Which of the following are replication methods available in Vault Enterprise? Choose two correct answers.
You have been tasked with writing a policy that will allow read permissions for all secrets at path secret/bar. The users that are assigned this policy should also be able to list the secrets. What should this policy look like?
When looking at Vault token details, which key helps you find the paths the token is able to access?
Which of the following cannot define the maximum time-to-live (TTL) for a token?
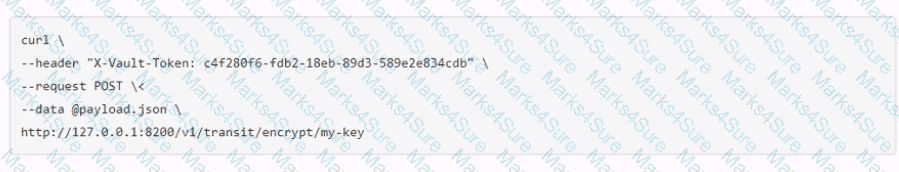
A user issues the following cURL command to encrypt data using the transit engine and the Vault AP:
Which payload.json file has the correct contents?
You are performing a high number of authentications in a short amount of time. You're experiencing slow throughput for token generation. How would you solve this problem?
Examine the command below. Output has been trimmed.
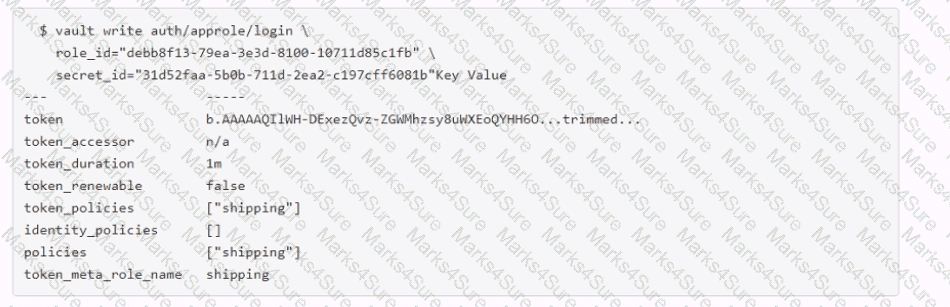
Which of the following statements describe the command and its output?
True or False? The Vault Secrets Operator does NOT encrypt client cache, such as Vault tokens and leases, by default in Kubernetes Secrets.
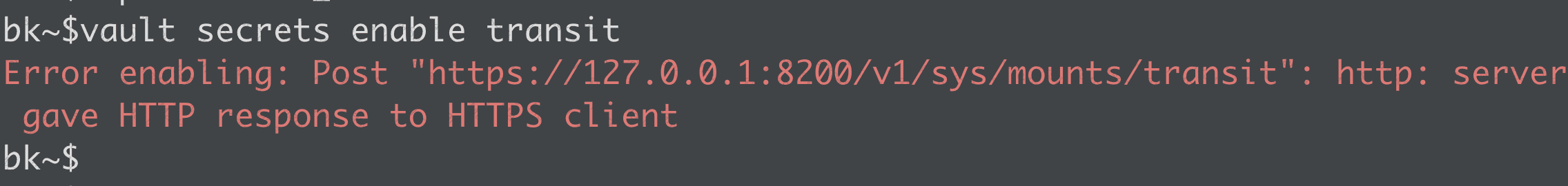
Which statement describes the results of this command: $ vault secrets enable transit
A developer team requests integration of their legacy application with Vault to encrypt and decrypt data for a backend database. They cannot modify the application for Vault authentication. What is the best way to achieve this integration?
You are using the Vault API to test authentication before modifying your CI/CD pipeline to properly authenticate to Vault. You manually authenticate to Vault and receive the response below. Based on the provided options, which of the following are true? (Select four)
$ curl \
--request POST \
--data @payload.json \
https://vault.krausen.com:8200/v1/auth/userpass/login/bryan.krausen | jq
*******************************************************************************
******* RESPONSE BELOW ********************************************************
*******************************************************************************
{
"request_id": "f758e8da-11b6-8341-d404-56f0c370a7fa",
"lease_id": "",
"renewable": false,
"lease_duration": 0,
"data": null,
"wrap_info": null,
"warnings": null,
"auth": {
"client_token": "hvs.CbzCNJCVWt63jyzyaJakgDwz",
"accessor": "rffwXzKFcxvaQi6Vgo8tY4Lt",
"policies": [
"training",
"default"
],
"token_policies": [
"training",
"default"
],
"metadata": {
"username": "bryan.krausen"
},
"lease_duration": 84600,
"renewable": true,
"entity_id": "f1795f6a-c576-d619-b2d5-74c0aee08edb",
"token_type": "service",
"orphan": true
}
}
Use this screenshot to answer the question below:
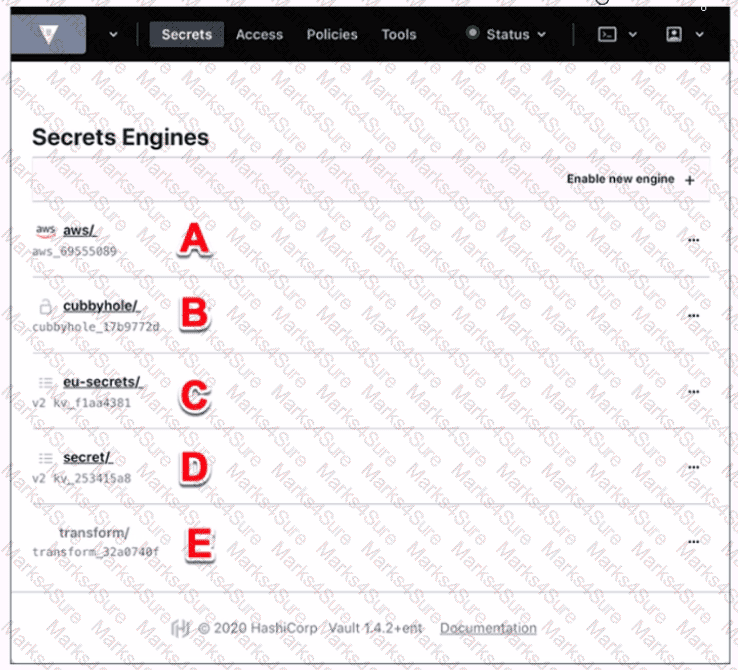
Where on this page would you click to view a secret located at secret/my-secret?
Your DevOps team would like to provision VMs in GCP via a CICD pipeline. They would like to integrate Vault to protect the credentials used by the tool. Which secrets engine would you recommend?
Your co-worker has asked you to perform certain operations in Vault and has provided you with a token accessor (not the token itself). What Vault operations would you be allowed to perform using only the provided accessor? (Select three)
Which of the following is true about the token authentication method in Vault? (Select three)
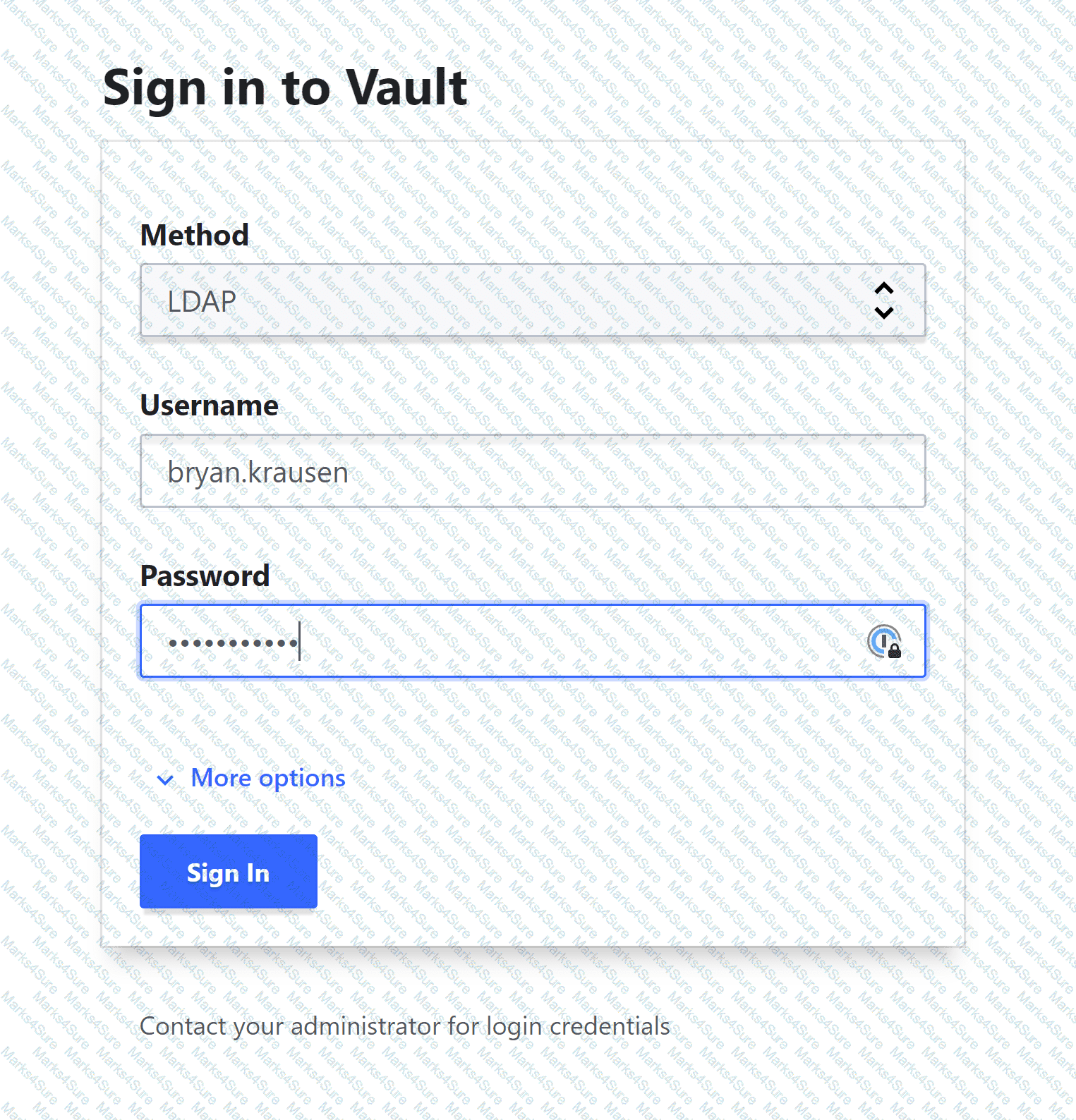
Your organization has enabled the LDAP auth method on the path of corp-auth/. When you access the Vault UI, you cannot log in despite providing the correct credentials. Based on the screenshot below, what action should you take to log in?
Your Azure Subscription ID is stored in Vault and you need to retrieve it via Vault API for an automated job. The Subscription ID is stored at secret/cloud/azure/subscription. The secret is stored on a KV Version 2 secrets engine. What curl command below would successfully retrieve the latest version of the secret?
A developer has requested access to manage secrets at the path kv/apps/webapp01. You create the policy below which gives them the proper access:
path "kv/apps/webapp01" {
capabilities = ["read", "create", "update", "list"]
}
However, when the developer logs in to the Vault UI, they see the following screenshot and cannot access the desired secret. Why can’t the developer see the secrets they need?
Your organization is integrating its legacy application with Vault to improve its security. However, you have discovered that the application has issues when the token changes for authentication during testing. What type of token could be used to help alleviate this issue without compromising security?
Before data is written to the storage backend, the data is encrypted by which Vault feature?
You are using Vault to generate dynamic credentials for a Microsoft SQL server to perform queries for a month-end report. The report seems to be taking much longer than expected due to degradation on the underlying server, and you are afraid that Vault might automatically revoke the credentials. How can you extend the time the credentials are valid to ensure your month-end query is successful?
True or False? Performing a rekey operation using the vault operator rekey command creates new unseal/recovery keys as well as a new root key?
You are using Vault CLI and enable the database secrets engine on the default path of database/. However, the DevOps team wants to enable another database secrets engine for testing but receives an error stating the path is already in use. How can you enable a second database secrets engine using the CLI?
To secure your applications, your organization uses certificates generated by a public CA. However, this strategy has proven expensive and you have to revoke certificates even though they have additional time left. What Vault plugin can be used to quickly generate X.509 certificates to secure your internal applications?
Your organization recently suffered a security breach on a specific application, and the security response team believes that MySQL database credentials were likely obtained during the event. The application generated the credentials using the database secrets engine in Vault mounted at the path database/. How can you quickly revoke all of the secrets generated by this secrets engine?
Security requirements demand that no secrets appear in the shell history. Which command does not meet this requirement?
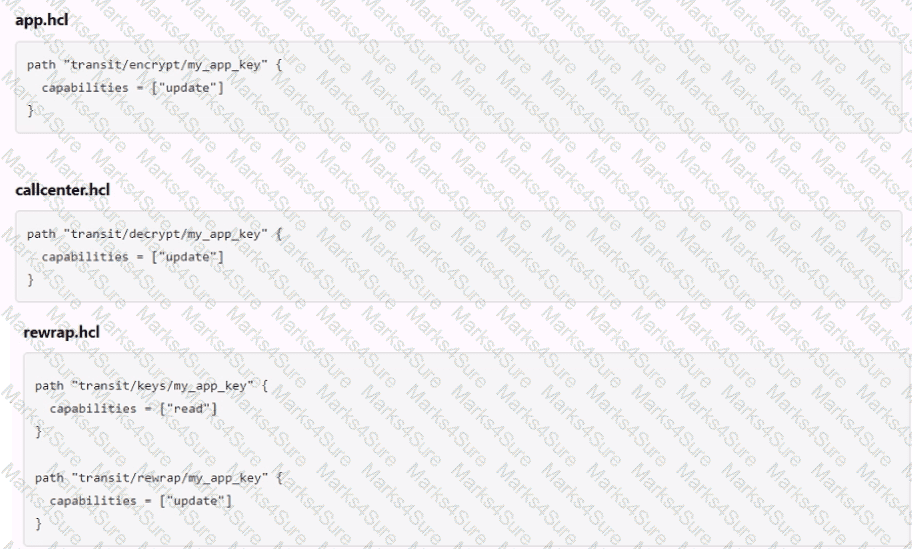
The following three policies exist in Vault. What do these policies allow an organization to do?
You are using Vault's Transit secrets engine to encrypt your data. You want to reduce the amount of content encrypted with a single key in case the key gets compromised. How would you do this?
Which of the following statements describe the CLI command below?
S vault login -method-1dap username-mitche11h
An application requires a specific key/value pair to be updated in order to process a batch job. The value should be either "true" or "false." However, when developers have been updating the value, sometimes they mistype the value or capitalize the value, causing the batch job not to run. What feature of a Vault policy can be used to restrict entry to the required values?
True or False? After initializing Vault or restarting the Vault service, each individual node in the cluster needs to be unsealed.
You have deployed an application that needs to encrypt data before writing to a database. What secrets engine should you use?
A new Vault administrator is writing a CURL command (shown below) to retrieve a secret stored in a KV v2 secrets engine at secret/audio/soundbooth but is receiving an error. What could be the cause of the error?
$ curl \
--header "X-Vault-Token: hvs.rffHw0iXqkRo19b2cjf93DM39WjpbN3J" \
https://vault.unlimited.com:8200/v1/secret/audio/soundbooth
Your application cannot manage authentication with Vault, but it can communicate with a local service to retrieve secrets. What solution can enable your app to generate dynamic credentials from Vault?
What is the result of the following Vault command?
$ vault auth enable kubernetes
Which of the following best describes the function of the Vault Secrets Operator in a Kubernetes environment?
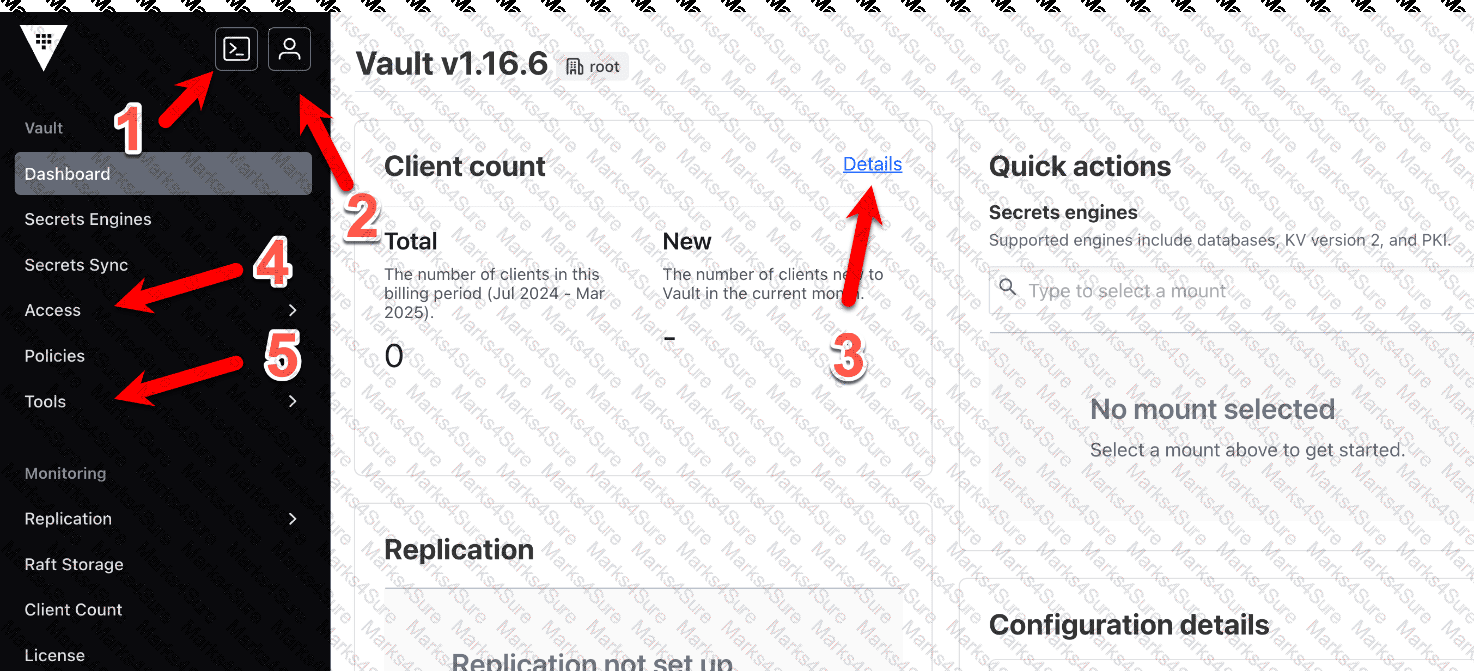
Without logging into another interface, what feature can Chad use to execute a simple CLI command to enable a new secrets engine?
When Vault is sealed, which are the only two operations available to a Vault administrator? (Select two)
Before the following command can be run to encrypt data, what (three) commands must be run to enable and configure the transit secrets engine in Vault? (Select three)
text
CollapseWrapCopy
$ vault write transit/encrypt/vendor \
plaintext="aGFzaGljb3JwIGNlcnRpZmllZA=="
You have a long-running app that cannot handle a regeneration of a token or secret. What type of token should be created for this application in order to authenticate and interact with Vault?
Which statement most accurately describes how the response wrapping feature functions in Vault?
You are trying to create a new orphan token but receiving a Permission Denied error. What capabilities are required to create this token without using a root token?
Based on the following output, what command can Steve use to determine if the KV store is configured for versioning?
text
CollapseWrapCopy
$ vault secrets list
Path Type Accessor Description
---- ---- -------- -----------
automation/ kv kv_56f991b9 Automation team for CI/CD
cloud/ kv kv_4426c541 Cloud team for static secrets
cubbyhole/ cubbyhole cubbyhole_9bd538e per-token priv secret storage
data_team/ kv kv_96d57692 Data warehouse KV for certs
identity/ identity identity_0042595e identity store
network/ kv kv_3e53aaab Network team secret storage
secret/ kv kv_d66e2adc key/value secret storage
sys/ system system_d6f218a9 system endpoints
Which of the following auth methods is the best choice for human interaction with Vault (as opposed to machine/system authentication)?
Which statement best explains the role and usage of storage backends in HashiCorp Vault?
What header must be included in an API request in order to provide authentication validation?
You need to decrypt customer data to provide it to an application. When you run the decryption command, you get the output below. Why does the response not directly reveal the cleartext data?
$ vault write transit/decrypt/phone_number ciphertext="vault:v1:tgx2vsxtlQRfyLSKvem..."
Key Value
--- -----
plaintext aGFzaGljb3JwIGNlcnRpZmllZDogdmF1bHQgYXNzb2NpYXRl
When a lease is created, what actions can be performed by using only the lease ID? (Choose two)
Kyle enabled the database secrets engine for dynamic credentials. Amy, the senior DBA, accidentally deleted the database users created by Vault, disrupting client applications. How can Kyle manually remove the leases in Vault?
You are enabling a secrets engine in Vault using the CLI. What subcommands are available when using the vault secrets command? (Select five)
Elijah manages a legacy application that requires strict control over when its service account credentials change. Which type of credential should be used for this legacy application?
What command would you use to enable the Kubernetes secrets engine at the path of /k8s-cluster?
Hanna is working with Vault and has been assigned a namespace called integration, where she stores all her secrets. Hanna configured her application to use the following API request, but the request is failing. What changes below will help Hanna correctly retrieve the secret? (Select two)
$ curl \
--header "X-Vault-Token:hvs.lzrmRe5Y3LMcDRmOttEjWoag" \
--request GET \
https://vault.example.com:8200/v1/secret/data/my-secret
Your organization operates active/active applications across multiple data centers for high availability. Which Vault feature should be used in the secondary data centers to provide local access to secrets?
Although batch and service tokens share many characteristics, which of the following are true only about batch tokens? (Select three)
Jarrad is an AWS engineer and has provisioned a new EC2 instance running MySQL since his application requires a specific MySQL version. He wants to integrate Vault into his workflow but is new to Vault. What secrets engine should Jarrad use to integrate this new database running in AWS?
Which of the following auth methods are intended for machine-to-machine authentication, and not necessarily human (operator) authentication? (Select four)
A DevOps engineer has set up LDAP and GitHub auth methods. The engineer must ensure user Sarah, who authenticates via either method, has consistent access permissions. Which approach correctly describes how to achieve this in Vault?
True or False? Although AppRole is designed for machines, humans can use it to authenticate to Vault if you wish.
You have TBs of data encrypted by Vault stored in a database and are worried about Vault becoming unavailable and not being able to decrypt the data. Is it possible to export the encryption key to store it somewhere else in the event Vault becomes unavailable?
When configuring Vault replication and monitoring its status, you keep seeing something called 'WALs'. What are WALs?
After encrypting data using the Transit secrets engine, you’ve received the following output. Which of the following is true based on the output displayed below?
Key: ciphertext Value: vault:v2:45f9zW6cglbrzCjI0yCyC6DBYtSBSxnMgUn9B5aHcGEit71xefPEmmjMbrk3
According to the screenshot below, what auth method did this client use to log in to Vault?
(Screenshot shows a lease path: auth/userpass/login/student01)
Which of the following is NOT a valid way in which a lease can be revoked in Vault?
You’ve hit the URL for the Vault UI, but you’re presented with this screen. Why doesn’t Vault present you with a way to log in?

You are deploying Vault in a local data center, but want to be sure you have a secondary Vault cluster in the event the primary cluster goes offline. In the secondary data center, you have applications that are running, as they are architected to run active/active. Which type of replication would be best in this scenario?
What command would have created the token displayed below?
$ vault token lookup hvs.nNeZ2I64ALCxuO7dqQEJGPrO
Key: policies Value: [default dev], num_uses: 5, ttl: 767h59m49s
Key Value
--- -----
accessor mfvaVMFgOcXHIeqlRasroSOn
creation_time 1604610457
creation_ttl 768h
display_name token
entity_id n/a
expire_time 2024-12-07T16:07:37.7540672-05:00
explicit_max_ttl 0s
id hvs.nNeZ2I64ALCxuO7dqQEJGPrO
issue_time 2024-11-05T16:07:37.7540672-05:00
meta < nil >
num_uses 5
orphan false
path auth/token/create
policies [default dev]
renewable true
ttl 767h59m49s
type service
How long does the Transit secrets engine store the resulting ciphertext by default?
True or False? When encrypting data with the Transit secrets engine, Vault always stores the ciphertext in a dedicated KV store along with the associated encryption key.
You logged into the Vault CLI and attempted to enable an auth method, but you received this error message. What can you do to resolve the error and configure Vault?
(Error: dial tcp 127.0.0.1:8200: connect: connection refused)
Tommy has written an AWS Lambda function that will perform certain tasks for the organization when data has been uploaded to an S3 bucket. Security policies for the organization do not allow Tommy to hardcode any type of credential within the Lambda code or environment variables. However, Tommy needs to retrieve a credential from Vault to write data to an on-premises database. What auth method should Tommy use in Vault to meet the requirements while not violating security policies?