You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. You create an application using .NET Framework. The application is using an assembly. You want to ensure that the application provides the best performance. Security is not a consideration. Which of the following permission sets will you use to accomplish the task?
Everything
FullTrust
Nothing
Execution
LocalIntranet
Internet
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. You create a Web form in the application that permits users to provide personal information. You add a DropDownList control to the Web form to retrieve the residential status of users. The default item that the DropDownList control displays is the " Select Country " option. You have to ensure that users select a country other than the default option. Which of the following validation controls should you use to accomplish this task?
RangeValidator
RequiredFieldValidator
CustomValidator
RegularExpressionValidator
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You are creating an ASP.NET Web application using .NET Framework 3.5. You need to implement a system to monitor Service Level Agreement (SLA) compliance in the application. You are required to make a method to enable precise calculation of the time taken by all requests to process. What will you do to accomplish this?
Implement a Timer component in the application. Calculate the elapsed time between the Start and Stop methods.
Implement a base Web form for all the Web forms in the application. Calculate the elapsed time between the Load and Unload events.
Create and register a custom HttpHandler.
Create and register a custom HttpModule.
Robert works as a Software Developer for InfoTech Inc. He develops an application named MyApp that uses SQL Server database and three database components. He wants to ensure that other developed applications cannot use these database components. Users should be authorized before they can access these components. Robert configures the database component assemblies to accomplish this task. Choose the correct actions that Robert should take after the configuration.
True
False
Mark works as a Software Developer for McRobert Inc. He develops an ASP.NET application using Visual Studio .NET. The application loads department name and employee data only once in each user ' s session. Mark creates two DataTable objects, named Employees and Departments. The
Departments object remains static, but the Employees object is modified whenever new employees join the company.
Mark wants to minimize the time it takes for the application to reload an ASP.NET page after each change. Which of the following statements will he use to accomplish this?
Session( " Departments " ) = Departments
Cache( " Employees " ) = Employees
Cache( " Departments " ) = Departments
Cache( " Employees " ) = Employees
Session( " Departments " ) = Departments
Session( " Employees " ) = Employees
Cache( " Departments " ) = Departments
Session( " Employees " ) = Employees
You work as a Software Developer for ABC Inc. You use Visual Studio .NET to develop a Windows application named MyWindowApp. You implement the security classes of the .NET Framework. When users interact with the application, the role-based validation should perform frequently. You must ensure that only validated Windows NT or Windows 2000 domain users are permitted to access the application. You add the appropriate Imports statements for the System.Security.Principal namespace and the System.Threading namespace. Which of the following code segments will you use to accomplish this task?
Dim identity As WindowsIdentity = _WindowsIdentity.GetAnonymous()
Dim myprincipal As New WindowsPrincipal(identity)
AppDomain.CurrentDomain.SetThreadPrincipal(_
PrincipalPolicy.WindowsPrincipal)
Dim myprincipal As WindowsPrincipal = _CType(Thread.CurrentPrincipal, WindowsPrincipal)
Dim identity As WindowsIdentity = WindowsIdentity.GetCurrent()
Dim myprincipal As New WindowsPrincipal(identity)
AppDomian.CurrentDomain.SetPrincipalPolicy(_
PrincipalPolicy.WindowsPrincipal)
Dim myprincipal As WindowsPrincipal = _CType(Thread.CurrentPrincipal, WindowsPrincipal)
You work as a Software Developer for ABC Inc. You use C# .NET to develop a windows application. The application will implement a role-based authorization scheme that is based on a Microsoft SQL Server database of user names. Users will enter their names in a text box named UserName. You must ensure that users are assigned the supervisor role and the PG role by default. Which of the following code segments will you use to accomplish this task?
GenericIdentity identity =
new GenericIdentity(UserName.Text);
string[] RoleArray = { " Supervisor " , " PG " };
WindowsPrincipal principal = new WindowsPrincipal(identity);
WindowsIdentity identity =
new WindowsIdentity.GetAnonymous();
string[] RoleArray = { " Supervisor " , " PG " };
WindowsPrincipal principal = new GenericPrincipal(identity, RoleArray);
GenericIdentity identity =
new GenericIdentity(UserName.Text);
string[] RoleArray = { " Supervisor " , " PG " };
GenericPrincipal principal = new GenericPrincipal(identity, RoleArray);
WindowsIdentity identity =
new WindowsIdentity.GetCurrent();
string[] RoleArray ={ " Supervisor " , " PG " };
GenericPrincipal principal = new GenericPrincipal(identity, RoleArray);
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. Allen creates an application that will be used to handle security information related to the company. He wants to secure the application by using the most secure authentication method. The method should have a strong key for encryption and send the encrypted password across the network. Which of the following authentication methods will Allen use to accomplish the task?
Integrated Windows authentication
Basic authentication
Certificate-based authentication
Digest authentication
Sandra works as a Software Developer for ABC Inc. She develops an application named MyApp that contains a data-bound control named MyDataControl. She wants to use an Oracle database in order to bind data to MyDataControl. Which of the following GUI-based data sources will Sandra use to accomplish the task?
AccessDataSource
SqlDataSource
ObjectDataSource
XmlDataSource
SitemapDataSource
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You create a remoting application that provides stock information to customers using .NET Framework. The server component raises an event on the client computer when certain conditions are met. You must ensure that the server raises exactly one event for each client application that is registered for the event. What will you do to accomplish this task?
Configure the server class as a SingleCall Activated Object (SAO) and check for duplicate client delegate methods before raising the event.
Configure the server class as a Singleton Activated Object (SAO) and check for duplicate client delegate methods before raising the event.
Configure the server class as a Client Activated Object (CAO) and override the CreateObjRef method to check for duplicate client delegate methods before raising the event.
Configure the server class as a Client Activated Object (CAO) and check for duplicate client delegate methods before raising the event.
Perry works as a Web Developer for BlueWell Inc. He creates a catalog application named MyCatalog for a server using Visual Studio .NET. MyCatalog contains data that describes the pricing values of design catalogs. He wants to ensure that only authenticated users are authorized to access the data. He also wants the data to be secured at the highest level of authentication. Which of the following authentication levels will Perry use to accomplish this?
Packet Privacy
Packet Integrity
Packet
Call
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are creating a .NET remoting application using .NET Framework 2.0. The object of the application will be shared by multiple applications. You want to use simple, modular, extensible, and XML-based protocol to exchange messages between remoting applications. What will you do to accomplish the task?
Use the SOAP protocol.
Use the SoapFormatter class.
Use the BinaryFormatter class.
Use client activated objects.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You create a Web service application using .NET Framework. The Web service provides confidential data of employees to applications that manage access to company facilities. The Web service is accessible by using TCP and is sheltered by using WSE 3.0. The company has implemented fingerprint readers to grant employees access to the facilities. All the captured images of the employees ' fingerprints are retained by the Web service application. You must make certain that the existing WSE encryption policy can be applied to the fingerprint image. You are required to provide the solution that must reduce the size of the Web service message.
What will you do to accomplish this task?
Configure the Web service to use base64 encoding to pass the binary fingerprint image.
Configure the Web service to use Message Transmission Optimization Mechanism to pass the binary fingerprint image.
Create a SOAP filter to manage encryption for the message.
Create a SOAP extension to manage encryption for the message.
You work as a Software Developer for ManSoft Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You create an application that will be used by all the branches of the company. You use the Regex class in the application to validate some strings. You want to search an input string for an occurrence of a regular expression. Which of the following methods of the Regex class will you use to accomplish the task?
Matches
Match
IsMatch
Equals
You work as an ADO.NET Application Developer for ABC Inc. The company uses Microsoft Visual Studio .NET 2008 as its application development platform. You create an ADO.NET application by using .NET Framework 3.5. You need to represent a strongly typed lambda expression as a data structure in the form of an expression tree. Which of the following classes will you use to accomplish the task?
MethodCallExpression
LambdaExpression
Expression
Expression (TDelegate)
Emily works as a Programmer in an Eye Research Center. The center keeps several records such as case history records for old patients and newly admitted patients, and records for outdoor patients. The Head of the Research Center wants Emily to generate reports for each outdoor patient with minimum network traffic. Emily develops an application named OutdoorPatientReport by using Visual Studio .NET. She needs to utilize the data repository as maintained by the center.
She wants to ensure that the application is displayed to all the doctors. Which of the following actions will Emily take to accomplish this task?
Use Microsoft SQL Server stored procedures for data calculations.
Implement a batch processing system for data calculations.
Create more than one database for data manipulations.
Use SQL Server indexes to optimize data calculations.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. The application uses Forms authentication. Your company uses Active Directory.
You need to modify the application to enable users to make use of their existing Active Directory account to access the application through the Internet. You are required to ensure that the application must be modified with the least amount of user interface changes, cost, and development effort. What will you do to accomplish this?
Remove Forms authentication and create an ASP.NET membership.
Change the membership provider to ActiveDirectoryMembershipProvider.
Create a custom membership provider that has access to the corporate Active Directory.
Change the application to use the Windows authentication provider instead of Forms authentication.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are deploying a class library using the .NET Framework. Portions of your code need to access system environment variables. You need to force a runtime security exception only when the callers that are higher in the call stack do not have necessary permissions to access the resources. Which of the following methods will you use to accomplish the task?
PermitOnly()
Demand()
Assert()
Deny()
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are creating a .NET remoting application using .NET Framework 2.0.
The object of the application will be shared by multiple applications. You want to use simple, modular, extensible, and XML-based protocol to exchange messages between remoting applications. What will you do to accomplish the task?
Use the BinaryFormatter class.
Use client activated objects.
Use the SoapFormatter class.
Use the SOAP protocol.
Sam works as a Software Developer for BlueWell Inc. He creates a .NET Remoting object named MyObj using Visual Studio .NET. He wants to configure MyObj to send and receive confidential information from an XML file stored in an encrypted hard drive. What will he do to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
Implement a declarative security check.
Implement an imperative security check.
Use the SecurityAction.Demand value for the SecurityAction flag.
Use the SecurityAction.RequestMinimum value for the SecurityAction flag.
You work as an Enterprise Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You are creating an Enterprise application using .NET Framework 3.5. The application must meet the following requirements:
l The application loads XML from streams.
l The application creates XML from scratch by using functional construction.
l The application queries XML using XPath-like axes.
l The application validates XML trees using XSD.
What will you do to meet these requirements with least development efforts?
Use LINQ to XML.
Use LINQ to SQL.
Use the XML Schema Definition Tool.
Use ADO.NET Data Services.
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. Allen develops an application using .NET Framework 3.5. The application connects to a SQL Server database using a SqlConnection object named Connection1. He creates some stored procedures in the database, which are used to update the data. Allen finds that sometimes, the update operation does not affect any row. He wants to add an error handling code to the application. Which of the following code segments will he use to accomplish the task?
try
{
Connection1.open();
}
catch(DataException Myexcept)
{
//Error-handling code
}
try
{
Connection1.open();
}
catch(SqlException Myexcept)
{
//Error-handling code
}
try
{
Connection1.open();
}
catch(DBConcurrencyException Myexcept)
{
//Error-handling code
}
try
{
Connection1.open();
}
catch(InvalidCastException Myexcept)
{
//Error-handling code
}
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are in process of creating an application using the .NET Framework 2.0. The application must collect data from different streams by performing the following operations:
l Reading data from the byte stream
l Reading data from the memory stream
l Reading data from the file stream
Which of the following stream classes will you use to accomplish the task?
Each correct answer represents a part of the solution. Choose all that apply.
MemoryStream
StreamWriter
FileStream
StreamReader
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You are developing an application for the customer support using the .NET Framework. The customer support application accepts phone numbers. While running a report, you notice that the phone numbers displayed do not pursue similar format. Furthermore, there are cases of missing digits and missing area codes. You are required to ensure that the phone numbers are entered in the following format:
(###) ###- ####
You need to accomplish this task with the least amount of code. What will you do?
Use the CustomValidator control.
Replace all TextBox controls that are used for phone number input with MaskedTextBox con trols.
Write code that uses a regular expression.
Use the RegularExpressionValidator control.
Sophia works as a Software Developer for BlueWell Inc. She creates a component, named MyComp, using Visual Studio .NET. MyComp includes a method named MyMethod1, which is used to process user requests. MyMethod1 calls a private method, named MyMethod2. Sophia wants to ensure that if an error occurs during the execution, the exceptions encountered by MyMethod2 are caught and passed on to MyMethod1 for exception handling. Which of the following combinations of the exception handler should she use to accomplish the task?
try, catch, and throw
catch, finally, and throw
try, catch, and finally
try and throw
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create the definition for a Car class by using the following code segment:
public class Car {
[XmlAttribute(AttributeName = " category " )]
public string CarType;
public string model;
[XmlIgnore]
public int year;
[XmlElement(ElementName = " mileage " )]
public int miles;
public ConditionType condition;
public Car() {
}
public enum ConditionType {
[XmlEnum( " Poor " )] BelowAverage,
[XmlEnum( " Good " )] Average,
[XmlEnum( " Excellent " )] AboveAverage
}}
You create an instance of the Car class. You fill the public fields of the Car class as shown in the table below:
You are required to recognize the XML block that is produced by the Car class after serialization. Which of the following XML blocks represents the output of serializing the Car class?
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema "
category= " sedan " >
< model > racer < /model >
< mileage > 15000 < /mileage >
< conditionType > Excellent < /conditionType >
< /
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema "
category= " sedan " >
< model > racer < /model >
< mileage > 15000 < /mileage >
< condition > Excellent < /condition >
< /Car >
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema " "
CarType= " sedan " >
< model > racer < /model >
< miles > 15000 < /miles >
< condition > AboveAverage < /condition >
< /Car >
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema " >
< category > sedan < /category >
< model > racer < /model >
< mileage > 15000 < /mileage >
< condition > Excellent < /condition >
<You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are developing an application using the .NET Framework 2.0.
You are required to use a datatype that will store only numbers ranging from -32,768 to 32,767.
Which of the following datatypes will you use to accomplish the task?
Each correct answer represents a complete solution. Choose two.
int
string
short
System.Int16
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You create a message queue named SecureQ using .NET Framework. The message queue requires each incoming message to be encrypted. You want to ensure that a message can be sent to SecureQ without an exception being thrown. What will you do to accomplish this task?
Use the CryptoStream class to encrypt the Body property on the message.
Set the HashAlgorithm property to a value from the HashAlgorithm enumeration on the me ssage.
Set the EncryptionAlgorithm property to a value from the EncryptionAlgorithm enumeration on the message.
Set the UseEncryption property to true on the message.
You work as an Enterprise Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET application using .NET Framework 3.5. You have already created a data contract for a WCF service and the ASP.NET Web application, which consumes the WCF service. The application has the following requirements:
l On low network bandwidth the serialized format of the data contract type should be minimum.
l The application uses AJAX to retrieve the data from the WCF service.
l Use the least amount of development effort.
What will you do?
Use the XML format.
Use the WPF format.
Use the Binary Format Description format.
Use the Java Script Notation format.
John works as a Web Developer for TechCom Inc. He creates an ASP.NET application, named MyApp1, by using Visual Studio .NET for a University Web site. Students will use MyApp1 to view their term end results. MyApp1 contains an ASP.NET page, named Page1. Page1 contains a TextBox control, named txtEnrolmentNo, and two Button controls, named btnSubmit and btnCancel.
John wants to display the text " Enter Enrolment Number " within txtEnrolmentNo. He wants to ensure that if a user tries to submit the page without entering an enrolment number, the word " Error " appears next to txtEnrolmentNo. Which of the following actions will he take to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
Add a RequiredFieldValidator control to the page. Set its ControlToValidate property to txtEnrolmentNo, InitialValue property to " Enter Enrolment Number " , and ErrorMessage property to " Error " .
Add a RequiredFieldValidator control to the page. Set its ControlToValidate property to txtEnrolmentNo, ErrorMessage property to " Enter Enrolment Number " , and InitialValue property to " Error " .
Set the InitialValue property of txtEnrolmentNo to " Enter Enrolment number " .
Set the Text property of txtEnrolmentNo to " Enter Enrolment number " .
Add a RegularExpressionValidator control to the page. Set its ControlToValidate property to txtEnrolmentNo, ErrorMessage property to " Enter Enrolment Number " , and InitialValue property to " Error " .
You work as a Software Developer for ManSoft Inc. You create an application using Visual Studio .NET 2005. You are using the Custom authentication provider in the application. In order to enable the Custom authentication provider, you have to make an entry in the Web.config file for the application. Which of the following entries will you use to accomplish the task?
< authentication mode= " Passport " / >
< authentication mode= " Custom " / >
< authentication mode= " Windows " / >
< authentication mode= " None " / >
< authentication mode= " Forms " / >
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Windows application using the .NET Framework.
You create a database to maintain the record of the students. You create a table named Student. You want to retrieve names and roll number of those students whose age is less than ten years. An instance of the SqlCommand class named StudentCommand is already created. Which of the following code segments should you use to execute the query?
StudentCommand.CommandType = CommandType.StoredProcedure;
StudentCommand.CommandText = " Name and Roll number of students less than ten years " ;
StudentCommand.CommandType = CommandType.StoredProcedure;
StudentCommand.CommandText = " SELECT Name, Roll number FROM Student WHERE Age <</p>
10 " ;
StudentCommand.CommandType = CommandType.Text;
StudentCommand.CommandText = " SELECT Name, Roll number FROM Student WHERE Age <</p>
10 " ;
StudentCommand.CommandText = CommandText.Text;
StudentCommand.CommandType = " SELECT Name, Roll number FROM Student WHERE Age <</p>
10 " ;
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. The application uses the health monitoring events to raise application audit events in the following situations:
l When users login
l When users modify their password
l When users perform other security-related actions
You must ensure that the application logs all audit events for all applications on the Web server.
What will you do?
Configure the eventMappings Element in the Web.config file to allow an entry for success a udits.
Configure the eventMappings Element in the Web.config file to allow a single entry for auditing events that is present for all audits.
Configure the eventMappings Element in the Machine.config file to allow an entry for success audits.
Configure the eventMappings Element in the Machine.config file to allow a single entry for auditing events that is present for all audits.
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create a Windows Forms application using .NET Framework 3.5. The application needs a thread that accepts an integer parameter. You write the following code segment in the application:
Thread myThread = new Thread(new ParameterizedThreadStart(doWork));
myThread.Start(125);
You are required to declare the signature of the doWork method. Which of the following method signatures will you use?
public void doWork(int nCount)
public void doWork(Object oCount)
public void doWork()
public void doWork(Delegate oCount)
Henry works as a Software Developer for InfoTech Inc. He develops a Web application for registered employees of the company. The application requires accessing several XML data stored in a database named Database1. However, Henry wants to ensure that the XML data is validated before being accessed. Which of the following classes will Henry use to validate the XML data?
XmlValidatingReader
XmlTextReader
XmlNodeReader
XmlReader
Andrew works as a Software Developer for BlueWell Inc. He develops a Windows-based application, named App1, using Visual Studio .NET. The application uses Microsoft SQL Server as a backend database. Andrew wants to perform security checks on App1. Which of the following statements regarding security checks are true?
Each correct answer represents a complete solution. Choose two.
Declarative security check works by instantiating security classes.
Declarative security check works by assigning attributes to assemblies.
Imperative security check works by instantiating security classes.
Imperative security check works by assigning attributes to assemblies.
Maria works as a Software Developer for MarcLync Inc. She creates an XML Web service, named MyWebService, using Visual Studio .NET. Maria wants to debug MyWebService. Therefore, she attaches a debugger to the Web service process. However, Maria notices that whenever MyWebService is executed, it throws an exception System.Net.WebException after a certain time period. The exception displays the message " The current operation has timed-out. " Maria wants to modify the code in MyWebService. Which of the following actions will Maria take in order to resolve this issue?
Set the timeout value for the MyWebService call to zero.
Set the timeout value for the MyWebService call to false.
Add an exception handling block.
Set the timeout value for the MyWebService call to -1.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You have recently finished development of a Windows application using .NET Framework. Users report that the application is not running properly. When the users try to complete a particular action, the following error message comes out:
Unable to find assembly ' myservices, Version=1.0.0.0, Culture=neutral,
PublicKeyToken=29b5ad26c9de9b95 ' .
You notice that the error occurs as soon as the application tries to call functionality in a serviced component that was registered by using the following commanD.
regsvcs.exe myservices.dll
You must make sure that the application can call the functionality in the serviced component with no exceptions being thrown. What will you do to accomplish this task?
Copy the serviced component assembly into the C.\Program Files\ComPlus Applications fold er
Run the command line tool: regasm.exe myservices.dll.
Copy the serviced component assembly into the C.\WINDOWS\system32\Com folder.
Run the command line tool: gacutil.exe /i myservices.dll.
Allen works as a Software Developer for ABC Inc. He develops an application using Visual Studio .NET
2005. The application will be used for the registration of employees by filling a form provided in the application. The form contains the following fields:
l First Name
l Last Name
l Date of Birth
l E-mail
He provides a TextBox control for each field. He wants an employee to be able to receive a user-defined error message when he makes a wrong entry. Which of the following properties is mandatory if a
CustomValidator control is used to validate an entry?
EnableViewState
EnableTheming
ErrorMessage
IsValid
You work as a Web Application Developer for SunInfo Inc. The company uses Visual Studio 2008 as its application development platform. You create a Web application using .NET Framework 3.5.
You want to ensure that the data input by a user falls within a predetermined range. Which of the following validation controls will you use to accomplish the task?
RangeValidator
CompareValidator
RequiredFieldValidator
RegularExpressionValidator
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You are creating an application using the .NET Framework. The application contains a class named globalInfo. You need to serialize all public and nonpublic data of the globalInfo class to ensure that the class generates the minimum byte stream so that the minimum load is placed upon network resources. What will you do?
Use the XmlSerializer class.
Use the BinaryFormatter class.
Use the SoapFormatter class.
Use the IXmlSerializable interface.
You work as a Software Developer for Mansoft Inc. You create an application and use it to create users as members of the local Users group. Which of the following code snippets imperatively demands that the current user is a member of the local Users group?
Each correct answer represents a complete solution. Choose all that apply.
System.AppDomain.CurrentDomain.SetPrincipalPolicy(PrincipalPolicy.WindowsPrincipal);
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " BUILTIN\Users " , true);
MyPermission.Demand();
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " BUILTIN\Users " , true); MyPermission.Demand();
System.AppDomain.CurrentDomain.SetPrincipalPolicy(PrincipalPolicy.WindowsPrincipal);
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " Users " , true);
MyPermission.Demand();
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " Users " , true);
MyPermission.Demand();
Samantha works as a Software Developer for InfoWorld Inc. She develops a Web page named SalesReport.aspx for the employees of the company. However, she wants to ensure that all the requests for a particular employee are not stored on the server ' s memory. She also wants to ensure that no data is lost even after each user session has expired. Which of the following actions will Samantha take to accomplish the task?
Use a cookieless session state for storing information.
Use the profile properties feature for storing information.
Use the application state for storing information.
Use the session state with cookie for storing information.
Mark works as a Web Developer for ABC Inc. He develops an ASP.NET application, named MyApp1, using Visual Studio .NET. MyApp1 allows users to view and purchase company products.
It includes several pages. The start-up page of the application is Page1.aspx. He configures the application ' s Web.config file to use form-based authentication.
Mark wants users to log on to Page1.aspx by providing their user names and passwords. To accomplish this, he creates an ASP.NET page named UsersLogIn.aspx that allows each user to specify a user name and password. He then writes the following syntax in the Web.config filE.
< authentication mode= " Forms " >
< forms name= " MyName "
loginUrl= " /UsersLogIn.aspx "
protection= " All "
timeout= " 60 "
slidingExpiration= " true " >
< /forms >
< /authentication >
What will be the result?
Each correct answer represents a part of the solution. Choose two.
The session will expire after 60 seconds.
The session will expire after 60 minutes.
The session will expire after 60 hours.
The session lifetime will be reset periodically.
The session will never expire.
Once the session lifetime is set, it will not change.
John works as a Web Developer for ProLabs Inc. He develops an ASP.NET application, named
MyWebApp1, using Visual Studio .NET. One of the pages in the application is named as Page1.aspx, which does not need to maintain session state. To improve the performance of the application, John wants to disable session state for Page1. Which of the following actions will he take to accomplish the task?
Set the EnableViewState attribute in the @ Page directive to false.
Set the DisableSessionState attribute in the @ Page directive to true.
In the sessionState configuration section of the application ' s Web.config file, set the mode attribute to off.
Set the EnableSessionState attribute in the @ Page directive to false.
Andrew works as a Software Developer for Mansoft Inc. The company ' s network has a Web server that hosts the company ' s Web site. Andrew wants to enhance the security of the Web site by implementing Secure Sockets Layer (SSL). Which of the following types of encryption does SSL use?
Each correct answer represents a complete solution. Choose two.
Symmetric
Secret
IPSec
Asymmetric
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You have recently finished development of a Windows application using .NET Framework. Users report that the application is not running properly. When the users try to complete a particular action, the following error message comes out:
Unable to find assembly ' myservices, Version=1.0.0.0, Culture=neutral,
PublicKeyToken=29b5ad26c9de9b95 ' .
You notice that the error occurs as soon as the application tries to call functionality in a serviced component that was registered by using the following command:
regsvcs.exe myservices.dll
You must make sure that the application can call the functionality in the serviced component with no exceptions being thrown. What will you do to accomplish this task?
Run the command line tool: regasm.exe myservices.dll.
Copy the serviced component assembly into the C:\Program Files\ComPlus Applications fold er.
Run the command line tool: gacutil.exe /i myservices.dll.
Copy the serviced component assembly into the C:\WINDOWS\system32\Com folder.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You need to write a code segment that transfers the contents of a byte array named ToSend by using a NetworkStream object named NetStr. You want to use a cache of size only 8,192 bytes. Which of the following code segments will you use to accomplish the task?
MemoryStream MStream = new MemoryStream(8192);
NetStr.Write(ToSend, 0, (int) MStream.Length);
BufferedStream BStream = new BufferedStream(NetStr);
BStream.Write(ToSend, 0, 8192);
BufferedStream BStream = new BufferedStream(NetStr, 8192);
BStream.Write(ToSend, 0, ToSend.Length);
MemoryStream MStream = new MemoryStream(8192);
MStream.Write(ToSend, 0, (int) NetStr.Length);
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You create an application for the company. You need to validate the phone number passed to a class as a parameter in the application. Which of the following is the most effective way to verify that the format of the data matches a phone number?
Regular expressions
Nested If statements
Use the String.Length property
A try/catch block
You work as a Software Developer for Mansoft Inc. You create an application and use it to create users as members of the local Users group. Which of the following code snippets imperatively demands that the current user is a member of the local Users group?
Each correct answer represents a complete solution. Choose all that apply.
System.AppDomain.CurrentDomain.SetPrincipalPolicy(PrincipalPolicy.WindowsPrincipal);
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " BUILTIN\Users " , true);
MyPermission.Demand();
System.AppDomain.CurrentDomain.SetPrincipalPolicy(PrincipalPolicy.WindowsPrincipal);
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " Users " , true); MyPermission.Demand();
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " BUILTIN\Users " , true); MyPermission.Demand();
PrincipalPermission MyPermission = new PrincipalPermission(null, @ " Users " , true); MyPermission.Demand();
John works as a Software Developer for InfoTech Inc. He develops an application named
SerializeObj. He creates a custom class and wants to serialize its object. He also wants the object to be stored into an XML file named File1.xml. He writes the following code: public class Employees
{
public string EmpID;
public string EmpName;
public decimal Salary;
}
Which of the following code statements will John add in the application?
XmlSerializer ObjectSerializer = new XmlSerializer(typeof(Employees), ObjectTypes);
XmlSerializer ObjectSerializer = new XmlSerializer(typeof(Employees));
XmlSerializer ObjectSerializer = new XmlSerializer(Employees);
XmlSerializer ObjectSerializer = new XmlSerializer();
Georgina works as a Software Developer for BlueChip Inc. She develops an application named App1 using Visual Studio .NET. The company wants her to deploy App1 to a customer ' s laptop. Georgina creates an assembly named Assembly1 to be stored in the Global Assembly Cache so that the Common Language Runtime (CLR) can locate and bind Assembly1.
As the application executes, the CLR locates the path of Assembly1 through the codebase setting. But, it finds no < codebase > element in the app.config file, and fails to bind Assembly1. Now, the CLR tries to locate Assembly1 through probing. Which of the following will the CLR check to locate Assembly1?
Each correct answer represents a part of the solution. Choose all that apply.
Previously loaded assemblies
The application base or root directory
The Gacutil.exe tool in the Global Assembly Cache
Sub-directories in the application ' s root directory
The culture attribute of the assembly
The correct version of the assembly
The assembly ' s name
Allen works as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. Allen creates an application that will be used to handle security information related to the company. He wants to secure the application by using the most secure authentication method. The method should have a strong key for encryption and send the encrypted password across the network. Which of the following authentication methods will Allen use to accomplish the task?
Integrated Windows authentication
Basic authentication
Certificate-based authentication
Digest authentication
George works as a Software Developer for GenTech Inc. He creates an application named App1 using Visual Studio .NET. App1 uses the version 2.0.0.0 of an assembly named Assembly1. However, he wants App1 to use a new version i.e. 2.1.0.0 of Assembly1. Therefore, he needs to specify Assembly1 ' s location so that App1 can use version 2.1.0.0 of Assembly1. What will George use to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
An unmanaged code.
A managed code.
The < probing > element.
The < codeBase > element.
Smith works as a Software Developer for ABC Inc. He creates an application using Visual Studio .NET 2005. The application displays " Welcome to ABC " on the top-left corner of a form. He writes the following code:
StringBuilder strbuild1 = new StringBuilder(20);
strbuild1.Append( " ' Welcome " );
strbuild1.Append( " " );
strbuild1.Append( " to " );
strbuild1.Append( " " );
strbuild1.Append( " ABC ' " );
string str1 = strbuild1.ToString();
Console.WriteLine(str1);
Console.ReadLine();
What is the main purpose of using StringBuilder object in the application?
To create dynamic or mutable strings.
To concatenate two or more different set of strings or a set of Unicode characters.
To convert a value of the StringBuilder object to the String object.
To append a specified string to the end of the StringBuilder object.
Mark works as a Software Developer for GenTech Inc. He develops an application, named App1, using Visual Studio .NET. The application contains a Form control, named Form1, which enables users to edit information in a SQL Server database. Mark wants to save all the changes made by users in the database. He defines a boolean variable, named DataIsSaved, in the application code. DataIsSaved indicates whether or not all data are saved in the database. Mark wants to prevent Form1 from closing until all the changes are saved in the database. Which of the following code will he use to accomplish this?
protected void Form1_Leave(object sender, System.ComponentModel.CancelEventArgs e) {
if(!DataIsSaved)
Cancel = false;
else
Cancel = true;
}
protected void Form1_Leave(object sender, System.ComponentModel.CancelEventArgs e) {
if(!DataIsSaved)
Cancel = true;
else
Cancel = false;
}
protected void Form1_Closed(object sender, System.ComponentModel.CancelEventArgs e) {
if(!DataIsSaved)
You work as a Web Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Web application using .NET Framework 2.0. The application is for members only. The behavior of the Web application varies according to the role of the user. The Web application uses the ASP.NET Membership control for creation of user accounts. You are required to find out whether a user is a member of a specific role. What will you do?
Pass the role names to the User.IsInRole method.
Pass the user names and passwords to the Membership.ValidateUser method.
Pass the role names to the Roles.RoleExists method.
Pass the user names to the User.IsUserInRole method.
Andrew works as a Software Developer for Mansoft Inc. The company ' s network has a Web server that hosts the company ' s Web site. Andrew wants to enhance the security of the Web site by implementing Secure Sockets Layer (SSL). Which of the following types of encryption does SSL use?
Each correct answer represents a complete solution. Choose two.
IPSec
Asymmetric
Symmetric
Secret
You work as a Software Developer for ABC Inc. You create a Console application named
ConsoleApplication4. You use the System.Security.Cryptography namespace. You want to use the key lengths of 384 bits to 16384 bits. You use RSACryptoServiceProvider class to encrypt and decrypt data. Which of the following code segments will you use to accomplish this task?
Each correct answer represents a part of the solution. Choose all that apply.
UnicodeEncoding ByteConverter = new UnicodeEncoding();
byte[] DataToEncrypt = ByteConverter.GetBytes( " Encrypt this line for testing " );
byte[] encryptData;
byte[] decryptData;
RSACryptoServiceProvider RSA = new RSACryptoServiceProvider();
encryptData = RSA.Encrypt(DataToEncrypt, true);
Console.WriteLine( " Encrypted : {0} " , ByteConverter.GetString(encryptData));
decryptData = RSA.Decrypt
UnicodeEncoding ByteConverter = new UnicodeEncoding();
byte[] DataToEncrypt = ByteConverter.GetBytes( " Encrypt this line for testing " );
byte[] encryptData;
byte[] decryptData;
RSACryptoServiceProvider RSA = new RSACryptoServiceProvider();
encryptData = RSA.Encrypt(DataToEncrypt, false);
Console.WriteLine( " Encrypted : {0} " , ByteConverter.GetString(encryptData));
decryptData = RSA.Decryp
UnicodeEncoding ByteConverter = new UnicodeEncoding();
byte[] DataToEncrypt = ByteConverter.GetBytes( " Encrypt this line for testing " );
byte[] encryptData;
byte[] decryptData;
RSACryptoServiceProvider RSA = new RSACryptoServiceProvider();
encryptData = RSA.Encrypt(DataToEncrypt, false);
Console.WriteLine( " Encrypted : {0} " , ByteConverter.GetString(encryptData));
decryptData = RSA.Decryp
UnicodeEncoding ByteConverter = new UnicodeEncoding();
byte[] DataToEncrypt = ByteConverter.GetBytes( " Encrypt this line for testing " );
byte[] encryptData;
byte[] decryptData;
RSACryptoServiceProvider RSA = new RSACryptoServiceProvider();
encryptData = RSA.Encrypt(DataToEncrypt, true);
Console.WriteLine( " Encrypted : {0} " , ByteConverter.GetString(encryptData));
decryptData = RSA.Decrypt
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. The application is hosted on Microsoft Windows Server 2008. Only FTP access is available to the server. You need to improve the searching of the pages in the search engines by taking action to URLs that do not have an .aspx file extension. You must ensure that all pages as well as static content can also be requested. What will you do to accomplish this?
Use an HttpHandler object.
Use a Request object.
Use an HttpModule object.
Use an ISAPI filter.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You are creating an assembly. The assembly contains a public method. The Global Assembly Cache contains a second assembly. You require that the public method is only called from the second assembly. Which of the following permission classes will you use to accomplish this task?
DataProtectionPermission
DBDataPermission
StrongNameIdentityPermission
GacIdentityPermission
PublisherIdentityPermission
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You have recently finished development of Web services using the .NET Framework. The access control to Web services is part of your accountability. You are currently revealing an existing class as a XML Web service. You are required to ensure that the XML Web service is exclusively accessible to Web service clients within the ABC Inc. domain. To fulfill this requirement you want to change the access modifiers on methods that must be represented as Web methods. What will you do to accomplish this task?
Use the Public access modifier for each Web method.
Use the Private access modifier for each Web method.
Use the Internal or Friend access modifier for each Web method.
Use the Protected access modifier for each Web method.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You are creating an ASP.NET Web application using .NET Framework 3.5. The application will be accessed by users from remote locations over the Internet. You need to use ASP.NET role management. You must ensure that any authorization information cached on remote client computers is as secure as possible. What will you do?
Use the RsaProtectedConfigurationProvider class.
Use the DpapiProtectedConfigurationProvider class.
Set the cookieProtection attribute to Validation in the roleManager element of the Web.conf ig file.
Set the cookieProtection attribute to Encryption in the roleManager element of the Web.con fig file.
Peter works as a Software Developer for GenTech Inc. He develops an application named App1 using Visual Studio .NET. App1 uses an assembly named Assembly1. Peter installs App1 and Assembly1 to the C:\Program Files\App1 and C:\Program Files\Assembly1 folders respectively. While executing App1, Peter finds that App1 fails to execute with TypeLoadException. What will he do to resolve this issue.
Each correct answer represents a part of the solution. Choose all that apply.
Uninstall Assembly from the C:\Program Files\Assembly1 folder.
Reinstall Assembly1 to the C:\Windows\Microsoft .NET Framework\Assembly1 folder.
Reinstall Assembly1 to the C:\Program Files\App1 folder.
Change the system path to C:\Program Files\Assembly1.
You work as a Software Developer for ManSoft Inc. You use Microsoft Visual Studio to create a Web service named MyWebService. You create a SOAP message that is not secure in the Web service. You want to use the SoapFilter class in the Web service to filter the SOAP message. Which of the following code segments will you use to accomplish the task?
Each correct answer represents a part of the solution. Choose all that apply.
public class MySoapFilter : SoapFilter
{
string soapmsg= " This is the soap message I want to filter " ;
public MySoapFilter()
{ }
public override SoapFilterResult ProcessMessage(SoapEnvelope envelope)
{
this.Trace(soapmsg);
return SoapFilterResult.Continue;
}
}
public class MySoapFilter : SoapFilter
{
string soapmsg= " This is the soap message I want to filter " ;
public override SoapFilterResult ProcessMessage(SoapEnvelope envelope)
{
this.Trace(soapmsg);
return SoapFilterResult.Continue;
}
}
public class MySoapFilter : SoapFilter
{
string soapmsg= " This is the soap message I want to filter " ;
public override SoapFilterResult ProcessMessage(SoapEnvelope envelope)
{
this.Trace();
return SoapFilterResult.Continue;
}
}
public class MySoapFilter : SoapFilter
{
string soapmsg= " This is the soap message I want to filter " ;
public MySoapFilter()
{ }
public override SoapFilterResult ProcessMessage(SoapEnvelope envelope)
{
this.Trace(soapmsg);
return SoapFilterResult;
}
}
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. You create an application using .NET Framework. You use the application to create an assembly. Now you need to encrypt assembly data. The company has not provided encryption requirements to you. Which of the following symmetric cryptography classes will you use to accomplish this task?
RSA
3DES
RijndaelManaged
DES
TDEA
You work as a Software Developer for ManSoft Inc. The company uses Visual Studio .NET as its application development platform. You create an application named MyRandomGen. You use the System.Security.Cryptography namespace. You want to create a code that randomly rolls the dice fifty times and displays the results on the screen. Which of the following code segments will you use to accomplish this task?
for(int x = 0; x < = 50; x++)
Console.WriteLine(RollTheDice(6));
public static int RollTheDice(int sides)
{
byte[] random = new byte[1] ;
RNGCryptoServiceProvider Gen = new RNGCryptoServiceProvider();
Gen.GetBytes(random);
int ran = Convert.ToInt32(random[0]);
return ran % sides + 1;
}
for(int x = 0; x < = 50; x++)
Console.WriteLine(RollTheDice(6));
public static int RollTheDice(int sides)
{
byte[] random = new byte[1] ;
RNGCryptoServiceProvider Gen = new RNGCryptoServiceProvider();
Gen.GetRandom(random);
int ran = Convert.ToInt32(random[0]);
return ran % sides + 1;
}
for(int x = 0; x < = 50; x++)
Console.WriteLine(RollTheDice(6));
public static int RollTheDice(int sides)
{
byte[] random = new byte[1] ;
RNGCryptoServiceProvider Gen = new RNGCryptoServiceProvider();
Gen.GetBytes(Gen);
int ran = Convert.ToInt32(random[0]);
return ran % sides + 1;
}
for(int x = 0; x < = 50; x++)
Console.WriteLine(RollTheDice(6));
public static int RollTheDice(int sides)
{
byte[] random = new byte[1] ;
RNGCryptoServiceProvider Gen = new RNGCryptoServiceProvider();
Gen.RandomNumber(random);
int ran = Convert.ToInt32(random[0]);
return ran % sides + 1;
}
Sam works as a Software Developer for GenTech Inc. He develops an ASP.NET application, named App1, using Visual Studio .NET. App1 is used within the company ' s intranet. Employees use Internet Explorer on the intranet. Sam creates a page named Page1.aspx. Sam wants the page to be redirected to the home page if an error occurs. Which of the following attributes of the @ Page directive will he use to accomplish the task?
MasterPageFile
CodePage
PageError
ErrorPage
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You are creating an application for a Bank using the .NET Framework. You create a method that gets the images of cancelled checks and displays them. You presently have access to a method that reads the images from a SQL server database as a sequence of bytes. You need to transfer the image from the SQL server database to a form with the least amount of temporary buffers and files. Which of the following classes will you use to accomplish this task?
FileStream
NetworkStream
BufferedStream
MemoryStream
Julia works as a Software Developer for Mansoft Inc. She develops an application using Visual Studio .NET. The application uses a method named MyMethod, which is located in an unmanaged DLL. Julia wants MyMethod to require the application to allocate unmanaged memory, fill the data, and pass the memory address to the application. She also wants to ensure that on returning from MyMethod, the application de-allocates the unmanaged memory. What will Julia do to accomplish the task?
Use the methods of the MemoryStream class.
Derive a new class from the Stream class, and override the allocation methods.
Use the Marshal class.
Use a byte array.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are in the process of creating an application that will handle unmanaged code using the .NET Framework 2.0. Which of the following services will you use to provide interoperability with the unmanaged code?
Each correct answer represents a complete solution. Choose two.
Windows service
COM Interop Service
Platform Invocation Service
.NET Service Installer
You work as a Software Developer for ABC Inc. You create a Web service named MyWebService using Visual Studio .NET. You implement a public Web method. You make the method accessible through a Web service application by attaching the WebMethod attribute to the public method. The public method is stored in the class file of the Web service file. When you create a Web service project using the Web service project template, by default, one public method named HelloWorld is created. The HelloWorld public method does not become available through the Web service until you attach the WebMethod attribute. The method must be applied to each method declaration. Now, you want to configure a Web service method. You want to ensure that the Web method performs updates on more than one databases or if the sequence of updates is critical to the overall success of the Web method. Which of the following properties will you use to accomplish this task?
TransactionOption
Description
BufferResponse
EnableSession
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Windows application using the .NET Framework. The application contains many controls. You add an ErrorProvider component named errorPro and a DateTimePicker control named datePick to the application. You are required to configure the application to display an error notification icon next to datePick when a user enters a date that is greater than today ' s date. What will you do to accomplish this task?
Each correct answer represents a part of the solution. Choose two.
Create an event handler named verifyDate for the Validating event of datePick.
Create an event handler named verifyDate for the Validated event of datePick.
In the verifyDate event handler, call errorPro.SetError(datePick, " Date is greater then today ' s date " ) if the value of datePick value is greater than today ' s date.
In the verifyDate event handler, call errorPro.SetError(datePick, " " ) if the datePick.Value is greater than today ' s date.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You are creating a .NET remoting application using .NET Framework 2.0. You are using Soap to exchange structured and type information on the Web. You want to ensure that all the parameters are contained within the single element in a SOAP message body. Which of the following Soap message formatting types will you use to accomplish the task?
Document-Based Body Formatting
Literal Parameter Formatting
Encoded Parameter Formatting
RPC-Based Body Formatting
Tony works as a Software Developer for TechNet Inc. He creates a satellite assembly named
SatAssembly1. He wants to install SatAssembly1 in the global assembly cache. Therefore, he compiles the assembly by using the Al.exe tool and signs SatAssembly1. Which of the following possible tools will Tony use to sign SatAssembly1?
Each correct answer represents a complete solution. Choose two.
File Signing tool
.NET Services Installation tool
Installer tool
Strong Name tool
Maria works as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. She creates a Web service and uses a Session object in it. She declares a variable in the Session object. What will be the scope of the variable?
The variable will be available as long as a user interacts with it.
The variable will be available forever.
The variable will be available even after the session becomes inactive.
The variable will be available as long as the session is active.
Sam works as a Software Developer for GenTech Inc. The company uses Visual Studio .NET as its application development platform. Sam develops an application named App1 using Visual C# .NET. App1 uses a non-COM DLL named Value1.dll, which contains unmanaged code. Sam wants to write a method named Method1 in Value1.dll. He wants to use Method1 for parsing a string into an array of string values and an array of numbers. He decides to specify three parameters for Method1. The first parameter will contain a static string value. After executing Method1, the second parameter will contain all string values found in the first parameter, and the third parameter will contain all integer values found in the first parameter. Sam wants to enable App1 to call this function. Which of the following code will he use to accomplish this?
int Method1 Lib " Value1.dll " (string, out string, out int);
int Method1 Lib " Value1.dll " (string, ref string, ref int);
int Method1 Lib " Value1.dll " (ref string, string, int);
int Method1 Lib " Value1.dll " (string, string, int);
You work as a Software Developer for SunSoft Inc. The company uses Visual Studio .NET 2005 as its application development platform. You use .NET Framework 2.0 to create several Windows applications. All applications use a common class library assembly named Customers. You deploy the application to the client computers on your company ' s intranet. Later, you modify the assembly. Any application that uses version 1.0.0.0 must now use version 2.0.0.0. Which of the following options will you use to accomplish the task?
Modify the Publisher Policy file containing a reference to Customers.
Modify the application configuration file for Customers.
Modify the reference path for Customers.
Modify the machine configuration file on your client computers.
Mark works as a Web Developer for TechCom Inc. He creates an ASP.NET application named
Application1 by using Visual Studio .NET. Only registered users of the company will be able to use the application. The application contains a page named UserAcc.aspx that allows new users to register themselves to the registered users ' list of the company. The UserAcc page contains several text box controls that accept users ' personal details such as user name, password, home address, zip code, phone number, etc. One of the text box controls on the page is named ZipProperty in which a user enters a zip code.
Mark wants to ensure that when a user submits the UserAcc page, ZipProperty must contain five numeric digits. Which of the following validation controls will he use to accomplish the task?
Each correct answer represents a complete solution. Choose two.
RequiredFieldValidator
RangeValidator
CompareValidator
RegularExpressionValidator
RequiredValidator
Mark works as a Software Developer for BlueWell Inc. He develops four Windows-based applications using Visual Studio .NET. All the applications use an assembly , named Assembly1. Mark deploys the applications on the company ' s intranet. Later, he modifies Assembly1 and wants to ensure that all the applications use the latest version of Assembly1. Which of the following files will Mark use to accomplish this?
Publisher policy configuration file
Security configuration file
Machine configuration file
Application configuration file
You work as a Web Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Web application using .NET Framework 2.0. You add a Web Form that contains a button named bCancel. The button allows users to exit the form. When users click the button, validation should not occur. However, during testing you find that clicking the button does not allow users to exit the form. You need to ensure that users can always exit the page. What will you do?
Set the CausesValidation property of the bCancel button to false.
Set the AccessibleName property of the validation controls on the Web Form to " false " .
Set the ControlToValidate property of the validation controls on the Web Form to the ID of the control.
Set the Enabled property of the validation controls on the Web Form to false.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. You need to represent a strongly typed lambda expression as a data structure in the form of an expression tree. Which of the following classes will you use to accomplish the task?
MethodCallExpression
Expression(TDelegate)
Expression
LambdaExpression
John works as a Web Developer for CyberNet Inc. He develops an ASP.NET application, named MyApp1, using Visual Studio .NET. The application will be used for online-shopping. He deploys the application on the company ' s Web server. The application receives millions of hits daily. In order to improve the performance of the application, John decides to use the in-process state management feature of ASP.NET for storing the session state information. Which of the following attributes will John use in the < sessionState > element of the application ' s Web.config file to accomplish the task?
mode= " InProcess "
sessionMode= " InProc "
sessionMode= " InProcess "
mode= " InProc "
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You are developing an application using .NET Framework 2.0. You are required to use a datatype that will store only the numbers. The numbers should be in positive form and should not be larger than 65,535. Which of the following datatypes will you use to accomplish the task?
Each correct answer represents a complete solution. Choose two.
int
short
System.UInt16
ushort
System.Int16
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You have recently finished the development of a class named TestCase and you have used only reference types in the class. The class will be used in an application that will use pointers. Therefore, you are required to convert the reference types to pointers in the class. Which of the following keywords will you use to accomplish the task?
base
virtual
override
unsafe
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You create a Web service using .NET Framework 2.0. You want the Web service to utilize a two step process to map XML generated by Web methods to .NET objects. What will you do to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
Use deserialization
Use serialization
Use Marshal-by-ref objects
Use Marshal-by-value objects
You work as a Software Developer for ABC Inc. You have created a console application that uses two threads, named thread1 and thread2. You need to modify the code to prevent the execution of thread1 until thread2 completes its execution. Which of the following steps will you take to accomplish this task?
Use a WaitCallBack delegate to synchronize the threads.
Call the sleep() method of thread1.
Call the SpinWait() method of thread1.
Configure thread1 to run at a lower priority.
Configure thread2 to run at a higher priority.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You are creating an ASP.NET Web application using .NET Framework 3.5. The application can be run only by a specific set of user credentials. Therefore, other applications are not permitted to employ these user credentials. The ASP.NET application uses asymmetric encryption to encrypt and decrypt messages to other servers. You are required to shield the private key that is used to encrypt and decrypt messages that are accessed by other users or applications on the same server. What will you do to accomplish the task?
Use the Triple Data Encryption Standard algorithm to encrypt the key.
Use the Secure Sockets Layer protocol.
Use the DataProtectionPermission class.
Use the ProtectedData class.
Store the private key in the App_Data directory.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You have created a class named Customer to be used in a billing application. The Customer class is shown below.
class Customer
{
public string FirstName { get; set; }
public string LastName { get; set; }
}
Each instance of the Customer class contains information about a customer of your company. You have written a segment of code that populates an ArrayList with a collection of Customer objects as shown below.
ArrayList customers = new ArrayList();
Customer myCustomer = new Customer();
myCustomer.FirstName = " Helen " ;
myCustomer.LastName = " of Troy " ;
customers.Add(myCustomer);
myCustomer = new Customer();
myCustomer.FirstName = " Elvis " ;
myCustomer.LastName = " Presley " ;
customers.Add(myCustomer);
You need to write code that iterates through the customers ArrayList and displays the name of each customer at the command prompt.
Which code segment should you choose?
foreach (Customer customer in customers) {
Console.WriteLine( " {0} {1} " ,
(Customer)customer.FirstName,
(Customer)customer.LastName);
}
foreach (Customer customer in customers) {
Console.WriteLine( " {0} {1} " ,
customer.FirstName,
customer.LastName);
}
for (int counter = 0; counter < = customers.Count; counter++) {
Console.WriteLine(customers[counter].ToString());
}
for (int counter = 0; counter < = customers.Count; counter++) {
Console.WriteLine(customers[counter]);
}
You work as a Software Developer for Mansoft Inc. The company uses Visual Studio.NET as its application development platform. You create an ASP.NET Web application using the .NET Framework. You want to authenticate the application and then deploy it on a server running
Microsoft Windows Server 2003 Standard Edition hosting Microsoft Internet Information Services 6.0. Which of the following authentication methods will you use to accomplish the task?
Each correct answer represents a complete solution. Choose two.
Integrated Windows
Extensible Authentication Protocol
Windows NT
Anonymous
Basic
John works as a Web developer for HiTech Inc. He develops an application named MyApp by using Visual C# .NET. John uses a SQL Server database. He writes the following code:
OleDbCommand cmd = new OleDbCommand();
cmd.CommandText = " UPDATE Employees SET Rank = ' Senior ' WHERE Basic > 10000 " ; cmd.ExecuteNonQuery();
Now he wants to improve the performance of the program code. Which of the following actions will he perform to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Use a Cache object to execute the program code.
Use a SqlCommand object instead of an OleDbCommand object.
Use the Prepare method on the OleDbCommand object before executing the program code.
Use an OleDbDataReader object to execute the program code.
Use database indexing.
Use a stored procedure instead of the CommandText property.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You create a remoting application that provides stock information to customers using .NET Framework. The server component raises an event on the client computer when certain conditions are met. You must ensure that the server raises exactly one event for each client application that is registered for the event. What will you do to accomplish this task?
Configure the server class as a Singleton Activated Object (SAO) and check for duplicate client delegate methods before raising the event.
Configure the server class as a Client Activated Object (CAO) and override the CreateObjRef method to check for duplicate client delegate methods before raising the event.
Configure the server class as a SingleCall Activated Object (SAO) and check for duplicate client delegate methods before raising the event.
Configure the server class as a Client Activated Object (CAO) and check for duplicate client delegate methods before raising the event.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You have recently finished the development of an ASP.NET Web application using .NET Framework 3.5. The application must be deployed by using the http://www.ABC.com/ URL. The application has several Web forms.
You need to implement Really Simple Syndication (RSS) feeds functionality. The RSS feeds will be used by the http://www.ABC.com/Updates.rss URL. You must ensure that the application displays the RSS-formatted information when accessing the given URL. What will you do to accomplish this?
Each correct answer represents a part of the solution. Choose two.
Create and register a custom HttpHandler class that releases the RSS feeds.
Create a Web form named Updates that releases the RSS feeds.
Create an ASMX Web service component named Updates.
Add the HttpHandler class to the .rss extension.
Create and register a custom HttpModule class.
You work as a Software Developer for ManSoft Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You are creating a global application that will be used by all the branches of the company. You want to perform the encoding of Unicode characters. Which of the following classes will you use to accomplish the task?
Each correct answer represents a complete solution. Choose three.
UnicodeEncoding
ASCIIEncoding
UTF32Encoding
UTF8Encoding
You work as a Software Developer for ABC Inc. You create a Console application to create multiple satellite assemblies. Which of the following statements about satellite assemblies are true?
Each correct answer represents a complete solution. Choose all that apply.
They do not contain any executable code.
They are used to deploy language-specific resources for an application.
The Assembly Linker tool is used to compile .resources files into satellite assemblies.
An application can have only one satellite assembly.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You create an ASP.NET Web application using the .NET Framework 3.5. 91. The application uses ASP.NET AJAX, and you need to deploy it in a Web farm environment. You are required to configure SessionState for the application. Which of the following code segments will you use to accomplish this task?
< sessionState mode= " InProc " cookieless= " UseDeviceProfile " / >
< sessionState mode= " InProc " cookieless= " UseCookies " / >
< sessionState mode= " SQLServer " cookieless= " UseUri " sqlConnectionString= " Integrated
Security=SSPI;data source=MySqlServer; " / >
< sessionState mode= " SQLServer " cookieless= " false " sqlConnectionString= " Integrated
Security=SSPI;data source=MySqlServer; " / >
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You create an ASP.NET Web application using the .NET Framework 3.5. The application uses Session objects. You are changing the application to run on a Web farm. You want to make sure that the application can access the Session objects from all the servers in the Web farm. You also make sure that when any server in the Web farm restarts or stops responding, the Session objects are not lost. What will you do?
Use InProc Session Management mode to store session data in the ASP.NET worker process
Use StateServer Session Management mode to store session data in a common State Server process on a Web server in the Web farm
Use SQLServer Session Management mode to store session data in an individual database for each Web server in the Web farm
Use SQLServer Session Management mode to store session data in a common Microsoft SQL Server 2005 database
Which of the following code snippets is an example of tight encapsulation?
protected int x;
protected void fun(){x=5;}
int x;
public void fun(){x=5;}
public int x;
public void fun() {x=5;}
private int x;
public void fun(){x=5;}
private int x;
private void fun(){x=5;}
George works as a Software Developer for GenTech Inc. He creates an application named App1 using Visual Studio .NET. App1 uses the version 2.0.0.0 of an assembly named Assembly1. However, he wants App1 to use a new version i.e. 2.1.0.0 of Assembly1. Therefore, he needs to specify Assembly1 ' s location so that App1 can use version 2.1.0.0 of Assembly1. What will George use to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
The < probing > element.
A managed code.
The < codeBase > element.
An unmanaged code.
You work as a Software Developer for ABC Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You are creating an application using .NET Framework 2.0. The application will be used by all the branches of the company. You sometimes require a variable number of arguments to be passed to a method. For example, you may require a sum method, which calculates the total of the numbers passed to it no matter how many numbers are passed. What will you do to accomplish the task?
Use the base keyword.
Use the ref keyword.
Use the params keyword.
Use the out keyword.
Use the volatile keyword.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET as its application development platform. You need to read the entire contents of a file named Msg.txt into a single string variable using .NET Framework. Which of the following code segments will you use to accomplish the task?
string NewResult = string.Empty;
StreamReader Strreader = new StreamReader( " Msg.txt " );
While (!Strreader.EndOfStream) {
NewResult += Strreader.ToString();
string NewResult = null;
StreamReader Strreader = new StreamReader( " Msg.txt " );
NewResult = Strreader.ReadLine();
string NewResult = null;
StreamReader Strreader = new StreamReader( " Msg.txt " );
NewResult = Strreader.ReadToEnd();
string NewResult = null;
StreamReader Strreader = new StreamReader( " Msg.txt " );
NewResult = Strreader.Read().ToString();
You work as an Enterprise Application Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create a logging utility class using .NET Framework 3.5. The utility class writes logs to event log services. You are required to ensure that the client applications that use the utility class can create an instance of the utility class only if they have access rights to write to the event log services.
What will you do?
Use role based security in the class constructor.
Use declarative security check on the assembly.
Use role based security on the class.
Use code access security on the class.
You work as a Web Application Developer for SunInfo Inc. The company uses Visual Studio 2008 as its application development platform. You create a Web application using .NET Framework 3.5. You use foreach loops to retrieve data from a collection. Now, you want to use LINQ queries instead of foreach loops. Choose the advantages of using LINQ queries over foreach loops.
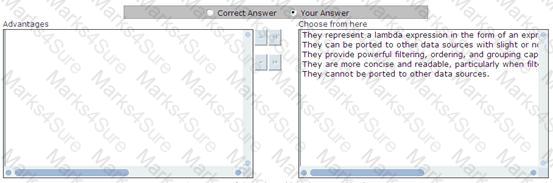
You work as a Software Developer for Blue Well Inc. You create a mobile Web application for mobile users. You want to ensure that a cookieless session is implemented on it. Which of the following statements are the main reasons of implementing a cookieless session on a mobile Web application?
Each correct answer represents a part of the solution. Choose two.
Tests mobile Web applications
Stores data in Web server memory
Ensures better compatibility with mobile devices
Maintains session state of each user
Dilton works as a Software Developer for GREC Research Center (Central). This research center has its subsidiaries in several different cities. Dilton wants to retrieve a Soil Test Report for the Geological Survey Department. He wants the test report to be available to all the members of the department over the Internet. He creates an XML Web service named SampleReport. SampleReport contains a Web method named SoilTestDetails that requires additional security.
Dilton decides to use generic role-based security to secure the SoilTestDetails method from unauthorized users. Dilton writes code to ensure that once a user is authenticated, a user identity named Generic is created. The Generic user identity has a group membership named GeoSurvey to allow the authenticated users access to the SoilTestDetails Web method. Which of the following code segments should Dilton use to accomplish the task?
GenericIdentity GenIdentity = new GenericIdentity( " Generic " , " Custom " );
string[] GeoRoles = { " GeoSurvey " };
GenericPrincipal GeoPrincipal = new GenericPrincipal(GenIdentity, GeoRoles);
Thread.CurrentPrincipal = GeoPrincipal;
IIdentity GeoIdentity = new GenericIdentity( " Generic " , " Custom " );
WindowsIdentity WinGeoIdentity = (WindowsIdentity) GeoIdentity;
string[] GeoRoles = { " GeoSurvey " };
GenericPrincipal GenGeoPrincipal = new GenericPrincipal(WinGeoIdentity, GeoRoles );
WindowsIdentity.Impersonate(WinGeoIdentity.Token);
IIdentity GeoIdentity = new GenericIdentity( " Generic " , " GeoSurvey " );
IPrincipal GeoPrincipal = new WindowsPrincipal((WindowsIdentity) GeoIdentity);
Thread.CurrentPrincipal = GeoPrincipal;
System.Security.Principal.IIdentity MyGenericIdentity = new GenericIdentity( " Generic " ,
" Custom " );
string[] GeoRoles = { " GeoSurvey " };
GenericPrincipal GenGeoPrincipal = new GenericPrincipal(MyGenericIdentity, GeoRoles);
MyGenericIdentity = WindowsIdentity.GetCurrent();
Peter works as a Software Developer for PatSoluTech Inc. He creates a .NET assembly using Visual Studio .NET. He wants to use this assembly in multiple .NET applications on a local computer. He decides to deploy the assembly into the global assembly cache (GAC). What will he do to accomplish the task?
Each correct answer represents a complete solution. Choose two.
Set the public attribute for the assembly.
Register the assembly within the GAC using Gacutil.exe.
Register the assembly within the GAC using Regasm.exe.
Give a strong name to the assembly.
You work as a Software Developer for ABC Inc. You create an ASP.NET Web application named MyWebApplication. You want to provide secure access to company ' s customers. You want to enable users to access the site from any browser by providing their user name and password. Which of the following authentication methods will you use to accomplish this task?
Windows NT
Secure Socket Layer
Basic
Single Sign-On
Certificate Server
Allen works as a Software Developer for ManSoft Inc. The company uses Visual Studio.NET as its application development platform. He creates an application. He wants to allow remote users to connect and access the application through a dial-up connection via the Internet. All data will be sent across a public network. For security reasons, the management wants to send data through the Internet in an encrypted form. The company plans to use a Layer 2 Tunneling Protocol (L2TP) connection. Which of the following communication protocols will Allen use to accomplish the task?
IP Security (IPSec)
Secure Electronic Transaction (SET)
Pretty Good Privacy (PGP)
Triple Data Encryption Standard (3DES)
You work as a Software Developer for ManSoft Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You create an application that will be used by all the branches of the company. You use the Regex class in the application to validate some strings. You want to search an input string for an occurrence of a regular expression. Which of the following methods of the Regex class will you use to accomplish the task?
Match
Matches
Equals
IsMatch
You work as an ADO.NET Application Developer for ABC Inc. The company uses Microsoft Visual Studio .NET 2008 as its application development platform. You create an ADO.NET application by using .NET Framework 3.5. You are using the System.Linq.Expressions namespace to represent the code expression as objects in the form of expression trees. You want to initialize the members of a newly created object. What will you do to accomplish the task?
Use the MemberBinding class
Use the UnaryExpression class
Use the MemberBindingType enumeration
Use the MemberListBinding class
John works as a Web Developer for ABC Inc. He develops an ASP.NET application, named MyApp1, using Visual Studio .NET. The application will be used in the Sales department to generate monthly reports. John wants to deploy the application on the company ' s intranet. The company uses Microsoft Windows authentication. John wants to deny access to all the members of the Guest1 role. Which of the following attributes will he use in the < authorization > element of the application ' s Web.config file to accomplish the task?
< deny= " Guest1 " / >
< deny users=Guest1( " All " ) / >
< deny users= " Guest1 " / >
< deny roles= " Guest1 " / >
Adam works as a Software Developer for ABC Inc. He creates an ASP.NET application, named MyApp. During beta testing of MyApp, he ensures that both developers and beta testers see the actual text of error messages. Adam performs beta testing of other applications on the same test server. All the other applications display ASP.NET error messages. After completing beta testing, Adam promotes the beta test server to a production server. He wants all the applications to display a single, userfriendly error message. Adam also wants to configure MyApp and the production server to meet these goals. What will he do to accomplish the required task with minimum administrative effort?
In the Web.config file for MyApp, add the following element:
< customErrors mode= " RemoteOnly " / >
In the Machine.config file, add the following element:
< customErrors mode= " On " / >
In the MyApp.config file, add the following element:
< customErrors mode= " On " / >
In the MyApp.config file, add the following element:
< customErrors mode= " RemoteOnly " / >
In the Web.config file for MyApp, add the following element:
< customErrors mode= " On " / >
In the Machine.config file, add the following element:
< customErrors mode= " RemoteOnly " / >
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You are developing the data access component that all applications in your company intranet will use to access Microsoft SQL Server. You must include code to correctly catch and iterate through any number of errors that could be encountered when connecting to SQL Server. Which code segment should you choose?
string connectionString =
" server=(local); database=Northwind; "
+ " integrated security=true; " ;
using (SqlConnection cnn = new SqlConnection(connectionString)){
try {
cnn.Open();
} catch (Exception ex) {
// handle the exception...
} catch (SqlException ex) {
foreach (SqlError error in ex.Errors) {
// handle the exception...
}
} finally {
// clean up
}
string connectionString =
" server=(local); database=Northwind; "
+ " integrated security=true; " ;
using (SqlConnection cnn = new SqlConnection(connectionString)){
try {
cnn.Open();
} catch (SqlException ex) {
foreach (SqlError error in ex.Errors) {
// handle the exception...
}
} catch (Exception ex) {
// handle the exception...
} finally {
// clean up
}
string connectionString =
" server=(local); database=Northwind; "
+ " integrated security=true; " ;
using (SqlConnection cnn = new SqlConnection(connectionString))}
try {
cnn.Open();
} catch (SqlException ex) {
switch (ex.Number) {
case 1:
// handle the exception...
break;
default:
// handle the exception...
break;
}
} catch (Exception ex) {
//
string connectionString =
" server=(local); database=Northwind; "
+ " integrated security=true; " ;
using (SqlConnection cnn = new SqlConnection(connectionString)){
try {
cnn.Open();
} catch (SqlException ex) {
switch (ex.Number) {
case 1:
// handle the exception...
break;
default:
// handle the exception...
break;
}
} catch (Exception ex) {
//
You work as a Database Developer for a Web based music company named Music2Music. You are designing a database for online order management application. The customers use the company ' s Web site to place orders for the music CDs. Orders details are first inserted into an online database named OrdersData. The Orders database includes a table named Orders and a table named OrderDetails. The Orders table contains basic information about the orders. The OrderDetails table contains information about the individual items in the orders. Fragments of the Orders database is given below:
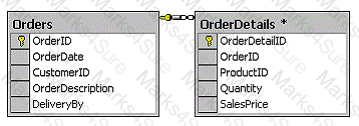
Requirements of the database design are given below:
l Customers must be able to use the company ' s Web site to view orders stored in the OrdersData database.
l Customers should be able to see only their own orders.
l Customers should not be able to modify the orders.
l The primary key values of the orders are not relevant to the customers and should not be
visible. What will you do?
Create a view that displays the order information for a customer.
Create a stored procedure that retrieves the order information for a customer.
Grant SELECT permissions on the Orders and OrderDetails tables to the customers
Create a scalar user-defined function that retrieves the order information for a customer.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You create an ASP.NET Web application using the .NET Framework 3.5. The application is used to map HTTP requests to HTTP handlers based on a file name extension. You need to ensure that each HTTP handler processes individual HTTP URLs or groups of URL extensions in the application.
Which of the following built-in HTTP handlers will you use to accomplish this task?
Each correct answer represents a part of the solution. Choose all that apply.
Generic Web handler (*.ashx)
Generic handler (*.ashx)
Web service handler (*.asmx)
ASP.NET page handler (*.aspx)
Trace handler (trace.axd)
You work as a Software Developer for ManSoft Inc. The company uses Visual Studio .NET 2005 as its application development platform. You create an application named MyApplication using Visual C# .NET. You use the Mutex class for synchronization among threads. You create three threads to enter the protected area one by one. This means that if one thread is already in the protected area, no other thread is allowed to enter in the protected area. When you execute the application, it gives the following output:
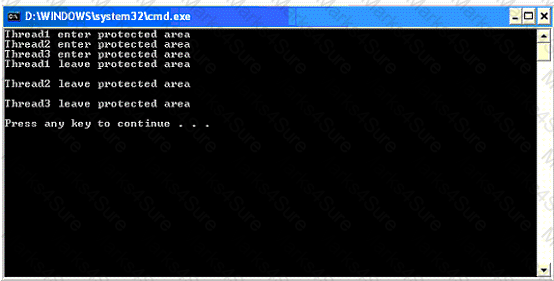
As you can see in the above code window, all the three threads enter the protected area at the same time. Drag and drop the appropriate statements that will allow the threads to enter the protected area one by one.
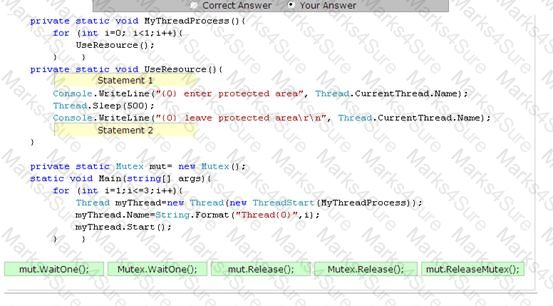
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create the definition for a Car class by using the following code segment:
public class Car {
[XmlAttribute(AttributeName = " category " )]
public string CarType;
public string model;
[XmlIgnore]
public int year;
[XmlElement(ElementName = " mileage " )]
public int miles;
public ConditionType condition;
public Car() {
}
public enum ConditionType {
[XmlEnum( " Poor " )] BelowAverage,
[XmlEnum( " Good " )] Average,
[XmlEnum( " Excellent " )] AboveAverage
}}
You create an instance of the Car class. You fill the public fields of the Car class as shown in the table below:
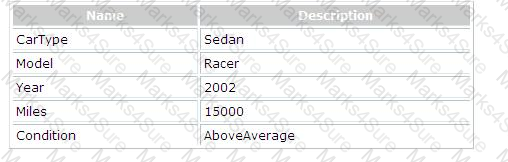
You are required to recognize the XML block that is produced by the Car class after serialization. Which of the following XML blocks represents the output of serializing the Car class?
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema "
category= " sedan " >
< model > racer < /model >
< mileage > 15000 < /mileage >
< condition > Excellent < /condition >
< /Car >
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema " >
< category > sedan < /category >
< model > racer < /model >
< mileage > 15000 < /mileage >
< condition > Excellent < /condition >
<< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema " "
CarType= " sedan " >
< model > racer < /model >
< miles > 15000 < /miles >
< condition > AboveAverage < /condition >
< /Car >
< ?xml version= " 1.0 " encoding= " utf-8 " ? >
< Car
xmlns:xsi= " http://www.w3.org/2002/XMLSchema-instance "
xmlns:xsd= " http://www.w3.org/2002/XMLSchema "
category= " sedan " >
< model > racer < /model >
< mileage > 15000 < /mileage >
< conditionType > Excellent < /conditionType >
< /
You work as a .NET Trainer for ABC Inc. The Company uses .NET Framework as its application development platform. You are creating an application to demonstrate the use of datatypes. You create an unsigned Short datatype in the application. Which of the following values can be assigned to the unsigned Short datatype?
Each correct answer represents a complete solution. Choose three.
123
65,535
127,625
32,636
-123
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2005 as its application development platform. You are creating an application using .NET Framework 2.0. The application uses serialization to allow users to take an instance of an object and convert it into a format that can be easily transmittable over the network or even stored in a database. You want to provide the base functionality for the common language runtime serialization formatters. Which of the following classes will you use to accomplish the task?
SoapFormatter
FormatterConverter
Formatter
BinaryFormatter
Which of the following is a reference type in Visual C#?
primitive types
strings
enums
structures
You work as a Software Developer for ManSoft Inc. You use Microsoft Visual Studio to create a Web service named MyWebService. You create a SOAP message that is not secure in the Web service. You want to use the SendSecurityFilter class in the Web service to handle the transmission and securing of SOAP messages. Which of the following code segments will you use to accomplish the task?
Each correct answer represents a part of the solution. Choose all that apply.
public class MySendSecurityFilter : SendSecurityFilter
{
public MySendSecurityFilter(string service, Boolean client)
{ }
public override void SecureMessage(SoapEnvelope envelope, Security security)
{
// Implement validation here
}
}
public class MySendSecurityFilter : SendSecurityFilter
{
public MySendSecurityFilter(string service, Boolean client)
{
base(service,client);
}
public override void SecureMessage(SoapEnvelope envelope, Security security)
{
// Implement validation here
}
}
public class MySendSecurityFilter : SendSecurityFilter
{
public MySendSecurityFilter(string service, Boolean client) : base(service,client)
{ }
public override void SecureMessage(SoapEnvelope envelope, Security security)
{
// Implement validation here
}
}
public class MySendSecurityFilter : SendSecurityFilter
{
public MySendSecurityFilter(string service, Boolean client) : base(service,client)
{ }
public void SecureMessage(SoapEnvelope envelope, Security security)
{
// Implement validation here
}
}
John works as a Web Developer for Bitsoft Inc. He creates an ASP.NET application, named MyApp1, by using Visual Studio .Net for a University Web site. Students will use MyApp1 to view their term end result. MyApp1 contains an ASP.NET page named, named Page1. Page1 contains a TextBox control, named txtEnrolmentNo, and two Button controls, named btnSubmit and btnCancel respectively.
John wants that if a user tries to submit the page by clicking the Submit button without entering his enrolment the word " Required " appears next to txtEnrolmentNo. However, when a user clicks the Cancel button he is redirected to a new page, named PageCancel.aspx. To accomplish this he adds a RequiredFieldValidator control to the page and sets its ControlToValidate and ErrorMessage properties to txtEnrolmentNo and " Required " respectively. However, when he executes the application he finds that the validation check is also performed on clicking the Cancel button. What is the most likely cause of the issue?
The CauseValidation property of btnSubmit is not set to True.
The CauseValidation property of btnCancel is not set to True.
The CauseValidation property of btnSubmit is not set to False.
The CauseValidation property of btnCancel is not set to False.
You work as a Web Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Web application using .NET Framework 2.0. You add a Web Form that contains a button named bCancel. The button allows users to exit the form. When users click the button, validation should not occur. However, during testing you find that clicking the button does not allow users to exit the form. You need to ensure that users can always exit the page. What will you do?
Set the CausesValidation property of the bCancel button to false.
Set the AccessibleName property of the validation controls on the Web Form to " false " .
Set the ControlToValidate property of the validation controls on the Web Form to the ID of the control.
Set the Enabled property of the validation controls on the Web Form to false.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You create an ASP.NET Web application using the .NET Framework 3.5. You want to use a HTTP module called on each and every request made by the application. It is called as part of the ASP.NET request pipeline. It has right to access life-cycle events throughout the request. You also want to ensure that the HTTP module allows a user to inspect incoming and outgoing requests and take appropriate action based on the request. What will be the correct order to create the HTTP module?
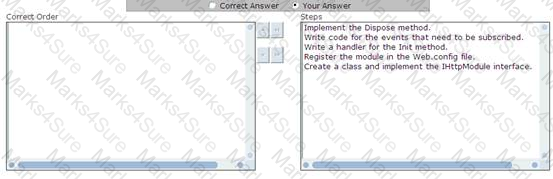
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You are creating an ASP.NET Web application using .NET Framework 3.5. The application will be used to share any type of photos on Internet. All the photos should be accessible in various sizes and formats. You need to add a download feature that can be easily maintained. You also need to make sure that only a single version of all photos is stored on a SQL server database. What will you do?
Create an HttpModule class to determine the request for the photo download. Process the photo according to the given format and size, and after that return the processed photo in the response.
Create a user control that converts the photo to the required format and size.
Create an HttpHandler class to determine the request for the photo download. Process the photo according to the given format and size, and after that return the processed photo in the response.
Create an ActiveX control that converts the photo to the required format and size.
You work as a Software Developer for InfoTech Inc. You create a Windows form in a Windows-based application named MyWinApp1. You use graphics in the form. You write the following code in your form:
private void MyMouseEvent1(object sender1, MouseEventArgs event)
{
// Code to handle mouse events
}
You want to implement a property of the MouseEventArgs object. This property will return a Point structure that contains the x-coordinate and y-coordinate of the mouse. Which of the following properties of the MouseEventArgs object will you use to accomplish this?
Y
Delta
Location
Button
Clicks
X
You work as a Software Developer for ManSoft Inc. You use C# .NET to create an assembly named TestAssembly that will be used by other applications, including a standard COM client application. You must deploy the assembly on the COM application to a client computer. You must ensure that the COM applications can instantiate components within the assembly as COM components. Which of the following options will you use to accomplish this task?
Generate a registry file for the assembly by using the Assembly Registration Tool (Regasm.exe) and register the file on the client computer.
Deploy the assembly to the global assembly cache on the client computer.
Add a reference to the assembly in the COM client application.
Create a strong name of the assembly by using the Strong Name tool(Sn.exe).
Generate a type library for the assembly by using the Type Library Importer (Tlbimp.exe) and register the file on the client computer.
You work as a Software Developer for HiTech Inc. You develop a Web application named
MyWebApp. The application contains several Web pages that display a registration form for a user. You want to perform user input data validation at the server-side, so that you can disable the client-side data input validation. Which of the following actions will you take to accomplish the task?
Set the CausesValidation property of a server control to false.
Set the Enabled property of a validation control to true.
Set the Enabled property of a validation control to false.
Set the EnableClientScript property of a validation control to true.
Set the EnableClientScript property of a validation control to false.
Which of the following modifiers is not available in C#?
private
friend
internal
public
protected
You work as an Application Developer for ABC Inc. You are assigned with developing a Web site that will handle information related to monthly sales of the company. You wish to secure the Web site so that only employees of the Accounts department can view the Web pages. You need to create roles for the employees of this department. The user account information will be stored in a SQL Server database named Database. You decide to do all this by using the Web Site Administration Tool. Which of the following types of security will you use to accomplish the task?
Forms-based authentication
Integrated Microsoft Windows authentication
Basic authentication
Digest authentication
Which of the following attributes of the customErrors element is used to specify whether custom errors are enabled, disabled, or shown only to remote clients?
Off
Mode
On
RemoteOnly
Mark works as a Software Developer for GenTech Inc. He develops an application, named App1, using Visual Studio .NET. The application contains a Form control, named Form1, which enables users to edit information in a SQL Server database. Mark wants to save all the changes made by users in the database. He defines a boolean variable, named DataIsSaved, in the application code. DataIsSaved indicates whether or not all data are saved in the database. Mark wants to prevent Form1 from closing until all the changes are saved in the database. Which of the following code will he use to accomplish this?
protected void Form1_Leave(object sender, System.ComponentModel.CancelEventArgs e) {
if(!DataIsSaved)
Cancel = false;
else
Cancel = true;
}
protected void Form1_Leave(object sender, System.ComponentModel.CancelEventArgs e) {
if(!DataIsSaved)
Cancel = true;
else
Cancel = false;
}
protected void Form1_Closed(object sender, System.ComponentModel.CancelEventArgs e) {
if(!DataIsSaved)
You work as a Software Developer for ABC Inc. The company has several branches worldwide. The company uses Visual Studio.NET 2005 as its application development platform. You have recently finished the development of an application using .NET Framework 2.0. The application can be used only for cryptography. Therefore, you have implemented the application on a computer. What will you call the computer that implemented cryptography?
Cryptographic toolkit
Cryptosystem
Cryptographer
Cryptanalyst
You work as a Software Developer for ABC Inc. The company has several branches worldwide. The company uses Visual Studio .NET 2005 as its application development platform. You are creating an application using .NET Framework 2.0. The application will be used by all the branches of the company. You are using the CompareInfo class for culture-sensitive string comparisons. You write the following code in the application:
String s1 = " C rtify " ;
String s2 = " c rtify " ;
String s3 = " c rtify " ;
You need to compare the s1 string with the s2 string and ensure that the string comparison must ignore case. Which of the following code segments will you use to accomplish the task?
CompareInfo cmp = CultureInfo.InvariantCulture.CompareInfo;
Console.WriteLine(cmp.Compare(s1, s2, CompareOptions.IgnoreCase));
CompareInfo cmp = CultureInfo.InvariantCulture.CompareInfo;
Console.WriteLine(cmp.Compare(s1, s2, CompareOptions.None));
CompareInfo cmp = CultureInfo.InvariantCulture.CompareInfo;
Console.WriteLine(cmp.Compare(s1, s2, CompareOptions.Ordinal));
CompareInfo cmp = CultureInfo.InvariantCulture.CompareInfo;
Console.WriteLine(cmp.Compare(s1, s2, CompareOptions.OrdinalIgnoreCase));
Tony works as a Software Developer for TechNet Inc. He creates a satellite assembly named
SatAssembly1. He wants to install SatAssembly1 in the global assembly cache. Therefore, he compiles the assembly by using the Al.exe tool and signs SatAssembly1. Which of the following possible tools will Tony use to sign SatAssembly1?
Each correct answer represents a complete solution. Choose two.
Installer tool
File Signing tool
.NET Services Installation tool
Strong Name tool
Henry works as a Software Developer for SoftTech Inc. He creates a Windows form named
MyForm1. The form contains detailed information about a student. The form uses a ListBox control named ListBox1 that concatenates two strings displayed in two TextBox controls. Henry wants a method to return a value for the control. Which of the following options will he consider while creating a method for the control?
A method with a string return type.
A void method that passes only one parameter.
A method with an integer return type.
A void method that passes more than one parameter.
Allen works as a Software Developer for ManSoft Inc. He develops an application using Visual Studio .NET 2005. Only the employees of the company use the application. Allen wants to ensure that when a request on a page is made by a user the application asks for his authentication. Which of the following actions will Allen take to accomplish the task?
Each correct answer represents a part of the solution. Choose two.
Specify User.Identity to authenticate the user.
Set the impersonate attribute of the < identity > element to true.
Specify the username and password attributes.
Set the impersonate attribute of the < identity > element to false.
You work as a Software Developer for ABC Inc. You create a Console application to create multiple satellite assemblies. Which of the following statements about satellite assemblies are true?
Each correct answer represents a complete solution. Choose all that apply.
They do not contain any executable code.
An application can have only one satellite assembly.
The Assembly Linker tool is used to compile .resources files into satellite assemblies.
They are used to deploy language-specific resources for an application.
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2008 as its application development platform. You are creating an ASP.NET Web application using the .NET Framework 3.5. The application stores sensitive profile data in a MS SQL Server 2008 database. You are required to make sure that the profile data never stored in clear text. What will you do?
Create a strongly typed custom ProfileProvider class. In the ProfileProvider class, encrypt the provided information before storing it in the database.
Use the ASP.NET IIS Registration Tool to encrypt the connection string to connect to the SQL Server database.
Create a custom profile provider. In the custom provider, encrypt the provided information before storing it in the database.
Enable the SSL encryption for the SQL Server connections.
John works as a Web developer for HiTech Inc. He develops an application named MyApp by using Visual C# .NET. John uses a SQL Server database. He writes the following code:
OleDbCommand cmd = new OleDbCommand();
cmd.CommandText = " UPDATE Employees SET Rank = ' Senior ' WHERE Basic > 10000 " ;
cmd.ExecuteNonQuery();
Now he wants to improve the performance of the program code. Which of the following actions will he perform to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
Use database indexing.
Use an OleDbDataReader object to execute the program code.
Use a Cache object to execute the program code.
Use a SqlCommand object instead of an OleDbCommand object.
Use a stored procedure instead of the CommandText property.
Use the Prepare method on the OleDbCommand object before executing the program code.
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a class library using the .NET Framework. The library will be used to open the NSCs of computers. Later, you will set up the class library to the GAC and provide it Full Trust permission. You write down the following code segments for the socket connections:
SocketPermission permission = new SocketPermission(PermissionState.Unrestricted);
permission.Assert();
A number of the applications that use the class library may not have the necessary permissions to open the network socket connections. Therefore, you are required to withdraw the assertion. Which of the following code segments will you use to accomplish the task?
permission.PermitOnly();
CodeAccessPermission.RevertDeny();
permission.Deny();
CodeAccessPermission.RevertAssert();
permission.Demand();
You work as a Windows Application Developer for ABC Inc. The company uses Visual Studio .NET as its application development platform. You create a Windows application using .NET Framework 2.0. The application allows computer engineers to design circuit boards for different types of hardware. You create a custom control that represents the design surface. You are required to highlight the vacant areas on the design surface where a component can be dropped. Which of the following events will you use to accomplish this task?
DragOver
QueryContinueDrag
DragEnter
DragLeave
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You have recently finished the development of an ASP.NET Web application using .NET Framework 3.5. The application must be deployed by using the http://www.ABC.com/ URL. The application has several Web forms.
You need to implement Really Simple Syndication (RSS) feeds functionality. The RSS feeds will be used by the http://www.ABC.com/Updates.rss URL. You must ensure that the application displays the RSS-formatted information when accessing the given URL. What will you do to accomplish this?
Each correct answer represents a part of the solution. Choose two.
Create and register a custom HttpHandler class that releases the RSS feeds.
Create a Web form named Updates that releases the RSS feeds.
Create an ASMX Web service component named Updates.
Add the HttpHandler class to the .rss extension.
Create and register a custom HttpModule class.
Which of the following provide simplified access to ASP.NET AJAX login, roles, and profile services from Windows Forms and WPF applications?
Entity Framework
AJAX application services
Client application services
Sync Framework

TESTED 02 May 2026
