Which of the following risks would Involve individuals attacking an oil company ' s IT system as a sign of solidarity against drilling in a local area?
Senior management is trying to decide whether to use the direct write-off or allowance method for recording bad debt on accounts receivables. Which of the following would be the best argument for using the direct write-off method?
The board and senior management agree to outsource the internal audit function. Which of the following is true regarding the company’s quality assurance and improvement program (QAIP)?
Which of the following parties is most likely to be responsible for maintaining the infrastructure required to prevent the failure of a real-time backup of a database?
During a review of payments to supplier invoices, the internal auditor identified that the IT process allows invoice processing staff to ignore the auto-generated alert triggered when the invoice amount is different from the purchase order value. The manager explained that staff must be able to bypass the alert because of small differences in transport charges. Which of the following would be the most appropriate internal audit recommendation?
During a review of the accounts payable process, an internal auditor gathered all of the vendor payment transactions for the past 24 months. The auditor then used an Analytics tool to identify the top five vendors that received the highest sum of payments. Which of the following analytics techniques did the auditor apply?
Which of the following statements is true regarding an organization ' s chief audit executive (CAE) when prioritizing the audit universe?
The chief audit executive (CAE) has embraced a total quality management approach to improving the internal audit activity ' s (lAArs) processes. He would like to reduce the time to complete audits and improve client ratings of the IAA. Which of the following staffing approaches is the CAE most likely lo select?
Which of the following measures the operating success of a company for a given period of time?
Which of the following scenarios would require the chief audit executive (CAE) to change the internal audit plan and seek approval for the changes from the board?
A bond that matures after one year has a face value of S250,000 and a coupon of $30,000. if the market price of the bond is 5265,000, which of the following would be the market interest rate?
An organization that soils products to a foreign subsidiary wants to charge a price that wilt decrease import tariffs. Which of the following is the best course of action for the organization?
According to Maslow ' s hierarchy of needs theory, which of the following best describes a strategy where a manager offers an assignment to a subordinate specifically to support his professional growth and future advancement?
Which of the following IT-related activities is most commonly performed by the second line of defense?
Which of the following attributes of data is the most significantly impacted by the internet of things?
Which of the following is on example of a smart device security control intended to prevent unauthorized users from gaining access to a device ' s data or applications?
Which of the following scenarios indicates an effective use of financial leverage?
Capital budgeting involves choosing among various capital projects to find the one(s) that will maximize a company ' s return on its financial investment. Which of the following parties approves the capital budget?
An employee was promoted within the organization and relocated to a new office in a different building. A few months later, security personnel discovered that the employee ' s smart card was being used to access the building where she previously worked. Which of the following security controls could prevent such an incident from occurring?
Which of the following actions should an internal auditor take to clean the data obtained for analytics purposes?
Which of the following best describes a cyberattacK in which an organization faces a denial-of-service threat created through malicious data encryption?
Which of the following best explains why an organization would enter into a capital lease contract?
How should a chief audit executive learn about emerging risk areas in an organization?
Which of the following situations best applies to an organization that uses a project, rather than a process, to accomplish its business activities?
According to IIA guidance on IT, which of the following best describes a situation where data backup plans exist to ensure that critical data can be restored at some point in the future, but recovery and restore processes have not been defined?
Which of the following would an organization execute to effectively mitigate and manage risks created by a crisis or event?
Which of the following would most likely be found in an organization that uses a decentralized organizational structure?
Which of the following is an advantage of a decentralized organizational structure, as opposed to a centralized structure?
A small chain of grocery stores made a reporting error and understated its ending inventory. What effect would this have on the income statement for the following year?
Which of the following organization structures would most likely be able to cope with rapid changes and uncertainties?
Which of the following concepts of managerial accounting is focused on achieving a point of low or no inventory?
Which type of bond sells at a discount from face value, then increases in value annually until it reaches maturity and provides the owner with the total payoff?
Which of the following situations best illustrates a " false positive " in the performance of a spam filter?
Which of the following describes the primary advantage of using data analytics in internal auditing?
According to IIA guidance, which of the following statements is true regarding the chief audit executive ' s (CAE’s) responsibility for following up on management action plans?
An intruder posing as the organization ' s CEO sent an email and tricked payroll staff into providing employees ' private tax information. What type of attack was perpetrated?
An organization has instituted a bring-your-own-device (BYOD) work environment. Which of the following policies best addresses the increased risk to the organization’s network incurred by this environment?
Which of the following network types should an organization choose if it wants to allow access only to its own personnel?
Which of the following authentication device credentials is the most difficult to revoke when an employee ' s access rights need to be removed?
Which of the following is classified as a product cost using the variable costing method?
Direct labor costs.
Insurance on a factory.
Manufacturing supplies.
Packaging and shipping costs.
Focus An organization has decided to have all employees work from home. Which of the following network types would securely enable this approach?
When preparing the annual internal audit plan, which of the following should the chief audit executive (CAE) consider to optimize efficiency and effectiveness?
Which of the following statements, is true regarding the capital budgeting procedure known as discounted payback period?
Several organizations have developed a strategy to open co-owned shopping malls. What would be the primary purpose of this strategy?
An internal audit uncovered high-risk issues that needed to be addressed by the organization. During the exit conference, the audit team discussed the high-risk issues with the manager responsible for addressing them. How should the chief audit executive respond if the manager agrees to correct the issues identified during the audit?
Which of the following purchasing scenarios would gain the greatest benefit from implementing electronic cate interchange?
According to Herzberg’s Two-Factor Theory of Motivation, which of the following factors are mentioned most often by satisfied employees?
Which of the following would most likely serve as a foundation for individual operational goats?
An organization requires an average of 58 days to convert raw materials into finished products to sell. An additional 42 days is required to collect receivables. If the organization takes an average of 10 days to pay for raw materials, how long is its total cash conversion cycle?
An internal auditor reviewed Finance Department records to obtain a list of current vendor addresses. The auditor then compared the vendor addresses to a record of employee addresses maintained by the Payroll Department Which of the following types of data analysis did the auditor perform?
An investor has acquired an organization that has a dominant position in a mature. slew-growth Industry and consistently creates positive financial income.
Which of the following terms would the investor most likely label this investment in her portfolio?
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized data?
An internal auditor observed that the organization ' s disaster recovery solution will make use of a cold site in a town several miles away. Which of the following is likely to be a characteristic of this disaster recover/ solution?
According to IIA guidance on IT, which of the following best describes a logical access control?
Which of these instances accurately describes the responsibilities for big data governance?
The internal audit activity has identified accounting errors that resulted in the organization overstating its net income for the fiscal year. Which of the following is the most likely cause of this overstatement?
Which of the following statements regarding flat and hierarchical internal audit functions is true?
Which of the following statements is true concerning the basic accounting treatment of a partnership?
Which of the following statements distinguishes a router from a typical switch?
Which of the following best describes the type of control provided by a firewall?
Which of the following capital budgeting techniques considers the tune value of money?
For employees, the primary value of implementing job enrichment is which of the following?
Which of the following risks would involve individuals attacking an oil company’s IT system as a sign of solidarity against drilling in a local area?
Based on lest results, an IT auditor concluded that the organization would suffer unacceptable loss of data if there was a disaster at its data center. Which of the following test results would likely lead the auditor to this conclusion?
During an internal audit engagement, it was found that several vendors were on a government sanctions list and must no longer be traded with. Which of the following would most effectively mitigate the risk of noncompliance with sanctions lists that are updated regularly?
Which of the following financial statements provides the best disclosure of how a company ' s money was used during a particular period?
An internal auditor was assigned to test for ghost employees using data analytics. The auditor extracted employee data from human resources and payroll. Using spreadsheet functions, the auditor matched data sets by name and assumed that employees who were not present in each data set should be investigated further. However, the results seemed erroneous, as very few employees matched across all data sets. Which of the following data analytics steps has the auditor most likely omitted?
During an audit of the payroll system, the internal auditor identifies and documents the following condition:
" Once a user is logged into the system, the user has access to all functionality within the system. "
What is the most likely root cause for tins issue?
In an organization with a poor control environment, which of the following indicators would help an internal audit function measure its ability to provide risk-based assurance?
Which of the following describes the most appropriate set of tests for auditing a workstation’s logical access controls?
Which of the following is the best example of a compliance risk that is likely to arise when adopting a bring-your-own-device (BYOD) policy?
Which of the following statements depicts a valid role of the internal audit function in ensuring the effectiveness of management action plans?
According to IIA guidance, which of the following would be the best first stop to manage risk when a third party is overseeing the organization ' s network and data?
A chief audit executive (CAE) is developing a strategic plan for the internal audit function. In the last two years, the organization has faced significant IT risks, but the internal audit function has not been able to audit those areas due to a lack of knowledge. How could the CAE address this in the strategic plan?
An internal audit function has commenced its annual follow-up activity. An internal auditor has been assigned to verify whether the recommendations from an audit engagement completed three months ago were implemented by the business unit. The auditor had not participated in that audit engagement. What should the auditor do first?
An internal auditor discovered that the organization was not in full compliance with a regulatory labeling requirement for one of its products. The responsible manager indicated that the current product labeling has been in use for several years without any problems. If discovered, this regulatory breach could result in significant fines for the organization. What should be the chief audit executive ' s next course of action?
Which of the following Issues would be a major concern for internal auditors when using a free software to analyze a third-party vendor ' s big data?
According to Herzberg ' s Two-Factor Theory of Motivation, which of the following factors arc mentioned most often by satisfied employees?
A organization finalized a contract in which a vendor is expected to design, procure, and construct a power substation for $3,000,000. In this scenario, the organization agreed to which of the following types of contracts?
Which of the following attributes of data are cybersecurity controls primarily designed to protect?
Which of the following should the chief audit executive agree upon with the board before starting an external assessment of the internal audit function?
A retail organization mistakenly did not include $10,000 of inventory in the physical count at the end of the year. What was the impact to the organization’s financial statements?
Internal audit discovered that several loads of pellets were deleted from the scaling database and consequently had no sales invoices, significantly affecting financial statements. An investigation revealed that technicians had deleted the pellet loads accidentally, with no evidence of fraud. Which of the following actions should management implement first?
Which of the following is a primary driver behind the creation and prloritteation of new strategic Initiatives established by an organization?
How can the chief audit executive best provide the internal audit function with the resources needed to fulfill the annual audit plan?
During which phase of the contracting process ere contracts drafted for a proposed business activity?
The management of working capital is most crucial for which of the following aspects of business?
The board of directors wants to implement an incentive program for senior management that is specifically tied to the long-term health of the organization. Which of the following methods of compensation would be best to achieve this goal?
According to 11A guidance on it; which of the following statements is true regarding websites used in e-commerce transactions?
Which of the following differentiates a physical access control from a logical access control?
What is the first step an internal audit function should take to define its organizational structure, deliverables, communication protocols, and resourcing model?
Which of the following is a distinguishing feature of managerial accounting, which is not applicable to financial accounting?
Which of the following practices circumvents administrative restrictions on smart devices, thereby increasing data security risks?
According to IIA guidance, which of the following statements is true regarding communication of engagement results?
During the second half of the audit year, the chief audit executive (CAE) identified significant negative variances to the approved audit budget required to complete the internal audit plan. Which of the following actions should the CAE take?
An organization uses the management-by-objectives method, whereby employee performance is based on defined goals. Which of the following statements is true regarding this approach?
While conducting ' audit procedures at the organization ' s data center an internal auditor noticed the following:
- Backup media was located on data center shelves.
- Backup media was organized by date.
- Backup schedule was one week in duration.
The system administrator was able to present restore logs.
Which of the following is reasonable for the internal auditor to conclude?
Which of the following measures would best protect an organization from automated attacks whereby the attacker attempts to identify weak or leaked passwords in order to log into employees ' accounts?
Which of the following is the most appropriate beginning step of a work program for an assurance engagement involving smart devices?
An internal auditor found the following information while reviewing the monthly financial siatements for a wholesaler of safety
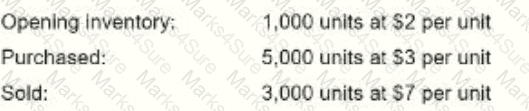
The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?
What kind of strategy would be most effective for an organization to adopt in order to implement a unique advertising campaign for selling identical products across all of its markets?
Which type of bond sells at & discount from face value, then increases in value annually until it reaches maturity and provides the owner with the total payoff?
An internal auditor is using data analytics to focus on high-risk areas during an engagement. The auditor has obtained data and is working to eliminate redundancies in the data. Which of the following statements is true regarding this scenario?
Upon completing a follow-up audit engagement, the chief audit executive (CAE) noted that management has not implemented any mitigation measures to address the high risks that were reported in the initial audit report. What initial step must the CAE take to address this situation?
Which of the following controls is the most effective for ensuring confidentially of transmitted information?
Based on test results, an IT auditor concluded that the organization would suffer unacceptable loss of data if there was a disaster at its data center. Which of the following test results would likely lead the auditor to this conclusion?
A multinational organization allows its employees to access work email via personal smart devices. However, users are required to consent to the installation of mobile device management (MDM) software that will remotely wipe data in case of theft or other incidents. Which of the following should the organization ensure in exchange for the employees ' consent?
An internal auditor considers the financial statement of an organization as part of a financial assurance engagement. The auditor expresses the organization ' s electricity and depreciation expenses as a percentage of revenue to be 10% and 7% respectively. Which of the following techniques was used by the internal auditor In this calculation?
An organization suffered significant damage to its local: file and application servers as a result of a hurricane. Fortunately, the organization was able to recover all information backed up by its overseas third-party contractor. Which of the following approaches has been used by the organization?
Which of the following is a primary driver behind the creation and prioritization of new strategic initiatives established by an organization?
When examining; an organization ' s strategic plan, an internal auditor should expect to find which of the following components?
An organization that relies heavily on IT wants to contain the impact of potential business disruption to a period of approximately four to seven days. Which of the following
business recovery strategies would most efficiently meet this organization ' s needs?
An organization with a stable rating, as assessed by International rating agencies, has issued a bond not backed by assets or collateral. Payments of the interests and the principal to bondholders are guaranteed by the organization. Which type of bond did the organization issue?
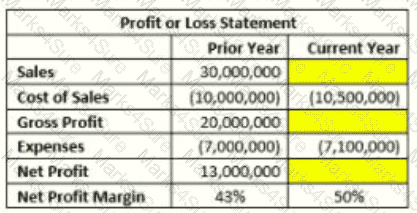
The manager of the sales department wants to Increase the organization ' s net profit margin by 7% (from 43% in the prior year to 50% in the current year). Given the information provided in the table below, what would be the targeted sales amount for the current year?
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized cate?
Which of the following attributes of data analytics relates to the growing number of sources from which data is being generated?
An internal auditor has finalized an engagement of the vendor master file. The results of the current engagement do not differ significantly from that of last year, in which several significant weaknesses in internal controls were reported. The internal auditor states in the final communication that the internal controls are as effective as that of the previous year. Which of the following elements of quality of communication could be improved?
An organization selected a differentiation strategy to compete at the business level. Which of the following structures best fits this strategic choice?
A newly appointed board member received an email that appeared to be from the company ' s CEO. The email stated:
“Good morning. As you remember, the closure of projects is our top priority. Kindly organize prompt payment of the attached invoice for our new solar energy partners.” The board member quickly replied to the email and asked under which project the expense should be accounted. Only then did he realize that the sender ' s mail domain was different from the company ' s. Which of the following cybersecurity risks nearly occurred in the situation described?
Which of the following is an example of a contingent liability that a company should record?
While auditing an organization ' s customer call center, an internal auditor notices that Key performance indicators show a positive trend, despite the fact that there have been increasing customer complaints over the same period. Which of the following audit recommendations would most likely correct the cause of this inconsistency?
What is the primary risk associated with an organization adopting a decentralized structure?
Which of the following statements is true regarding user developed applications (UDAs) and traditional IT applications?
According to IIA guidance, which of the following are typical physical and environmental IT controls?
An organization is considering outsourcing its IT services, and the internal auditor as assessing the related risks. The auditor grouped the related risks into three categories;
- Risks specific to the organization itself.
- Risks specific to the service provider.
- Risks shared by both the organization and the service provider
Which of the following risks should the auditor classify as specific to the service provider?
Which of the following networks is suitable for an organization that has operations In multiple cities and countries?
Which of the following statements is true regarding internal audit methodologies?
According to IIA guidance, which of the following statements is true regarding penetration testing?
Which of the following statements is true regarding the term " flexible budgets " as it is used in accounting?
A one-time password would most likely be generated in which of the following situations?
An organization requires an average of 5S days to convert raw materials into finished products to sell. An average of 42 additional days is required to collect receivables. If the organization takes an average of 10 days to pay for the raw materials, how long is its total cash conversion cycle?
An organization’s account for office supplies on hand had a balance of $9,000 at the end of year one. During year two, the organization recorded an expense for purchasing office supplies. At the end of year two, a physical count determined that the organization has $11,500 in office supplies on hand. Based on this information, what would be recorded in the adjusting entry at the end of year two?
At one organization, the specific terms of a contract require both the promisor end promise to sign the contract in the presence of an independent witness.
What is the primary role to the witness to these signatures?
During which phase of the contracting process are contracts drafted for a proposed business activity?
Which of the following is the most appropriate way to record each partner’s initial investment in a partnership?