N10-009 CompTIA Network+ Certification Exam Questions and Answers
Which of the following protocols is used to route traffic on the public internet?
Which of the following requires network devices to be managed using a different set of IP addresses?
Which of the following, in addition to a password, can be asked of a user for MFA?
Which of the following steps of the troubleshooting methodology would most likely include checking through each level of the OSI model after the problem has been identified?
Which of the following should be used to obtain remote access to a network appliance that has failed to start up properly?
An IT manager needs to connect ten sites in a mesh network. Each needs to be secured with reduced provisioning time. Which of the following technologies will best meet this requirement?
A company recently rearranged some users ' workspaces and moved several users to previously used workspaces. The network administrator receives a report that all of the users who were moved are having connectivity issues. Which of the following is the MOST likely reason?
Which of the following is an XML-based security concept that works by passing sensitive information about users, such as login information and attributes, to providers?
Which of the following is the most secure way to provide site-to-site connectivity?
Which of the following allows a network administrator to analyze attacks coming from the internet without affecting latency?
Which of the following is most closely associated with having a leased line to a public cloud provider?
An organization wants to ensure that incoming emails were sent from a trusted source. Which of the following DNS records is used to verify the source?
A network administrator receives complaints of intermittent network connectivity issues. The administrator investigates and finds that the network design contains potential loop scenarios. Which of the following should the administrator do?
Which of the following connector types is most commonly associated with Wi-Fi antennas?
After installing a new wireless access point, an engineer tests the device and sees that it is not performing at the rated speeds. Which of the following should the engineer do to troubleshoot the issue? (Select two.)
A network administrator ' s device is experiencing severe Wi-Fi interference within the corporate headquarters causing the device to constantly drop off the network. Which of the following is most likely the cause of the issue?
Which of the following helps a network administrator understand security risk from external malicious actors and offers insights on which threats to mitigate?
Which of the following routing protocols is most commonly used to interconnect WANs?
Which of the following layers of the OSI model is responsible for end-to-end encryption?
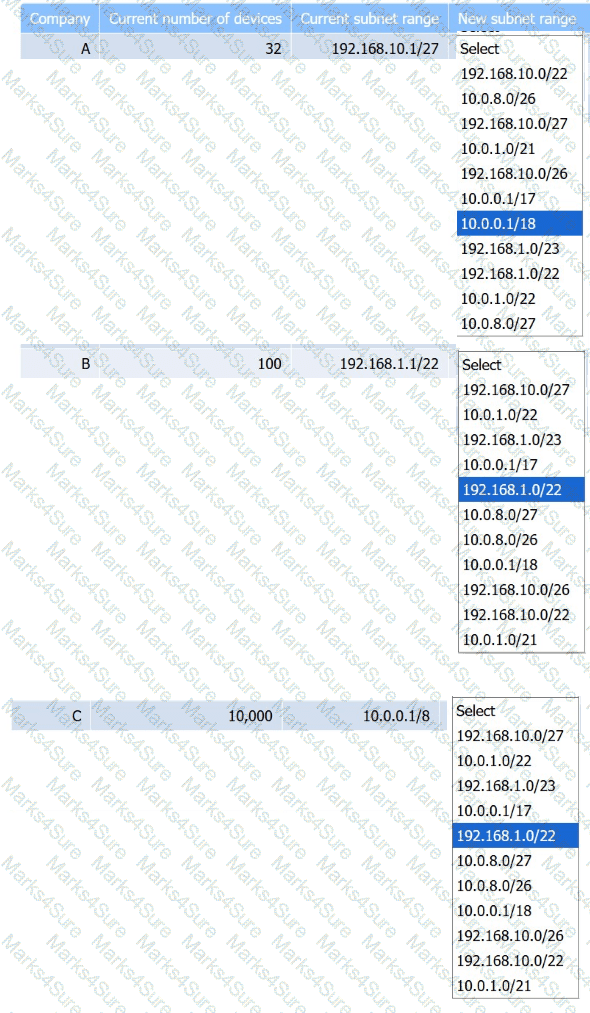
Company C is acquiring Company A and Company B. Company C needs to merge all
three networks into one Class B network. Additionally, the network capacity of each company needs to grow by 20%. Company C also requires segmentation of Company A and Company B to account for unknown security vulnerabilities within each.
Instructions:
Select the correct subnet range to meet Company C ' s requirements.
A junior network administrator gets a text message from a number posing as the domain registrar of the firm. The administrator is tricked into providing global administrator credentials. Which of the following attacks is taking place?
Users at a satellite office are experiencing issues when using videoconferencing. Which of the following should a technician focus on first to rectify these issues?
A customer needs six usable IP addresses. Which of the following best meets this requirement?
A research facility is expecting to see an exponential increase in global network traffic in the near future. The offices are equipped with 2.5Gbps fiber connections from the ISP, but the facility is currently only utilizing 1Gbps connections. Which of the following would need to be configured in order to use the ISP ' s connection speed?
Which of the following protocol ports should be used to securely transfer a file?
A network engineer is completing a wireless installation in a new building. A requirement is that all clients be able to automatically connect to the fastest supported network. Which of the following best supports this requirement?
Which of the following best describes the transmission format that occurs at the transport layer over connectionless communication?
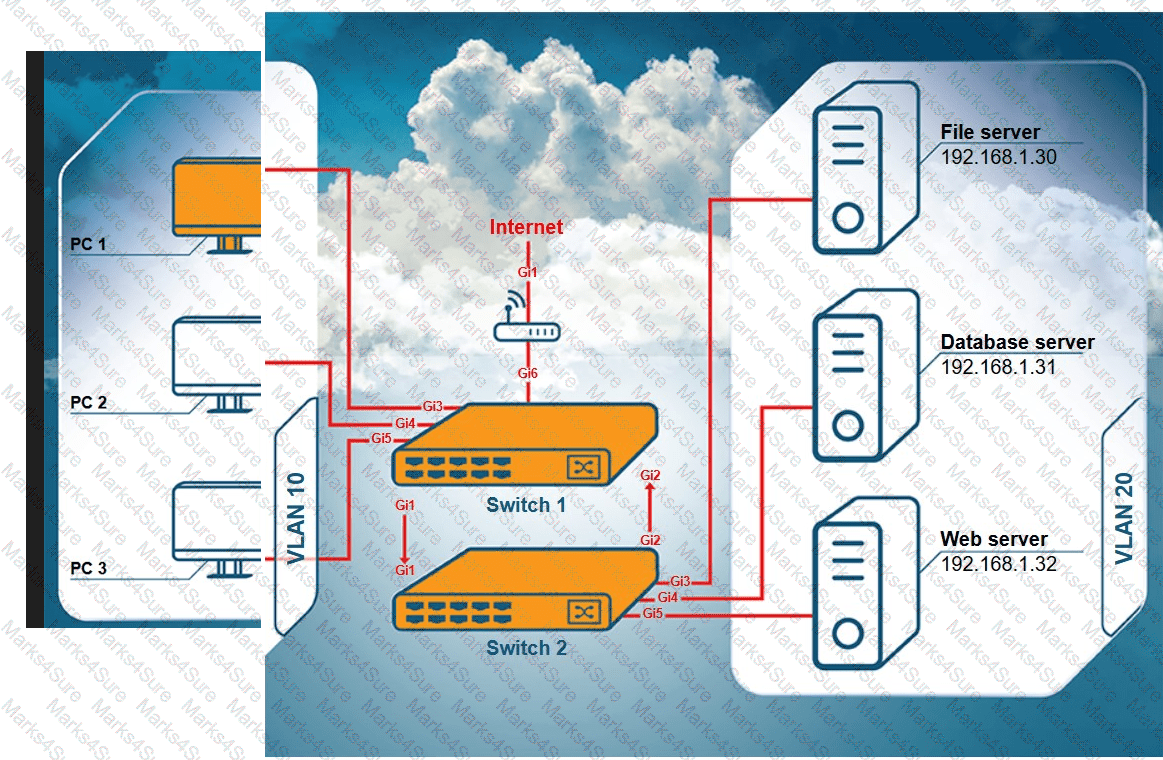
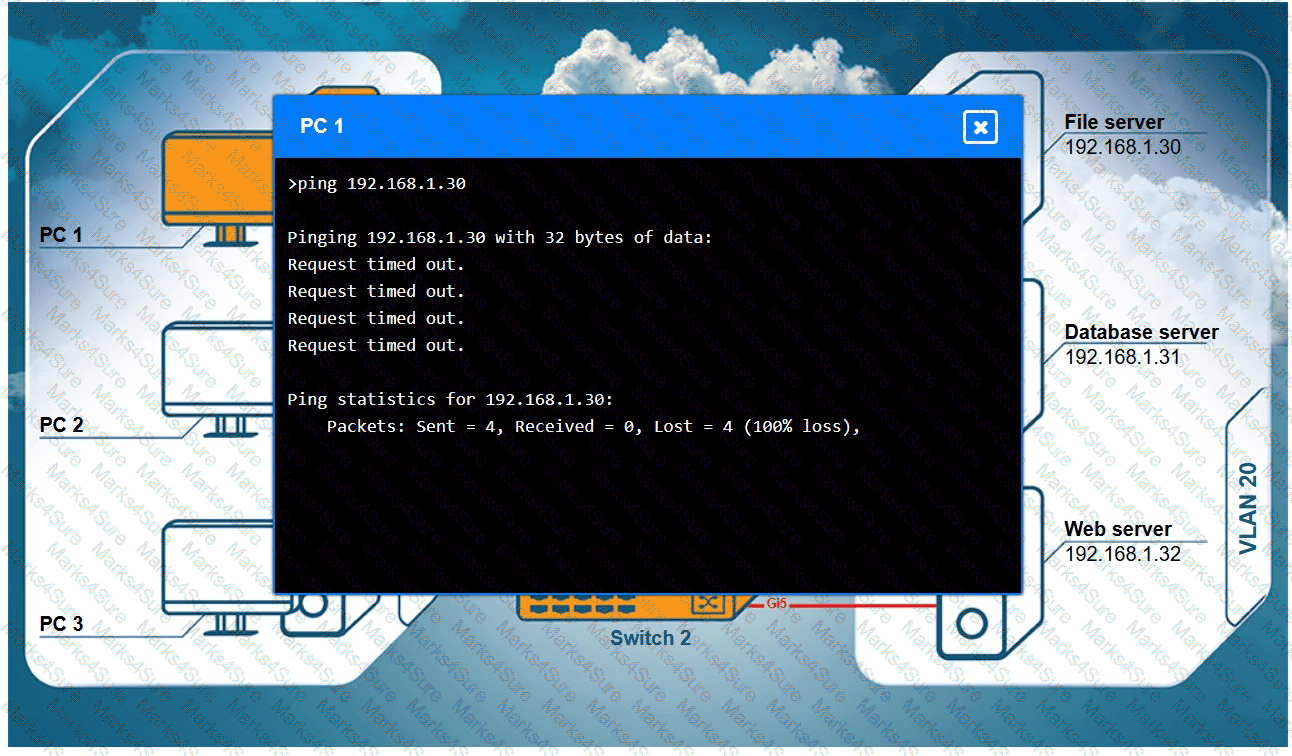
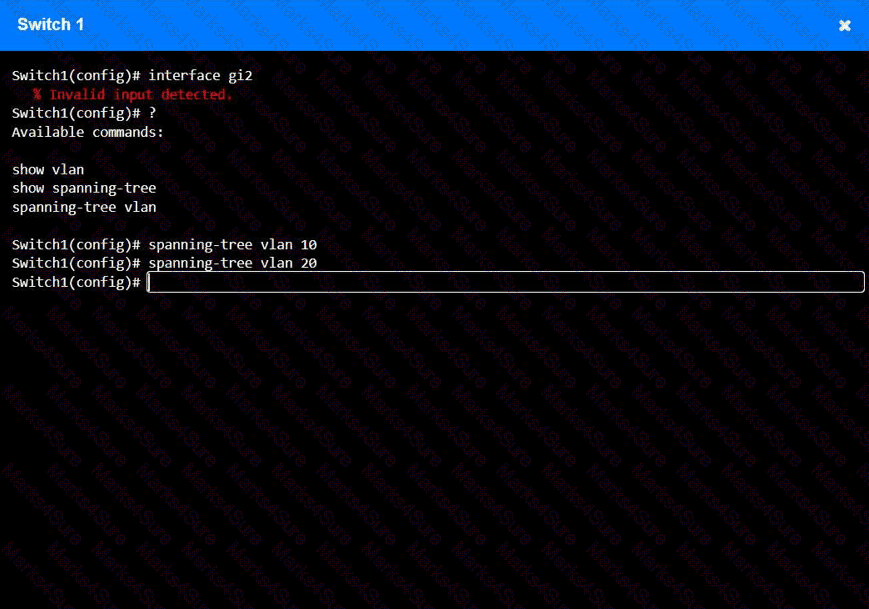
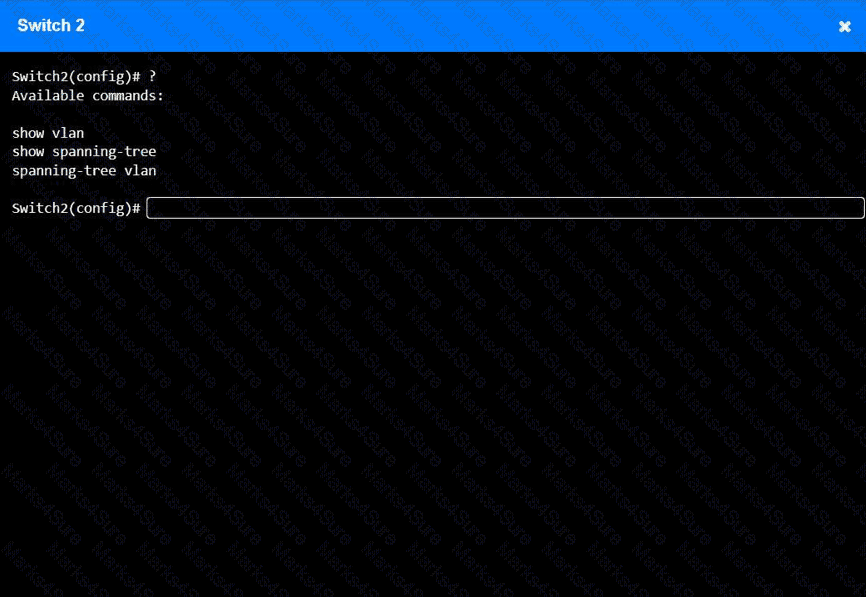
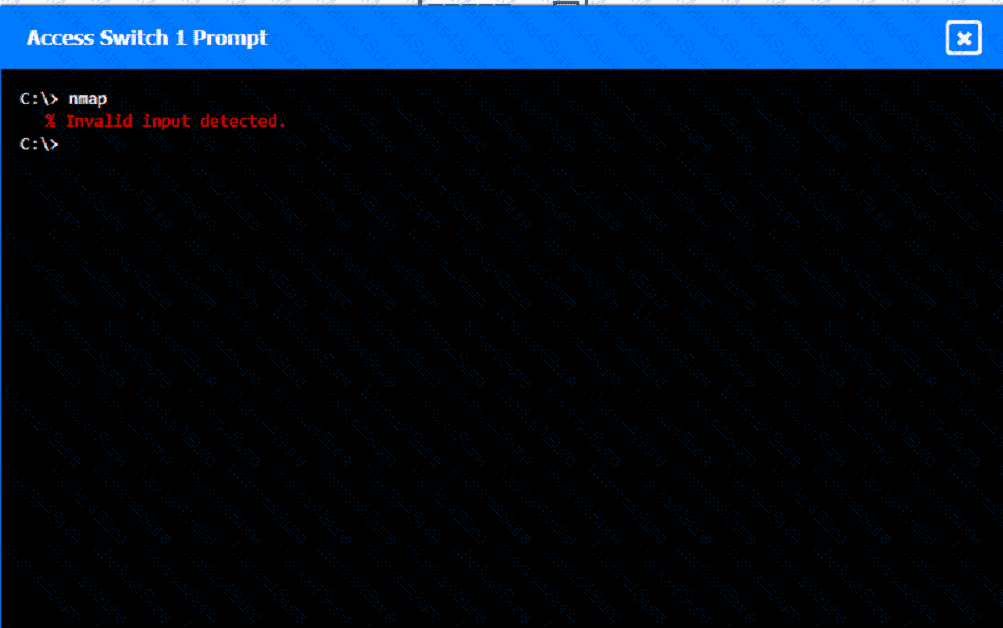
A network technician receives a ticket from an employee who is working on PC 1 but is unable to connect to the database server. The technician pings the database server from PC 1, but the request times out. After reviewing the utilization of Switch 1 and Switch 2, the technician finds high CPU utilization and sees that the MAC table is continuously changing.
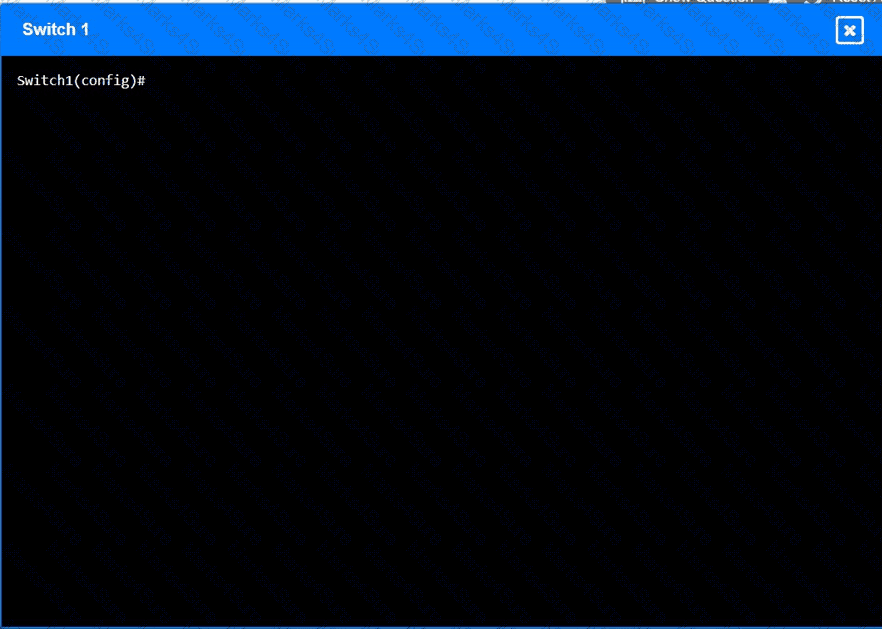
INSTRUCTIONS
Configure Switch 1 and Switch 2 to remediate the employee ' s issue. Then, validate connectivity between PC 1 and the database server.
Switch 1 and Switch 2 are already in configuration mode. Type help to view a list of available commands.
A data center interconnect using a VXLAN was recently implemented. A network engineer observes slow performance and fragmentation on the interconnect. Which of the following technologies will resolve the issue?
A user is unable to navigate to a website because the provided URL is not resolving to the correct IP address. Other users are able to navigate to the intended website without issue. Which of the following is most likely causing this issue?
Which of the following is the most cost-effective way for a network administrator to establish a persistent, secure connection between two facilities?
A network technician sets up a computer on the accounting department floor for a user from the marketing department. The user reports that they cannot access the marketing department’s shared drives but can access the internet. Which of the following is the most likely cause of this issue?
Which of the following is most commonly associated with many systems sharing one IP address in the public IP-addressing space?
Which of the following connection methods allows a network engineer to automate the configuration deployment for network devices across the environment?
Which of the following can be implemented to add an additional layer of security between a corporate network and network management interfaces?
A junior network administrator is auditing the company network and notices incrementing input errors on a long-range microwave interface. Which of the following is the most likely reason for the errors?
Which of the following is the most likely reason an insurance brokerage would enforce VPN usage?
A small company has the following IP addressing strategy:
A user is unable to connect to the company fileshare server located at 192.168.10.1. The user’s networking configuration is:
Which of the following will most likely correct the issue?
Which of the following cloud deployment models is most commonly associated with multitenancy and is generally offered by a service provider?
A network technician is terminating a cable to a fiber patch panel in the MDF. Which of the following connector types is most likely in use?
A network engineer receives a vendor alert regarding a vulnerability in a router CPU. Which of the following should the engineer do to resolve the issue?
A network engineer runs ipconfig and notices that the default gateway is 0.0.0.0. Which of the following address types is in use?
A network technician was recently onboarded to a company. A manager has
tasked the technician with documenting the network and has provided the technician With partial information from previous documentation.
Instructions:
Click on each switch to perform a network discovery by entering commands into the terminal. Fill in the missing information using drop-down menus provided.
While deploying a new fleet of computers on a DHCP network, a network administrator notices that new computers cannot connect to the internet. Which of the following is most likely the problem?
A user tries to visit www.abc.com, but the website that displays is www.cba.com. Which of the following should be done in order to reach the correct website?
A company is concerned that the public can use network wall jacks in publicly available conference rooms to access company servers. Which of the following is the best way to mitigate the vulnerability?
Which of the following types of connectors allows the transmission of network data through a coaxial cable?
A network engineer configures a NIC that has an IP address of 192.168.123.232. Which of the following classes is this address an example of?
A network administrator upgrades the wireless access points and wants to implement a configuration that gives users higher speed and less channel overlap based on device compatibility. Which of the following accomplishes this goal?
Which of the following is a documented set of requirements, such as quality, availability, and responsibilities delivered by a vendor?
A security engineer is trying to connect cameras to a 12-port PoE switch, but only eight cameras turn on. Which of the following should the engineer check first?
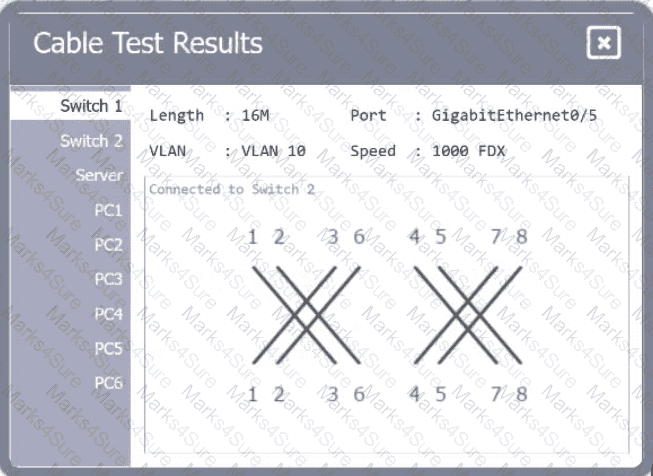
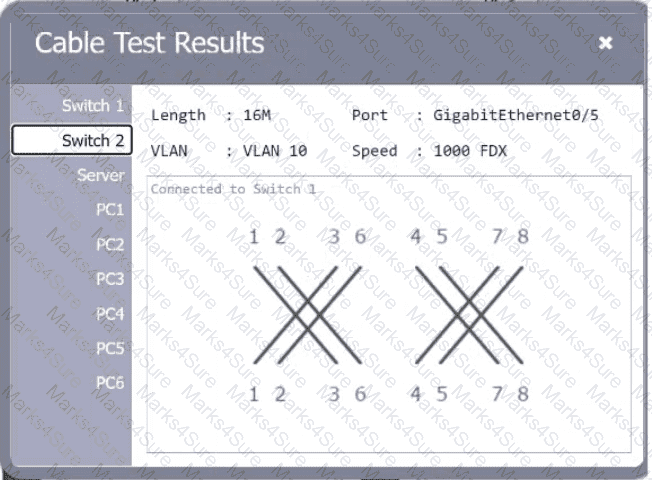
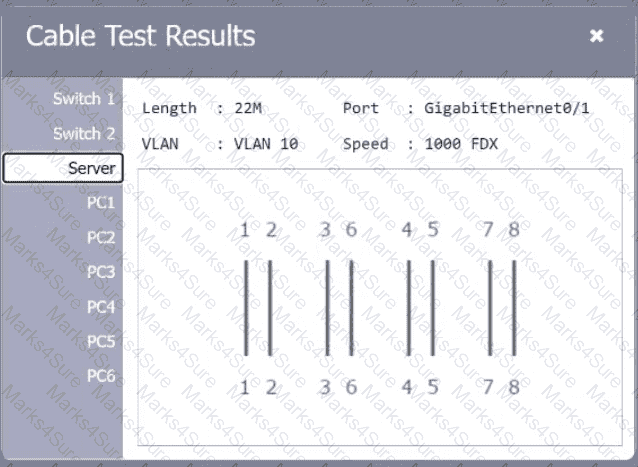
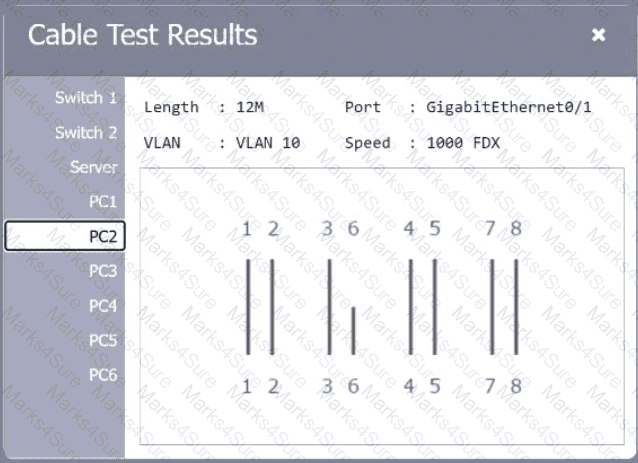
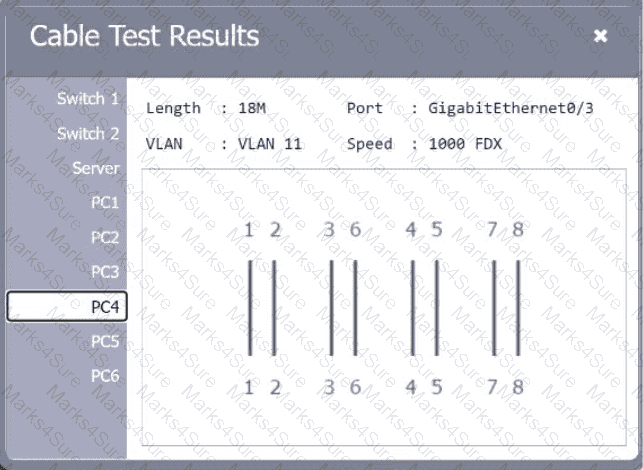
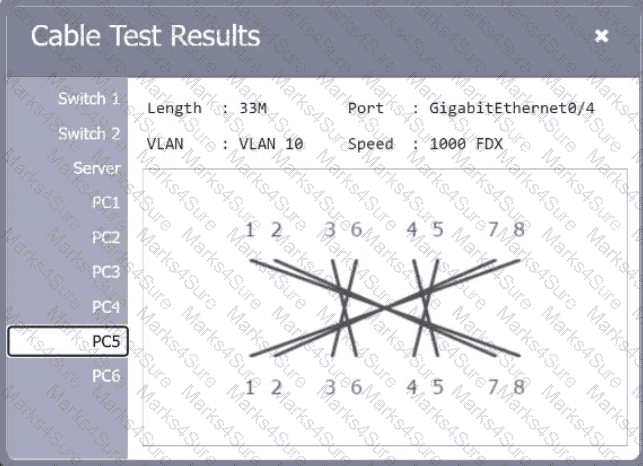
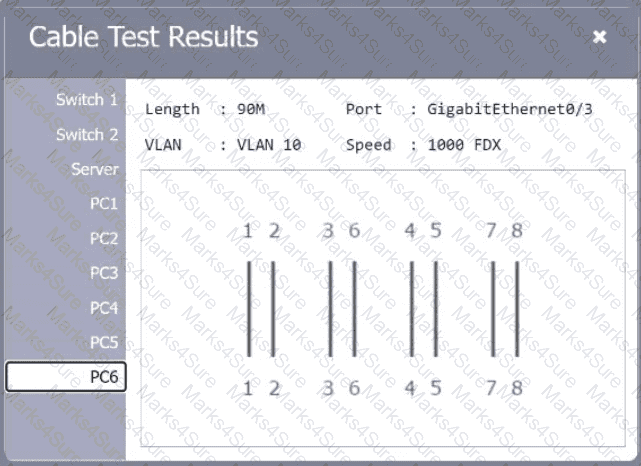
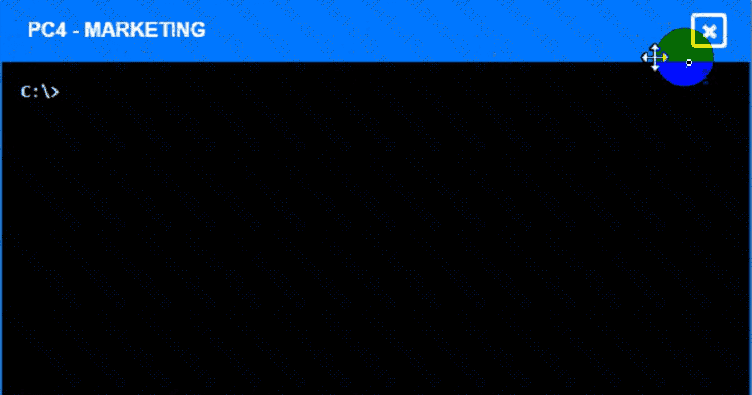
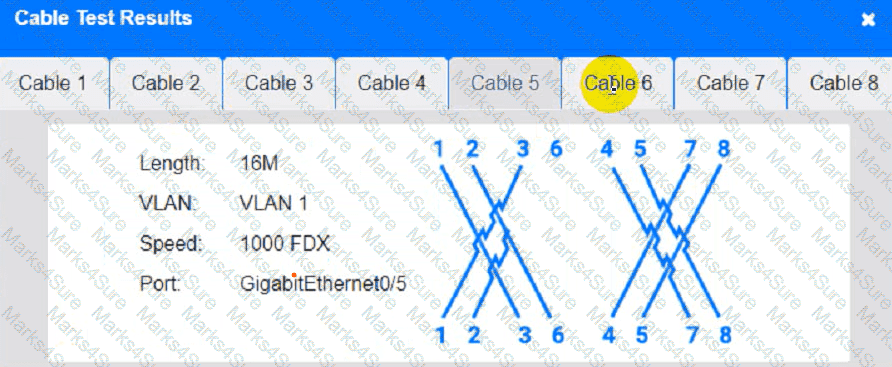
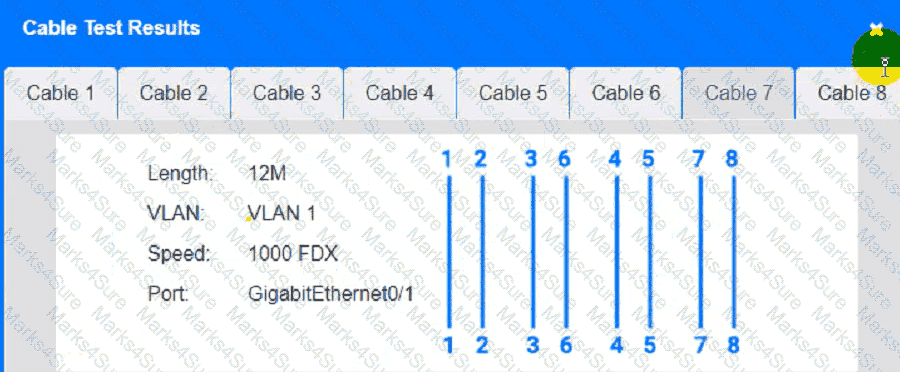
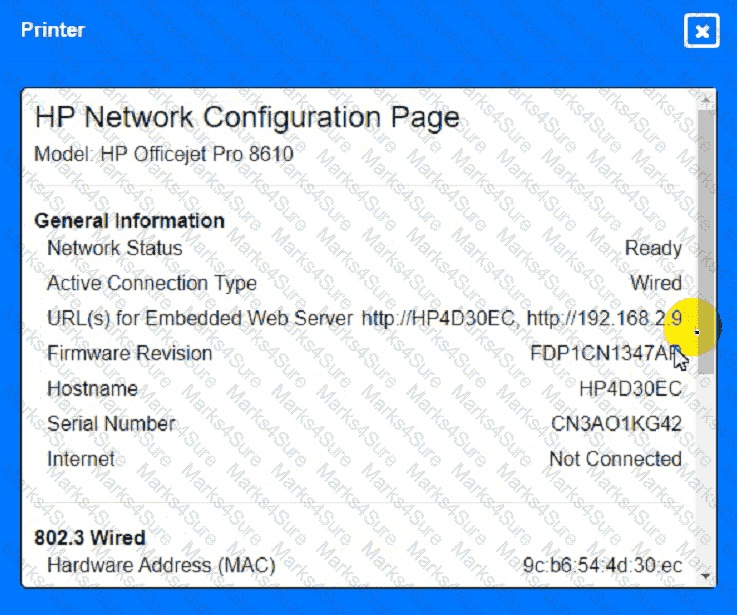
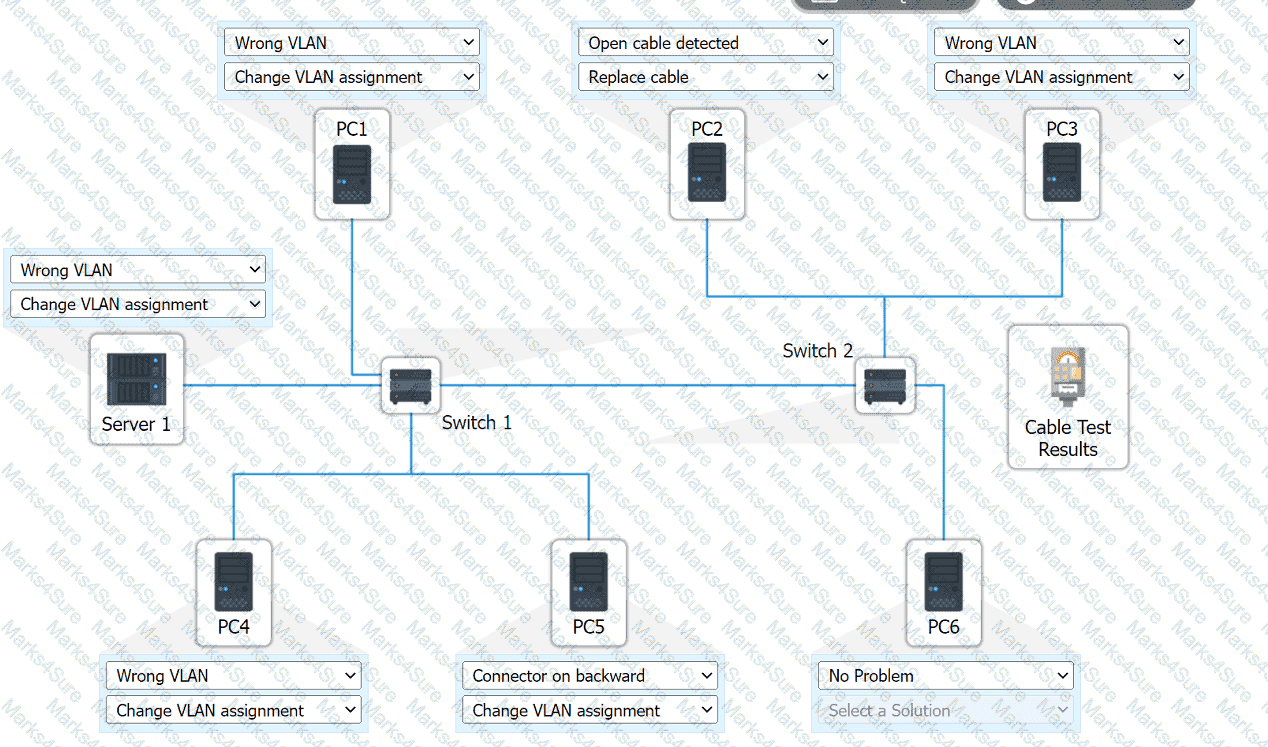
A network technician needs to resolve some issues with a customer ' s SOHO network. The
customer reports that some of the PCs are not connecting to the network, while others
appear to be working as intended.
INSTRUCTIONS
Troubleshoot all the network components.
Review the cable test results first, then diagnose by clicking on the appropriate PC,
server, and Layer 2 switch.
Identify any components with a problem and recommend a solution to correct each
problem.
If at any time you would like to bring back
the initial state of the simulation, please
click the Reset All button.
While troubleshooting connectivity issues, a junior network administrator is given explicit instructions to test the host’s TCP/IP stack first. Which of the following commands should the network administrator run?
Which of the following network devices converts wireless signals to electronic signals?
A user calls the help desk after business hours to complain that files on a device are inaccessible and the wallpaper was changed. The network administrator thinks that this issue is an isolated incident, but the security analyst thinks the issue might be a ransomware attack. Which of the following troubleshooting steps should be taken first?
Which of the following is created to illustrate the effectiveness of wireless networking coverage in a building?
Which of the following allows a user to connect to an isolated device on a stand-alone network?
A network technician needs to resolve some issues with a customer ' s SOHO network.
The customer reports that some of the devices are not connecting to the network, while others appear to work as intended.
INSTRUCTIONS
Troubleshoot all the network components and review the cable test results by Clicking on each device and cable.
Diagnose the appropriate component(s) by identifying any components with a problem and recommend a solution to correct each problem.
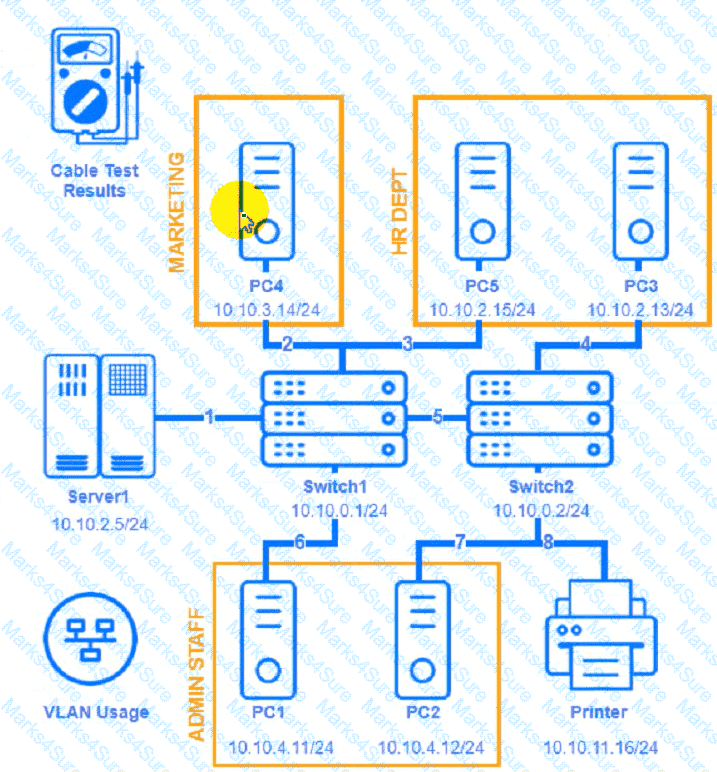

Cable Test Results:
Cable 1:
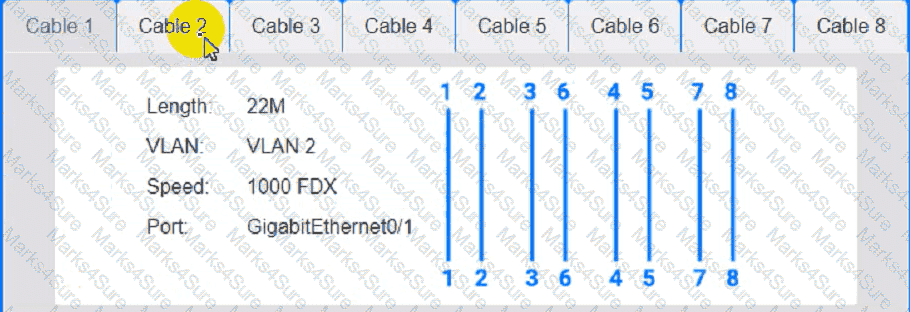
Cable 2:
Cable 3:
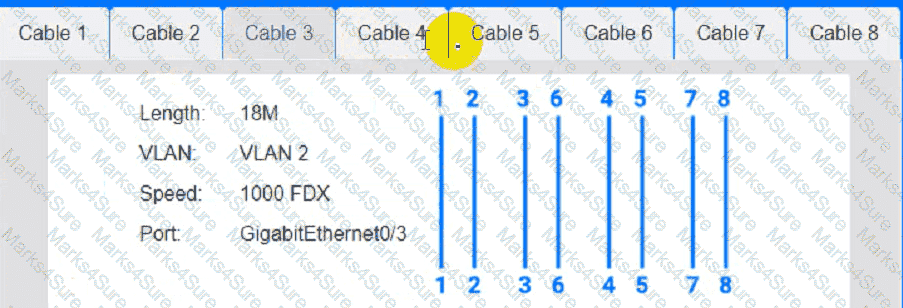
Cable 4:
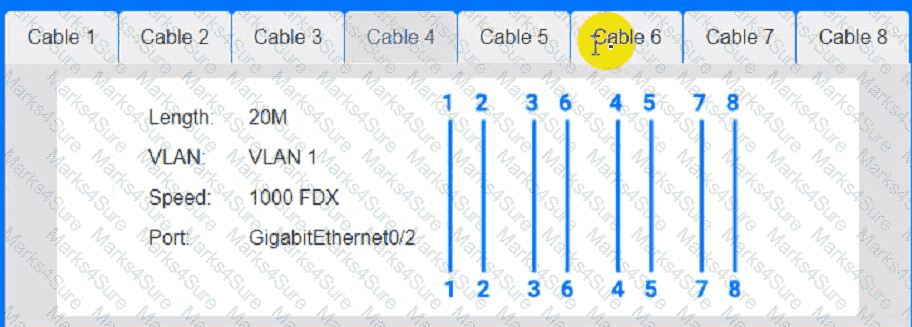
Which of the following can be used when a server at a remote site is physically unreachable?
Which of the following steps of the troubleshooting methodology comes after testing the theory to determine cause?
An organization recently connected a new computer to the LAN. The user is unable to ping the default gateway. The technician examines the configuration and sees a self-assigned IP address. Which of the following is the most likely cause?
A network engineer is installing new PoE wireless APs. The first five APs deploy successfully, but the sixth one fails to start. Which of the following should the engineer investigate first?
A network technician is working on a PC with a faulty NIC. The host is connected to a switch with secured ports. After testing the connection cables and using a known-good NIC, the host is still unable to connect to the network. Which of the following is causing the connection issue?
A network administrator is looking for a solution to extend Layer 2 capabilities and replicate backups between sites. Which of the following is the best solution?
A network administrator installs a node that requires a media converter to connect Ethernet to fiber but sees no link light on the node. The administrator notices the following:
Both terminating points are properly seated.
Both the fiber and Ethernet cables have been successfully tested.
The media converter is turned on.
The switchport is configured as half duplex.
Which of the following is the reason the link light is not on?
A user reports issues accessing a file server on a LAN with the IP address 192.168.50.140 at a large facility with incomplete infrastructure documentation. The following are the results of the ping command:
ping -c 10 192.168.50.140
Packets: Sent = 10, Received = 5, Lost = 5 (50% loss)
Round-trip times: Minimum = 3ms, Maximum = 144ms, Average = 42ms
Which of the following should a technician do next to continue troubleshooting the issue at the switch with minimal impact?
A network administrator needs to add 255 useable IP addresses to the network. A /24 is currently in use. Which of the following prefixes would fulfill this need?
A Chief Executive Officer (CEO) of a company purchases a new phone that will be used while traveling to different countries. The CEO needs to be able to place outgoing calls and receive incoming calls on the phone using a SIM card. Which of the following cellular technologies does the CEO ' s phone need?
A network administrator wants users to be able to authenticate to the corporate network using a port-based authentication framework when accessing both wired and wireless devices. Which of the following is the best security feature to accomplish this task?
A network engineer needs to order cabling to connect two buildings within the same city. Which of the following media types should the network engineer use?
After a networking intern plugged in a switch, a significant number of users in a building lost connectivity. Which of the following is the most likely root cause?
A technician is implementing a new SD-WAN device with a default configuration. The technician receives a URL via email and connects the new device to the internet to complete the installation. Which of the following is this an example of?
A network engineer is now in charge of all SNMP management in the organization. The engineer must use a SNMP version that does not utilize plaintext data. Which of the following is the minimum version of SNMP that supports this requirement?
Which of the following protocols has a default administrative distance value of 90?
Which of the following kinds of targeted attacks uses multiple computers or bots to request the same resource repeatedly?
A network administrator recently configured an autonomous wireless AP and performed a throughput test via comptiaspeedtester.com. The result was 75 Mbps. When connected to other APs, the results reached 500 Mbps. Which of the following is most likely the reason for this difference?
Three access points have Ethernet that runs through the ceiling. One of the access points cannot reach the internet. Which of the following tools can help identify the issue?
Which of the following should be configured so users can authenticate to a wireless network using company credentials?
Users are reporting issues with mobile phone connectivity after a cellular repeater was recently installed. Users also note that the phones are rapidly losing battery charge. Which of the following should the technician check first to troubleshoot the issue?
A network administrator is connecting two Layer 2 switches in a network. These switches must transfer data in multiple networks. Which of the following would fulfill this requirement?
A network engineer is configuring network ports in a public office. To increase security, the engineer wants the ports to allow network connections only after authentication. Which of the following security features should the engineer use?
After a recent merger, a large number of alerts are coming in regarding extremely high utilization. Which of the following should be generated to help inform new alerting requirements?
Users cannot connect to an internal website with an IP address 10.249.3.76. A network administrator runs a command and receives the following output:
1 3ms 2ms 3ms 192.168.25.234
2 2ms 3ms 1ms 192.168.3.100
3 4ms 5ms 2ms 10.249.3.1
4 *
5 ’
6 *
7 •
Which of the following command-line tools is the network administrator using?
A network engineer receives a new router to use for WAN connectivity. Which of the following best describes the layer the network engineer should connect the new router to?
After a company installed a new IPS, the network is experiencing speed degradation. A network administrator is troubleshooting the issue and runs a speed test. The results from the different network locations are as follows:
LocationSpeed DownSpeed Up
Wireless laptop4.8 Mbps47.1 Mbps
Wired desktop5.2 Mbps49.3 Mbps
Firewall48.8 Mbps49.5 Mbps
Which of the following is the most likely issue?
After a security incident, a technician reveals that company data was stolen. During the investigation, it is discovered that a host disguised itself as a switch. Which of the following best describes the attack that occurred?
Which of the following concepts describes the idea of housing different customers in the same public cloud data center?
An organization has four departments that each need access to different resources that do not overlap. Which of the following should a technician configure in order to implement and assign an ACL?
Which of the following should a network engineer check to verify that updates are still being released for a device?
A network administrator has been monitoring the company ' s servers to ensure that they are available. Which of the following should the administrator use for this task?
Which of the following must be implemented to securely connect a company ' s headquarters with a branch location?
A newtwork administrator needs to create an SVI on a Layer 3-capable device to separate voice and data traffic. Which of the following best explains this use case?
A user submits an escalated ticket regarding failed logins on their laptop. The user states that the time displayed on the laptop is incorrect. An administrator thinks the issue is related to the NTP. Which of the following should the administrator do next?
A firewall administrator is mapping a server ' s internal IP address to an external IP address for public use. Which of the following is the name of this function?
Which of the following is used to redistribute traffic between one source and multiple servers that run the same service?
A network administrator needs to connect two routers in a point-to-point configuration and conserve IP space. Which of the following subnets should the administrator use?
A network administrator needs to implement a solution to filter access to the internet. Which of the following should the administrator most likely implement?
A company discovers on video surveillance recordings that an unauthorized person installed a rogue access point in its secure facility. Which of the following allowed the unauthorized person to do this?
A company is opening a new site that needs to be divided into subnets that accommodate 75 hosts each. Which of the following is the most efficient subnet?
As part of a recovery strategy, a network administrator needs to make sure no more than eight hours of data loss occurs. Which of the following DR metrics describes this requirement?
A company is expanding to another floor in the same building. The network engineer configures a new switch with the same VLANs as the existing stack. When the network engineer connects the new switch to the existing stack, all users lose connectivity. Which of the following is the MOST likely reason?
A network administrator for a small office is adding a passive IDS to its network switch for the purpose of inspecting network traffic. Which of the following should the administrator use?
Which of the following best describes the purpose of a UPS and PDU in a network installation?
A network administrator needs to change where the outside DNS records are hosted. Which of the following records should the administrator change the registrar to accomplish this task?
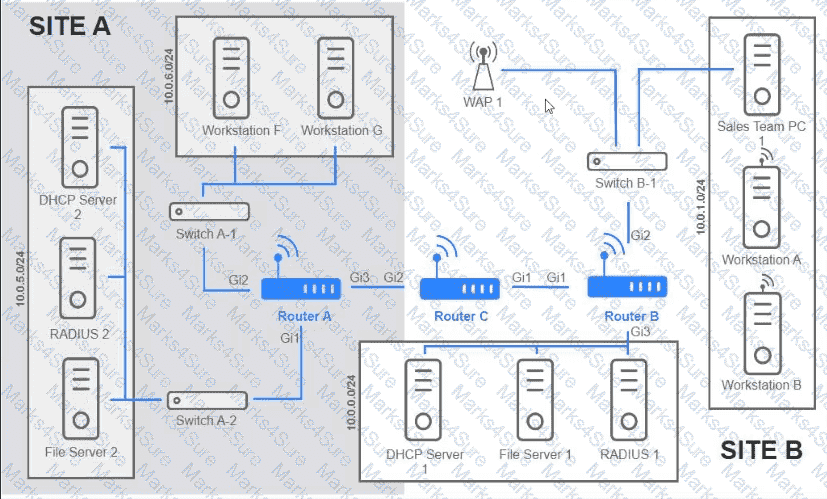
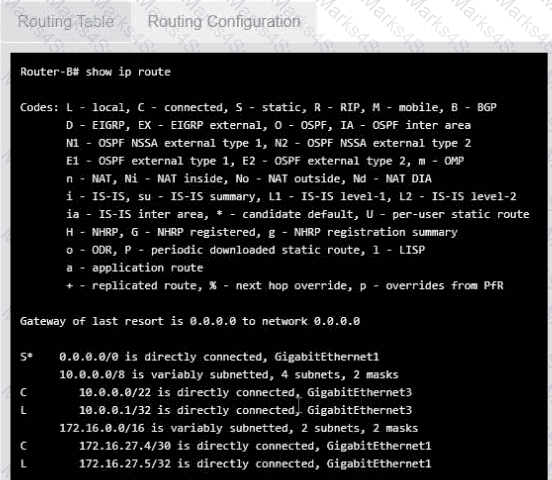
Users are unable to access files on their department share located on flle_server 2. The network administrator has been tasked with validating routing between networks hosting workstation A and file server 2.
INSTRUCTIONS
Click on each router to review output, identity any Issues, and configure the appropriate solution
If at any time you would like to bring back the initial state of trie simulation, please click the reset All button;
A network engineer must determine which ports are currently established from a client device. Given the following:
Active Connections
Proto Local Address Foreign Address State
TCP 10.203.10.11:3389 207.141.201.10:65278 ESTABLISHED
TCP 10.203.10.11:49678 168.63.129.16:32526 ESTABLISHED
TCP 10.203.10.11:49688 168.63.129.16:http ESTABLISHED
TCP 10.203.10.11:49701 168.63.129.16:32526 ESTABLISHED
TCP 10.203.10.11:52502 20.190.135.17:https TIME_WAIT
TCP 10.203.10.11:52554 168.63.129.16:http TIME_WAIT
Which of the following commands was used to produce the output?
While troubleshooting a VoIP handset connection, a technician ' s laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch. Which of the following should the technician use to determine the switch and port?
Users report that they cannot print to a specific IPv4-enabled printer after an extended power outage. Which of the following should a technician configure?
A network administrator notices uncommon communication between VMs on ephemeral ports on the same subnet. The administrator is concerned about that traffic moving laterally within the network. Which of the following describes the type of traffic flow the administrator is analyzing?
A network administrator needs to monitor data from recently installed firewalls in multiple locations. Which of the following solutions would best meet the administrator ' s needs?
A company’s Chief Information Security Officer requires that servers and firewalls have accurate timestamps when creating log files so that security analysts can correlate events during incident investigations. Which of the following should be implemented?
Which of the following is used to store and deliver content to clients in a geographically distributed manner using edge servers?
A virtual machine has the following configuration:
•IPv4 address: 169.254.10.10
•Subnet mask: 255.255.0.0
The virtual machine can reach colocated systems but cannot reach external addresses on the Internet. Which of the following Is most likely the root cause?
After running a Cat 8 cable using passthrough plugs, an electrician notices that connected cables are experiencing a lot of cross talk. Which of the following troubleshooting steps should the electrician take first?
A network technician is troubleshooting the connection to the company website. The traceroute command produces the following output:
Traceroute towww.mysite.com(8.8.8.8) over a maximum of 30 hops
10.1.1.1 < 1 ms 2. * < 1 ms < 1 ms
k k
k kTraceroute completeWhich of the following should the technician do to identify the path to the server?
A wireless technician wants to implement a technology that will allow user devices to automatically navigate to the best available frequency standard. Which of the following technologies should the technician use?
A network manager wants to implement a SIEM system to correlate system events. Which of the following protocols should the network manager verify?
Which of the following best explains the role of confidentiality with regard to data at rest?
A small business is deploying new phones, and some of the phones have full HD videoconferencing features. The Chief Information Officer (CIO) is concerned that the network might not be able to handle the traffic if it reaches a certain threshold. Which of the following can the network engineer configure to help ease these concerns?
A technician is plugging an Ethernet cable into a switch to bring a new device online, but the device is not showing an active network connection. Previously, another technician turned off unused switchports as part of device hardening. Which of the following describes the port status?
Which of the following are the best device-hardening techniques for network security? (Select two).
Which of the following technologies are X.509 certificates most commonly associated with?
A company reports that their facsimile machine no longer has a dial tone when trying to send a fax. The phone cable is damaged on one end. Which of the following types of connectors should a technician replace?
An organization has a security requirement that all network connections can be traced back to a user. A network administrator needs to identify a solution to implement on the wireless network. Which of the following is the best solution?
A network administrator needs to limit devices that can connect to a small wireless network. The network consists of less than ten unique laptops, and no network changes are anticipated. Which of the following is the simplest way to accomplish this task?
A technician is troubleshooting performance and connectivity issues associated with a web server. The technician wants to examine the packets to and from the server but has the following requirements:
Capture 100% of packets
Capture all Layer 1 error packets
Minimize the impact on infrastructure
Which of the following best meets these requirements and allows for the packet capture?
Which of the following routing technologies allows all users to access the internet using only two public IPs?
Which of the following IP transmission types encrypts all of the transmitted data?
Which of the following enables an organization to leverage an identity provider to manage access across SaaS applications?
A network administrator is extending a network beyond the primary equipment location. Which of the following is where the administrator should install additional network switches?
A network technician needs to configure IP addressing in a Class C network with eight subnets total:
Three subnets for 60 hosts
Three subnets for 15 hosts
Two subnets for seven hosts
Which of the following solutions should the technician use to accomplish this task?
An organization wants better network visibility. The organization ' s requirements include:
Multivendor/OS-monitoring capabilities
Real-time collection
Data correlation
Which of the following meets these requirements?
Which of the following is the MOST appropriate solution to extend the network to a building located across the street from the main facility?
During a recent security assessment, an assessor attempts to obtain user credentials by pretending to be from the organization ' s help desk. Which of the following attacks is the assessor using?
A network administrator is configuring a network for a new site that will have 150 users. Within the next year, the site is expected to grow by ten users. Each user will have two IP addresses (one for a computer and one for a phone). Which of the following classful IPv4 address ranges will be best-suited for the network?
An ISP provided a company with a pre-configured modem and five public static IP addresses. Which of the following does the company ' s firewall require to access the internet? (Select TWO).
Following a fire in a data center, the cabling was replaced. Soon after, an administrator notices network issues. Which of the following are the most likely causes of the network issues? (Select two).
A storage network requires reduced overhead and increased efficiency for the amout of data being sent. Which of the following should an engineer likely configure to meet these requirements > ?
A network administrator installs new cabling to connect new computers and access points. After deploying the equipment, the administrator notices a few of the devices are not connecting properly. The administrator moves the devices to a different port, but it does not resolve the issue. Which of the following should the administrator verify next?
Which of the following attacks can cause users who are attempting to access a company website to be directed to an entirely different website?
Which of the following is a type of NAC that uses a set of policies to allow or deny access to the network based on the user ' s identity?
A network architect of a stock exchange broker is implementing a disaster recovery (DR), high-availability plan. Which of the following approaches would be the best fit?
Which of the following connectors allows a singular QSFP transceiver to have several physical connections?
An administrator is configuring a switch that will be placed in an area of the office that is accessible to customers. Which of the following is the best way for the administrator to mitigate unknown devices from connecting to the network?
A network administrator wants an automatic alert to be sent when a switch ' s link status changes, administered through SNMP. Which of the following SNMP technologies will allow for this alert?
A network engineer adds a tunnel for a new branch network. Which of the following ensures that all data is encrypted inside the tunnel?
Which of the following network traffic types is sent to all nodes on the network?
Which of the following steps in the troubleshooting methodology includes checking logs for recent changes?
A network engineer is deploying switches at a new remote office. The switches have been preconfigured with hostnames and STP priority values. Based on the following table:
Switch Name
Priority
core-sw01
24576
access-sw01
28672
distribution-sw01
32768
access-sw02
36864
Which of the following switches will become the root bridge?
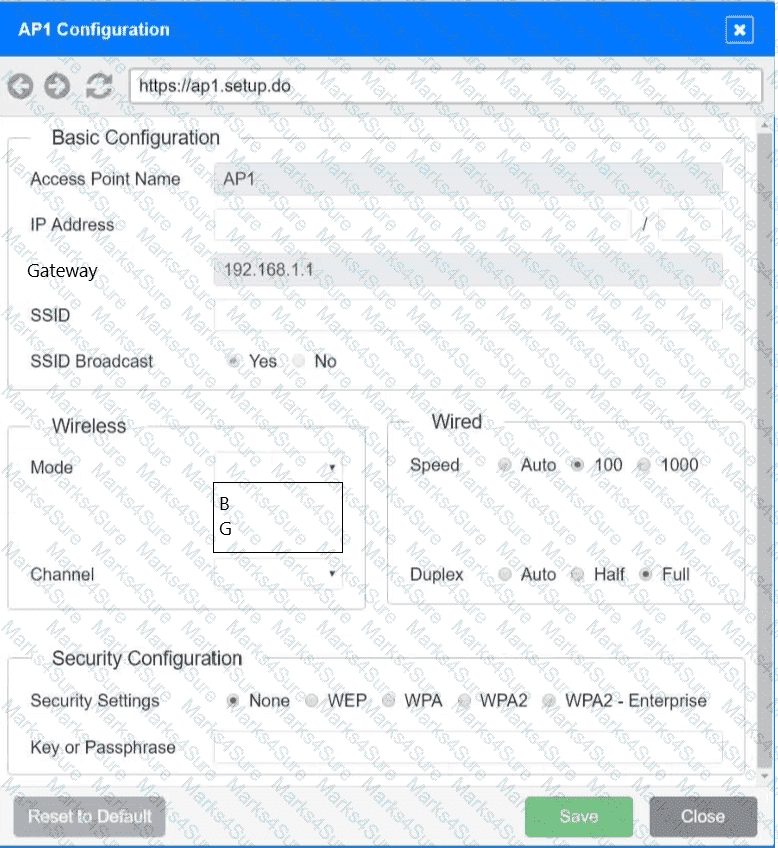
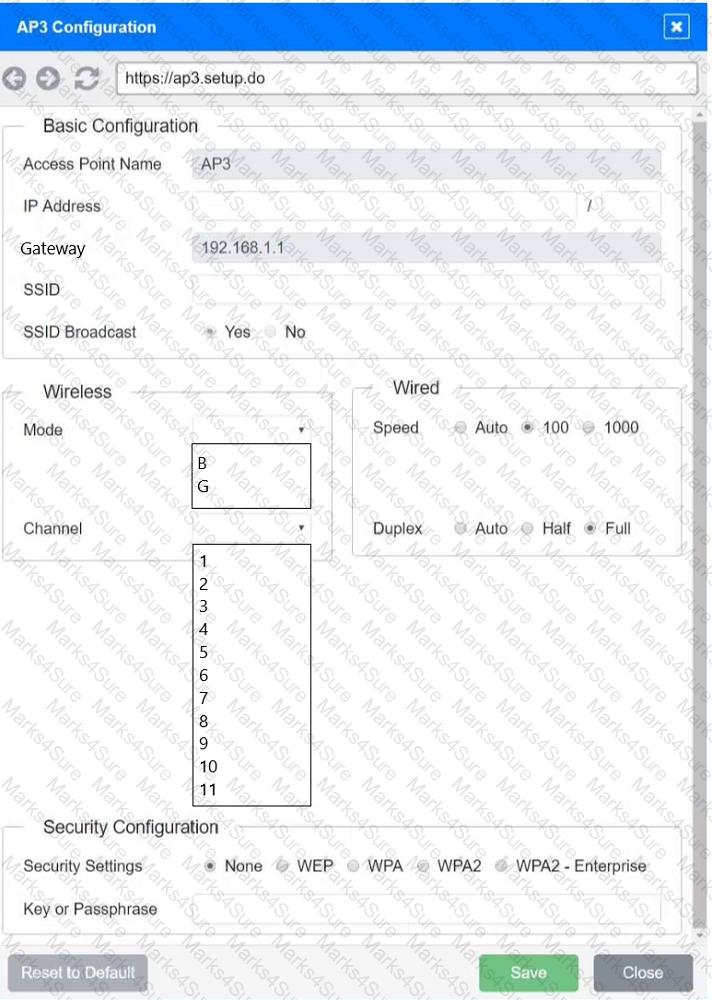
SIMULATION
You have been tasked with setting up a wireless network in an office. The network will consist of 3 Access Points and a single switch. The network must meet the following parameters:
The SSIDs need to be configured as CorpNet with a key of S3cr3t!
The wireless signals should not interfere with each other
The subnet the Access Points and switch are on should only support 30 devices maximum
The Access Points should be configured to only support TKIP clients at a maximum speed
INSTRUCTONS
Click on the wireless devices and review their information and adjust the settings of the access points to meet the given requirements.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
After installing a new 6E wireless router in a small office, a technician notices that some wireless devices are not able to achieve the rated speeds.
Which of the following should the technician check to troubleshoot the issue? (Select two)
Which of the following most likely determines the size of a rack for installation? (Select two).
To reduce costs and increase mobility, a Chief Technology Officer (CTO) wants to adopt cloud services for the organization and its affiliates. To reduce the impact for users, the CTO wants key services to run from the on-site data center and enterprise services to run in the cloud. Which of the following deployment models is the best choice for the organization?
Which of the following is the best example of a networking appliance that connects different network segments and directs allowed traffic between specific segments?


 A computer network diagram with many boxes and text AI-generated content may be incorrect.
A computer network diagram with many boxes and text AI-generated content may be incorrect.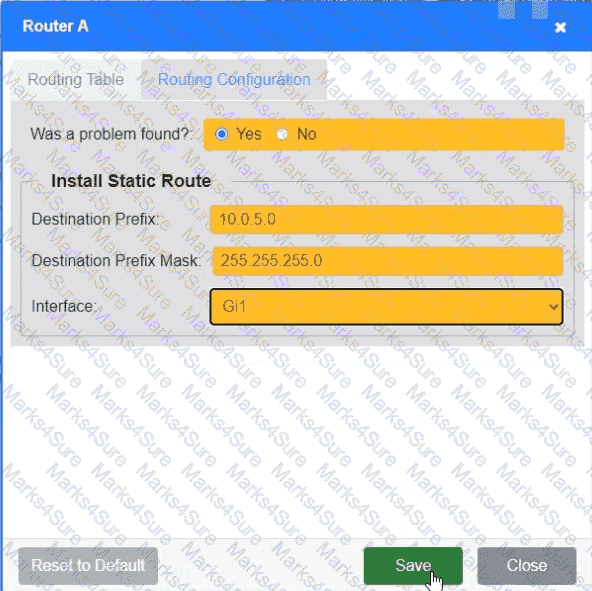 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.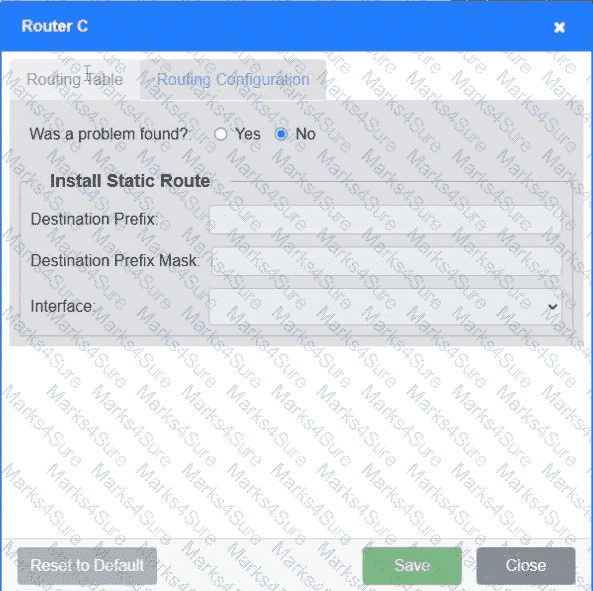 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.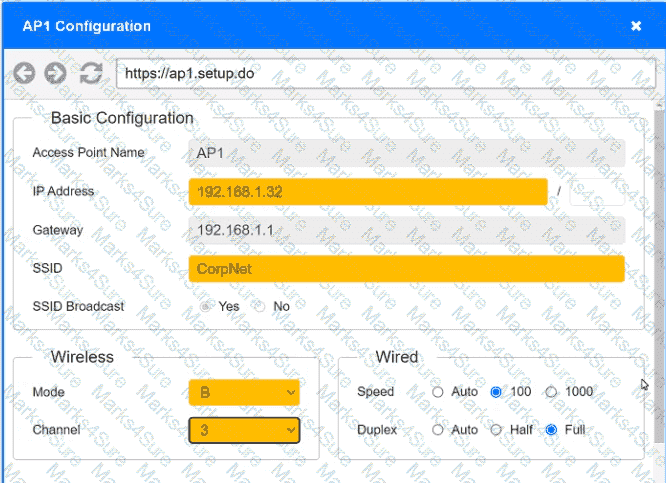 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.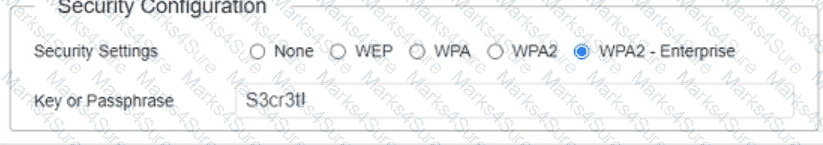 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.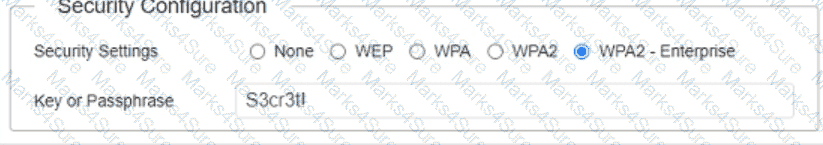 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.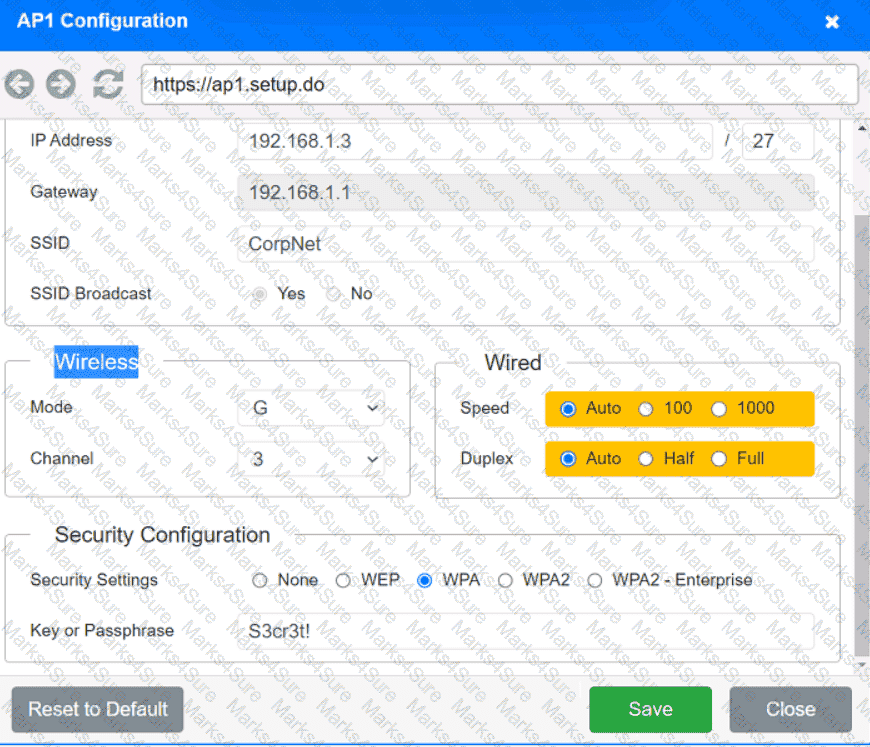 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.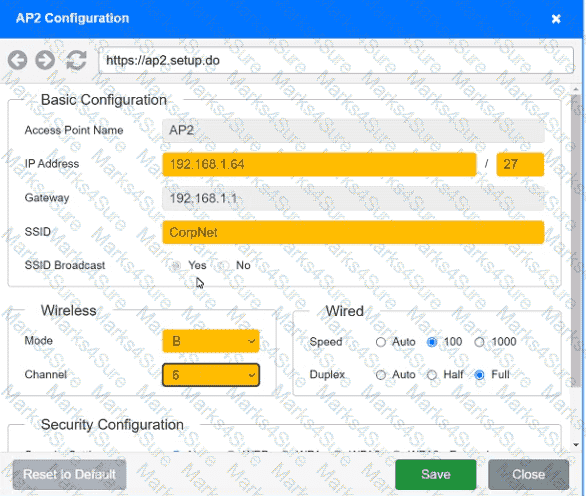 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.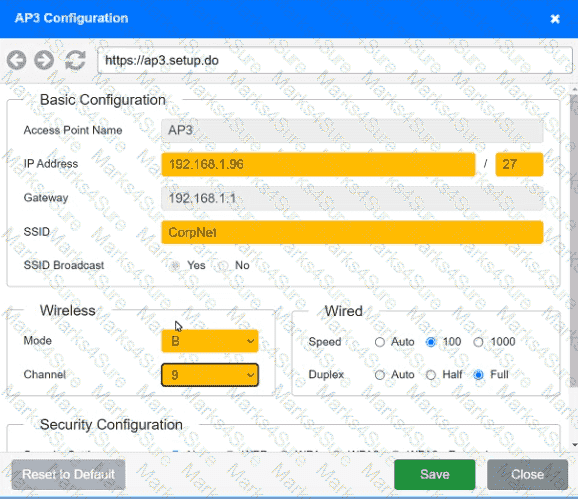 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.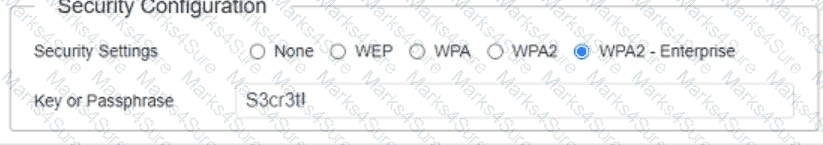 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.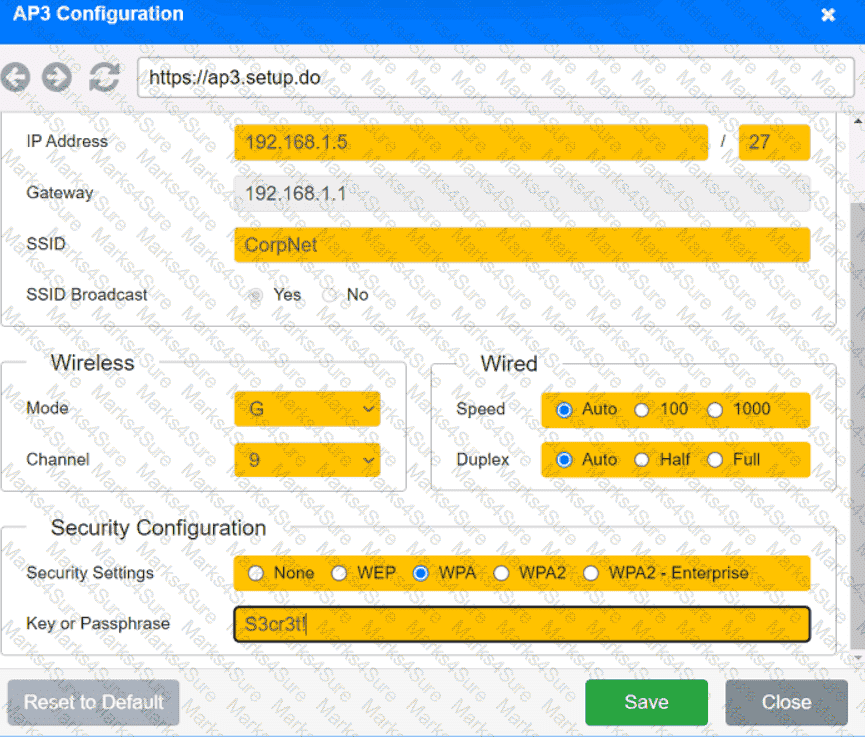 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.
