Your network uses a single JSA host and you want to implement a cluster.
In this scenario, which two statements are correct? (Choose two.)
Which two statements about SRX Series device chassis clusters are true? (Choose two.)
Exhibit
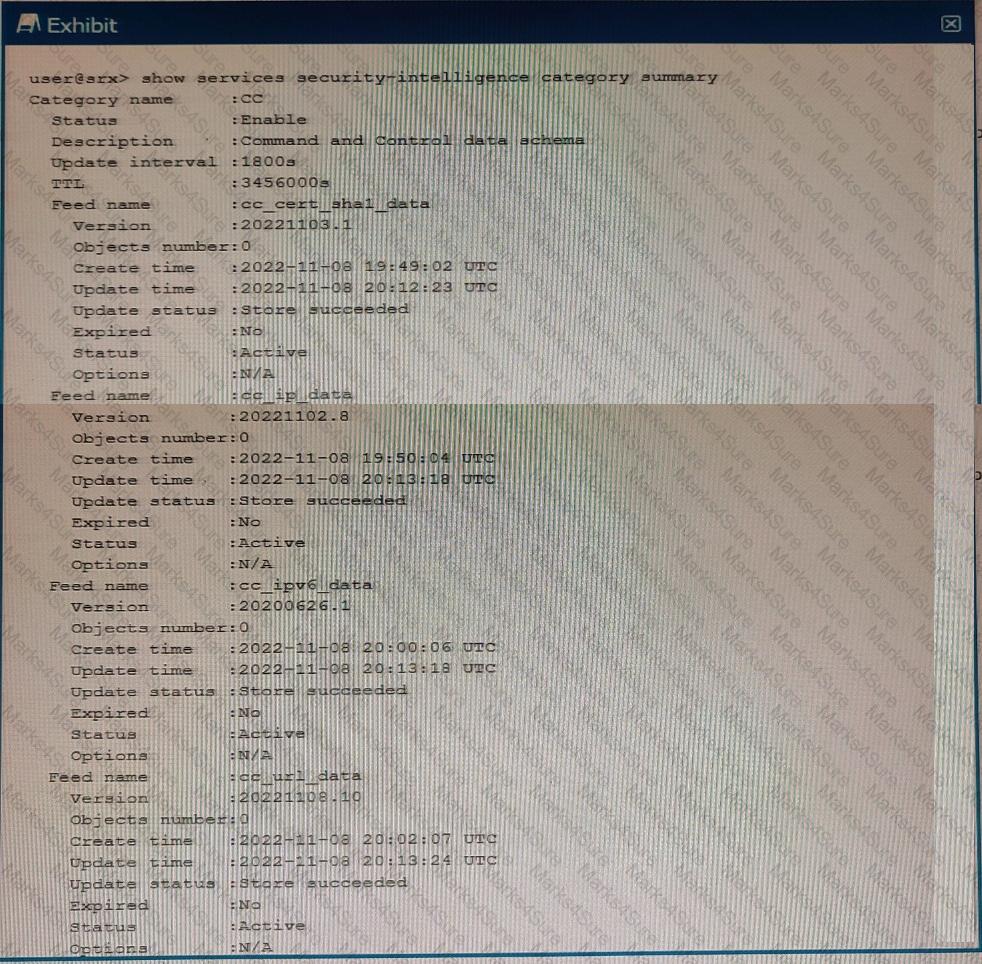
You just finished setting up your command-and-control (C & C) category with Juniper ATP Cloud. You notice that all of the feeds have zero objects in them.
Which statement is correct in this scenario?
You are asked to find systems running applications that increase the risks on your network. You must ensure these systems are processed through IPS and Juniper ATP Cloud for malware and virus protection.
Which Juniper Networks solution will accomplish this task?
Which statement regarding Juniper Identity Management Service (JIMS) domain PC probes is true?
You are asked to reduce the load that the JIMS server places on your Which action should you take in this situation?
Click the Exhibit button.
Which two statements describe the output shown in the exhibit? (Choose two.)
You need to deploy an SRX Series device in your virtual environment.
In this scenario, what are two benefits of using a CSRX? (Choose two.)
Which two statements about SRX Series device chassis clusters are correct? (Choose two.)
Click the Exhibit button.

You have implemented SSL client protection proxy. Employees are receiving the error shown in the exhibit.
How do you solve this problem?
Which two statements are true about the fab interface in a chassis cluster? (Choose two.)
You are asked to implement IPS on your SRX Series device.
In this scenario, which two tasks must be completed before a configuration will work? (Choose two.)
You have deployed an SRX300 Series device and determined that files have stopped being scanned.
In this scenario, what is a reason for this problem?
You are asked to ensure that if the session table on your SRX Series device gets close to exhausting its resources, that you enforce a more aggress.ve age-out of existing flows.
In this scenario, which two statements are correct? (Choose two.)
After JSA receives external events and flows, which two steps occur? (Choose two.)
You enable chassis clustering on two devices and assign a cluster ID and a node ID to each device.
In this scenario, what is the correct order for rebooting the devices?
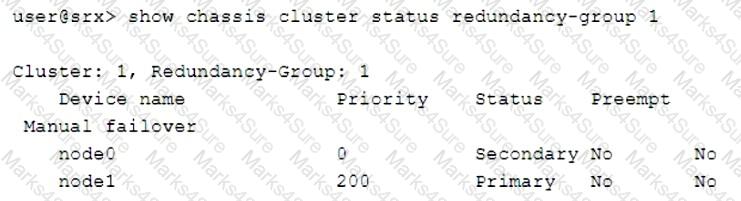
Exhibit
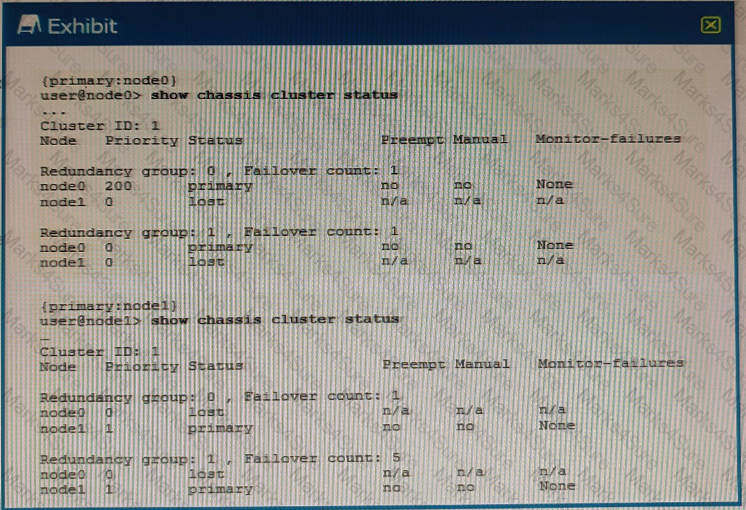
Referring to the exhibit, what do you determine about the status of the cluster.