NCP-NS-7.5 Nutanix Certified Professional - Network and Security (NCP-NS) 7.5 Questions and Answers
During a security review, the administrator confirms that the existing security policy does not explicitly allow traffic from Environment: Development to Environment: Production. A VM in the Development category was still able to reach a Production VM over IPv6. What is the most likely cause of this behavior?
An administrator has two user VPCs connected via a Transit VPC. Routing works for most subnets, but one overlay subnet cannot reach external networks. What is the most probable cause?
While configuring a new security policy in a Nutanix microsegmentation environment, an administrator wants the policy to remain flexible even if virtual machines change subnets or obtain new IP addresses. Which configuration approach should the administrator use when defining the policy scope?
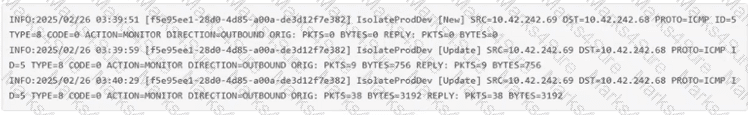
An administrator has observed the following message: Which two statements most accurately describe the security hitlog captured above? (Choose two.)
While configuring third-party services (Service Insertion) in Flow Network Security Next-Gen, an administrator notices dropped packets when redirecting traffic through a network function. Which configuration change would address this issue?
In Nutanix Flow, which action transitions a security policy from observing traffic to actively enforcing the rules?
An administrator is building a VPC... VPC CIDR: 10.10.0.0/16 Subnet CIDR: 10.10.10.0/24 "Ext_Net_Ext" (NAT): 192.168.1.0/24 "Ext_Net_Internal" (Routed): 172.16.1.0/24 The on-premises application server has an IP address of 172.16.2.50/24. A VM (10.10.10.100) in the VPC Subnet can reach the internet but cannot reach the on-premises server. Which static route needs to be added to the VPC route table to resolve this?
An administrator notices that several VMs in a Nutanix AHV cluster are intermittently losing network connectivity. In Prism Central, a critical alert appears: "Network Function VM (NFVM) packet processing delays" What is the next step that the administrator should take for this issue?
An administrator uses Nutanix Flow to secure a three-tier application (Web, App, and Database tiers). After observing the traffic, they find that: The Web tier communicates with the App tier over HTTP (port 80) The App tier communicates with the Database tier over TCP port 1433 The Database tier does not initiate connections The Web tier receives inbound HTTP traffic from the corporate DMZ on port 8080 No other traffic should be allowed What should the administrator do to document and then securely apply these flows in Nutanix Flow?
Which prerequisite is required before enabling Flow Network Security Next-Gen micro segmentation?
An administrator is using Flow Network Security to secure a 3-tier application and has already created and assigned the categories. The administrator does not have the details of the rules that need to be allowed to secure the application. How can the administrator use Flow Network Security to monitor the traffic and help with the policy creation without impacting the applications connectivity?
An administrator has created a VPC with the following subnets: 10.1.1.0/24 10.1.2.0/24 10.1.3.0/24 What action must be taken for these networks to be externally routable?
A customer wants to migrate VMs from a VLAN Basic Subnet to an Overlay Subnet with the same IP prefix. Which migration approach ensures minimal disruption?
What is the additional resource requirement for each Prism Central VM when enabling Flow Virtual Networking on a Small Prism Central deployment?
An administrator is designing a new Transit VPC to service multiple Tenant VPCs. While adding subnets, the administrator must choose the correct network type supported by Flow Virtual Networking for this VPC. Which network type is supported for subnets inside a Transit VPC in Flow Virtual Networking?
When configuring an Application policy, an administrator defines a VM Category Application:MySQL as a Secured Entity. The administrator wants to ensure that traffic between VMs in the Secured Entity is kept to only required replication traffic on the default mysql service port. How should the administrator best accomplish this?
An administrator receives a ticket reporting unwanted traffic between production and development servers. The administrator reviews the Flow Network Security logs and finds the following:
How can the administrator resolve the issue?
An administrator needs to isolate communication between VMs in Production and Development environments. Each VM is categorized by Environment and Site category values. The administrator wants this isolation to apply only to VMs located at Site: Branch-001. Which configuration best meets the requirement?
An administrator is configuring a Nutanix environment for Flow Network Security Next-Gen. Where should the MTU be set to ensure that Geneve encapsulation overhead is properly accounted for?
Exhibit:
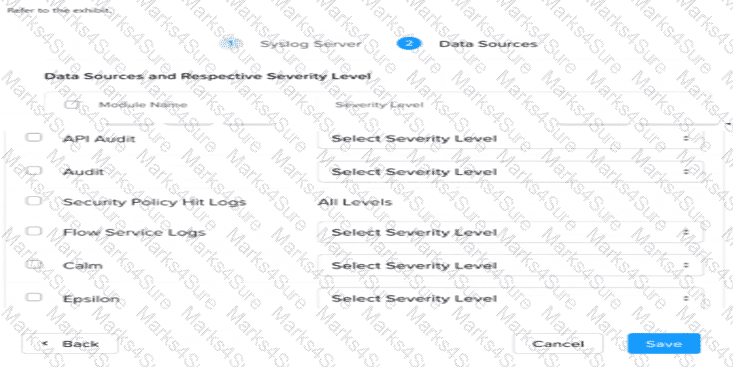
An administrator needs to setup a Syslog server to capture the Flow Network Security Hit logs. Which module name should be selected?
An administrator has a VPC with a single active gateway node that successfully peers with an external router using a single BGP GW and session. To eliminate a single point of failure, the administrator deploys a second BGP gateway to the VPC. After the second gateway is added and shows a healthy state, the external router still only sees a single BGP session. What is the most likely reason for the second session not being established on the external router?
An administrator has a VPC with multiple overlay subnets and a VPN gateway configured for site-to-site connectivity. During testing, the administrator noticed fragmented packets and poor performance. Which configuration change resolves this issue without disabling VPN?
An administrator needs to use Prism Central to identify a subnet belonging to a VPC. How can the administrator identify networks associated with a VPC within Prism Central?
An administrator is setting up a transit VPC to connect two VPCs and enable both internal (on-prem) and Internet connectivity. Which is the best configuration to meet the requirement?


