index configured on the loopback1 interface of R3 is 30.
In this case, the MPLS label corresponding to the loopback1 interface of R3 is _____.
(Enter an Arabic numeral without symbols.)
The telemetry network model is broadly and narrowly defined. Which of the following modules are involved in telemetry in a narrow sense (device-side telemetry)?
On the network shown in the figure, OSPF-based SR-MPLS TE is enabled on all routers. Which of the following adjacency labels are allocated by P3?
In Huawei Open Programmability System (OPS), /ifm/interfaces/interface is the URL used to identify a device ' s managed object.
In the admission design for large- and medium-sized campus networks, which of the following authentication modes can be used for PCs connected to IP phones?
Which of the following technologies can be used to measure performance based on actual service traffic in Huawei ' s CloudWAN solution?
K company has two types of network services: UDP-based real-time video streaming services and TCP-based FTP download services. The company ' s network administrator often receives complaints that the FTP download speed is slow or unstable. What are the possible causes?
The RR (Route Reflector) is critical to the Huawei SD-WAN Solution, and its deployment mode varies based on the scenario. In which of the following modes can an RR be deployed?
When a client invokes the iMaster NCE-Campus RESTful API, it sends an HTTP request. The server then returns the status code 401. Which of the following errors has occurred?
Before connecting an SSH client to an SSH server in public key authentication mode, a client needs to create a key pair. Which of the following commands is used to create a DSS key pair on the client using Git Bash?
Huawei Open Programmability System (OPS) uses standard HTTP methods to access managed objects to manage network devices. Which of the following HTTP methods is used to configure the value of a network device ' s managed object?
A network administrator needs to retrieve a token ID from iMaster NCE using the following Python code:
import requests
nbi_name = " demol3@north.com "
nbi_pwd = " qqcOVcVel@ "
host = " 139.9.213.72 "
port = " 18002 "
URI = " /controller/v2/tokens "
post_token_url = " https:// " + host + " : " + port + URI
headers_post = { ' Content-Type ' : ' application/json ' , ' Accept ' : ' application/json ' }
r = requests.post(post_token_url, headers=headers_post, json={ " userName " : nbi_name, " password " : nbi_pwd}, verify=incorrect)
Which of the following statements is incorrect?
When an SSH client logs in to an SSH server that is configured only with username and password authentication in SSH mode, the key exchange phase is not involved (no key is generated).
In the Huawei CloudCampus Solution, which of the following deployment modes are supported by Huawei switches?
Refer to the following command output on the router R1. Which of the following statements is incorrect?
< R1 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:23 UTC-08:00
Description: ! 0.0.3.3
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.1/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.1.1 (LoopBack0), destination 10.0.3.3
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
Current system time: 15:21:37-08:00
300 seconds input rate 0 bits/sec, 0 packets/sec
300 seconds output rate 0 bits/sec, 0 packets/sec
13 seconds input rate 0 bits/sec, 0 packets/sec
13 seconds output rate 448 bits/sec, 0 packets/sec
9 packets output, 824 bytes
0 output error
Input bandwidth utilization : -
Output bandwidth utilization : -
Huawei Open Programmability System (OPS) uses standard HTTP methods to access managed objects and manage network devices.
Which of the following HTTP methods is used to configure the value of a network device’s managed object?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, run the command on the VTEP to view BGP EVPN routes. The route entries shown in the following figure are displayed. Which of the following statements about these routing entries are correct?
Network (EthTagId/IP Prefix/IP PrefixLen)
NextHop
* > i 0:172.16.2.0:24 1.1.1.2
* > i 0:172.16.13.0:24 1.1.1.2
* > i 0:192.168.122.0:30 1.1.1.2
In Huawei SD-WAN Solution, which of the following tunneling technologies is used to establish data channels?
How long is an IPv6 prefix assigned to a host when an IPv6 address is configured for the host in SLAAC mode?
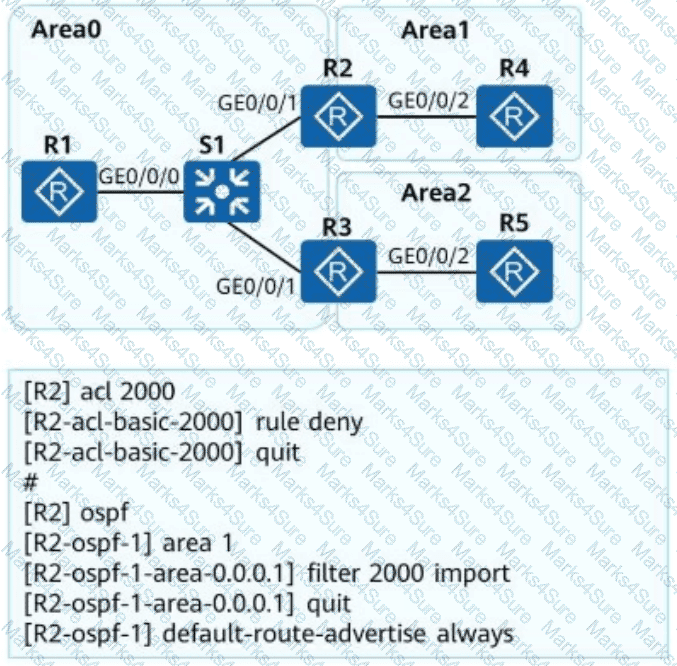
OSPF is deployed on a campus network to implement network interconnection. An engineer configures R2 as shown in the figure. Which of the following statements is incorrect about LSAs on the OSPF network?
OSPFv2 is an IGP running on IPv4 networks, whereas OSPFv3 is an IGP running on IPv6 networks. OSPFv2 and OSPFv3 have similar LSA types, but their LSA functions are slightly different. Which of the following is not an OSPFv3 LSA type?
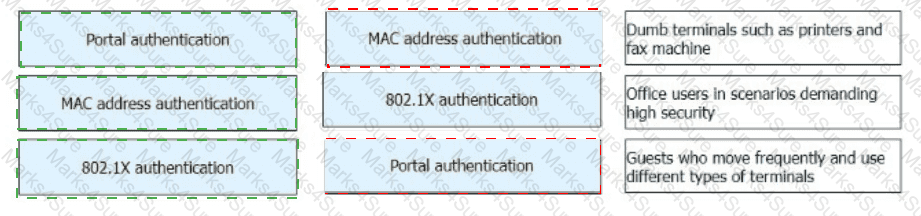
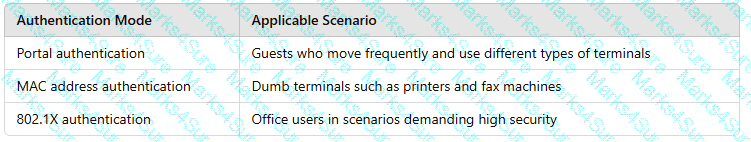
Drag the authentication modes on the left into their applicable scenarios on the right.

BGP routing policies can be used to control the advertisement and acceptance of routes.
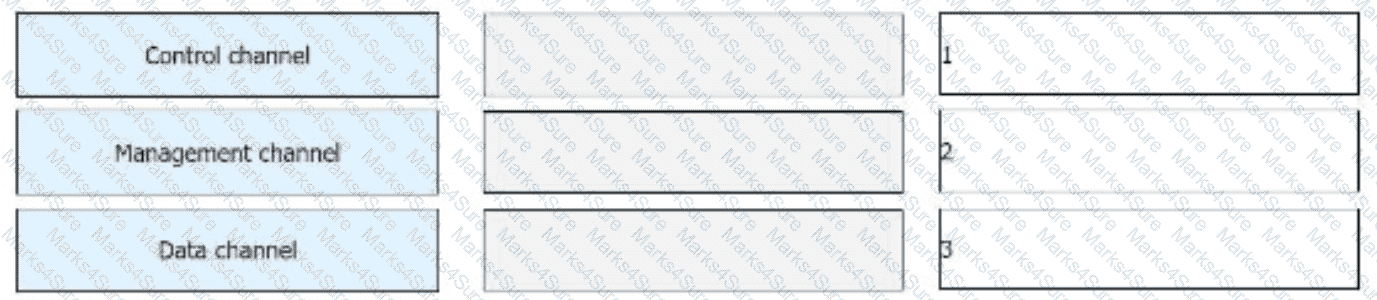
On a campus network, iMaster NCE-Campus is used to deploy two VNs (Virtual Networks): R & D VN and Marketing VN. Users in these two VNs belong to two separate security groups.
The campus network requires R & D personnel and sales personnel to communicate with each other. To meet this requirement, which of the following tasks does a network administrator need to perform?
NAFTIR policing can only be applied to the inbound direction. Its purpose is to monitor the traffic entering the device and ensure that the upstream device does not unnecessarily consume network resources.
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following statements about symmetric IRB forwarding are correct?
In OSPF, an ABR translates all Type 7 LSAs in a Not-So-Stubby Area (NSSA) into Type 5 LSAs.
When a client invokes the iMaster NCE-Campus RESTful API, it sends an HTTP request. The server then returns the status code 401.
Which of the following errors has occurred?
On traditional campus networks, network admission control (NAC), VLAN, and ACL technologies are used to control users ' network access rights. This results in heavy network O & M workload. Which of the following improvements does the free mobility solution of iMaster NCE-Campus make to traditional campus networks in terms of policy management and control?
Huawei Open Programmability System (OPS) provides openness and programmability capabilities for network devices and enables users to perform secondary development. To facilitate script completion, Huawei OPS provides the Python script template in which the OPSConnection class is created. The member function for creating device resources is def post(self, uri, req_data).
On an SR-MPLS network, manually configured prefix SIDs on different devices may conflict with each other. Assume that there are four routes (prefix/mask SID) as follows. Which of the following routes will be selected according to the conflict handling principle?
Which of the following inter-AS MPLS L3VPN solutions needs ASBRs to transmit VPNv4 routes?
Exhibit:
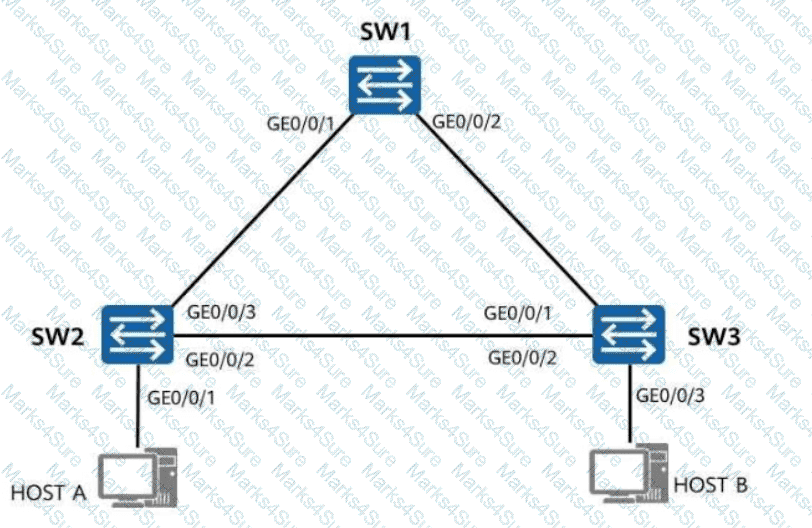
A loop occurs because Spanning Tree Protocol (STP) is not enabled on the network. Which of the following symptoms may occur?
Which MPLS label will be used by PE2 for forwarding traffic to 10.0.1.1 based on the following SR-MPLS database?
Given Data (LSDB Information):
Prefix-SID: 100
SRGB Base: 40000
The Ingress VTEP performs both Layer 2 and Layer 3 table lookup for packet forwarding. The forwarding mode is _____ IRB forwarding. (Capitalize the first letter.)
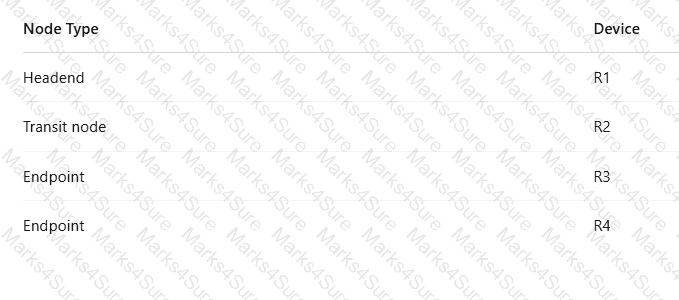
R1 receives a common IPv6 packet from the CE and generates a packet carrying the SRH (Segment Routing Header), as shown in the figure. The packet is forwarded along the path R1 → R2 → R3 → R4. Identify the node type of each device based on their role in SRv6 processing.
Which of the following statements is incorrect about intranet security design for a large or medium-sized virtualized campus network?
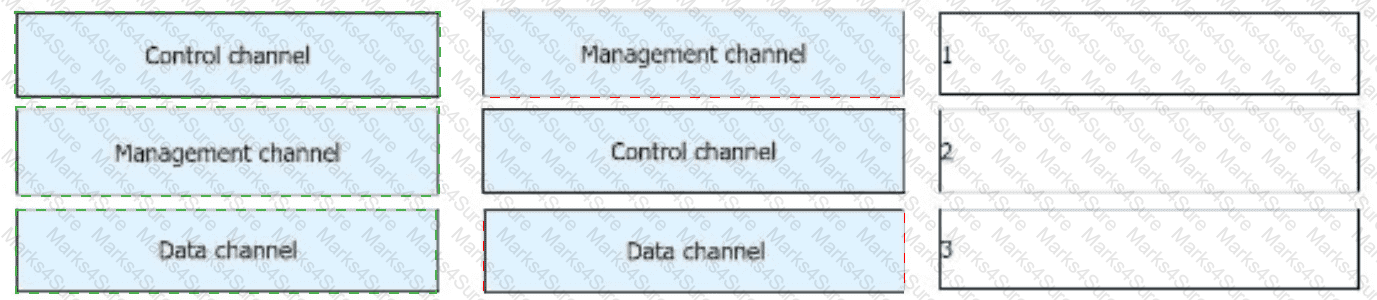
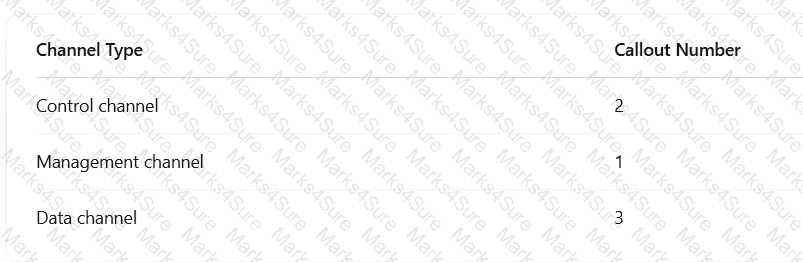
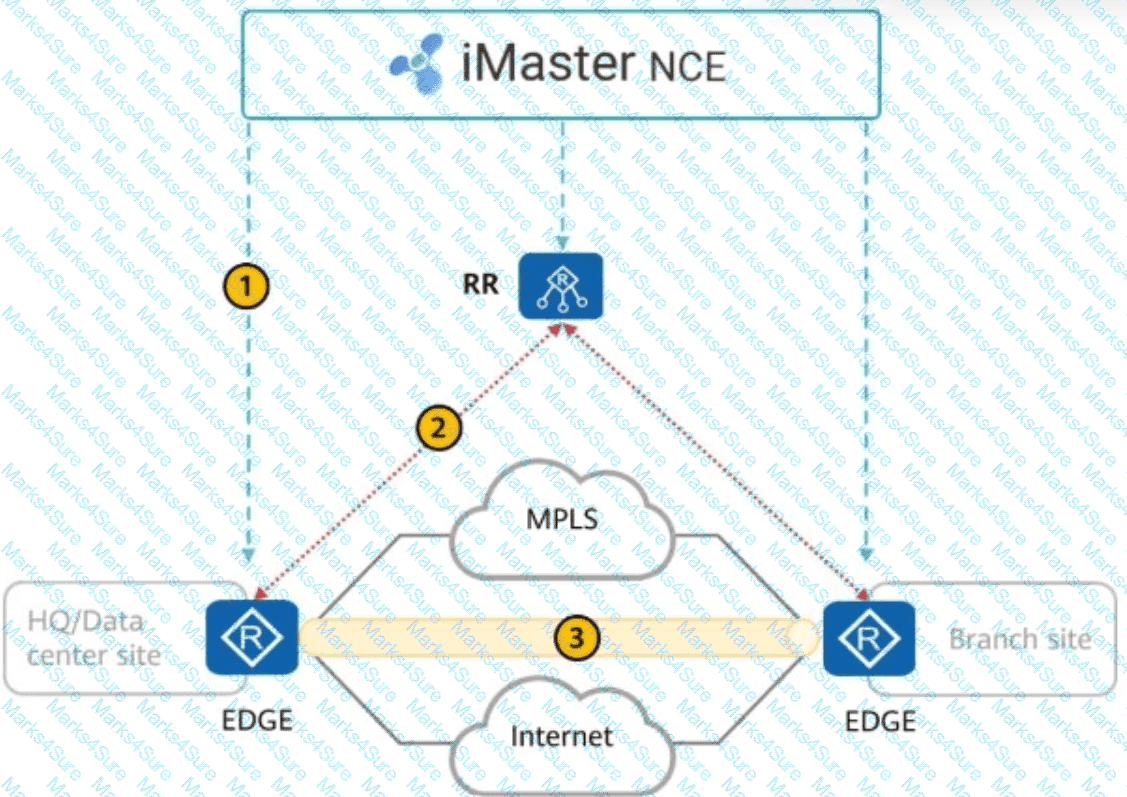
The Huawei SD-WAN solution has three types of channels. Drag the channel names to their corresponding callouts.
Which of the following factors does not need to be considered during the selection of core devices for the enterprise bearer WAN?
Telemetry data must be encoded in GPB binary format. This format reduces the number of bytes in telemetry messages and improves the transmission efficiency compared with messages encoded in JSON format.
The free mobility function is deployed on the iMaster NCE-Campus on a campus network. Which of the following information should an administrator pay attention to?
NETCONF uses an XML-based encoding format. NETCONF uses text files to represent complex hierarchical data. Which of the following statements are correct about the following XML file?
< ?xml version= " 1.0 " encoding= " UTF-8 " ? >
< note >
< to > Learners < /to >
< from > Huawei < /from >
< heading > Reminder < /heading >
< body > Don ' t forget Reading! < /body >
< /note >
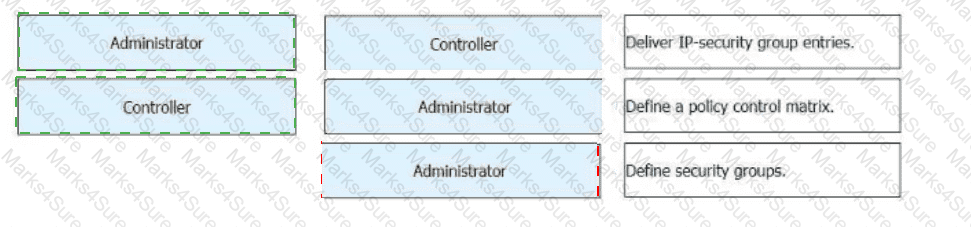
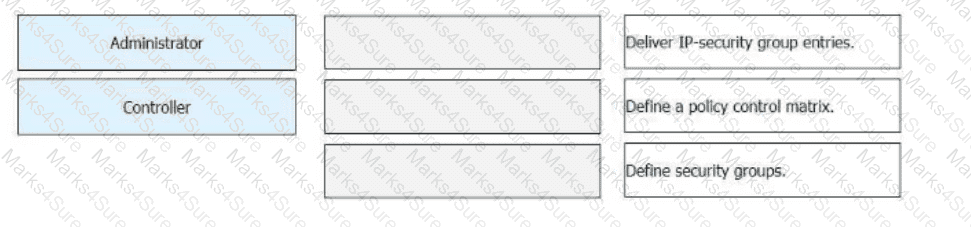
Free mobility is deployed on a campus network through iMaster NCE-Campus. During this deployment, which of the following steps are performed by administrators and which are automatically performed by iMaster NCE-Campus? Drag the administrators and iMaster NCE-Campus icons on the left to the corresponding steps on the right.
To enhance reliability, you can deploy Huawei iMaster NCE-WAN controllers in active/standby mode. Which of the following IP addresses must be configured to be the same for the active and standby controllers so that the controllers can be accessed properly? (Select All that Apply)
Congestion management technology can be used to discard data packets in the buffer queue to prevent the buffer queue from being exhausted.
Which of the following statements is incorrect about the user authentication points on the network?
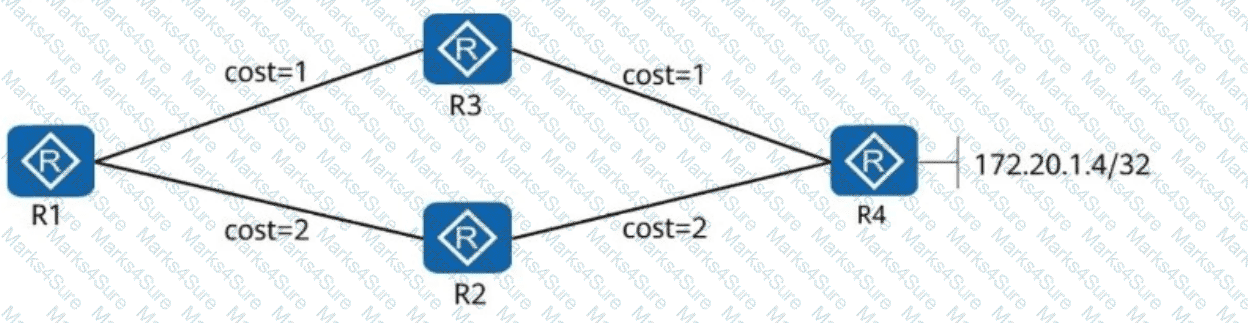
In the following figure, R1, R2, R3, and R4 all belong to OSPF area 0. The link costs are marked in the figure. The Loopback0 addresses of R1, R2, R3, and R4 are advertised to OSPF. R1, R2, and R3, which are R4 clients, use Loopback0 to establish an iBGP peer relationship with R4. The directly connected network segment 172.20.1.4/32 of R4 is advertised to BGP. Which of the following statements are correct about the direction of traffic from R1 to 172.20.1.4/32?
There are multiple SR-MPLS TE tunnel protection mechanisms. FRR (Fast Reroute) constructs a virtual node to convert multiple identical route advertisement nodes into a single route advertisement node, and then computes the backup next hop of the virtual node based on the TI-LFA algorithm. In this way, traffic can be quickly switched when a fault occurs.
What is the name of this protection mechanism?
iMaster NCE-CampusInsight uses SNMP technology to collect metrics and logs of network devices and detects network exceptions based on real service traffic.
AH is an IP-based transport-layer protocol. The protocol number is _____. (Enter only digits.)
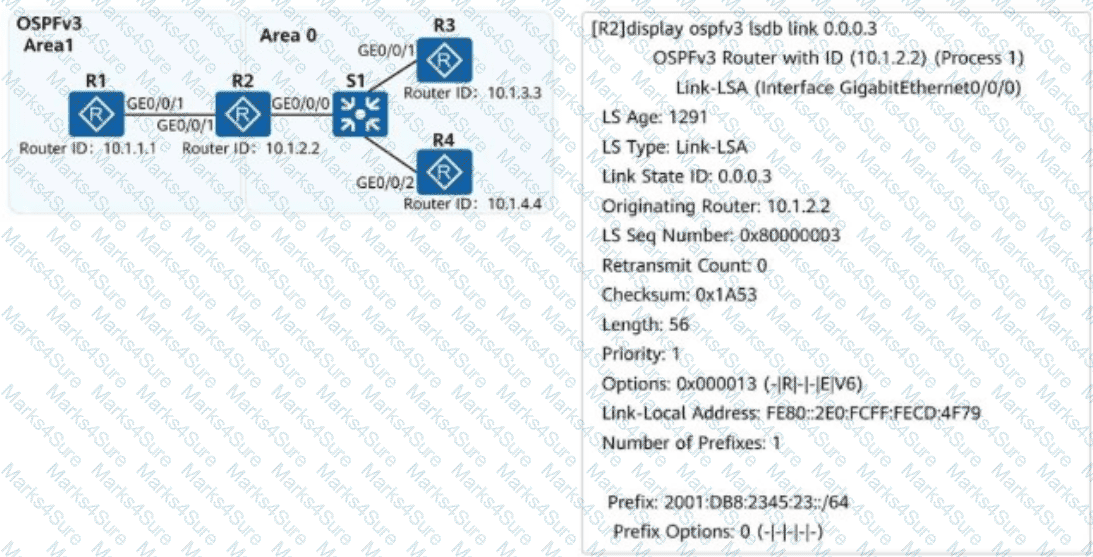
On the campus network shown, IPv6 is deployed for service tests. Four routers are deployed on the network, and OSPFv3 is used for IPv6 network connectivity. An engineer checks the LSDB of R2 and obtains a Link-LSA. Which of the following statements about the LSA are correct?
Flavors are additional behaviors defined to enhance the End series instructions in SRv6. Which of the following End instructions can the PSP flavor be attached to?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following fields is NOT carried in BGP EVPN Type 5 routes?
As shown in the figure, what is known about the default routes on R4?
Routing Table on R4:
< R4 > display ip routing-table protocol isis
Destination/Mask Proto Pre Cost Flags NextHop Interface
0.0.0.0/0 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
172.16.1.2/32 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
172.16.1.3/32 ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0